CI/CD Pipeline Security: Secure Every Release Step
CI/CD Pipeline Security: Secure Every Release Step

CI/CD Pipeline Security: Secure Every Release Step
CI/CD pipeline security is no longer optional for teams shipping weekly, daily, or multiple times a day. Your pipeline now touches source code, build logic, cloud access, secrets, deployment workflows, and release evidence. If that path is weak, attackers do not need to break production first. They can compromise the release process itself.
A strong CI/CD pipeline security checklist helps you secure secrets, enforce meaningful scans, and add approval and integrity checks before code reaches production. For most teams, the fastest improvements come from replacing long-lived credentials, scanning earlier in the software lifecycle, and making every production release signed, traceable, and auditable.
For DevSecOps leaders, platform teams, and CTOs, this is the practical goal: make secure delivery the default, not a special project that only appears before an audit.
What CI/CD Pipeline Security Actually Covers
CI/CD pipeline security is the discipline of protecting the full path from commit to deployment. That includes your source repository, build runners, package retrieval, secrets handling, artifact storage, approval workflows, signing, provenance, and deployment permissions.
This is bigger than “running a scanner in CI.” It is the security model for the delivery system itself.
In practice, a secure pipeline should answer a few basic questions at every stage.
Who or what is allowed to run this step?
What was scanned, and when?
Which artifact is being promoted?
Was it signed and approved?
Can you prove what was released and by whom?
Those questions matter whether you use GitHub Actions, GitLab CI/CD, Jenkins, self-hosted runners, or Kubernetes-based build environments.
Why Secrets, Scans, and Approvals Matter Most
Not every control has the same impact. In most real environments, the biggest wins come from three areas: secrets, scans, and approvals.
Secrets
Pipelines often hold powerful access to cloud platforms, registries, production environments, and internal systems. A leaked token or hard-coded key can let an attacker modify releases, access data, or move laterally into infrastructure.
Scans
If security checks only happen at the end of the pipeline, teams miss issues earlier when fixes are cheaper and clearer. Modern pipelines need layered coverage across source code, dependencies, secrets, containers, and infrastructure as code.
Approvals and release integrity
Even good scanning is not enough if weak approval logic allows unreviewed changes into production. Signed artifacts, approval gates, and auditable release evidence help teams prove that software came from a trusted build path.
Together, these controls reduce the most common high-impact failure modes in software delivery: stolen credentials, vulnerable components, and unauthorized promotion.
Core CI/CD Pipeline Security Risks to Address First
The quickest way to reduce pipeline risk is to focus on the controls that shrink blast radius immediately.
Exposed secrets and long-lived credentials
Static cloud keys, personal access tokens, shared deploy accounts, and secrets stored too broadly are still common. They are also one of the easiest ways for attackers to turn a small foothold into full release compromise.
Over-privileged runners and deployment roles
Many pipelines can do far more than they should. A build runner that can also deploy to production, change infrastructure, and access multiple registries creates avoidable risk.
Incomplete scan coverage
Running only SAST or only dependency scanning leaves gaps. Secure delivery needs broader coverage across code, dependencies, containers, and IaC.
Weak flow control
A release process without protected environments, branch protections, approval rules, and clear separation of duties is easier to bypass under pressure.
Unsigned artifacts and poor traceability
If teams cannot verify what was built, how it was built, and who approved it, incident response and compliance become much harder.
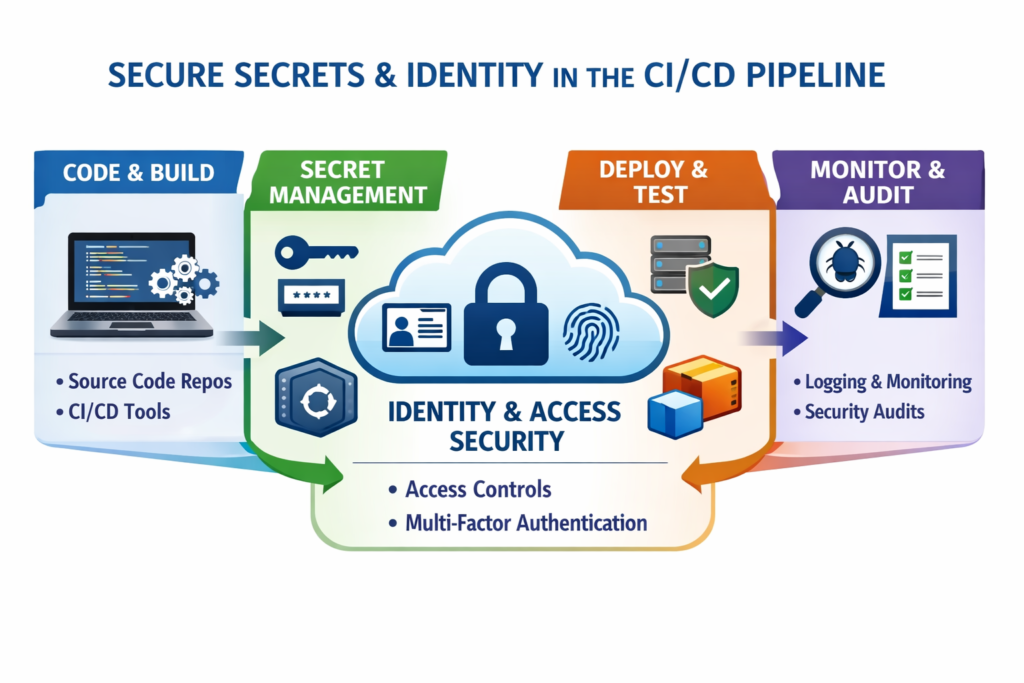
CI/CD Security Checklist for Secrets, Identity, and Access
Secrets management is often the highest-return place to start.
Replace static credentials with short-lived access
Move away from long-lived cloud keys and stored tokens wherever possible. Use workload identity, OIDC federation, or vault-backed dynamic credentials so each pipeline job gets short-lived access tied to the workload and context.
This improves both security and traceability. It also makes revocation easier when a job, branch, environment, or integration changes.
Enforce least privilege everywhere
Apply least privilege to.
Build runners
Repositories
Deployment roles
Cloud permissions
Kubernetes service accounts
Environment access
Build jobs should build. Deploy jobs should deploy. Avoid broad admin permissions just because they are convenient at the start.
For multi-team environments in the U.S., UK, Germany, or wider EU, this becomes even more important because shared platforms can quietly create cross-team exposure.
Add secret scanning and rotation
Secret scanning should run on pull requests, default branches, and key repositories. Rotation should be automated where possible and triggered immediately after exposure, team changes, or suspected compromise.
Break-glass access should be rare, time-bound, logged, and reviewed afterward. In practice, this is one of the clearest ways to separate mature pipeline security from ad hoc operations.
Shift-Left Security Controls That Belong in Every Pipeline
Shift-left security works when teams make secure defaults automatic, not when they pile on random late-stage blockers.
Run checks early in pull requests
At minimum, most teams should run these early.
SAST for source issues
SCA for dependency risk
Secret detection for accidental exposure
Basic policy checks for unsafe changes
Running checks close to the pull request gives developers better context and reduces expensive surprises later.
Scan containers and IaC before promotion
For cloud-native teams, container images and infrastructure definitions are part of the release surface. Scan them before staging or production promotion, not after deployment.
This matters even more in Kubernetes-heavy organizations, where image trust, manifest quality, and cluster configuration all affect release safety.
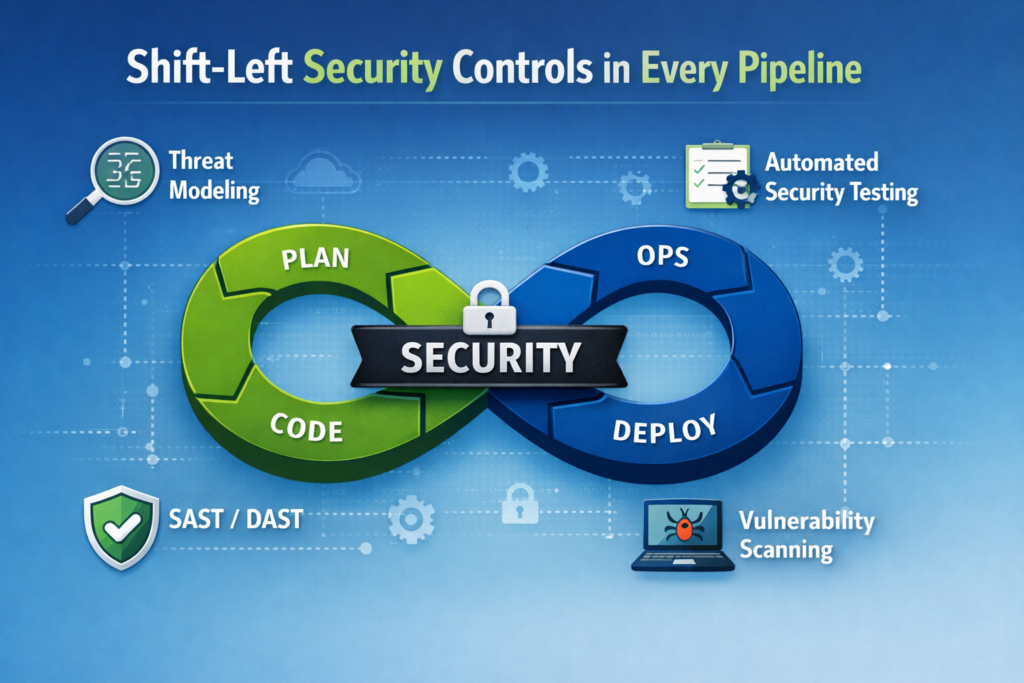
Standardize decisions with policy as code
Policy as code helps platform teams avoid inconsistent release rules across products and regions. Instead of arguing about which repos need which checks, encode the rules once for.
Required scans
Protected branches
Environment approvals
Artifact signing
Provenance requirements
Exception handling
That keeps security more consistent without turning every release into a custom debate.
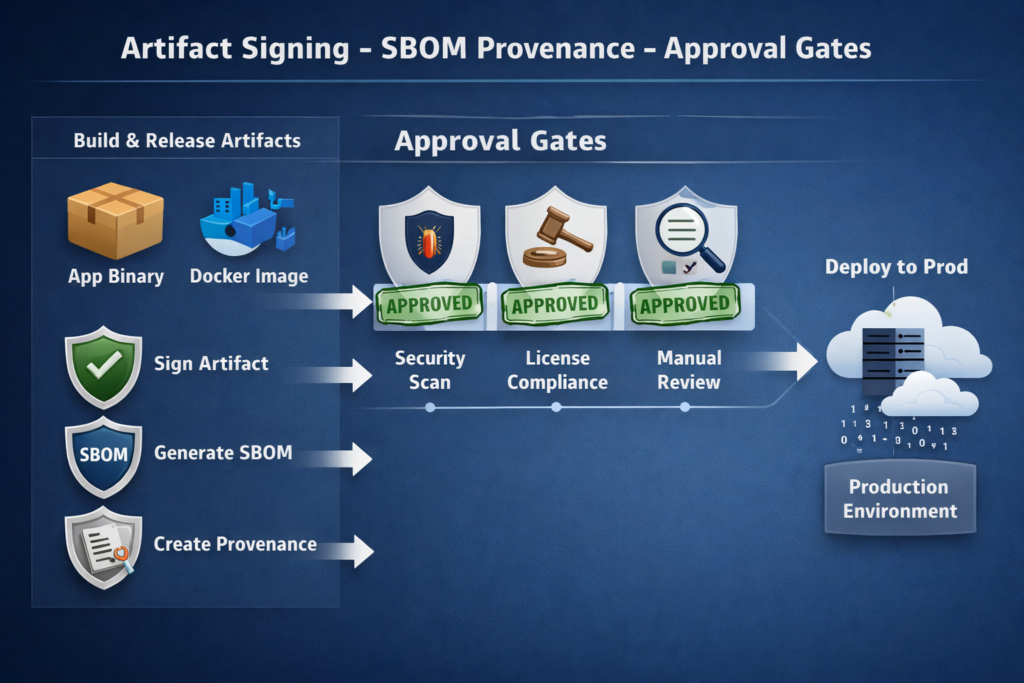
Approval Gates, Artifact Integrity, and Supply Chain Assurance
Approval gates are useful, but only when they are placed thoughtfully. The goal is not to slow every deployment. It is to control the moments that carry the highest business or compliance risk.
Where approvals add value
Use approvals at high-risk transitions such as.
Production deployments
Privileged environment changes
Emergency hotfixes
Regulated releases
Changes affecting payment, healthcare, or sensitive data workflows
A fintech team in London may need a second reviewer for production payment logic. A healthcare supplier in the U.S. or UK may need clearer release evidence tied to compliance expectations. The principle is the same: apply human review where the cost of error is high.
Why SBOMs, signing, and provenance matter
SBOMs show what is inside the release. Signing helps verify who produced or approved it. Provenance helps demonstrate how it was built.
Together, they strengthen software supply chain security and give teams better answers during.
Security incidents
Enterprise customer reviews
Procurement due diligence
Internal audits
Regulated change reviews
Many teams delay these controls because they sound advanced. In practice, starting with basic SBOM generation and production artifact signing is already a meaningful step forward.
Use NIST SSDF and SLSA as practical anchors
NIST SSDF gives organizations a broad framework for secure software development. SLSA goes deeper into build integrity and provenance. Used together, they help teams move beyond “we ran some scans” toward “we can show this release came from a trusted and policy-controlled system.”
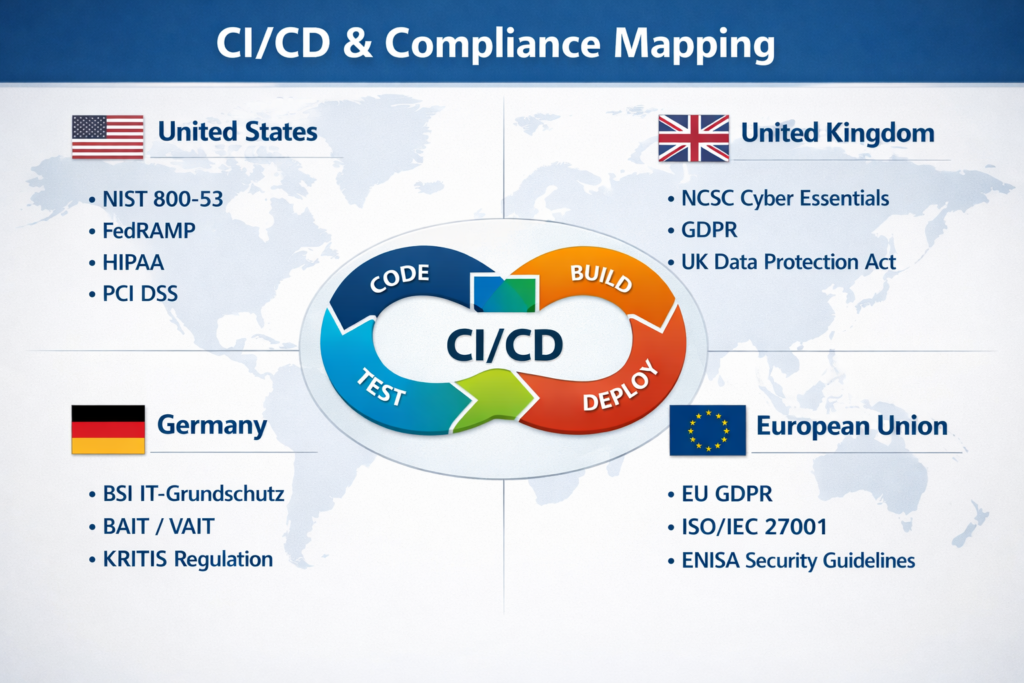
CI/CD Pipeline Security in U.S., UK, Germany, and EU Contexts
Compliance should not replace engineering judgment, but it should help shape priorities.
U.S.
For U.S. teams, pipeline controls often support SOC 2, HIPAA, PCI DSS, and broader secure development expectations. Auditors and customers usually care about controlled access, separation of duties, change approval records, vulnerability management, and release evidence.
UK
For UK organizations, pipeline logging, approval history, and access control support accountability under UK GDPR and sector-specific expectations. NHS suppliers and fintech teams may face stronger evidence requirements around changes, identity, and operational governance.
Germany and wider EU
In Germany and across the EU, GDPR and regulated-sector oversight raise the importance of audit trails, least privilege, data handling, and supplier accountability. For firms in Berlin, Frankfurt, Amsterdam, Dublin, or Munich, CI/CD pipeline security often becomes part of a broader cloud governance and risk discussion.
The core controls stay largely the same across regions. What changes is how teams map those controls to evidence and governance requirements.
How to Operationalize CI/CD Pipeline Security Without Slowing Delivery
Security at scale works best when it feels like a paved road.
Start with a maturity baseline
Review your current state across.
Secrets
Identity and access
Scan coverage
Approval gates
Artifact integrity
Logging and evidence
Exception handling
This gives you a practical baseline before buying more tools or writing more policies.
Separate quick wins from advanced controls
Quick wins usually include.
OIDC or vault-backed access
Protected branches
Required pull request scans
Environment approvals
Secret rotation
Advanced controls often include
Signed artifacts
Provenance attestations
Centralized policy as code
Workload-identity-based deployments
Stronger supply chain evidence
That sequencing matters. Teams get more value by fixing obvious identity and approval gaps first than by chasing mature supply chain controls while still storing long-lived production keys in CI.
Measure what matters
Track metrics that show whether the pipeline is becoming safer and easier to manage.
Number of long-lived secrets removed
Failed gate rate
Exception age
Mean time to remediate findings
Unsigned artifact rate
Production override frequency
From a small business point of view, better evidence is often just as important as better tooling. It makes audits, customer reviews, and incident response much less painful.
10-Point CI/CD Pipeline Security Checklist
Remove long-lived cloud keys from CI/CD.
Use OIDC or vault-backed short-lived credentials.
Enforce least privilege for runners and deployment roles.
Run SAST, SCA, and secret scanning on pull requests.
Scan containers and IaC before promotion.
Protect production environments with approvals.
Generate SBOMs for release artifacts.
Sign artifacts and verify signatures before deployment.
Store auditable logs for exceptions and releases.
Review controls against NIST SSDF, SLSA, and your compliance scope.
Final Take
A strong CI/CD pipeline security checklist helps teams ship faster without losing control of secrets, approvals, and release integrity. When you replace long-lived credentials, enforce least privilege, and run security checks early, you reduce both risk and last-minute release friction. For most organizations, the real win is not adding more tools, but creating a delivery process that is secure by default and easy for teams to follow every day.
As software supply chain threats keep growing, release security needs to be treated as part of core engineering quality. Signed artifacts, SBOMs, provenance, and auditable approvals are no longer optional for serious teams. The best approach is to start with practical controls, standardize them across pipelines, and improve maturity over time without slowing delivery.( Click Here’s )
Key Takeaways
A practical CI/CD pipeline security checklist is about protecting the delivery system, not just scanning application code. The strongest starting controls are short-lived credentials, least privilege, early scanning, approval gates, and verified release artifacts.
For teams across the U.S., UK, Germany, and the EU, the same foundation works across very different compliance environments. What changes is the evidence you need to show. The best results usually come when platform teams make those controls reusable, consistent, and hard to bypass.
If your team wants safer releases without turning deployment into a bottleneck, start by baselining secrets, scans, approvals, and artifact integrity. That creates a practical roadmap for stronger DevSecOps without slowing the business.
FAQs
Q : What is the difference between DevSecOps and CI/CD pipeline security?
A : DevSecOps is the broader operating model that brings development, security, and operations together across the software lifecycle. CI/CD pipeline security is the specific discipline focused on securing the path from commit to production, including secrets, identities, scans, approvals, signing, provenance, and release evidence.
Q : How often should teams rotate CI/CD pipeline secrets?
A : The stronger approach is to replace static secrets with short-lived credentials wherever possible. For any remaining static secrets, rotation should be automated and risk-based, with immediate rotation after exposure, personnel changes, or suspected compromise.
Q : Which CI/CD security controls matter most for SOC 2 audits?
A : The biggest controls are usually least-privilege access, separation of duties, protected branches, change approval records, vulnerability management, log retention, and evidence that production releases follow a controlled process.
Q : Do small SaaS teams need SBOMs and artifact signing?
A : Yes, but they can start small. Generating SBOMs for release artifacts and signing production images or packages gives smaller teams better incident visibility and prepares them for enterprise customer scrutiny later.
Q : How can platform teams add security checks without slowing deployments?
A : Place fast checks in pull requests, keep higher-assurance controls for trusted builds or promotion stages, and use reusable templates plus policy as code so developers inherit secure defaults automatically.


