OT Cybersecurity for Oil and Gas in Saudi & UAE
OT Cybersecurity for Oil and Gas in Saudi & UAE

OT Cybersecurity for Oil and Gas in Saudi & UAE
OT cybersecurity for oil and gas in the GCC means protecting industrial control systems (ICS), such as SCADA, DCS and PLCs, so refineries, pipelines and LNG terminals in Riyadh, Dubai and Doha can run safely and reliably. The basic controls every GCC plant should start with are OT asset inventory, network segmentation, hardening of SCADA/DCS/PLCs, secure remote access, monitoring and an OT-focused incident response plan aligned with NCA OTCC-1:2022, UAE Information Assurance and Qatar’s national cyber strategies.
Introduction
Across the Gulf Cooperation Council, OT cybersecurity for oil and gas has moved from “nice to have” to a board-level priority. Recent ransomware and industrial-control incidents worldwide have shown how quickly a single compromise can halt pipelines, LNG exports and refinery operations.
In Saudi Arabia, the National Cybersecurity Authority (NCA) now expects operators to implement dedicated Operational Technology Cybersecurity Controls (OTCC-1:2022).In the UAE, Information Assurance regulations driven by TDRA and NESA-style frameworks cover critical energy infrastructure,while Qatar’s updated national cyber strategy extends to LNG plants and gas pipelines around Doha.
This guide is written for OT managers, CISOs and control engineers working in refineries, pipelines and LNG terminals in Riyadh, Dubai, Abu Dhabi and Doha who need practical basics they can apply this year.
What Is OT Cybersecurity for Oil and Gas in the GCC?
OT vs IT security in refineries, pipelines and LNG terminals
OT cybersecurity for oil and gas focuses on systems like DCS, PLCs and SCADA that directly control valves, compressors and safety systems, rather than email or ERP. In Riyadh, Dubai and Doha plants, the top priority is safety and uptime, so controls must avoid unplanned shutdowns while still protecting industrial control systems (ICS). Industrial cybersecurity here is about carefully balancing process safety, availability and integrity.
Key OT systems in GCC oil and gas operations
Upstream wellheads and offshore platforms near Abu Dhabi and Qatar rely on SCADA, RTUs and safety instrumented systems (SIS). Midstream pipelines and export terminals use SCADA, leak detection and historian servers to coordinate logistics. Downstream refineries and petrochemical complexes in Saudi’s Eastern Province run large DCS environments with integrated SIS and tank-farm automation. Together, these create a complex OT landscape that needs consistent protection.
Main OT cyber risks facing GCC operators
Common threats for GCC operators include ransomware on engineering workstations, APTs abusing remote access and supply-chain compromises through vendors. Because oil and gas is defined as critical infrastructure in national cyber strategies, disruption can trigger regulatory scrutiny and reputational damage. That’s why “practical basics” like visibility, segmentation and secure access are the first priority before advanced analytics or AI.
Basic OT Cybersecurity Controls Every GCC Oil and Gas Plant Should Implement First
What are the basic OT cybersecurity controls every GCC oil and gas plant should implement first?
For a refinery in Jubail, a gas plant near Abu Dhabi or an LNG terminal outside Doha, the first controls should be: build an accurate OT asset inventory, segment IT and OT networks, harden SCADA/DCS/PLCs, secure all remote access, and prepare an OT-specific incident response playbook. These steps align directly with NIST/IEC 62443-based OT controls and GCC regulations such as NCA OTCC and UAE IA.
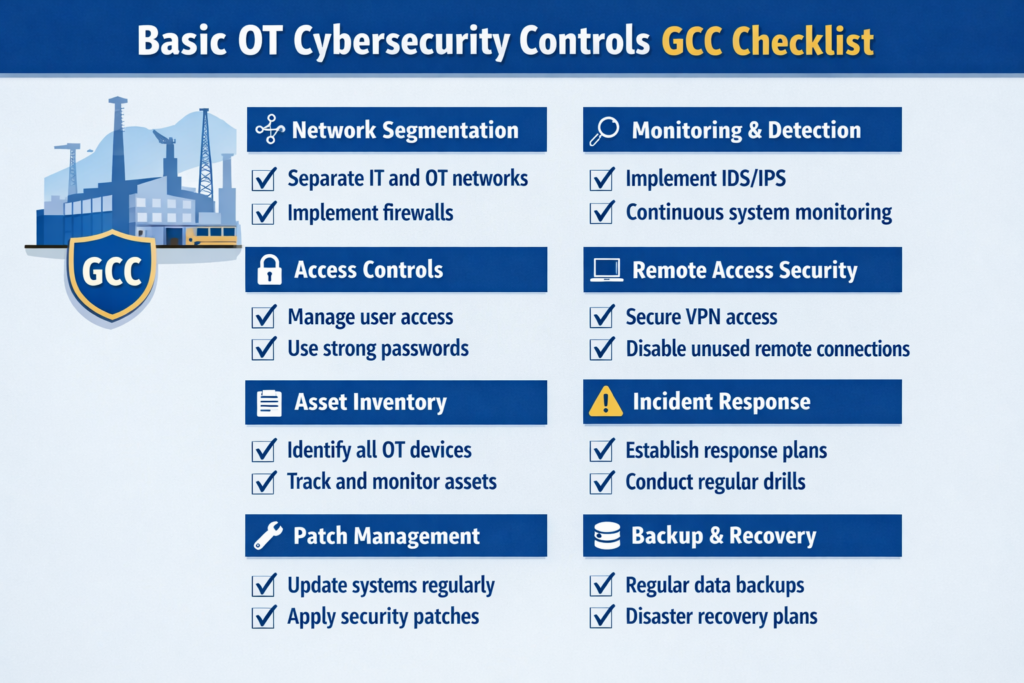
Know your assets and zones: OT inventory, visibility and segmentation
Many Saudi and UAE sites still operate without a complete list of PLCs, RTUs and HMIs. Start with passive discovery tools, updated network diagrams and mapping PLCs/RTUs to process areas. Then group them into zones (for example, safety, control and supervisory) and conduits, using IEC 62443 as a reference. This becomes the foundation for any Saudi oil & gas OT security checklist or UAE refinery ICS cybersecurity best practice.
Hardening SCADA, DCS and PLCs with simple, doable controls
Next, apply basic configuration hygiene: unique strong passwords, disabling unused services, removing default vendor accounts and enforcing change control on engineering stations. In brownfield plants, simple application whitelisting on HMIs, regular backups of controller logic and standardised bilingual (Arabic/English) HMI terminology can significantly reduce operational mistakes and cyber risk.
OT incident response basics for refineries and pipelines
Every plant should have a minimal OT incident playbook: who leads, which systems to isolate, how to collect logs without affecting safety and when to escalate to national CSIRTs or regulators. Joint IT–OT tabletop exercises for pipeline and LNG scenarios help teams practise decisions such as controlled shutdown versus degraded, monitored operation.
Aligning OT Security with GCC Regulations: OTCC, UAE IA and Qatar Requirements
Why is OT security in Saudi oil and gas now tightly linked to NCA OTCC-1:2022 requirements?
In Saudi Arabia, OT security for refineries and petrochemicals is now measured against OTCC-1:2022, which sets minimum controls for ICS environments and extends the earlier Essential Cybersecurity Controls. Compliance is increasingly tied to licensing and can be audited or fined, so oil and gas operators align governance, risk assessments, asset inventory and segmentation to OTCC’s domains and sub-controls.
What NCA OTCC-1:2022 means for Saudi refineries and petrochemicals
NCA OTCC-1:2022 expects Saudi operators to define OT governance, classify critical facilities, maintain an accurate OT asset inventory, segment networks, secure remote access and monitor for threats.It also reinforces the security culture already driven by the Saudi Central Bank (SAMA) in financial services, showing a broader national direction towards stronger critical infrastructure OT protection.
UAE IA / NESA and TDRA expectations for OT cybersecurity
In the UAE, the Information Assurance Regulation, historically driven by NESA and now under TDRA, is mandatory for critical information infrastructure, including energy and utilities. For offshore platforms and onshore facilities near Abu Dhabi, mapping OT basics (asset inventory, segmentation, monitoring, secure telecom links) into UAE IA controls helps demonstrate due diligence and support TDRA’s connectivity requirements.
Qatar LNG and national cyber requirements for OT environments
Qatar’s National Cyber Security Strategy 2024–2030 and broader digital agenda explicitly focus on protecting critical infrastructure, including LNG trains and gas pipelines around Doha.Operators look to guidance from the National Cyber Security Agency and regulators such as the Qatar Central Bank (QCB) for consistent expectations on resilience, incident response and coordination across energy and finance.
Data residency, NDMO and OT logging in the GCC
Saudi Arabia’s National Data Management Office (NDMO) and similar UAE and Qatar initiatives emphasise data residency and governance, especially for logs and monitoring data. OT teams therefore deploy local log collectors and use regional cloud regions like AWS Bahrain, Azure UAE Central or GCP Doha for analytics while keeping sensitive historian and OT log data within national boundaries wherever required.
Practical OT Network Segmentation and Monitoring for Brownfield Refineries
What is the most practical way to segment IT and OT networks in a brownfield refinery in the GCC?
The most practical approach is to move gradually from a flat network to a 3–4 zone model: Corporate IT, a DMZ, the control network and a safety/critical network, separated with firewalls and strict rules. Start by carving out a DMZ for historians and remote access, then tighten pathways into the control networks during planned maintenance windows so production is not disturbed.
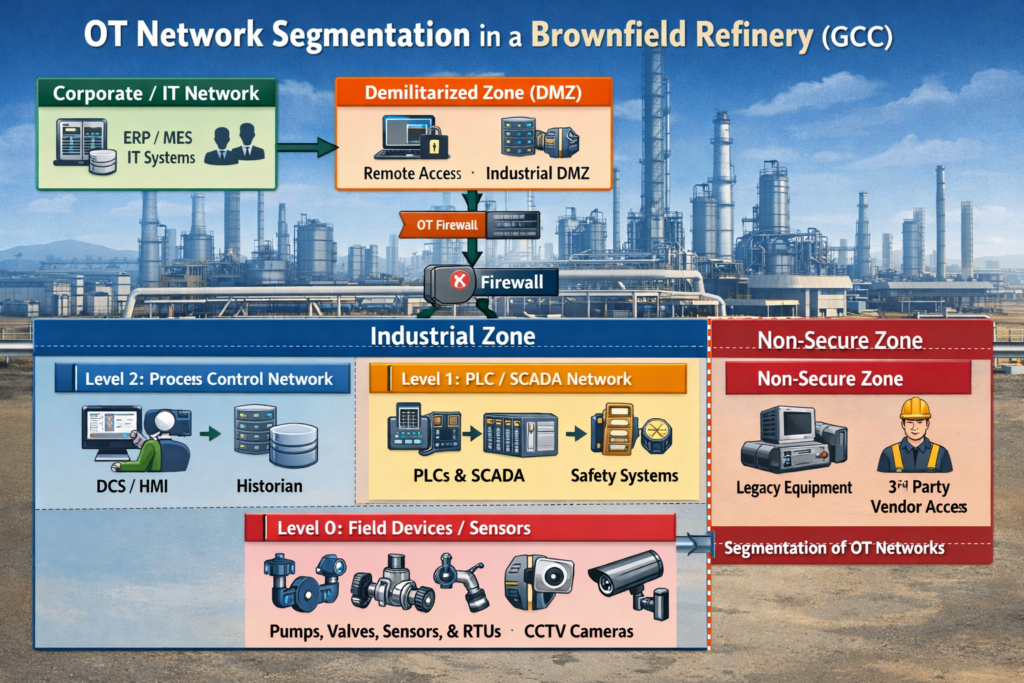
A simple reference architecture for separating IT and OT in existing plants
For refineries in Jeddah or Dubai, begin with clear boundaries: IT on one side, OT on the other, bridged by a DMZ hosting jump servers, patch repositories and historians. Legacy switches and vendor-owned equipment can stay in place initially, but routes between zones should be strictly controlled and logged.
DMZs, one-way gateways and secure remote access for pipelines and offshore platforms
For pipelines and offshore rigs, use firewalls, VPNs and hardened jump hosts to terminate all vendor and support access. High-value facilities may deploy data diodes for one-way data flow from OT to IT. Avoid direct RDP into control systems, shared accounts and unmanaged 4G/5G modems connecting RTUs.
OT SOC options.
Many operators now use managed OT SOC services that understand OTCC, UAE IA and Qatar’s national strategy instead of building everything in-house. ([Shieldworkz][9]) Hybrid models are common: log collection and some analytics on-prem in the plant, but 24/7 monitoring and threat hunting from regional SOCs similar to models already proven in regulated hubs like ADGM and DIFC.
OT Incidents, Ransomware and Business Impact on Oil & Gas in the GCC
Global OT attacks on pipelines and plants lessons for GCC operators
Global OT incidents show how malware in IT networks can force shutdowns of pipelines and plants because billing, scheduling or safety functions are affected. Lessons for GCC operators include the need for clear isolation points, tested manual fallback procedures and strong vendor governance.
Impact on safety, production and reputation for refineries and LNG terminals
In a refinery or LNG terminal, OT cyber attacks can lead to loss of view or loss of control, increasing the risk of misoperation, flaring or spills. Business impacts include lost production days, contract penalties, export disruption and heightened inspections by regulators and insurers. For national oil companies, a major OT incident quickly becomes a national-reputation issue.
Using playbooks and tabletop exercises to improve OT resilience
Plant-specific playbooks and regular tabletop exercises help teams understand how a ransomware outbreak on IT could affect OT, or how to respond to a compromised engineering station. In Riyadh, Dubai and Doha, many companies now run joint IT–OT drills that directly feed into improved segmentation, backup/restore procedures and vendor-access reviews.
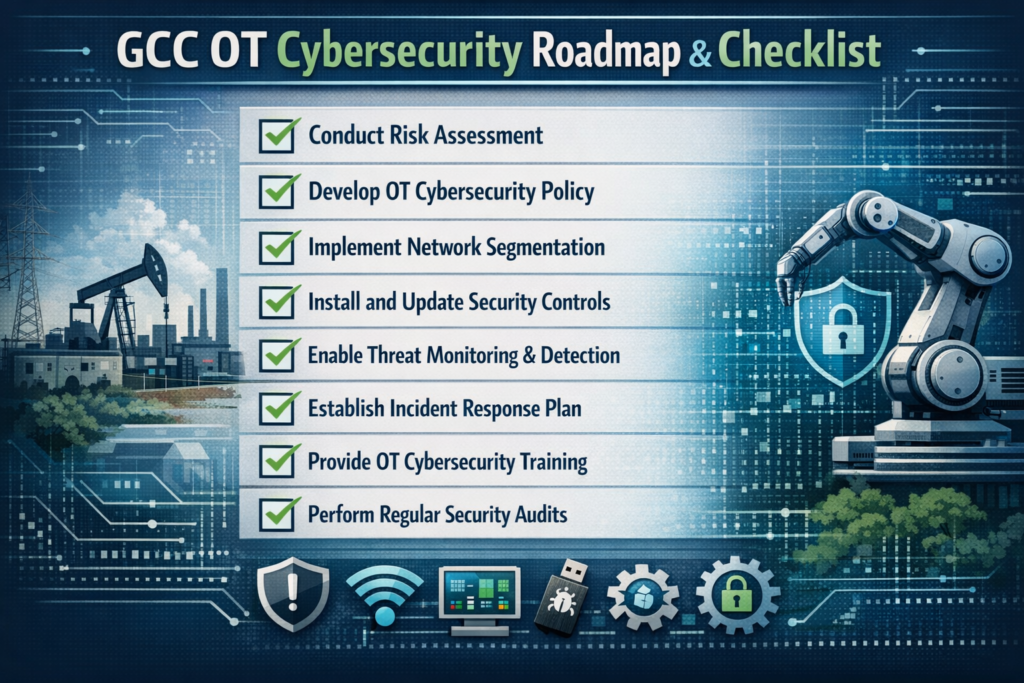
Roadmap and Checklist for OT Cybersecurity in GCC Oil & Gas
A simple OT cybersecurity maturity checklist for GCC plants
A practical roadmap can be staged as: Basic (asset inventory, network diagrams, password policies, backup of critical controllers), Intermediate (segmentation, secure remote access, centralised logging, OT incident playbooks) and Advanced (continuous monitoring, threat hunting, red teaming, full compliance mapping to OTCC, UAE IA and Qatar requirements).
Aligning IT, OT and leadership in Saudi, UAE and Qatar
Successful OT cybersecurity for oil and gas depends on aligning CISOs, plant managers, control engineers and vendors. RACI models, bilingual (Arabic/English) policies and joint governance forums help keep decisions consistent from the boardroom in Riyadh or Dubai to the control room at an LNG jetty in Doha.
When to bring in local OT security partners and managed services
GCC operators typically bring in specialised OT partners when facing regulatory deadlines, major expansions or repeated OT incidents. External experts can perform assessments, hardening projects and then offer ongoing managed OT SOC services tailored to regional data residency rules and sector regulators.
If you’re responsible for OT cybersecurity for oil and gas in Saudi Arabia, the UAE or Qatar, now is the time to turn regulatory pressure into a clear, practical roadmap. Start with the basics visibility, segmentation, hardening and playbooks and build towards full alignment with NCA OTCC-1:2022, UAE IA and Qatar’s cyber strategy.
Mak IT Solutions can help you review your current OT posture, prioritise quick wins and design a GCC-ready roadmap that fits your plants, vendors and budget. Reach out to discuss an OT readiness assessment, a brownfield segmentation design or a managed OT monitoring approach tailored to your operations.( Click Here’s )
FAQs
Q : Is OT cybersecurity now mandatory for Saudi oil and gas companies under OTCC?
A : Yes. For Saudi oil and gas operators, OTCC-1:2022 from the National Cybersecurity Authority sets mandatory minimum controls for OT and ICS environments that support critical infrastructure. While implementation can be phased, refineries, pipelines and petrochemical plants are expected to show progress in areas such as governance, risk assessments, asset inventory, network segmentation and secure remote access. Failure to comply can attract scrutiny or penalties, especially as Saudi Vision 2030 emphasises resilience of strategic sectors.
Q : How often should refineries and gas plants in the UAE review or update their OT security controls?
A : In the UAE, critical infrastructure entities are expected to treat cybersecurity as an ongoing lifecycle, not a one-time project. Under UAE Information Assurance and related NESA/TDRA guidance, regular risk assessments, audits and control reviews are recommended, typically at least annually for high-criticality sites. Refineries and gas plants should also re-evaluate OT controls after major changes new units, new vendors or significant incidents to stay aligned with national critical information infrastructure protection policies.
Q : Can Saudi and Qatar oil and gas operators send OT logs to cloud platforms while staying compliant with local data residency rules?
A : Yes, but they must design architectures carefully. Saudi operators follow NDMO and NCA guidance, which often favour keeping sensitive logs and historian data within the Kingdom or in approved regional zones, then sending aggregated or anonymised telemetry to cloud analytics where appropriate. Qatar’s national cyber strategy and digital agenda encourage cloud adoption while protecting critical infrastructure, so using regional regions such as AWS Bahrain, Azure UAE Central or GCP Doha with clear data-classification and retention policies can support compliance.
Q : What OT cybersecurity certifications are most valuable for engineers working on offshore platforms in the UAE and Oman?
A : Engineers supporting offshore platforms in the UAE and Oman benefit from certifications focused on industrial control systems, such as GICSP, IEC 62443 practitioner courses or vendor-specific OT security training. These complement general security certifications like CISSP or Security+. Many UAE energy companies align their programmes to UAE IA and NESA-style frameworks, so training that references NIST, ISO 27001 and ICS security guidance is well regarded.Combined with internal competency frameworks and the wider GCC focus on energy resilience, these certifications help engineers understand both cyber and process-safety impacts.
Q : How does OT cybersecurity differ between onshore fields in Kuwait and offshore assets in the wider GCC region?
A : Onshore fields in Kuwait, Saudi Arabia or the UAE often have more reliable terrestrial connectivity and easier physical access, but also larger attack surfaces due to contractors, shared facilities and integrated logistics. Offshore assets across the GCC rely heavily on satellite or microwave links and remote operations, which increases reliance on secure remote access, strong authentication and robust DMZ designs. Regulatory expectations from bodies like NCA, TDRA, QCB and others all emphasise protecting critical infrastructure, but offshore environments require extra focus on latency, bandwidth and safety-critical fallback modes.