Confidential Computing in Cloud for GCC Banks & Government
Confidential Computing in Cloud for GCC Banks & Government
Confidential Computing in Cloud for GCC Banks & Government
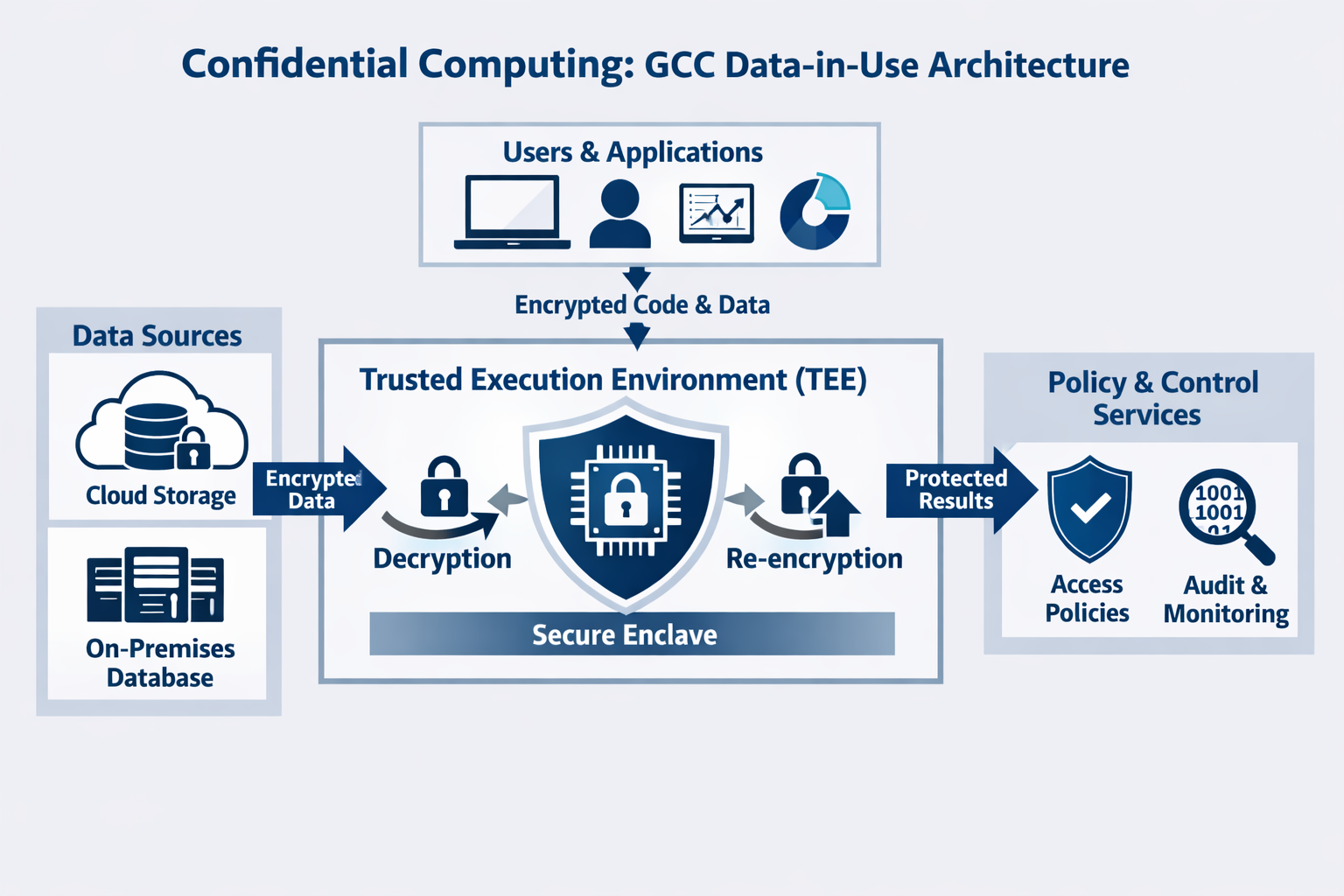
Confidential computing in cloud uses hardware-based trusted execution environments (TEEs) and confidential virtual machines to protect data while it is being processed, not just at rest or in transit. For GCC CISOs in Saudi Arabia, United Arab Emirates and Qatar, it offers a practical way to meet strict data-residency rules, reduce insider risk and run sensitive AI workloads safely on public cloud
Introduction
Across the GCC, most banks, ministries and hospitals already encrypt data at rest and in transit. Yet the real exposure often sits in data in use when core banking engines, national ID systems or AI models process plaintext on shared platforms. For many GCC CISOs exploring confidential computing in cloud, the core question has become simple: who can see our memory, our models, our keys really?
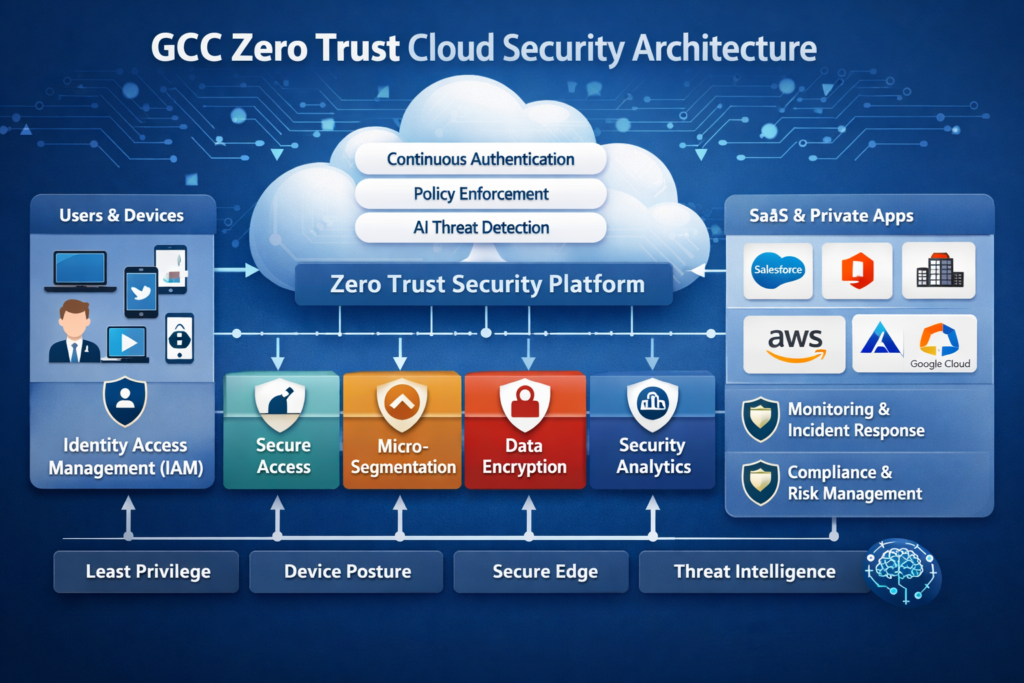
Confidential computing in cloud directly tackles this “data-in-use gap” by running your most sensitive workloads inside hardware-isolated, attested environments that even cloud admins can’t peek into. For GCC organizations facing NCA cloud controls, SAMA and QCB supervision, UAE PDPL and TDRA expectations, this is now a realistic way to combine public cloud agility with sovereign-style assurance in Riyadh, Dubai, Abu Dhabi and Doha.
In this guide, we’ll unpack what confidential computing is, how it differs from normal cloud encryption, how it maps to GCC regulations, and which architectures, vendors and governance patterns make sense for KSA, UAE and Qatar decision-makers.
What Is Confidential Computing in Cloud for GCC Enterprises?
What is confidential computing and how does it protect data in use on public cloud?
Industry bodies define confidential computing as protecting data in use by processing it inside hardware-based Trusted Execution Environments (TEEs). These TEEs encrypt memory and isolate code so that even if the host OS, hypervisor or cloud admin is compromised, the plaintext inside the enclave remains protected.
Unlike traditional cloud security, which focuses on encryption at rest (storage) and in transit (network), confidential computing extends the trust boundary into the CPU itself. This is crucial when you move “crown jewel” workloads core banking, payments, citizen ID, PHI analytics to public cloud regions serving Riyadh, Dubai or Doha, where regulators expect you to show exactly how data in use is protected from insiders and shared infrastructure risk.
Confidential computing vs traditional cloud encryption for GCC workloads
Encryption at rest and in transit still matters, but it doesn’t stop a privileged insider on the host, a malicious admin at the provider, or a compromised hypervisor from reading data while your VM is running. In multi-tenant GCC regions, these are exactly the risk scenarios regulators worry about.
With confidential computing, keys stay inside the enclave, memory is encrypted, and workload identity is proven through remote attestation before decryption happens. For a Saudi digital bank, a Dubai health-tech platform or a Doha payment processor, this reduces the blast radius if the underlying platform is attacked and supports a zero-trust cloud security architecture where you don’t implicitly trust the infrastructure operator.
Key terms: TEEs, secure enclaves and confidential virtual machines
A trusted execution environment (TEE) is a secure area of the processor where code and data are protected in terms of confidentiality and integrity. When TEEs are exposed to developers, we often call them secure enclaves or enclave technology.
Major clouds wrap this in familiar packaging: confidential virtual machines (CVMs) encrypt VM memory and isolate workloads using hardware-based workload isolation. On Microsoft Azure, confidential VMs and databases are already supported in the UAE North region Amazon Web Services (AWS) offers Nitro Enclaves across all regions, including Middle East (Bahrain and UAE) and Google Cloud provides confidential VMs that build on TEEs in its global regions, including the Doha region that supports Qatar’s National Vision 2030.
GCC Compliance, Sovereign Cloud & Data Residency Drivers
Why GCC regulators now care about protecting data in use
Saudi Arabia’s Cloud Cybersecurity Controls (CCC) from the National Cybersecurity Authority link cloud adoption to strict data classification and localization requirements, and these have recently been updated to sharpen expectations on how regulated tenants protect sensitive data. The Saudi Central Bank (SAMA) cyber and cloud standards require banks and fintechs to keep critical financial data under strong technical and contractual controls, even when outsourced.
In the UAE, PDPL, TDRA guidance and the National Cloud Security Policy expect additional safeguards when sensitive or biometric data is processed on shared infrastructure. Qatar’s QCB cloud rules and national cloud initiatives focus on keeping regulated workloads inside the national data boundary and ensuring that supervisors retain effective oversight. In all three countries, regulators now recognize that “data in use” is part of the threat surface, especially for AI and analytics.
How can Saudi organizations meet cloud cybersecurity controls while moving sensitive workloads to confidential VMs?
For Saudi ministries, banks and regulators, a practical approach is to map NCA cloud controls and SAMA requirements directly onto confidential computing features: use in-kingdom regions, confidential VMs, hardware-backed attestation and strong key management. A Saudi compliant confidential cloud solution typically combines TEEs, HSM/BYOK, centralized logging and continuous posture management.
For example, a Riyadh fintech deploying open banking APIs can run its payment and risk engines on confidential VMs in a local cloud region, prove attestation logs to internal audit, and store keys in a dedicated HSM. This reduces insider risk, supports NDMO data-classification and residency expectations, and gives risk committees defensible evidence that cloud workloads meet national cyber controls.

Sovereign cloud vs public cloud for sensitive data in KSA, UAE and Qatar
“Sovereign cloud” usually means a region or platform with locally controlled operations, legal jurisdiction and sometimes air-gapped management, whereas standard public cloud regions share global operational stacks. In the GCC, you’ll see both national sovereign environments and hyperscaler regions in Riyadh, Jeddah, Dubai, Abu Dhabi and Doha.
Confidential computing can run in either model: sovereign clouds may offer enclave-backed compute inside national facilities, while hyperscalers provide confidential VMs in AWS Bahrain/UAE regions, Azure UAE North and GCP Doha. The trade-off for banks, government and healthcare is between maximum locality and ecosystem richness but with confidential computing, many CISOs can safely keep ultra-sensitive workloads on public cloud while staying aligned with local regulators. For deeper comparisons, Mak It Solutions’ sovereign cloud vs hyperscalers GCC decision guide explores these options in detail.(Mak it Solutions)
How Confidential Computing Secures Sensitive GCC Workloads
Reference architecture for banking and fintech workloads in KSA & UAE
A typical architecture for digital banks in Riyadh and Dubai uses confidential VMs for payment switching, risk scoring and AML models, fronted by API gateways and protected by WAF and tokenization services. Keys live in a cloud KMS or external HSM, with hardware-based workload isolation ensuring card data and transaction histories never leave the enclave in plaintext.
To build a Saudi compliant confidential cloud solution, Mak It Solutions often designs a landing zone that unifies confidential compute, HSM/BYOK, centralized SIEM and open banking APIs. This lets banks plug in new fintech partners while keeping core workloads inside attested environments, and it complements our broader GCC data localization requirements in KSA & UAE guidance.(Mak it Solutions)
Confidential computing for government, smart city and healthcare platforms
For UAE digital government, smart city platforms and UAE Pass-style identity services, confidential computing provides strong isolation for citizen identity data and transaction logs. Running these services on confidential VMs in Dubai or Abu Dhabi helps align with PDPL and TDRA expectations while enabling modern microservices and AI assistants.
In Saudi and Qatar, e-government and e-health platforms can process PHI, national IDs and clinical data inside enclaves, while cross-agency integrations use tokenization and attribute-based access. This is especially powerful when you’re building Arabic-language virtual assistants for citizens: the model can see sensitive text, but the underlying infrastructure cannot.
Data in use protection for AI training and advanced analytics
Confidential computing is critical when training AI on sensitive datasets such as citizen records, financial histories or clinical notes. Encrypted data can be decrypted only inside the TEE, and training jobs run on confidential VMs with attested configurations, which is increasingly aligned with regulators’ expectations for “AI with controls.
For cross-border GCC analytics say, a joint KSA–UAE–Qatar fraud consortium confidential multi-party analytics let participants share features without directly exposing raw data. This matters even more for Arabic AI models, where training corpora may include identifiable text; TEEs and secure enclave technology ensure these workloads follow a zero-trust approach to both infrastructure and participants.
Real GCC Use Cases: From Banks in Riyadh to AI Campuses in UAE
Banks and fintechs: from PCI to “Qatar central bank approved confidential computing”
Banks in Riyadh, Jeddah, Dubai and Doha can isolate card processing, core banking and fraud detection workloads inside confidential VMs while keeping supporting apps on standard VMs. This aligns with SAMA, QCB, Abu Dhabi Global Market (ADGM) and Dubai International Financial Centre (DIFC) expectations on outsourcing, cloud and operational resilience.
A Doha bank aiming for “Qatar central bank approved confidential computing” could run payment-clearing engines on confidential VMs in the GCP Doha region, use in-country key management and provide QCB with attestation and logging evidence. Fintechs offering Sharia-compliant products can adopt the same pattern for wallets, BNPL and open finance APIs.

Government & critical infrastructure across GCC
Ministries, digital government authorities and national ID platforms across KSA, UAE, Qatar, Kuwait, Bahrain and Oman can place their highest sensitivity systems e.g., civil registries, customs, defence-adjacent analytics on confidential compute. This reduces reliance on physical segmentation alone and allows gradual migration from on-prem to GCC cloud regions.
Critical infrastructure operators in energy, utilities and logistics can process OT telemetry and incident logs on enclaves for advanced analytics, while still complying with national cybersecurity strategies and data residency mandates. For example, a Jeddah logistics hub can run route-optimization AI in the cloud without exposing raw shipment manifests to the broader platform.
Healthcare, research and Arabic AI initiatives
National health records, hospital information systems and telemedicine platforms can run encryption, tokenization and analytics inside confidential VMs, protecting PHI from both external attackers and privileged insiders. Research institutes can share anonymised but still sensitive cohorts using confidential analytics, enabling federated studies without centralizing all raw data.
Arabic medical AI models clinical summarization, triage assistants, decision support can be trained and served from confidential compute in GCC data centers. This ensures PHI and notes remain inside TEEs during both training and inference, helping health ministries and regulators justify the use of generative AI in care pathways.
Vendor & Implementation Playbook for GCC Cloud Teams
How does Azure confidential computing in UAE North help with data residency and PDPL requirements?
Azure confidential computing encrypts data in memory inside TEEs and only processes it after verifying the environment, helping protect data from cloud provider access and host compromise.In UAE North, confidential VMs and managed databases give you in-region, hardware-backed protection for sensitive workloads, which is particularly useful for PDPL-regulated data and TDRA-supervised telecom and digital services.
A UAE enterprise can migrate an existing workload by first moving it into a standard UAE North VM, then switching to the equivalent confidential VM SKU, enabling attestation and integrating with its KMS. This creates a UAE PDPL friendly data in use encryption pattern without rewriting the entire application stack.
AWS, Google Cloud and local providers.
On AWS, Nitro Enclaves provides isolated execution environments for sensitive data processing and is now available in all regions, including Middle East (Bahrain and UAE).(Amazon Web Services, Inc.) Many GCC banks and fintechs use this for payment tokenization, HSM-wrapped key operations and secure KYC checks.
Google Cloud offers confidential VMs based on AMD SEV/TDX in multiple regions, and the Doha region provides low-latency, in-country infrastructure that supports Qatar’s digital government ambitions.Local and national cloud providers across KSA and UAE increasingly expose confidential computing as a managed service, sometimes integrated with sovereign AI campuses in Abu Dhabi or Riyadh. Mak It Solutions helps compare these options in its GCC sovereign cloud and data residency guide. (Mak it Solutions)

Step-by-step: how to plan a pilot for confidential computing in your GCC organization
Identify candidate workloads
Start with high-value but bounded systems payment engines, citizen-facing portals, health analytics or AI models that process sensitive data.
Check data classification and residency
Align with NDMO or equivalent schemes and confirm which records must stay in-kingdom or in-country.
Engage security, compliance and architecture early
Form a joint squad with CISO, DPO, cloud architects and risk to agree objectives and guardrails.
Design your reference pattern
Choose cloud regions, confidential VM SKUs, KMS/HSM integration, logging, attestation flows and connectivity.
Define success metrics
Track security posture (e.g., reduced privilege), performance, regulator feedback and operational overhead to decide whether to scale.
Governance, Cost & Best Practices for GCC Cloud and Security Leaders
How costs differ between Saudi, UAE and Qatar when using confidential computing
Confidential VMs usually cost more than standard instances, and some managed databases or AI services charge a premium for TEE-backed options. In GCC regions, price deltas vary by provider and instance family, so CISOs should compare confidential and non-confidential SKUs for their main workloads.(Google Cloud)
From a TCO perspective, you also need to account for governance, observability and skills: more advanced logging, attestation verification and KMS integration. For mid-sized enterprises, pilots tend to stay within existing cloud budgets; for large ministries or tier-1 banks, confidential computing becomes part of broader cloud and zero-trust investment, justified by regulatory comfort and reduced on-prem spend.
Governance model.
A workable governance model assigns CISOs and DPOs responsibility for policies, cloud architects for design patterns, and platform teams for day-to-day operations. RACI charts should clearly state who approves which workloads can use confidential computing, who validates attestation reports and who owns incident response.
Policies should cover onboarding (when a workload qualifies for confidential compute), attestation requirements, key management, monitoring and evidence retention. Align these with SAMA, TDRA, QCB and NDMO guidance so that internal risk teams and regulators see consistent controls across sovereign and public cloud deployments.
GCC-specific best practices and common pitfalls
Avoid assuming that confidential computing alone solves data residency: you still need to ensure the region is in KSA, UAE or Qatar and that backups, logs and DR all respect localization rules. Misconfigured cross-border backups are a common pitfall.
For citizen-facing apps and Arabic AI assistants, pair confidential compute with clear consent flows, Arabic UX and transparent explanations of how data is processed. Across the GCC, involving regulators early sharing reference architectures, pilot scope and attestation plans usually leads to smoother approvals than presenting a finished solution at the end. Our GCC sovereign cloud and data residency guide and GCC data localization requirements in KSA & UAE articles deepen these themes.(Mak it Solutions)
Concluding Remarks
Confidential computing in cloud is moving from niche to “must have” for GCC organizations that run core banking, government, healthcare and AI workloads in public cloud. By protecting data in use with TEEs, enclaves and confidential VMs, CISOs can meet stricter regulatory expectations while still benefiting from the scale and innovation of hyperscaler platforms and sovereign clouds.
A pragmatic roadmap starts with an assessment workshop, selecting one or two candidate workloads, designing a GCC-ready architecture, then moving the first production workload into confidential compute with clear success metrics. For GCC CISOs, this turns confidential computing in cloud from a buzzword into a concrete control you can explain to auditors, boards and supervisors.
If you’re a CISO, architect or regulator-facing leader in KSA, UAE or Qatar, you don’t have to figure this out alone. Mak It Solutions already helps GCC banks, governments and scale-ups design confidential computing patterns that align with local regulators and real-world constraints.
You can explore our broader cloud and software services and specialized business intelligence and analytics offerings to see how we operationalize secure data platforms. Or simply contact our team to request a confidential computing readiness assessment or a tailored pilot design for your GCC workloads.
FAQs
Q : Is confidential computing allowed under Saudi cloud cybersecurity controls and SAMA cyber framework?
A : Yes. The NCA’s Cloud Cybersecurity Controls (CCC) and the SAMA cyber framework do not prohibit confidential computing; they focus on outcomes such as data classification, localization, technical safeguards and oversight.Confidential computing can actually strengthen compliance because it reduces the risk of privileged access to regulated data in use on shared platforms. For example, a Riyadh bank can run card-processing on confidential VMs in a local region, keep keys in an HSM, enforce strict RACI for access and provide attestation evidence to auditors. This supports Saudi Vision 2030’s digital ambitions while remaining within national cyber and financial-supervisory rules.
Q : Do UAE PDPL rules require confidential computing for all sensitive workloads in public cloud?
A : No, PDPL does not mandate a specific technology such as confidential computing for every workload, but it does require appropriate technical and organizational measures for personal and sensitive data. For many cloud-native services in Dubai or Abu Dhabi, standard encryption and access controls may be enough, especially for low- to medium-risk data. However, for high-risk use cases—biometrics, identity, financial and health data confidential computing in UAE North or other in-country regions can be a strong way to demonstrate “state of the art” protection. TDRA and sector regulators increasingly look favourably on designs that combine PDPL principles with TEEs, strong key management and zero-trust cloud security architectures.
Q : How can Qatar banks use confidential VMs while staying inside the national data boundary?
A : Qatar banks can start by choosing in-country cloud regions and providers that keep primary and backup data within Qatar’s borders. The GCP Doha region, for example, offers in-country infrastructure aligned with Qatar’s National Vision 2030 digital agenda.On top of that, banks can run payment-clearing, AML and fraud workloads on confidential VMs, keeping memory encrypted and keys in local KMS or HSMs. Network controls should restrict outbound traffic, and logs must be stored in-country or in regulator-approved environments. By combining these patterns with QCB cloud rules, outsourcing approvals and regular reporting, banks can use confidential computing without breaching the national data boundary.
Q : What are the main differences between using a GCC sovereign cloud and a global hyperscaler for confidential workloads?
A : A GCC sovereign cloud is usually operated under local legal jurisdiction with tighter control over staff, operations and data movement, which can simplify localization and legal-risk analysis. Global hyperscalers, by contrast, offer massive ecosystems, advanced AI services and mature confidential computing features, but come with more complex cross-border and shared-operations considerations. In practice, many CISOs in KSA, UAE and Qatar adopt a hybrid approach: keep the most sensitive or classified workloads on sovereign or national clouds, while using hyperscaler regions like AWS Bahrain, Azure UAE North and GCP Doha for regulated but less sensitive workloads with TEEs and confidential VMs. The right mix depends on regulator expectations, supply-chain comfort and your internal risk appetite.
Q : Can Arabic language AI assistants for citizens run safely on confidential VMs in GCC data centers?
A : Yes confidential VMs are a strong fit for Arabic government and banking assistants that handle personal data, identity information or financial details. The model and its runtime process sensitive prompts inside a TEE, so even if an attacker gains access to the host system, they cannot easily read memory or extract raw logs. When combined with local data centers in KSA, UAE or Qatar, strong KMS/HSM integration and careful logging policies, this pattern lets ministries and banks deliver modern Arabic AI services without losing control of citizen data. It also helps demonstrate to regulators and the public that AI is being deployed responsibly, with privacy and sovereignty built into the infrastructure.


