OT Cybersecurity in Saudi Arabia: Why Convergence Is Hard
OT Cybersecurity in Saudi Arabia: Why Convergence Is Hard

OT Cybersecurity in Saudi Arabia: Why Convergence Is Hard
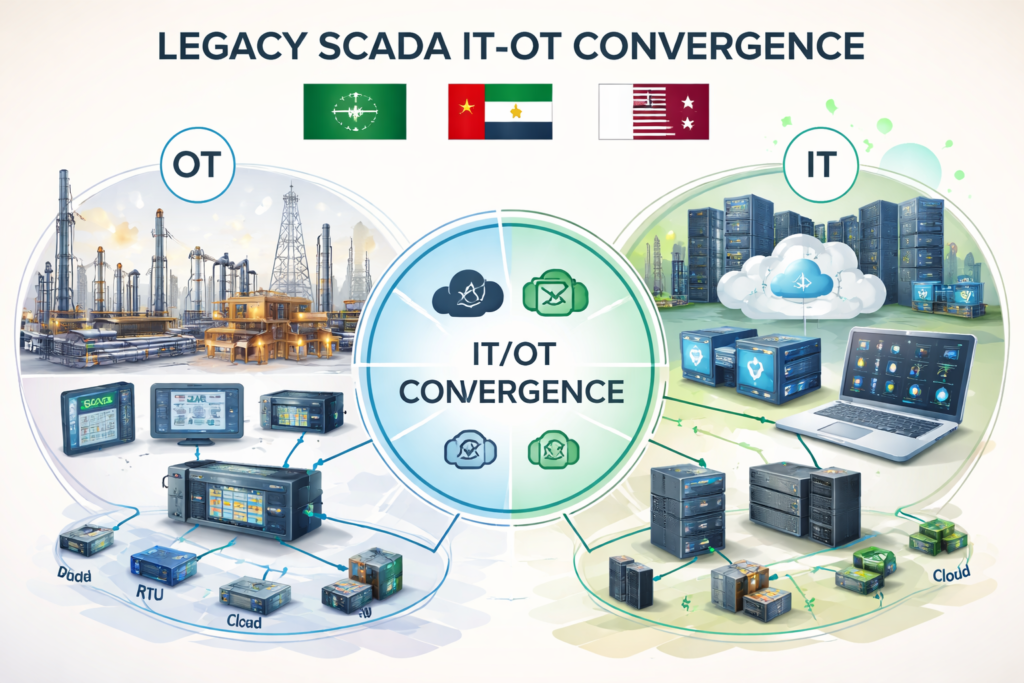
OT cybersecurity is one of the biggest reasons IT/OT convergence is still difficult for GCC industry in 2026. Across Saudi Arabia, the UAE, and Qatar, operators want smarter plants, connected warehouses, modern utilities, and data-driven infrastructure, but they cannot afford unsafe exposure, downtime, or weak governance.
That is the real issue behind many stalled modernization programs. In the GCC, OT cybersecurity is not just about blocking threats. It is about protecting uptime, safety, compliance, and trust while industrial environments become more connected.
Introduction
Across Riyadh, Dubai, Abu Dhabi, Jeddah, and Doha, operators are under pressure to modernize factories, utilities, ports, warehouses, and smart facilities without increasing cyber risk or interrupting operations.
On paper, IT/OT convergence sounds straightforward. In practice, it is slower, more expensive, and more sensitive than many business teams expect. Legacy systems, strict uptime requirements, third-party access, and regional compliance obligations all add friction.
For GCC businesses, this is no longer a narrow technical issue. It sits at the intersection of operational resilience, safety, governance, and regulator expectations. In Saudi Arabia, industrial operators must think carefully about how NCA controls apply inside OT environments. In the UAE, resilience and trust expectations shape how connected infrastructure is designed. In Qatar, regulated sectors increasingly treat cybersecurity as part of service continuity, not just IT hygiene.
What OT Cybersecurity Means in GCC Industry Today
OT cybersecurity vs IT security in industrial environments
OT cybersecurity protects industrial control systems, plant networks, field devices, and physical processes where a cyber incident can disrupt operations or create safety consequences.
Traditional IT security usually focuses on business systems, users, endpoints, and data confidentiality. OT security is different because the key question is not only whether data was exposed, but whether operations slowed down, stopped, or became unsafe.
In a refinery, utility site, logistics hub, airport, or smart facility, that difference matters. A plant outage or control-system issue can carry operational and financial consequences that go far beyond a standard IT incident.
Why GCC search favors “OT cybersecurity” over “IT/OT convergence”
In the GCC, buyers often search for OT cybersecurity because it matches the real concern inside leadership teams: how to modernize without creating operational risk.
“IT/OT convergence” sounds strategic. “OT cybersecurity” sounds immediate. It speaks directly to the budget owner who has to protect uptime, justify investment, and reassure leadership that digital transformation will not introduce unsafe exposure.
That is especially true in sectors like energy, logistics, manufacturing, utilities, ports, airports, retail facilities, and government-linked infrastructure.
Where OT security shows up in Saudi, UAE, and Qatar sectors
In Saudi Arabia, OT security is central to critical infrastructure, industrial expansion, smart manufacturing, and utility modernization.
In the UAE, it shows up in smart operations, ports, airports, utilities, real estate technology, and connected facilities where continuity and trust are board-level concerns.
In Qatar, OT security shapes decisions around regulated infrastructure, industrial systems, and digital service environments that require tightly controlled integration.
Cloud-region choices also influence these decisions. Regional hosting options in Bahrain, the UAE, and Doha make it easier for GCC organizations to design architectures around latency, governance, and trust expectations.
Why IT/OT Convergence Is So Hard in 2026
Legacy PLCs, SCADA, and industrial control systems were not built for modern integration
Most PLCs, SCADA environments, historians, and field devices were built for reliability and longevity, not for open, always-on connectivity.
They were not designed for cloud-native observability, zero-trust assumptions, or constant API-based integration. So when a Riyadh manufacturer, a Dubai warehouse operator, or a Doha infrastructure team adds analytics, remote monitoring, or IIoT layers, the old environment often becomes the bottleneck.
The challenge is rarely one system alone. It is the mix of aging assets, undocumented dependencies, and fragile connectivity paths that makes secure integration difficult.
Safety, uptime, and patch-cycle constraints slow modernization
In enterprise IT, fast patching often signals maturity.
In OT, a poorly timed patch can interrupt a production line, affect a control process, or create unnecessary operational risk. That is why modernization moves more slowly in industrial environments. Every change must be tested against uptime, maintenance windows, and safety requirements.
This leads to longer approval cycles, slower remediation, and heavier reliance on compensating controls such as segmentation, monitoring, restricted access, and change governance.
IT and OT teams still operate with different goals, tools, and risk models
IT teams are usually pushed toward standardization, visibility, and rapid remediation.
OT teams are measured on continuity, predictability, and safe operations. Those priorities are both valid, but they are not the same. That difference affects tooling, decision-making, incident response, and even the pace of modernization.
In many GCC environments, the governance gap is larger than the technical gap. Convergence slows down not only because systems are hard to connect, but because teams do not always agree on who owns risk, who approves change, and what “secure enough” really means.
The GCC Compliance Layer Making Convergence More Complex
How Saudi NCA OTCC and ECC shape OT modernization decisions
Saudi Arabia has one of the clearest compliance signals in the region. OTCC extends the broader ECC baseline and raises the bar for OT and ICS environments.
That changes how industrial modernization is planned. Convergence cannot be treated like a normal IT integration project. It has to show stronger control maturity, governance, accountability, and operational protection from the start.
When industrial data begins moving into enterprise platforms, reporting layers, or analytics environments, data responsibility also becomes more important. That makes architectural decisions more sensitive in Saudi projects than many vendors initially assume.
How UAE governance and resilience expectations influence OT security programs
In the UAE, OT security is strongly shaped by resilience, trust, and governance expectations.
For operators in Dubai and Abu Dhabi, it is not enough to build a connected environment that works. The environment also needs to be governable, auditable, and resilient enough to support critical or customer-facing services.
That is why UAE projects often place heavier emphasis on access control, continuity planning, vendor oversight, and trust in operational data flows.
How Qatar’s regulated digital infrastructure environment affects industrial integration
Qatar’s model is especially relevant in regulated sectors and critical-service environments.
In Doha, modernization decisions often reflect a controlled-risk mindset. Vendor discipline, data governance, continuity, and technology-risk management all influence how OT systems connect to broader digital platforms.
This means industrial integration in Qatar often moves carefully. The goal is not just faster connectivity. It is controlled modernization that does not weaken service reliability or trust.

The Biggest OT Cybersecurity Risks Created by Convergence
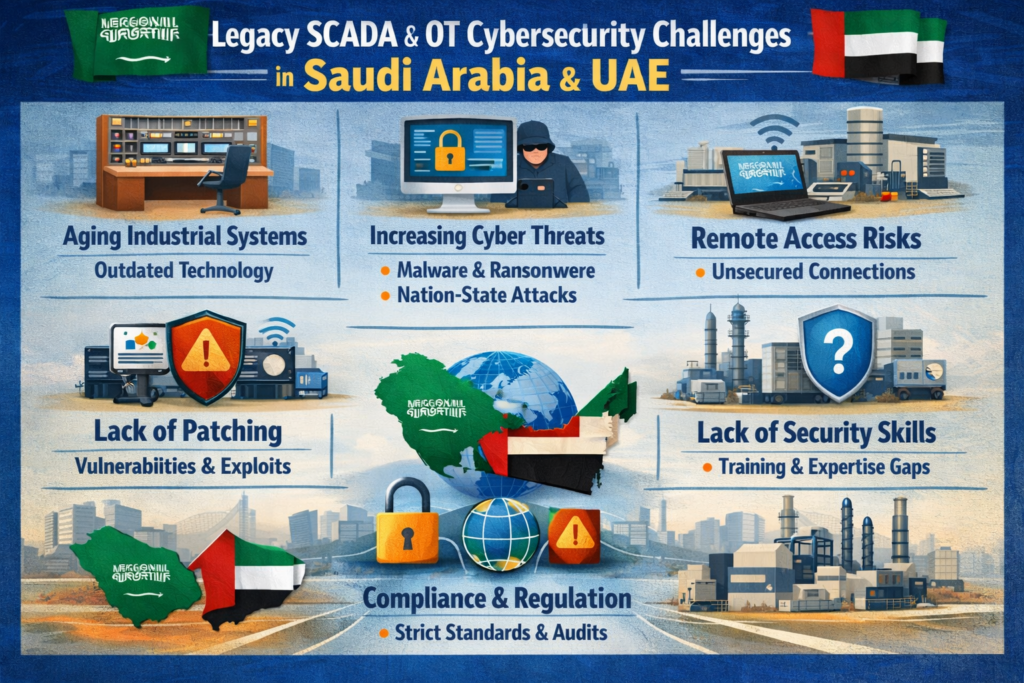
Expanded attack surface from IIoT, remote access, and connected operations
Every new sensor gateway, engineering workstation, remote-access path, cloud connector, or third-party integration expands the attack surface.
The business value may be clear, but the exposure grows quickly. A warehouse automation project, smart utility program, or connected port environment can become far more reachable than leadership expected.
That is often where risk accelerates faster than governance.
Poor OT asset visibility and weak segmentation increase operational risk
You cannot secure what you cannot clearly see.
Many operators still do not have complete OT asset visibility, reliable zone mapping, or strong industrial segmentation. Without that foundation, it becomes harder to detect unauthorized devices, understand exposure paths, or contain an incident before it affects production or service delivery.
In practice, visibility and segmentation are often the first real maturity test in an OT security program.
Vendor interoperability and third-party access create blind spots
Convergence introduces more OEMs, integrators, managed-service providers, maintenance partners, and external support teams into the environment.
That creates convenience, but it also creates blind spots. Without strict access control, logging, approval workflows, and vendor governance, third-party access can undermine an otherwise strong security program.
For many GCC operators, this is one of the most overlooked risks in modernization.
How Saudi, UAE, and Qatar Operators Approach the Problem Differently
Saudi Arabia.
In Saudi Arabia, OT modernization is often compliance-led before it is expansion-led.
Operators in Riyadh, Jeddah, and major industrial zones often begin with assessments, control alignment, and risk reduction before scaling connectivity. That approach may look slower at first, but it usually creates a stronger base for long-term convergence.
UAE.
In the UAE, the emphasis is often on resilience, customer trust, and operational excellence.
In Dubai and Abu Dhabi, convergence works best when it improves visibility and service performance without weakening governance. Smart operations matter, but they have to be supported by clear accountability and strong recovery planning.
Qatar.
In Qatar, operators often take a more controlled path to integration, especially in regulated or high-trust environments.
In Doha, data residency, vendor assurance, continuity, and governance can carry more weight than speed alone. That makes projects more deliberate, but often better aligned with long-term operational confidence.
What a Practical OT-IT Convergence Strategy Looks Like in GCC
Start with OT asset visibility, segmentation, and risk assessment
The first step is to map assets, communication paths, critical processes, and remote-access dependencies.
The second step is to segment industrial networks based on operational role and risk.
The third step is to assess which systems can safely connect to analytics, enterprise dashboards, cloud platforms, or mobile workflows without creating unnecessary exposure.
This is often the point where organizations realize they need stronger business intelligence services, web development support, or a more secure data foundation before exposing operational data to wider business users.
Build an OT governance model shared by operations, IT, and security leaders
A practical convergence model needs shared decision-making across operations, IT, and cybersecurity.
That includes clear ownership for change control, incident response, third-party access, escalation paths, and risk acceptance. In GCC environments, it also helps when reporting, dashboards, and internal workflows are bilingual and easy for both technical and non-technical stakeholders to use.
For businesses rolling out portals, apps, or digital operational layers, services like React development, mobile app development, and Next.js development should support OT governance instead of running as a disconnected digital track.
Align architecture with Arabic UX, data residency, and regional trust requirements
A Riyadh-based operator may need architecture that reflects stricter governance thinking around critical workflows. A Dubai business with connected warehouses may care more about multilingual visibility and resilient day-to-day operations. A Doha organization may prioritize controlled hosting patterns and stronger vendor assurance.
That is why OT-IT convergence in the GCC must be designed around.
Data residency expectations
Bilingual or Arabic-friendly user experience
Role-based access and governance
Trusted data movement between OT and enterprise systems
Resources like data analytics and business intelligence in the Middle East and SEO-oriented content strategy can support broader digital maturity, but only when the operational security foundation is already in place.
Best Practices for Reducing Risk Without Slowing Transformation
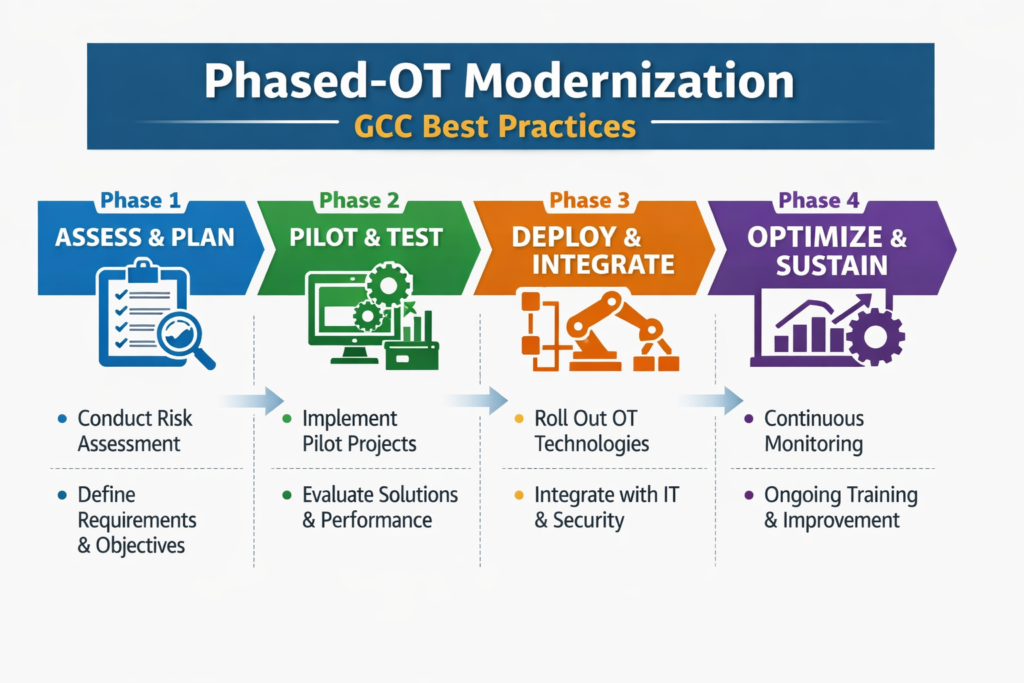
Prioritize phased modernization instead of full-stack replacement
Full replacement is not always realistic for uptime-sensitive environments.
A phased model is usually safer.
Replace what is unsupported or clearly unsafe first.
Isolate systems that cannot yet be replaced.
Harden remote access and monitoring.
Connect only the systems that provide clear operational value.
Expand integration gradually once controls are proven.
Use IEC 62443-style thinking alongside local GCC controls
Global industrial-security frameworks can provide useful structure, especially for segmentation, zones, conduits, and lifecycle thinking.
But in the GCC, local realities still decide what is practical. Saudi, UAE, and Qatar operators need to balance international good practice with local compliance expectations, trust requirements, and residency considerations.
Choose partners who understand industrial operations, not just enterprise IT
The right partner should understand maintenance windows, uptime sensitivity, integration risk, and the operational realities of industrial environments.
That matters more than polished transformation language. In practice, a partner that understands plant operations, warehouse systems, utility workflows, and Arabic-speaking stakeholder environments will usually add more value than a generic enterprise integrator.
For connected portals and digital layers, Webflow development, Shopify development, or broader digital marketing services only make sense when the underlying OT governance model is already sound.
Final Take
OT cybersecurity is a core reason IT/OT convergence remains difficult for GCC industry in 2026. Legacy industrial systems, uptime pressure, compliance obligations, vendor access risks, and governance gaps all slow down modernization across Saudi Arabia, the UAE, and Qatar.
The organizations making real progress are not the ones moving fastest. They are the ones building convergence on a stronger foundation of OT asset visibility, segmentation, governance, and regional trust requirements.
If your team is planning connected operations in the GCC, start there first. Secure modernization is usually phased, deliberate, and operationally grounded.
Mak It Solutions can help design secure digital layers around complex operations, from data and dashboards to web, mobile, and platform experiences. Explore the relevant services, contact the team, or request a custom GCC strategy built around your operational reality.
FAQs
Q : Is OT cybersecurity mandatory for critical infrastructure operators in Saudi Arabia?
A : For many Saudi organizations linked to national or critical operations, OT cybersecurity is no longer optional in practical terms. OT controls increasingly shape audit readiness, project approval, vendor qualification, and operational governance. For industrial operators, OT security has become part of doing business safely.
Q : How is OT security different from ICS security in the UAE market?
A : ICS security usually refers more narrowly to control systems like PLCs, SCADA environments, and plant-level processes. OT security is broader and can include industrial networking, connected facilities, remote access, edge devices, and resilience governance. In the UAE, that broader view matters because connected operations are often evaluated through a trust and continuity lens.
Q : What are the main OT compliance concerns for Qatar infrastructure operators?
A : The main concerns usually include technology risk, third-party access, continuity, data governance, and recovery planning. In regulated environments, the challenge is not just connecting systems securely. It is proving that modernization will not weaken reliability, control, or trust.
Q : Can GCC manufacturers modernize legacy SCADA systems without full replacement?
A : Yes, and in many cases that is the most realistic approach. Phased modernization lets operators improve visibility, segmentation, remote-access security, and monitoring before replacing legacy SCADA outright. That is often safer, less disruptive, and better aligned with real maintenance cycles.
Q : How does data residency affect OT-IT convergence projects in Saudi Arabia and the UAE?
A : Data residency affects where industrial data is stored, processed, and shared once OT systems start feeding dashboards, cloud tools, or multi-site workflows. In Saudi Arabia and the UAE, many organizations prefer architectures that keep sensitive operational data within regional or clearly governed environments. That helps support trust, compliance, and operational control.


