Cloud Disaster Recovery GCC: Practical DR That Works
Cloud Disaster Recovery GCC: Practical DR That Works
Cloud Disaster Recovery GCC: Practical DR That Works
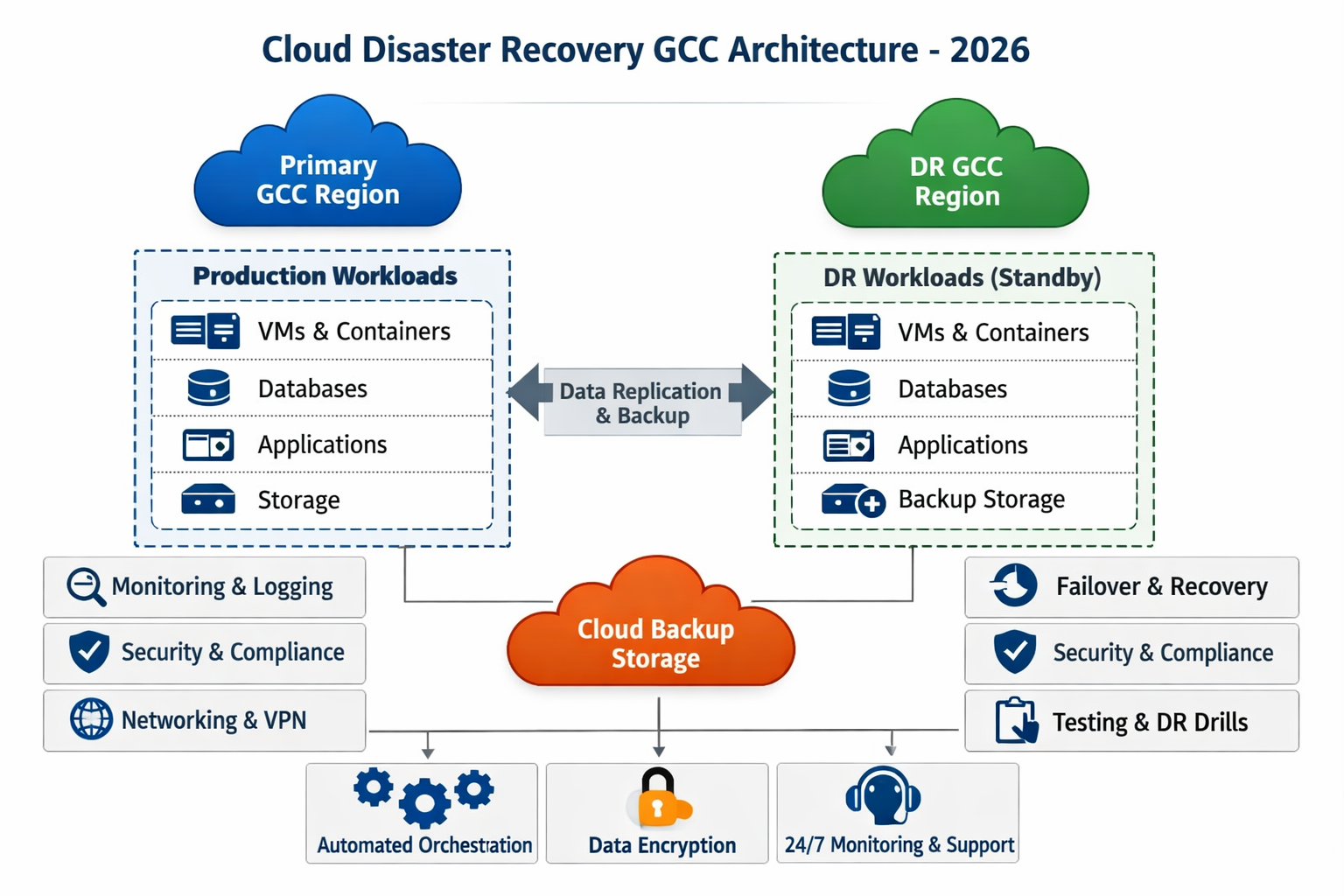
Cloud disaster recovery in the GCC means running backups, replicas and failover environments across compliant cloud and data center regions so your critical systems keep working during outages, cyber-attacks or regional disruptions. For leaders in Saudi Arabia, the UAE and Qatar, a practical cloud disaster recovery GCC strategy combines in-country or GCC-region hosting, tested RPO/RTO targets, and multi-region designs that align with key regulators such as SAMA, TDRA and QCB.
Introduction
Over the last few years, CIOs in Riyadh, Dubai and Doha have all felt the same jolt: a major cloud region slowdown, a data center power incident, or a telecom cut that suddenly made “we’ll fail over later” sound very naive. For many boards, cloud disaster recovery GCC has moved from a line item in the IT budget to a core business risk.
The pressure points are familiar: strict data residency rules, increasingly detailed regulatory expectations, growing dependence on SaaS, and the simple fact that a single cloud region no matter how modern—can suffer outages or even geopolitical disruption. In this guide, we’ll look at what cloud DR actually means, how GCC regulations shape your options, which architectures work in practice, how DRaaS providers compare, and a 90-day roadmap you can realistically execute.
What Is Cloud Disaster Recovery for GCC Companies?
Cloud disaster recovery is the set of processes and cloud architectures that let you restore or fail over your applications and data when your primary site fails without losing critical transactions or days of productivity. For GCC companies, cloud disaster recovery GCC usually means using in-country, GCC-region or carefully selected foreign regions to keep services available while respecting Saudi, UAE and Qatar data laws.
From Traditional DR Sites to Cloud DRaaS in the GCC
Ten years ago, disaster recovery in Saudi Arabia or the United Arab Emirates often meant a secondary data center in Riyadh, Jeddah, Dubai or Abu Dhabi, with duplicated hardware sitting idle until something broke. Today, DRaaS providers and hyperscalers let you replicate VMs, databases and storage to on-demand infrastructure, paying mainly for storage until a failover test or real incident.
For GCC firms, that shift unlocks faster recovery, easier testing and access to resilient regional footprints such as AWS Bahrain, Azure UAE Central and GCP’s Doha region. Combined with regional partners like Mak It Solutions, you can design DR patterns that match both latency expectations and local regulators.
Key BCDR Terms: RPO, RTO and SLAs for GCC Workloads
In business language, RPO is “how much recent data can we afford to lose?” while RTO is “how long can this service be down before we hurt customers or regulators notice?”. Banking and fintech platforms often target near-zero RPO and RTO measured in minutes; government portals and smart city platforms might accept under one hour; mid-market enterprises may live with a few hours.
Your SLAs with providers should clearly state these numbers, plus test frequency, notification timelines and penalties if your DRaaS partner fails to meet them. For GCC entities, it’s also worth confirming how those SLAs map to SAMA, TDRA, QCB, NDMO and sector-specific requirements.
Why Single-Region Cloud Is Not Real Disaster Recovery
If all your production and “DR” workloads sit in a single cloud region, you don’t really have disaster recovery—you have high availability. A full region outage, a long-running control plane incident, a cable cut or a sudden legal restriction can still take everything down at once. Recent global incidents have shown entire regions of major providers going offline for hours.
In the GCC context, cloud disaster recovery GCC must plan for region-wide failures and keep at least one truly independent region or provider able to serve your critical users. That usually means a second GCC region, a sovereign cloud, or a carefully governed foreign region as an additional safety net.
GCC Regulations Driving Cloud Disaster Recovery
GCC data residency and privacy laws define where you can host backups and DR environments, not just production workloads. In practice, this means classifying data and systems, then deciding which can live in sovereign cloud data centers in Saudi, UAE or Qatar, and which can safely use European or other regions with strong contractual and technical safeguards.
SAMA, NDMO and In-Kingdom DR Expectations in Saudi Arabia
For Saudi banks and fintechs, the Saudi Central Bank (SAMA) cyber and cloud rules expect robust business continuity and disaster recovery, including tested DR plans, clear RPO/RTO and strict oversight of cloud outsourcing.The National Data Management Office (NDMO) drives data classification and residency, pushing “in-kingdom” or GCC-region DR for sensitive datasets.
In practice, that often means pairing a Riyadh primary site with a secondary in another Saudi region or in a GCC neighbor where data localization rules and supervisory arrangements still feel acceptable to auditors.
TDRA, National Cloud Policy and DR in the UAE
In the UAE, the Telecommunications and Digital Government Regulatory Authority (TDRA) operates FedNet DRaaS and promotes sovereign cloud offerings for federal and local entities, with built-in failover to remote sites. The National Cloud Security Policy sets expectations for resilience, cyber controls and vendor governance across public and private sectors. (UAE Legislation)
For UAE-based businesses, cloud disaster recovery GCC planning usually starts with sovereign or local hyperscaler regions (Dubai, Abu Dhabi), then carefully chosen EU or other regions for less sensitive DR replicas. Data classification is the foundation: mission-critical citizen data, regulated financial data and national security workloads generally stay in-country.
QCB, PDPPL and DR Requirements in Qatar
For Qatari banks and payment providers, the Qatar Central Bank (QCB) Cloud Computing Regulation and technology risk instructions require clear cloud strategies, approved outsourcing models and resilient DR sites, with data center locations explicitly reviewed by QCB. (Qatar Chamber of Commerce) Qatar’s Personal Data Privacy Protection Law (PDPPL) expects secure, encrypted, geographically redundant backups and regularly tested DR plans for personal data.
Together, these push Doha-based institutions to use in-country or close GCC sovereign/cloud regions for DR rather than far-flung locations especially when dealing with payments, identity systems or large volumes of citizen data.
Note
This article is for information only and does not constitute legal or regulatory advice. Always confirm your DR approach with your compliance, risk and legal teams.
Cloud DR Architectures That Actually Work in the GCC
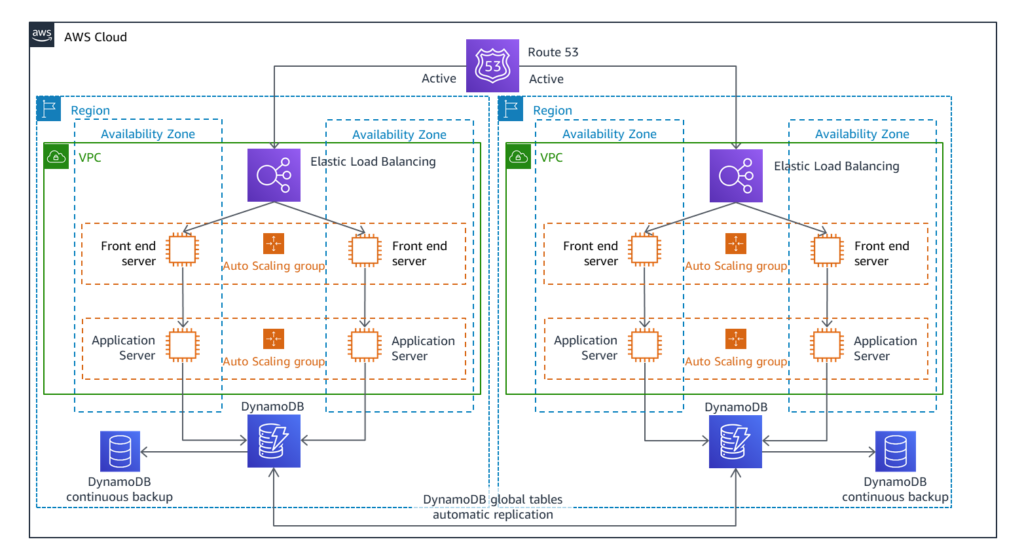
Active-Passive vs Active-Active DR Across GCC Regions
In active-passive patterns, your primary region (for example Dubai or Riyadh) handles all traffic while a secondary in Abu Dhabi, Bahrain or Doha stands ready for failover. Active-active runs live traffic in two regions say Riyadh↔Dubai or Doha↔Abu Dhabi. 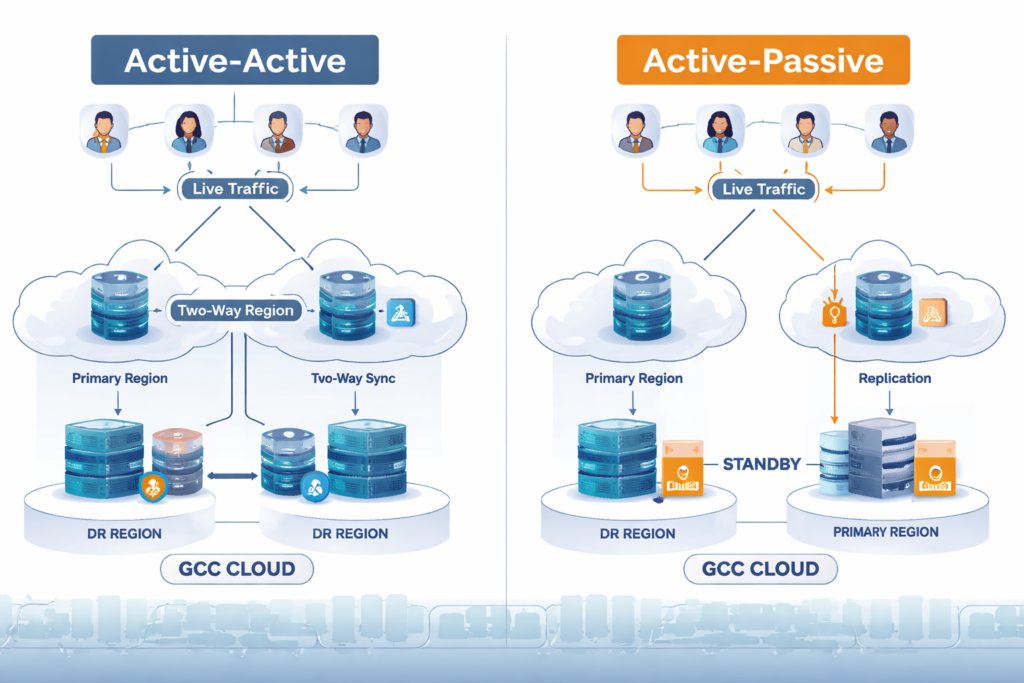
offering better RPO/RTO but higher cost and complexity.
For latency-sensitive fintech and smart-city workloads, active-active across nearby GCC regions is attractive. For internal ERP or logistics systems, a well-tuned active-passive DRaaS setup can be more than enough, especially when budgets are tight but regulators still expect robust DR.
Multi-Region DR on AWS, Azure and Local Sovereign Clouds
Many GCC teams combine AWS Bahrain, Azure UAE Central and GCP Doha with national sovereign clouds run in partnership with regulators or telcos. (Mak It Solutions) A Saudi bank might keep primary workloads on a sovereign or in-kingdom cloud, with encrypted replicas in AWS Bahrain; a Dubai ecommerce brand could run in Azure UAE with DR copies in a local DRaaS provider’s data center.
The key is mapping each dataset to an allowed geography, then choosing regions accordingly. When in doubt, start with data classification and regulatory obligations, then design network paths, identity integration and monitoring around that map.
Cross-Cloud and Hybrid DR for Critical National Systems
Critical national systems national IDs, open banking APIs, real-time payment rails—often require cross-cloud DR: on-prem or sovereign for the “source of truth”, a hyperscaler for scale and analytics, and a second cloud for true diversification. For example, a platform regulated by ADGM or DIFC might run core services in a UAE sovereign cloud, analytics in a hyperscaler, and maintain a warm standby in another GCC country.
For this class of workload, cloud disaster recovery GCC becomes a national resilience question, not just a technical architecture. Expect more direct regulator involvement, deeper testing obligations and closer scrutiny of cross-border data flows.
Comparing DRaaS and Cloud DR Providers in the GCC
Local DRaaS in Saudi Arabia (Riyadh, Jeddah)
In Saudi, DRaaS providers around Riyadh and Jeddah such as DETASAD, SITE or Skyline—typically offer in-kingdom data centers, MPLS or SD-WAN connectivity to major business hubs, and managed runbooks aligned with SAMA and NCA expectations. These can pair well with hyperscaler regions, giving you local failover plus a secondary cloud copy for extreme scenarios.
When evaluating, ask for reference architectures for similar Saudi clients, clarity on in-kingdom vs out-of-kingdom components, and how they handle joint drills with your internal teams.
UAE Sovereign Cloud DR and DRaaS (Dubai, Abu Dhabi)
In the UAE, providers like CloudHPT, EBM and BYO Services run DRaaS on top of sovereign or local cloud infrastructure in Dubai and Abu Dhabi. They position around TDRA-aligned controls, FedNet integration for government and strong bilingual support. For a UAE TDRA-approved cloud disaster recovery service, look for evidence of past government projects and clear mappings to the National Cloud Security Policy.
Also confirm how they support mixed estates: for example, combining on-prem workloads in Dubai Internet City with Azure UAE and a sovereign cloud tenant.
Qatar and Wider GCC: Managed Cloud DR Portfolios
In Doha, providers such as GBM Qatar and QHost offer managed cloud backup and disaster recovery tailored to QCB and PDPPL demands, often paired with GCP Doha or regional clouds. Many of these firms extend portfolios across Kuwait, Bahrain and Oman so you can cover multiple GCC countries with a single DRaaS contract, unified SLA and shared monitoring.
If you operate across Saudi, UAE and Qatar, this “regional portfolio” model can simplify procurement provided the provider can prove they treat each country’s localization rules separately and correctly.

Industry-Specific Cloud DR Use Cases in the GCC
Banking, Fintech and Capital Markets
Banks, fintechs and capital markets platforms must align DR with SAMA, QCB, ADGM and DIFC rules, where regulators increasingly expect near-real-time replication and rapid failover for payment and trading systems. Open banking APIs and instant payments often need RPO measured in seconds and RTO in minutes.
For this sector, cloud disaster recovery GCC strategies usually combine sovereign clouds, hardened hyperscaler regions and frequent DR tests observed by internal audit—and sometimes by regulators themselves.
Government, Smart Cities and National Digital IDs
Gulf governments run e-government portals, smart city platforms and digital identity systems that citizens rely on every day. DR here is about citizen trust: outages during major events can quickly become front-page news. Best practice is bilingual (Arabic/English) DR documentation, regular drills across ministries, and diversified hosting across in-country regions such as Riyadh, Dubai, Abu Dhabi and Doha with clear escalation paths to senior officials.
For large GCC smart-city programs, consider including DR drills in wider crisis simulations so business and technical teams rehearse together.
Healthcare, Oil & Gas and Large Enterprises
Hospitals in Abu Dhabi, Doha or Jeddah need DR that covers clinical systems and imaging, often with local storage plus encrypted replicas to compliant cloud regions. Oil & gas and logistics enterprises spread across Saudi, UAE and Qatar must protect SCADA/OT and ERP workloads, often using a mix of on-prem, edge and cloud DR.
Here, DRaaS with OT-aware partners and strong RPO/RTO for operational systems can literally keep production lines and field operations running. That usually means tighter integration with SOCs, OT security teams and on-site engineers than in pure IT environments.
Cost, ROI and Buying Checklist for Cloud Disaster Recovery in the GCC
DRaaS vs Building Your Own DR Site
Building your own second data center means heavy CAPEX on land, power, cooling and hardware, plus ongoing operations teams. DRaaS spreads those costs across many customers, turning disaster recovery into an OPEX subscription tied to actual protected workloads.
For many GCC SMB and mid-market teams, DRaaS unlocks enterprise-grade business continuity and disaster recovery (BCDR) planning they could never justify alone. When you present this to the board, frame DRaaS as insurance against regulatory penalties, reputational damage and lost revenue—not just a “nice-to-have” IT expense.
What Impacts DRaaS Pricing in the GCC?
DRaaS pricing is usually driven by:
Protected TBs and storage tier
VM or container counts
Chosen RPO/RTO targets
Test frequency and scope
Connectivity options (VPN, MPLS, SD-WAN)
Compliance add-ons such as dedicated links or sovereign cloud options
Saudi deployments may pay more for in-kingdom Tier III/IV facilities; UAE setups sometimes pay a premium for sovereign or FedNet-aligned environments; Qatar projects must factor in connectivity to Doha and any cross-border links. Expect to pay more for near-zero RPO and monthly DR drills, less for cold standby archives.
Due Diligence Checklist for GCC Cloud DR Providers
When shortlisting providers, make sure you can answer
Where exactly will backups and replicas live, and who are the subcontractors?
Which regulators (SAMA, TDRA, QCB, NDMO, sector regulators) have they already worked with?
What is their incident history and RTO/RPO performance for similar clients?
How often do they test DR with customers, and how do they report results?
Can they provide bilingual support and documentation?
Request sample DR runbooks, evidence of bilingual service desks and a clear SLA covering notification times, test support and penalties for missed targets.
Note
Any cost ranges in this article are illustrative only and not financial advice. Always build a detailed business case for your specific environment.
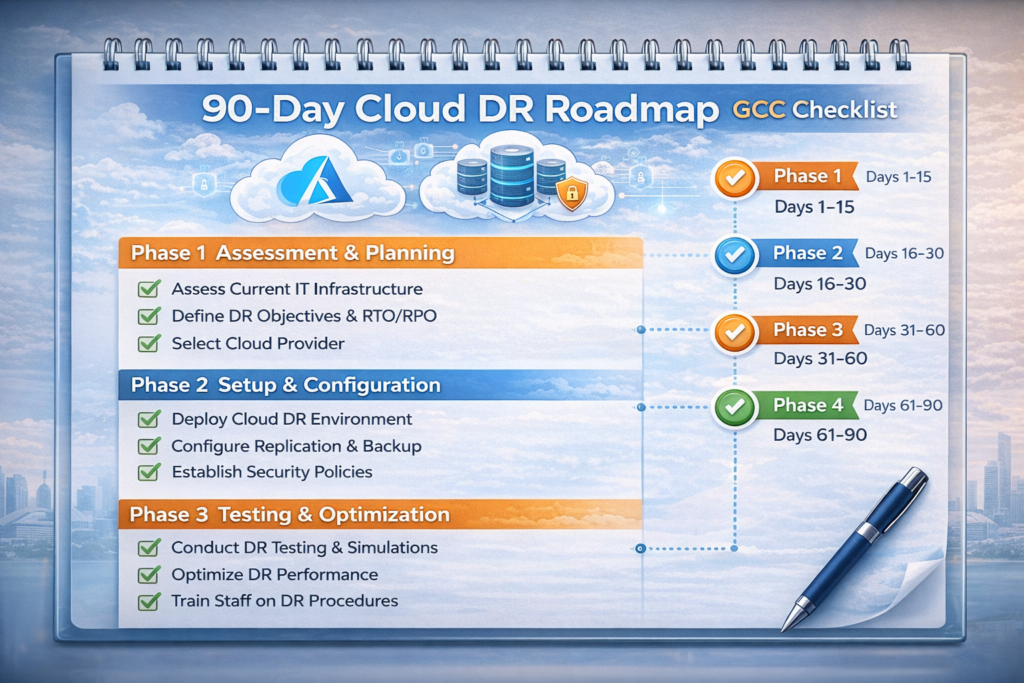
90-Day Roadmap to a Working Cloud DR Plan in the GCC
You don’t need a multi-year program to make real progress. A focused 90-day sprint can move you from “theoretical DR” to a tested, board-ready plan.
Assess, Classify and Align with Regulators
Inventory critical workloads and data across your Saudi, UAE and Qatar operations.
Map each to NDMO, SAMA, TDRA and QCB classifications: what must stay in-country, what can stay in the GCC, and what can sit in Europe or elsewhere.
Use this phase to agree RPO/RTO targets with business owners and to align with any existing data localization or cyber policies.
Capture current gaps versus regulatory expectations and internal risk appetite.
Design, Select Providers and Run a Pilot
Design your target architecture: active-active vs active-passive, single-cloud vs multi-cloud, sovereign vs hyperscaler.
Shortlist DRaaS and cloud providers that match your regulatory, latency and budget needs.
Run a pilot on one or two critical apps perhaps a Riyadh fintech platform or a Dubai ecommerce site—to validate failover, monitoring and runbooks.
Use pilot results to fine-tune network design, identity integration and incident runbooks.
Automate, Document and Run Full DR Tests
Automate as much of the failover/failback as possible, integrating with CI/CD, infrastructure-as-code and incident management tools.
Document bilingual DR playbooks, assign clear roles, and align with your broader crisis management plan.
Run full end-to-end DR tests involving business users in Riyadh, Dubai, Abu Dhabi and Doha.
Present results, gaps and next steps to your risk committee or board so DR becomes a living program, not a one-off exercise.
At the end of 90 days, you should have a living, tested cloud disaster recovery GCC plan, not just a PDF on a shelf.
Concluding Remarks
Cloud disaster recovery in the GCC is no longer about ticking a backup box; it’s about proving to boards and regulators that your services can survive outages, cyber-attacks and regional disruptions. When you align DR designs with data residency rules, choose resilient multi-region architectures and actually test them, compliance pressure turns into real resilience and competitive advantage.
If you want help translating regulations and cloud options into a concrete DR design, the team at Mak It Solutions has already worked on GCC-grade cloud, data residency and BCDR programs. Combine this guide with a focused assessment, and you can move from slideware to a working DR plan in the next quarter.
If you’re a CIO, CISO or founder in Saudi Arabia, the UAE or Qatar and your current DR plan feels theoretical, this is the right moment to fix it. Reach out to Mak It Solutions for a cloud disaster recovery GCC assessment, a multi-region architecture review, or a 90-day DRaaS pilot tailored to your regulators and latency needs. Together, you can align your DR strategy with SAMA, TDRA and QCB expectations without over-engineering or overspending.( Click Here’s )
FAQs
Q : Is it mandatory for Saudi banks to keep their disaster recovery sites inside Saudi Arabia or just within the GCC?
A : For Saudi banks and fintechs, SAMA’s cybersecurity and cloud guidelines expect very strong control over where regulated data is processed, stored and recovered, with a strong default bias toward in-kingdom hosting for critical workloads. In practice, that often means DR sites inside Saudi Arabia, or within tightly governed GCC arrangements that SAMA has explicitly reviewed and approved. Boards should assume regulators will ask for clear documentation of DR locations, data flows and encryption, and treat any non-Saudi DR region as an exception that needs strong justification and controls.
Q : Can UAE companies use European cloud regions for DR if production data is hosted in Dubai or Abu Dhabi?
A : Yes, many UAE companies use EU regions for secondary backups or cold DR environments, especially for less sensitive datasets, but they must follow TDRA and National Cloud Security Policy expectations. That usually means classifying data, keeping critical government or regulated records in UAE sovereign or local regions, and using Europe mainly for encrypted replicas with contractual safeguards and strong key management. For regulated entities, it is wise to consult your compliance team and, if needed, TDRA or sector regulators before relying heavily on non-UAE DR.
Q : What is a realistic DRaaS budget for a mid-size company in Riyadh or Dubai?
A : A typical mid-size company with a handful of mission-critical systems might spend the equivalent of a few thousand US dollars per month on DRaaS, depending on storage volume, VM counts and RPO/RTO targets. Costs rise when you require near-zero data loss, monthly DR drills or sovereign cloud options in Riyadh, Dubai or Abu Dhabi. When building a business case, compare this to the CAPEX and staffing of running your own secondary site, and remember that SAMA or TDRA non-compliance penalties or brand damage from downtime can be far more expensive than a well-designed DRaaS subscription.
Q : How often should Qatar government entities test their cloud disaster recovery plans?
A : While exact frequencies depend on local policy, most Qatar government and financial entities align with QCB and PDPPL expectations by running at least annual full DR tests, alongside more frequent component or tabletop exercises. The important thing is not just to prove that failover works once, but to validate that bilingual runbooks, contact lists and integrations are still accurate as systems evolve. For critical citizen services or payment platforms, semi-annual or quarterly tests, reported back to QCB or relevant authorities, are becoming a practical norm rather than a nice-to-have.
Q : Can one cloud DR solution cover multiple GCC countries (Saudi, UAE, Qatar) under a single contract and SLA?
A : Yes, many regional DRaaS providers now offer portfolios that cover Saudi Arabia, the UAE, Qatar and sometimes Kuwait, Bahrain and Oman under a single framework agreement. The key is ensuring the contract and SLA still respect each country’s local rules for example, SAMA expectations for Saudi banks, TDRA policies for UAE entities, and QCB cloud regulations for Doha-based institutions. A well-designed multi-country DR program will standardise tooling and monitoring while still allowing you to keep the most sensitive workloads inside each jurisdiction as required.


