IoT Security in Smart Cities: GCC Risks & Fixes
IoT Security in Smart Cities: GCC Risks & Fixes
IoT Security in Smart Cities: GCC Risks & Fixes
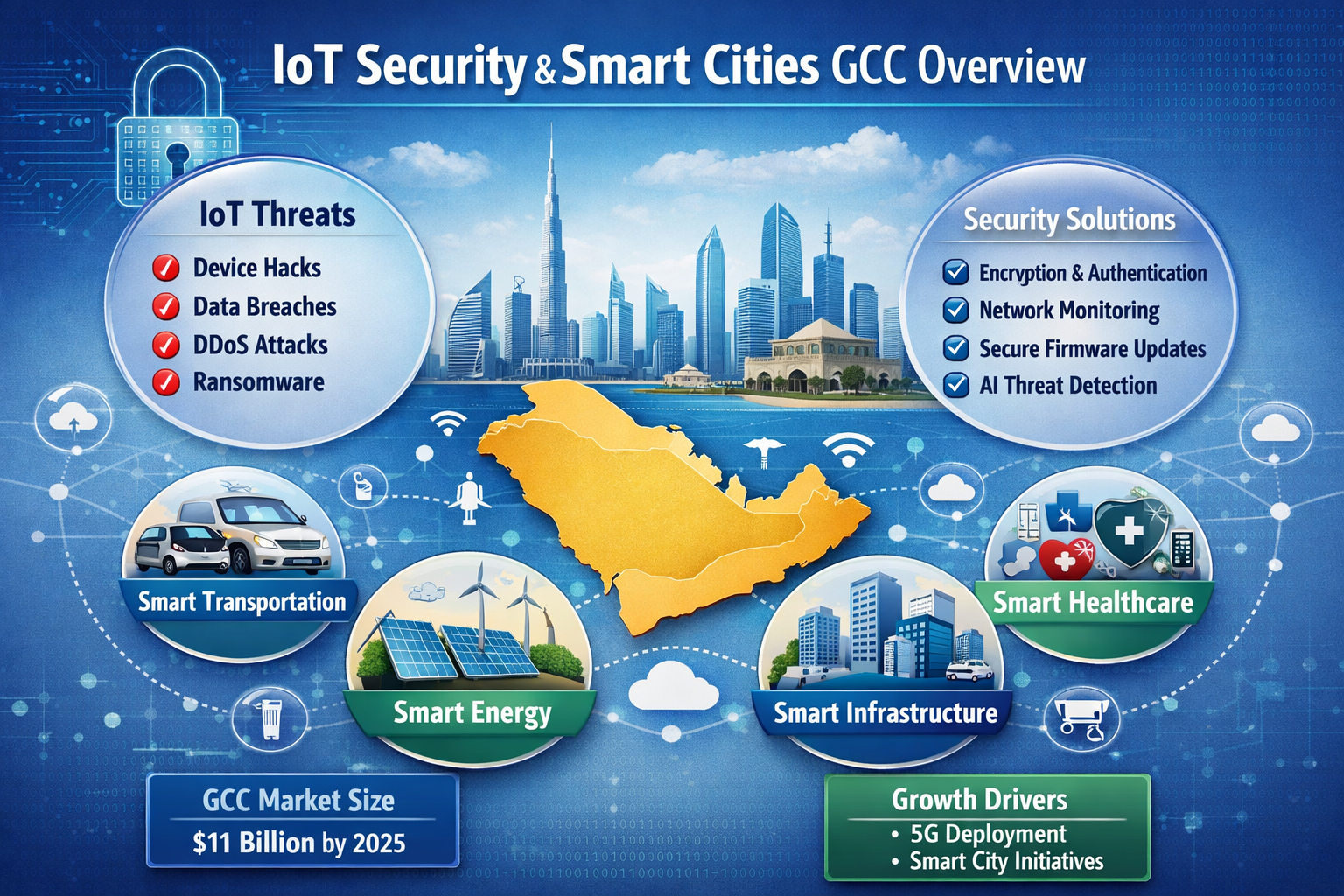
Smart cities across Saudi Arabia, the UAE, and Qatar rely on connected devices to keep transport, utilities, buildings, surveillance, and public services running smoothly. That same connectivity also expands cyber risk. IoT security in smart cities is the practice of protecting sensors, cameras, gateways, platforms, and control systems so digital infrastructure can scale without putting operations, compliance, or public trust at risk.
In the GCC, the most effective approach usually combines strong device identity, network segmentation, secure firmware, continuous monitoring, and governance aligned with national expectations. For municipalities, developers, and operators in Riyadh, Dubai, Abu Dhabi, and Doha, that is no longer optional. It is part of resilient city planning.
What IoT Security in Smart Cities Means in the GCC
How smart city ecosystems connect sensors, OT, cloud, and public services
In GCC smart city environments, connected infrastructure rarely works in isolation. A traffic sensor in Riyadh may feed a central operations platform. A building management system in Dubai may connect with cloud dashboards, access control, and mobile applications. An environmental monitor in Doha may support broader municipal planning and service delivery.
That interconnected model improves visibility and efficiency, but it also increases dependency between devices, operational technology, cloud environments, and public-facing systems. This is why modern city programs increasingly combine cyber controls with secure web development services, business intelligence services, and reliable mobile app development services.
Why Riyadh, Dubai, and Doha face a broader attack surface
Traditional IT environments are easier to contain. Smart city infrastructure is different. It is distributed, long-lived, and often managed by multiple vendors across different sites.
Field devices may run outdated firmware. Some connect through mixed networks. Others still rely on weak authentication or inconsistent maintenance. The result is a wider attack surface and more opportunities for lateral movement between systems.

Where cybersecurity overlaps with public safety and city operations
The impact of weak IoT security in smart cities goes beyond data loss. A compromised system can affect traffic operations, CCTV reliability, utilities visibility, smart building access, and service continuity.
For GCC governments and operators, that turns cybersecurity into a public trust issue. When citizens depend on connected infrastructure every day, resilience matters just as much as innovation.
Biggest IoT Security Risks in Smart Cities
Insecure devices, default credentials, and unmanaged firmware
One of the biggest problems is still the device itself. Default passwords, weak asset inventory, and delayed updates remain common in large deployments.
In municipal estates with hundreds or thousands of endpoints, unmanaged firmware can leave entire groups of sensors, cameras, or gateways exposed at the same time. That makes even small oversights scale into major risk.
Weak network segmentation across buildings, traffic, CCTV, and utilities
When surveillance systems, building controls, transport infrastructure, and utilities sit on flat or loosely separated networks, attackers can move sideways from a low-priority device to a critical system.
Strong segmentation reduces that risk. In practice, this means separating environments by function, limiting east-west traffic, and applying tighter controls around access between zones.
Third-party vendors, supply chain gaps, and legacy OT integration
Most smart city projects in Saudi Arabia, the UAE, and Qatar involve multiple vendors. Telecom providers, systems integrators, cloud platforms, OT specialists, and maintenance contractors all play a role.
That speeds up delivery, but it can also create inconsistent controls, unclear accountability, and security gaps between old and new systems. Vendor due diligence matters. So does platform hardening, whether the deployment includes custom portals, enterprise tools, or selected WordPress web development services.
Why GCC Smart City Projects Face Unique Security Pressure
Compliance-led procurement in Saudi Arabia, UAE, and Qatar
In the GCC, technology buying decisions are often shaped by compliance, governance, and risk review as much as functionality. Public-sector and regulated projects are expected to show control maturity early, not after deployment.
That means IoT security in smart cities often becomes part of procurement, architecture approval, and vendor selection from the start.
Data residency, sovereignty, and public-sector trust
Smart city systems may process location data, video feeds, building events, operational logs, and records linked to public services. In Saudi Arabia, data governance expectations are influenced by national oversight bodies such as NDMO under SDAIA. In Qatar, digital infrastructure priorities are tied closely to national transformation goals. In the UAE, public-sector trust and regulated jurisdictions such as ADGM and DIFC shape governance expectations around technology and risk.
For municipalities and operators, hosting and data flow decisions are not just technical. They are strategic.
Bilingual operations and distributed teams
Many GCC projects operate across Arabic- and English-speaking teams. Municipal command centers, facility operators, contractors, and support vendors may all work within the same environment.
That means security controls must be usable in real operations. Dashboards, alerts, workflows, and incident procedures should be clear across multilingual teams, not just well designed on paper.

GCC Compliance and Governance Triggers for IoT Security
Saudi Arabia.
In Saudi Arabia, connected infrastructure should align with national cybersecurity expectations and stronger data governance discipline. For smart city operators, this usually affects procurement standards, asset handling, access control, and operational accountability.
Where public-sector data or regulated environments are involved, governance maturity becomes especially important.
UAE.
In the UAE, digital government initiatives and telecom oversight help shape the wider direction of secure infrastructure. At the same time, regulated business environments such as ADGM and DIFC reinforce the importance of strong IT risk controls, vendor governance, and operational resilience.
That broader compliance culture influences how connected infrastructure is designed and managed in Dubai and Abu Dhabi.
Qatar.
In Qatar, smart infrastructure planning sits close to national digital transformation goals. For municipal and public-facing deployments, that means connected platforms should fit into a wider governance model rather than being treated as isolated pilots.
Where projects intersect with regulated services, procurement teams should also review the relevant control expectations early in the process.
Practical Fixes for Smart City IoT Security
Device identity, certificate management, and secure onboarding
Every device should have a unique identity and a trusted onboarding path. Shared credentials may be easy to deploy, but they are difficult to defend at scale.
Certificate-based authentication is a stronger option for city-wide environments because it improves trust, accountability, and lifecycle management.
Zero trust, micro-segmentation, and continuous monitoring
The strongest smart city environments do not assume internal traffic is safe. They separate transport systems, smart buildings, CCTV, and utilities into controlled zones, apply least-privilege access, and monitor east-west movement continuously.
This is where cyber architecture matters far more than marketing features. Even when public platforms include e-commerce solutions or digital interfaces supported by secure delivery teams, governance still needs to sit at the center.
Secure updates, vulnerability management, and incident response
Smart cities need a repeatable process for firmware updates, rollback planning, vulnerability tracking, and field incident response.
A mobility project in Riyadh, a smart venue in Dubai, or a logistics operation in Doha should all know how to isolate compromised endpoints quickly and recover without prolonged disruption.
Use Cases Across Saudi, UAE, and Qatar Smart Cities
Securing smart transport and mobility in Riyadh and Doha
Transport systems depend on reliable data and constant availability. Roadside devices, telemetry feeds, and edge gateways should be isolated from broader networks, continuously monitored, and validated for integrity.
That is especially important in cities expanding connected mobility services at pace.
Protecting smart buildings in Dubai and Abu Dhabi
Dubai and Abu Dhabi continue to invest heavily in connected buildings and facilities. In these environments, HVAC, access control, lifts, and CCTV should be segmented and managed with role-based visibility for facilities teams.
Operational dashboards also need to be clear and usable. In some cases, that includes support from secure interface design and graphic designing services that improve visibility without weakening control discipline.

Reducing cyber risk in utilities, surveillance, and public services
Utilities and surveillance systems often carry some of the highest operational risk because they are widely distributed and frequently supported by third parties.
Across GCC cities, these environments benefit from.
Asset discovery across connected estates
Third-party access review
Clear ownership of devices and gateways
Stronger segmentation
hosting decisions aligned with sovereignty and resilience needs
Cloud choices, including regional options such as AWS Bahrain, Azure UAE regions, or expanding Qatar cloud capacity, should support governance requirements where needed.
How GCC Municipalities Should Prioritize IoT Security Investments
Start with quick wins for high-risk assets
A practical starting point is simple:
Build a reliable asset inventory
Remove default credentials
Classify critical devices
Identify unmanaged firmware
Segment the most exposed networks first
These steps do not solve everything, but they reduce immediate risk fast.
Evaluate vendors beyond features alone
When comparing vendors or managed service providers, municipalities should ask direct questions about.
Device identity and certificate support
Firmware update processes
Incident response capability
Arabic-friendly operational workflows
Regional hosting and sovereignty options
Support for long-lived field assets
The goal is not just to buy technology. It is to buy control, visibility, and accountability.
Build a phased roadmap for long-term resilience
The most effective roadmap usually follows a clear sequence: visibility first, segmentation next, then governance and automation.
That approach helps Saudi, UAE, and Qatar teams expand smart city services without expanding unmanaged risk at the same pace.

Final Thoughts
Smart city growth creates real value, but growth without security introduces operational, compliance, and reputational exposure. IoT security in smart cities should be treated as a core part of digital infrastructure planning, not a late-stage add-on.
Mak It Solutions can help review connected assets, strengthen segmentation, improve visibility, and build a GCC-ready roadmap for secure digital infrastructure. Explore the full services portfolio or request a tailored strategy for Saudi, UAE, or Qatar deployments.( Click Here’s )
FAQs
Q : Is IoT security mandatory for smart city projects in Saudi Arabia?
A : In many Saudi public-sector and regulated environments, strong IoT security is effectively expected because connected infrastructure must align with broader cybersecurity and data governance requirements. It may not always appear as one standalone IoT rule, but it still affects procurement, architecture, and operations in practice.
Q : How do UAE smart buildings reduce IoT cyber risk without slowing operations?
A : The most effective approach is not to apply one heavy control across everything. Smart buildings reduce risk by segmenting HVAC, access control, CCTV, and tenant systems, then adding monitoring, device identity, and vendor access controls. That keeps operations efficient while improving trust and resilience.
Q : What should Qatar municipalities check before deploying connected sensors?
A : They should review device identity, firmware support, data flows, vendor responsibility, and hosting location first. They should also assess whether the project touches regulated services, public-sector data, or critical infrastructure before rollout.
Q : Which smart city systems are most vulnerable in Riyadh, Dubai, and Doha?
A : The highest-risk systems are usually the most distributed and least consistently managed. That often includes CCTV estates, traffic devices, smart building controllers, utility monitoring equipment, and third-party managed gateways.
Q : How does data residency affect CCTV, utilities, and public IoT platforms in the GCC?
A : Data residency shapes where video, telemetry, logs, and citizen-linked records can be stored, processed, and accessed. In the GCC, that matters because public trust, sovereignty, and sector-specific governance often influence approval, hosting, and access models.



[…] Why Edge AI Smart City Architecture Fits the GCC […]