GCC Data Localization Requirements in KSA & UAE
GCC Data Localization Requirements in KSA & UAE
GCC Data Localization Requirements in KSA & UAE
Across KSA, UAE and Qatar, GCC data localization requirements typically demand clear data classification, in-country hosting for critical and regulated records, and tight control of any cross-border personal data transfer in cloud environments. For cloud and AI workloads, that usually means using in-country or sovereign cloud regions, local key management, strong security controls and regulator-approved outsourcing models that you can evidence during audits.
Introduction
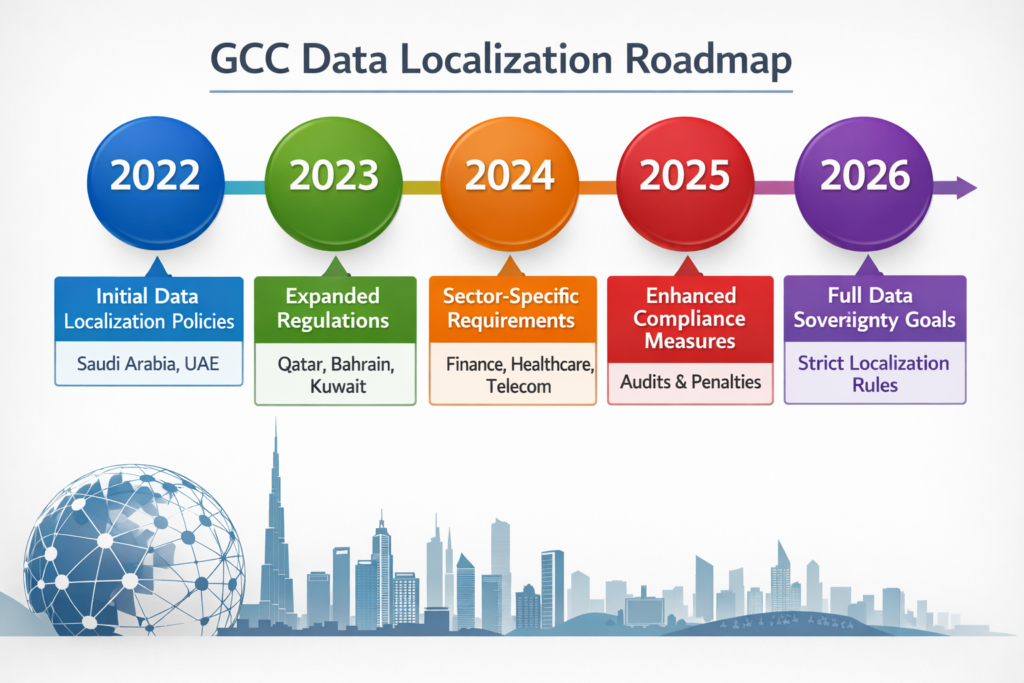
Why GCC data localization just became a board topic
Board conversations in the Gulf have shifted from “Which cloud is cheapest?” to “Will our architecture survive the next regulator visit?”. As PDPL-style laws and cloud regulations tighten in KSA, UAE and Qatar, GCC data localization requirements now sit alongside profitability and AI strategy on the board agenda.
The core question:
CIOs and CISOs want to keep using hyperscalers, SaaS and GenAI without triggering red flags from Saudi Central Bank (SAMA), the Telecommunications and Digital Government Regulatory Authority (TDRA) or Qatar Central Bank (QCB). The real design question is: how do you keep critical data in-country, use modern cloud services and still walk into every audit with calm confidence?
Who this guide is for in KSA, UAE, Qatar and wider GCC
This guide is for heads of architecture, CISOs, DPOs and compliance leads in banks, government entities, healthcare providers and SaaS/fintech teams across Riyadh, Dubai, Abu Dhabi, Doha and other GCC hubs. You’ll find practical patterns you can feed straight into your next architecture review, RFP or board pack.
Regulatory landscape.
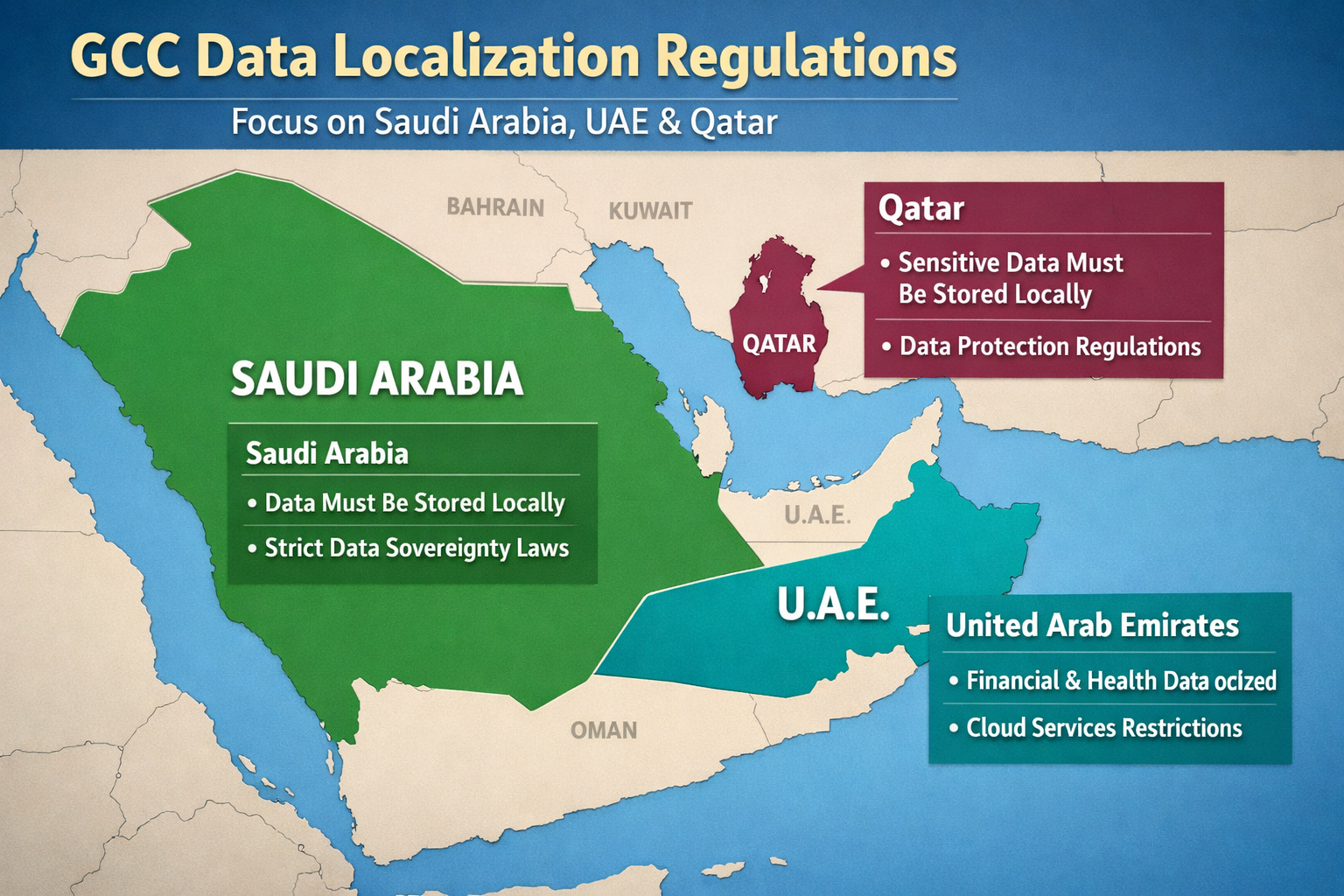
Saudi PDPL, NDMO and sector regulators
Saudi Arabia’s PDPL, together with standards from the National Data Management Office (NDMO), creates a national baseline for data governance, classification and cross-border movement. In practice, NDMO and sector rules expect sensitive and government data to be tightly governed and, for many categories, kept within Saudi borders or under clear control in an NDMO-compliant data residency architecture in KSA.
For cloud teams, that translates into clear data classification, documented data flows and a landing zone that shows exactly which datasets ever touch non-KSA regions, and under what safeguards.
UAE PDPL, TDRA cloud frameworks and free-zone regimes
The UAE PDPL (Federal Decree-Law 45/2021) sets national rules for processing and cross-border personal data transfers, while TDRA oversees telecom and cloud infrastructure used by many regulated entities. DIFC and ADGM run their own GDPR-style regimes, so a bank with operations in those free zones must align UAE PDPL, DIFC/ADGM data protection laws and sector guidance when choosing where to host workloads.
Practically, UAE architectures often need a matrix view: which workloads are federal, which sit under DIFC/ADGM, and which fall under sector regulators like the Central Bank or health authorities.
Qatar’s QCB cloud regulations and data handling rules
QCB’s 2024 Cloud Computing Regulation and Data Handling & Protection Regulation require banks and payment institutions to treat cloud as material outsourcing. That means in-country storage for critical financial data, rigorous due diligence, exit strategies and explicit approval for using offshore regions or foreign subcontractors, especially for core banking workloads.
For Doha-based institutions, GCC data localization requirements usually mean that primary records and detailed logs live in Qatar, with offshore regions used only for carefully controlled resilience or analytics scenarios.
Core architectural principles for GCC data localization
Data classification and zoning for KSA, UAE and Qatar
Start by aligning your taxonomy with NDMO-style levels (public, internal, confidential, restricted) and PDPL concepts of sensitive and high-risk data. Then map each dataset into zones: in-country only, regional GCC, or global regions allowed, with clear rules on when pseudonymisation or tokenization can “downgrade” data to a less restricted zone. (SDAIA)
The goal is simple: any architect looking at a workload should immediately see which jurisdictions it can touch and under which conditions.
Data residency vs localization vs sovereignty
Data residency answers “where is it stored?”.
Data localization adds “and it must stay there unless strict conditions are met”.
Data sovereignty goes further: “and it remains under local legal and operational control”.
For cloud teams, understanding data residency vs data localization vs full data sovereignty in GCC markets is the foundation for any design discussion, especially when mixing sovereign clouds, regional public regions and SaaS.
Security controls regulators expect around localized data
Across KSA, UAE and Qatar, regulators expect encryption for data in transit and at rest, in-country key management, strong IAM, logging, DLP and SIEM tuned to critical datasets. Zero-trust patterns, privileged-access monitoring and clear incident-response runbooks are now table stakes for passing financial-sector cloud reviews.
In heavily regulated sectors, assume you will be asked to demonstrate who can see what, from where, and under which approval path down to admin actions and cross-border support access.
Reference architecture patterns that pass GCC compliance reviews
In-country sovereign cloud region
Highly regulated workloads often land in sovereign or national clouds, or in-country hyperscaler regions such as AWS Bahrain, Azure UAE Central or GCP’s Doha region, forming a sovereign cloud region Middle East backbone. Core ledgers, payment systems and health records stay here, with HSM-backed keys and admin access restricted to in-country teams. (Mak it Solutions)
This pattern works well for banks, digital government and health providers that want hyperscaler capabilities without compromising regulatory comfort around GCC data localization requirements.
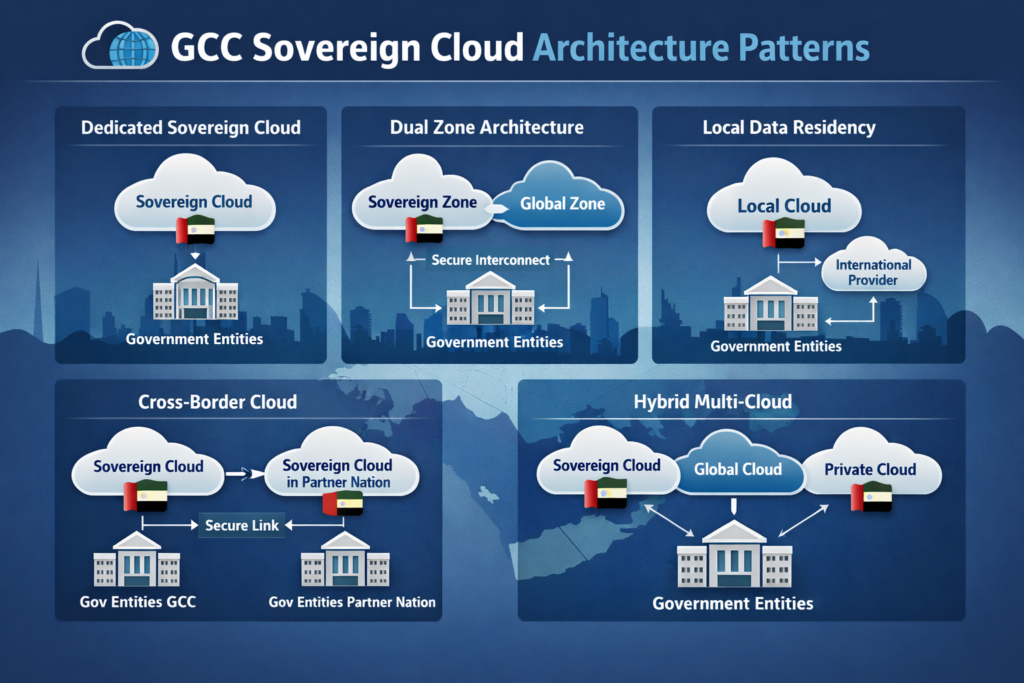
Local data center + global hyperscaler
Many enterprises use a local data center in cities like Jeddah or Sharjah for PII and regulated data, paired with global hyperscaler regions for less sensitive services. Think of transactional data stored locally, while anonymised analytics and non-PII workloads run in global regions for elasticity and advanced AI services. (Mak it Solutions)
Done properly, this gives you local control and low latency for citizens and customers, while still letting teams tap into the latest AI and SaaS platforms.
Multi-region / multi-cloud for pan-GCC institutions
Pan-GCC banks and telcos often segment data by country while sharing hardened cross-border services. Local pods in Manama, Muscat and Kuwait City keep regulated data at rest, while regional analytics and AI layers consume tokenized or pseudonymised feeds to support cross-market insight.
This pattern needs careful key management and data zoning, but it can unlock regional growth without breaking localization rules in any single market.
Sector-specific blueprints.
Banking architectures for SAMA, UAE Central Bank and QCB
A bank with branches in KSA, UAE and Qatar might keep core ledgers and payment data in each country, with a regional reporting lake containing tokenized data only. Outsourcing registers, cloud risk assessments and robust exit plans then help satisfy central-bank expectations during on-site inspections.
From a practical delivery perspective, that often means.
Separate country pods with their own encryption keys and admin roles
A regional analytics layer that never sees raw identifiers
Documented playbooks for regulator access, investigations and e-discovery
Government and critical national infrastructure workloads
Smart-city and e-government platforms in capitals across the region frequently use national or sovereign clouds with lawful-access capabilities and strong content controls. Integration with global SaaS is allowed only where residency, contractual controls and monitoring match national-security expectations.
For ministries and critical infrastructure operators, GCC data localization requirements are as much about operational control (who can push changes and from where) as they are about where disks physically sit.
GCC SaaS and fintech multi-tenant patterns
Regional SaaS and fintech platforms increasingly adopt country-specific data pods or sharded multi-tenancy for KSA, UAE and Qatar. For regulated journeys such as onboarding, Open Banking Saudi Arabia APIs or local e-ID schemes, they combine in-country keys, segregated storage and bilingual Arabic/English UX. (Mak it Solutions)

Example scenarios (real-world flavour)
A Riyadh fintech aligning Open Banking, PDPL and NDMO rules while using cloud under SAMA’s outsourcing expectations.
A Dubai e-commerce brand hosting customer data in UAE while offloading anonymised recommendation models to global regions.
A Doha SME keeping CRM data in Qatar while using offshore analytics fed only with tokenized identifiers under QCB guidance.
Operations, monitoring and cross-border data transfers
Monitoring, logging and incident response across GCC
Centralised observability is compatible with localization if you design it deliberately: logs for regulated systems stay in-country, while dashboards can be shared across regional SOC teams with controlled access. Runbooks should reflect PDPL-style breach-notification timelines and each regulator’s expectations on evidence and reporting.
Think of it as “federated logging”: storage remains local, but insights are shared securely.
Handling cross-border transfers, AI and analytics
To enable cross-border personal data transfer GCC-wide, many teams use pseudonymisation, tokenization and “privacy vaults” that keep raw identifiers in-country. AI or analytics platforms in regional or global regions only see masked data, while in-country services resolve tokens back to real customers when needed.

This pattern is especially powerful for GenAI pilots: large models can run in global regions, but only ever see de-identified data, with re-identification strictly controlled inside KSA, UAE or Qatar.
Audit readiness, RFP responses and evidence packs
Regulators and large customers increasingly expect architecture diagrams, data-flow maps, DPIAs, SLAs and third-party risk assessments as standard. Building reusable evidence packs makes RFP responses faster and turns localization from a last-minute scramble into a repeatable, well-governed process.
A good rule of thumb: if a control is not documented, logged and periodically reviewed, assume an inspector will treat it as “not in place”.
Practical roadmap and next steps for GCC leaders
Step-by-step roadmap from assessment to go-live
A pragmatic 12–18 month roadmap starts with data discovery and classification, then mapping each dataset to local rules and risk. Next, choose your target pattern, run pilots in non-critical workloads, then progressively migrate core systems once controls and monitoring are battle-tested.
In practice, many GCC organizations run one or two pilot workloads in each key country first, using those projects to refine playbooks and regulator engagement before touching core platforms.
Working with hyperscalers, sovereign clouds and local partners
Combining hyperscaler regions, sovereign or national clouds and specialist partners helps you balance cost, resilience and data sovereignty in GCC markets. Local partners can translate dense regulator text into concrete landing-zone designs and support NDMO-compliant data residency architecture in KSA alongside UAE PDPL data residency requirements for financial institutions in Dubai. (Amazon Web Services, Inc.)
For teams in Riyadh, Dubai and Doha, this often means a blended model: in-country regions for crown-jewel data, regional public regions for shared services and carefully governed SaaS for productivity and collaboration.
KPIs, governance and continuous improvement
Set KPIs such as “% of high-risk datasets classified and localized” and track regulator guidance as it evolves under initiatives like Saudi Vision 2030. A cross-functional steering committee should own cloud, data and AI decisions so localization doesn’t fragment across projects.
Regular reviews with audit, legal and security teams help you keep ahead of regulator expectations instead of reacting after inspection findings.
Key takeaways for GCC data localization strategy
Localize smart, not blindly: classify first, choose patterns second. Design for regulators and auditors as much as for uptime and latency, and extend your thinking to cover analytics, GenAI and cross-border services not just the primary transactional systems.
If you can point to clear data zones, sovereign or in-country regions for critical workloads, and documented cross-border controls, your GCC data localization requirements stop being a blocker and start becoming a competitive advantage in regulated tenders.
How to apply this guide to your Riyadh/Dubai/Doha roadmap
Map your current workloads against the patterns in this guide and identify quick wins and high-risk gaps. Then turn those findings into a board-approved roadmap and RFP pack that you can share with internal teams, hyperscalers and specialist partners across KSA, UAE and Qatar.
If you’d like a second pair of eyes on your current cloud and data maps, you don’t have to figure this out alone. Mak It Solutions already supports banks, government entities and SaaS teams designing GCC-ready landing zones and sovereign architectures. Explore our dedicated GCC sovereign cloud and data residency guide and GCC data localization laws for cloud computing, then reach out for a tailored GCC data localization strategy for your Riyadh, Dubai or Doha roadmap.( Click Here’s )
FAQs
Q : Is data localization mandatory for all workloads in Saudi Arabia, or only for specific sectors like banking and government?
A : Data localization in Saudi Arabia is risk- and sector-based rather than a blanket rule for every workload. PDPL and NDMO standards push organizations to classify data and apply stricter controls to government, financial, health and other sensitive categories, often requiring local hosting or strong safeguards for transfers. Banks and critical infrastructure supervised alongside PDPL under bodies such as SAMA and the National Cybersecurity Authority face the tightest expectations, while low-risk corporate data can often use regional or global cloud with appropriate safeguards.
Q : Can a bank in Dubai or Doha keep backups in an EU or US cloud if the primary data center is in-country?
A : Often yes, but only under strict conditions. Under UAE PDPL, cross-border transfers require adequate protection in the destination country or contractual and technical safeguards such as strong encryption and robust data-processing contracts. Qatar’s QCB Cloud Computing Regulation treats offshore backups as cloud outsourcing, meaning banks must secure QCB approval, maintain data-protection controls and ensure regulators retain access to records and logs. In both cases, a clear data-flow map and contractual rights are essential before using EU or US regions for backup.
Q : How do GCC regulators view encryption-only approaches where data leaves KSA, UAE or Qatar but keys stay locally?
A : Keeping encryption keys in-country is helpful but not a silver bullet. GCC regulators increasingly look at the full context sensitivity of the data, strength of encryption, location of admins and legal jurisdiction over the cloud provider when assessing residual risk. For very sensitive workloads, such as regulated financial or government data, they may still expect primary storage to remain in-country, with offshore access tightly limited and justified. Encryption-only approaches work best for pseudonymised analytics or lower-risk workloads backed by strong contracts and demonstrable operational controls.
Q : What is the difference between a sovereign cloud region and a normal public cloud region in the Gulf?
A : A sovereign cloud region is designed so that infrastructure operations, support staff and legal jurisdiction all sit under one country’s control, often with extra controls aligned to national security and public-sector rules. A normal public cloud region in the Middle East might be physically nearby but still subject to foreign laws or offshore administration. For high-risk workloads under regimes like PDPL, UAE DP Law or QCB’s banking rules, sovereign options can simplify compliance at the cost of higher price or fewer services; lower-risk workloads can often use standard regions if transfer rules and security are carefully designed and documented.
Q : What should a GCC data localization RFP include when shortlisting cloud or SaaS vendors for Riyadh, Dubai and Doha?
A : A strong RFP goes beyond generic “ISO-certified” questions and asks vendors to prove how they meet local rules. That includes in-country hosting options, data-classification support, encryption and key-management models, cross-border transfer controls, regulator-access clauses and exit strategies. You should also request detailed architecture diagrams, data-flow maps, DPIA templates and sample audit reports so your team can validate claims quickly. Finally, align scoring with your multi-year cloud roadmap and national initiatives like Vision 2030, so shortlisted vendors support both regulatory and growth objectives across Riyadh, Dubai and Doha.