Cloud Security Misconfigurations: Top Risks to Remediate
Cloud Security Misconfigurations: Top Risks to Remediate
Cloud Security Misconfigurations: Top Risks to Remediate
Cloud security misconfigurations are one of the fastest ways to turn a manageable cloud estate into a real business risk. In AWS, Azure, and Google Cloud, a single overly broad permission, public storage setting, or missing log source can expose sensitive data, weaken compliance posture, and slow down incident response.
The good news is that the highest-impact fixes are usually clear. Start with excessive IAM permissions, publicly accessible storage, weak network rules, missing encryption, and disabled logging. For teams operating in the USA, UK, Germany, and the wider EU, fixing those issues early reduces both breach risk and audit pressure.
Cloud misconfigurations matter because they are usually easier to exploit than advanced software flaws. Attackers do not need a complex zero-day when access is already wider than intended. For cloud security leaders, the question is not whether misconfigurations exist. It is which ones to fix first, how to prioritize them, and how to keep them from returning.
In practice, this becomes harder in hybrid and multi-cloud environments. IBM reported in 2024 that 40% of breaches involved data spread across multiple environments, while Flexera’s 2025 State of the Cloud reporting said organizations used an average of about 2.4 public cloud providers. IBM’s 2024 Cost of a Data Breach benchmark also put the global average breach cost at $4.88 million. Those numbers help explain why cloud posture is now a board-level conversation, not just an infrastructure issue.
What Are Cloud Security Misconfigurations?
Cloud security misconfigurations are incorrect, overly permissive, or poorly maintained cloud settings that expose resources more than intended. They can affect identities, storage, networking, encryption, logging, and platform services across AWS, Azure, and GCP.
A practical executive definition is this: a cloud misconfiguration is a preventable configuration error that expands attack surface, weakens control effectiveness, or creates compliance exposure. That framing keeps the conversation tied to business impact instead of cloud syntax.
They remain common for a simple reason. Cloud teams move fast, environments change constantly, and ownership is often split between platform engineering, DevSecOps, application teams, and compliance stakeholders. What starts as a temporary exception can quietly become a permanent risk.
It also helps to separate misconfigurations from other security problems:
Misconfiguration: a control failure in how a cloud resource is set up
Vulnerability: a flaw in software, code, or a component
Runtime threat: suspicious or malicious behavior during execution
Modern CNAPP tools may correlate all three, but remediation usually begins with getting the configuration right.
The Cloud Security Misconfigurations to Fix First
The most urgent cloud security misconfigurations usually share four traits: they are easy to discover, easy to exploit, tied to sensitive assets, and capable of causing broad blast radius.
The top priorities are.
Excessive IAM permissions
Publicly exposed storage buckets
Missing encryption for data at rest or in transit
Overly broad key access
Open management ports and weak network rules
Disabled or incomplete logging
Unmanaged internet-facing services
Default service accounts or inherited privileged roles
These are the issues that most often turn a simple cloud review into a material security finding.
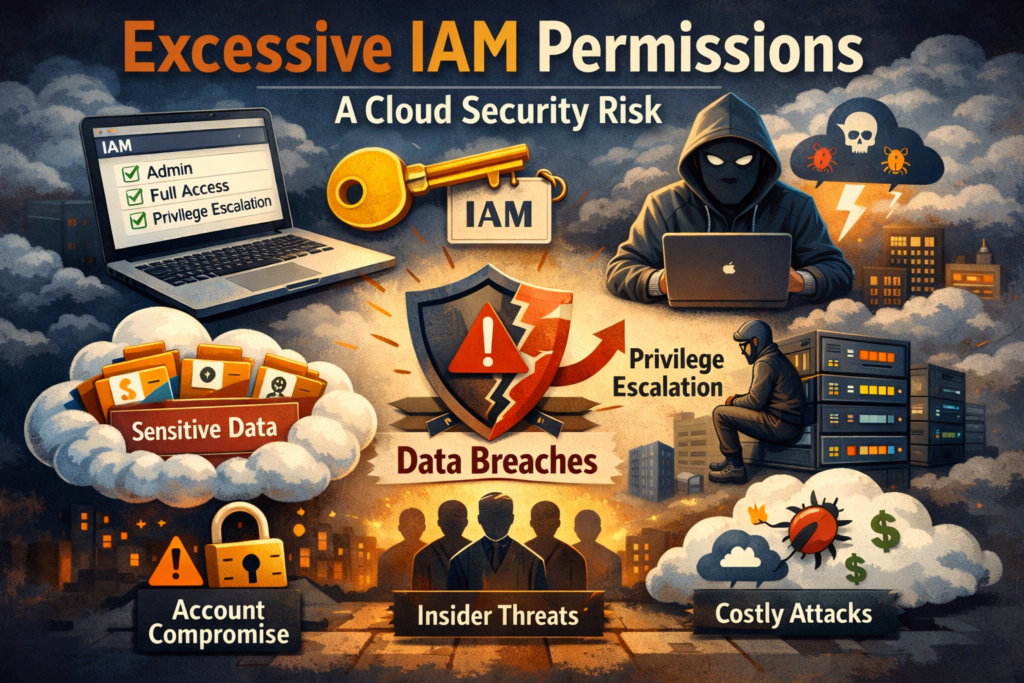
Identity and access mistakes
Identity misconfigurations usually deserve first place because they make every other problem worse. If an attacker gains access through phishing, leaked credentials, or a vulnerable workload, excessive permissions can turn that foothold into privilege escalation.
Common identity risks include.
Over-privileged IAM roles
Weak separation of duties
Dormant privileged accounts
Default service accounts left with unnecessary access
Broad project- or subscription-level rights
Federation or SSO gaps that create blind spots
In practice, least privilege is where many cloud programs drift. Teams grant broad access to move faster, then rarely remove it later.
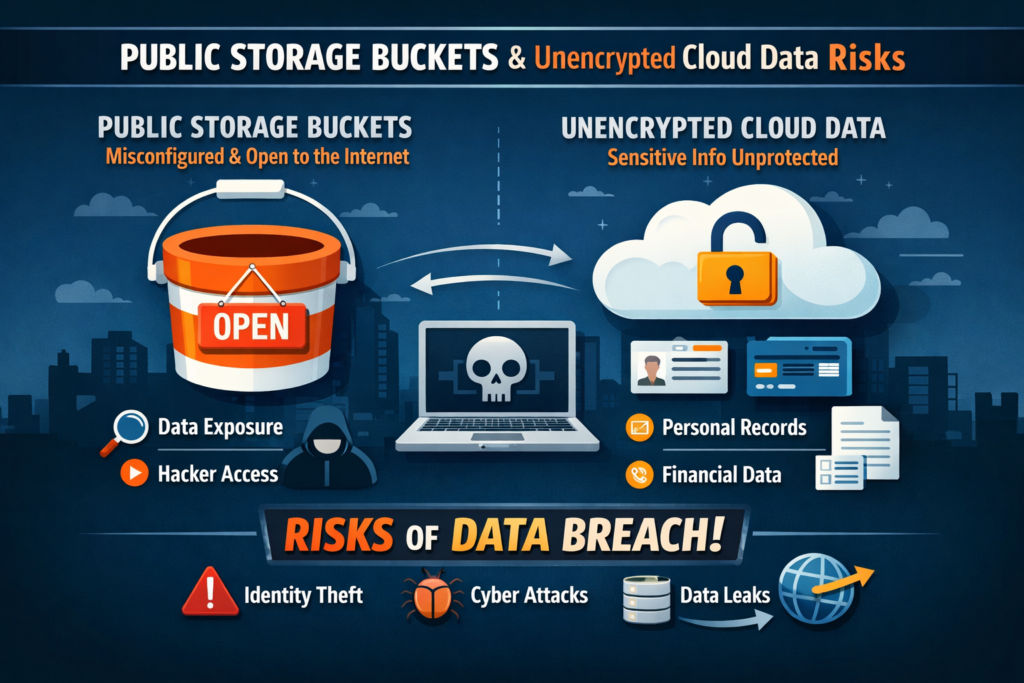
Data exposure issues
Publicly exposed storage remains one of the clearest examples of preventable cloud risk. A single misapplied bucket policy, container setting, or access rule can expose customer data, backups, logs, or internal files.
The biggest data exposure risks usually involve.
Public storage buckets or containers
Missing encryption controls
Weak KMS or key access policies
Sensitive data stored in the wrong region
Backups accessible to too many identities
For regulated teams, this is where security and compliance meet quickly. A storage issue is not just a technical flaw. It can become a reportable incident, an audit exception, or a contractual problem with enterprise customers.
Network and visibility gaps
Weak network rules and missing visibility often turn a manageable incident into a costly one. Open admin ports, permissive security groups, overly broad firewall rules, and disabled audit logs make containment harder and forensic evidence weaker.
The most common problems include.
Security groups or firewall rules open too broadly
SSH, RDP, or management interfaces exposed to the internet
Logging disabled in key services
Incomplete retention for audit evidence
Internet-facing assets not tracked by any owner
For SaaS businesses, fintech platforms, and regulated outsourcing environments, logging failures can create as much damage as the initial exposure itself.
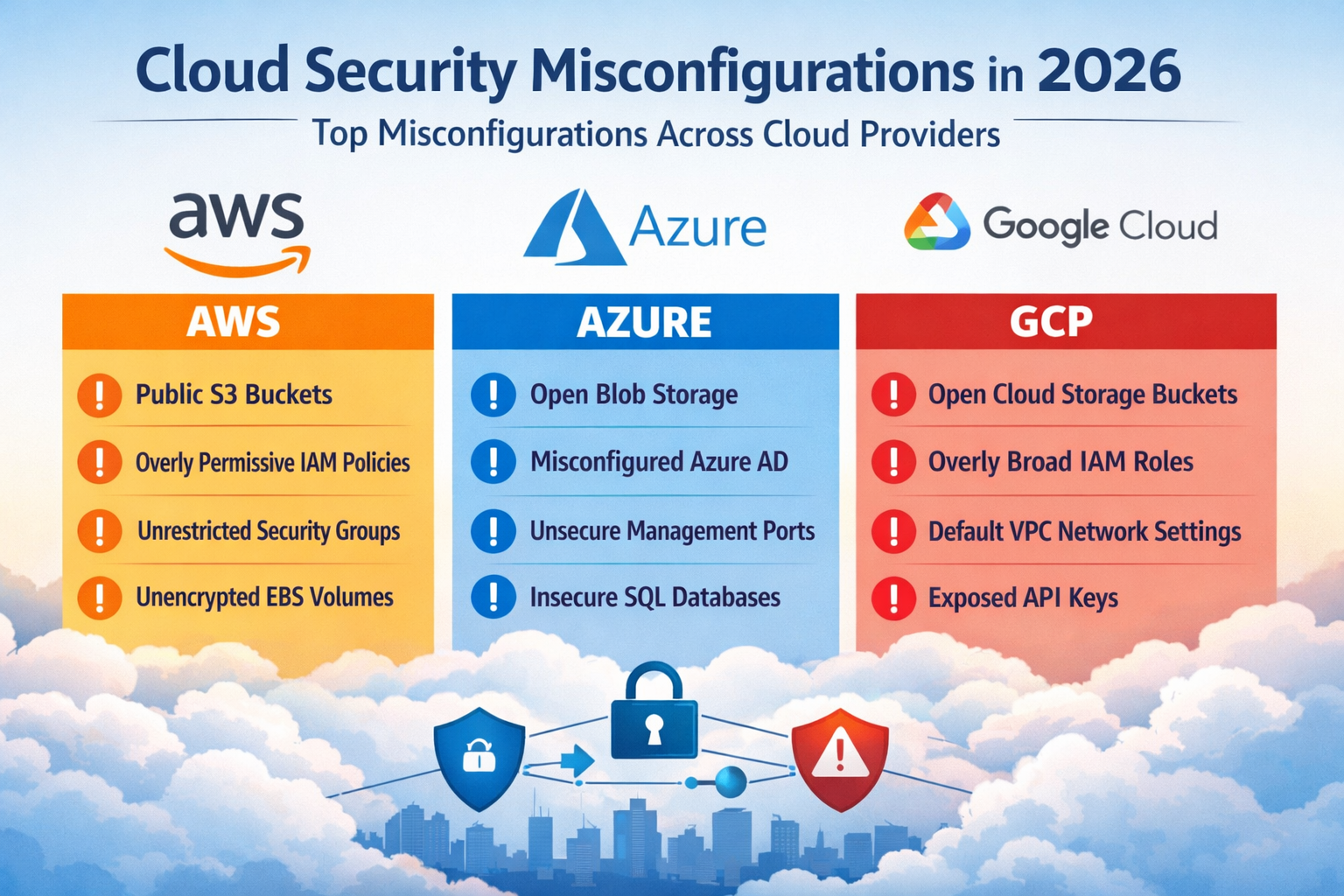
AWS, Azure, and GCP Misconfigurations Compared
Across AWS, Azure, and GCP, the patterns are familiar, but the way they appear is slightly different.
| Cloud Platform | Common Misconfigurations | Where Teams Usually Start |
|---|---|---|
| AWS | S3 exposure, IAM sprawl, security group drift | S3 public access controls, IAM review, org guardrails |
| Azure | RBAC sprawl, policy inconsistency, storage exposure | Role cleanup, policy enforcement, scope review |
| GCP | Default service accounts, broad project permissions, policy blind spots | Service account review, least privilege, project policy checks |
AWS misconfigurations
In AWS, exposed S3 buckets and sprawling IAM policies are still the classic issues. Security groups also drift over time, especially when ports are opened for testing or troubleshooting and never fully restricted again.
For many teams, the fastest AWS wins come from.
Enforcing S3 public access protections
Reviewing privileged IAM roles and cross-account access
Tightening security groups
Standardizing logging and encryption baselines
Applying organization-level guardrails
Azure misconfigurations
Azure environments often become risky through role assignment sprawl, inconsistent policy enforcement, and identity complexity across subscriptions, tenants, and hybrid Microsoft ecosystems.
Common Azure problems include.
RBAC assignments that outgrow original intent
Resource scopes that are too broad
Policy exceptions that are never revisited
Weak storage access controls
Inconsistent logging or monitoring across subscriptions
Azure’s flexibility is powerful, but only when role boundaries and governance remain clean.
GCP misconfigurations
In GCP, default service accounts and broad project permissions are frequent trouble spots. Teams sometimes assume defaults are safe enough, but responsibility still sits with the organization after those accounts are created.
Typical GCP risks include.
Default service accounts with unnecessary access
Project-level permissions that are too broad
Weak service account key management
Limited visibility into inherited access paths
Policy drift between projects and folders
For multi-project environments, identity review usually provides the highest-value first fix.
How to Prioritize Remediation
To prioritize cloud security misconfigurations well, focus on what is exposed, what is sensitive, what is exploitable, and what would hurt the business most if abused.
A practical order of operations looks like this.
Fix anything internet-exposed
Prioritize assets tied to sensitive data or production systems
Address issues with high blast radius, especially identity-related ones
Resolve gaps that weaken logging, evidence, or containment
Map remaining issues to regulatory and contractual obligations
This matters because alert volume alone is misleading. A public bucket with customer data should outrank dozens of low-risk development findings. A role with access to production secrets should outrank a minor test environment exception.
Tie fixes to business context
Risk only becomes useful when it is mapped to the business.
A US healthcare workload handling ePHI should prioritize access control, encryption, and audit logging.
A UK fintech environment supporting payments or Open Banking integrations should focus heavily on identity boundaries, evidence retention, and privileged access review.
A Germany-based regulated platform may need tighter data residency enforcement, cross-border admin controls, and stronger traceability for regulator-facing reviews.
From a small business point of view, this also prevents wasted effort. Teams do better when they fix the few issues that genuinely affect customers, revenue, and compliance outcomes first.
Build a real workflow
Cloud remediation works best with shared ownership.
Platform engineering owns landing zones, shared services, and guardrails
DevSecOps or cloud security owns detection logic, policy-as-code, and prioritization
Application teams fix workload-specific issues
Compliance or risk teams verify evidence and control mapping
That model is far more effective than sending tickets to security and hoping someone closes them.
When CSPM and CNAPP Actually Help
CSPM and CNAPP tools become valuable when cloud complexity grows faster than manual review can handle.
What CSPM does well
CSPM is mainly about posture management. It helps teams.
Detect risky configurations continuously
Check alignment against policy and compliance requirements
Spot drift from secure baselines
Centralize findings across cloud accounts and subscriptions
Export evidence for audits and internal reviews
It is especially useful when native cloud controls already exist, but enforcement is inconsistent.
Where CNAPP adds more value
CNAPP goes further by combining posture with broader context. It can connect.
A misconfigured identity
An exposed workload
A vulnerable package
Runtime behavior
A possible attack path
That correlation matters in multi-cloud environments where isolated findings create noise. Instead of seeing separate alerts, teams see which chain of issues actually matters.
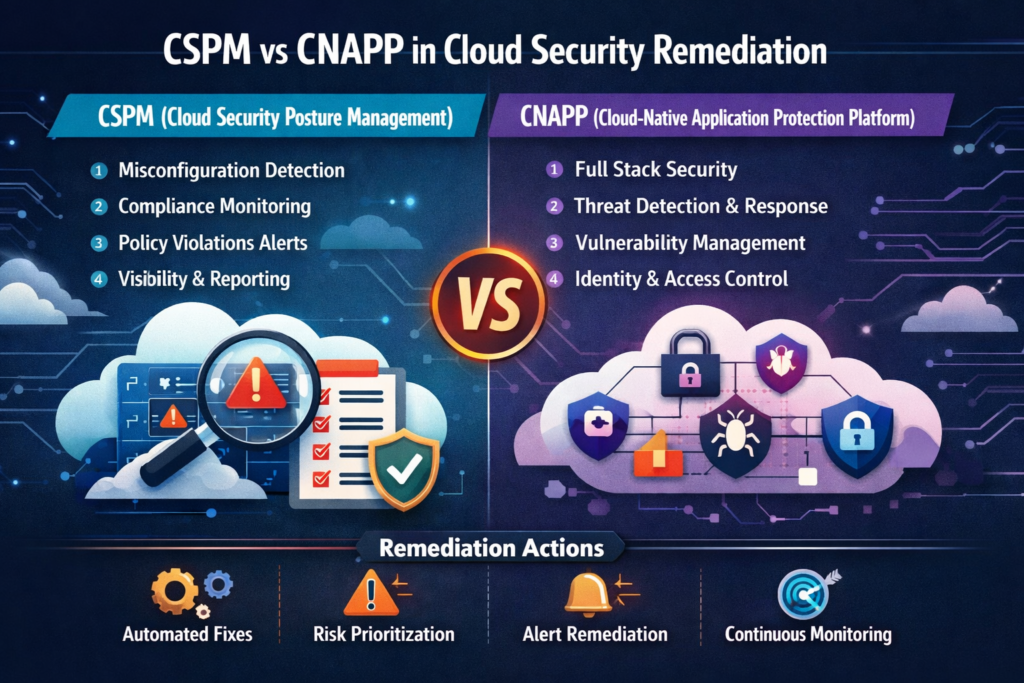
What to evaluate in tools
When comparing CSPM or CNAPP options, look for.
Strong AWS, Azure, and GCP policy coverage
Support for automation and remediation workflows
Evidence export for frameworks like PCI DSS and SOC 2
Clear ownership mapping
Context that explains why a finding matters
A platform that generates 5,000 findings but cannot tell you which 20 need action first is not helping enough.
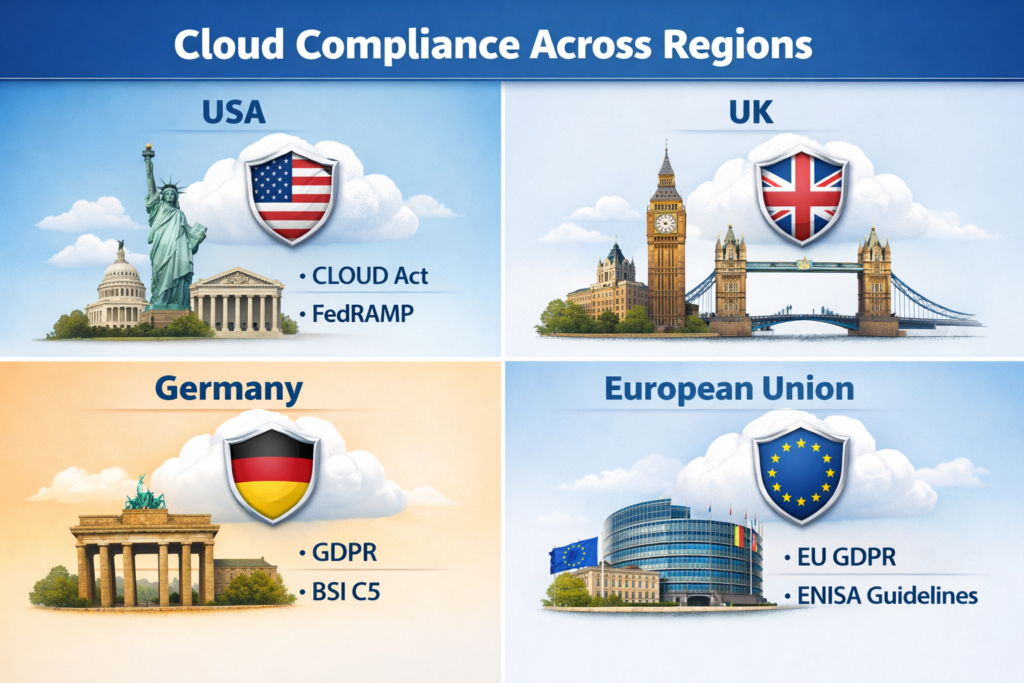
Compliance-Driven Cloud Security Fixes for USA, UK, Germany, and EU Teams
The cloud misconfigurations that create the most regulatory stress are usually the same ones that create the most technical risk: identity over-permissioning, exposed storage, weak encryption governance, missing logs, and poor evidence retention.
USA.
In the US, healthcare teams handling ePHI need tight access controls, dependable logging, and disciplined encryption practices. Payment environments need segmentation, key management, and evidence that cardholder-related systems are not broadly reachable. SaaS providers pursuing enterprise contracts also face recurring SOC 2 scrutiny around least privilege, monitoring, and change control.
UK.
In the UK, posture issues often become governance issues quickly. Access minimization, accountability, and evidence handling matter just as much as the underlying technical fix. For health-related or public-sector-adjacent workloads, weak cloud controls can also undermine assurance expectations beyond general data protection requirements.
Germany and the wider EU.
In Germany and across the EU, cloud misconfigurations often intersect with data residency, cross-border access, and outsourcing governance. A Frankfurt deployment that stores data in the wrong region or allows unnecessary administrative reach across borders creates both security and regulatory risk. For regulated institutions, traceability and governance are especially important.
Best Practices to Prevent Repeat Misconfigurations
Fixing the first wave of issues is important. Preventing the second wave is what maturity looks like.
Use policy-as-code and secure baselines
Build opinionated guardrails for identity, networking, encryption, and logging. Secure defaults should be enforced before deployment, not discovered after production rollout.
Monitor continuously for drift
Cloud environments change fast. Continuous monitoring helps catch meaningful control drift before it becomes a larger problem.
Collect evidence as you go
Teams in regulated industries should not wait until audit season to assemble proof. Logging, retention, and control evidence should be part of normal cloud operations.
Track the right metrics
The most useful cloud security metrics include.
Mean time to remediate
Percentage of high-risk findings closed within SLA
Repeat control failures
Coverage of cloud assets under policy checks
Number of exceptions still open after review cycles
These metrics tell you whether posture is improving. Raw alert count rarely does.
A Practical Remediation Strategy for Multi-Cloud Enterprises
A strong remediation strategy does not start with buying the biggest platform on the market. It starts with disciplined prioritization.
If your environment is still small, native AWS, Azure, and GCP controls plus strong engineering ownership may be enough. Once you are juggling multiple accounts, subscriptions, projects, and regulated workloads, manual review tends to break down. That is usually the point where CSPM, CNAPP, or automation-backed posture reviews start delivering real operational value.
A realistic next step is a focused posture review.
Identify the top 10 exploitable misconfigurations
Map them to business-critical assets
Assign named owners
Set deadlines and remediation SLAs
Review exceptions instead of letting them live forever
For teams building broader cloud resilience, this is also a natural place to connect posture work with internal resources such as Multi Cloud Strategy Guide Cloud Disaster Recovery GCC Business Intelligence Services and Mak It Solutions Services.
Key Takeaways
Fix identity and access issues first because they create the biggest blast radius.
Public storage, missing encryption, weak network rules, and poor logging remain the fastest path to preventable cloud incidents.
In multi-cloud environments, prioritization matters more than raw finding volume.
Regulated teams in the USA, UK, Germany, and the EU need cloud remediation that supports both security outcomes and audit evidence.
CSPM improves posture visibility, while CNAPP adds broader attack-path context.
Strong cloud security is as much an operating model as it is a tooling decision.
If your team is dealing with AWS, Azure, and GCP findings without a clear remediation order, start with a focused review of your highest-risk cloud security misconfigurations. Mak It Solutions can help turn posture noise into a practical remediation plan aligned with business risk, technical priorities, and compliance expectations.( Click Here’s )
FAQs
Q : What is the difference between a cloud misconfiguration and a cloud vulnerability?
A : A cloud misconfiguration is a settings or policy problem, such as a public bucket, open port, or over-privileged role. A vulnerability is a flaw in software or a component, such as an unpatched library or operating system weakness. In many real incidents, the two overlap: the vulnerability creates access, and the misconfiguration increases the impact.
Q : Which cloud security misconfigurations are hardest to detect in multi-cloud environments?
A : The hardest ones are usually identity and policy issues that look acceptable in isolation but become dangerous when combined. Examples include inherited admin rights, dormant privileged roles, federation gaps, and permission creep spread across multiple cloud environments.
Q : Can native AWS, Azure, and GCP tools replace CSPM platforms?
A : Sometimes they can, especially in smaller environments with strong engineering discipline and clear ownership. In larger estates, teams often struggle to maintain consistent policy coverage, evidence export, and risk prioritization across providers, which is where CSPM becomes more useful.
Q : How often should cloud configuration baselines be reviewed?
A : At minimum, review them quarterly and after major architectural changes, regulatory updates, acquisitions, or new platform rollouts. High-change environments should review critical controls much more often through automated policy checks and drift detection.
Q : Which teams should own remediation in regulated companies?
A : No single team should own it alone. Platform engineering, cloud security, DevSecOps, application teams, and compliance stakeholders all need defined responsibilities. Shared ownership with clear escalation paths works better than a ticket-only model.



[…] may need Kubernetes sooner than a 200-person company running one core application on a single cloud. The real question is whether your environments, release process, and compliance requirements are […]