Platform Engineering Guide for Regulated Teams
Platform Engineering Guide for Regulated Teams

Platform Engineering Guide for Regulated Teams
Platform engineering is becoming the default operating model for teams that need to ship quickly without losing control. In 2026, platform engineering means giving developers self-service paths, built-in security guardrails, and compliance-ready workflows so delivery gets faster while risk stays manageable.
At a practical level, that means developers should be able to create services, provision environments, deploy code, and follow policy without opening a trail of tickets. The platform team turns infrastructure, security, and delivery standards into reusable products the rest of engineering can actually use.
For engineering leaders in the US, UK, and Germany, that shift matters even more. Regulated delivery is no longer just about adding more approvals at the end. It is about making the safe path the easiest path from day one.
What Platform Engineering Means in 2026
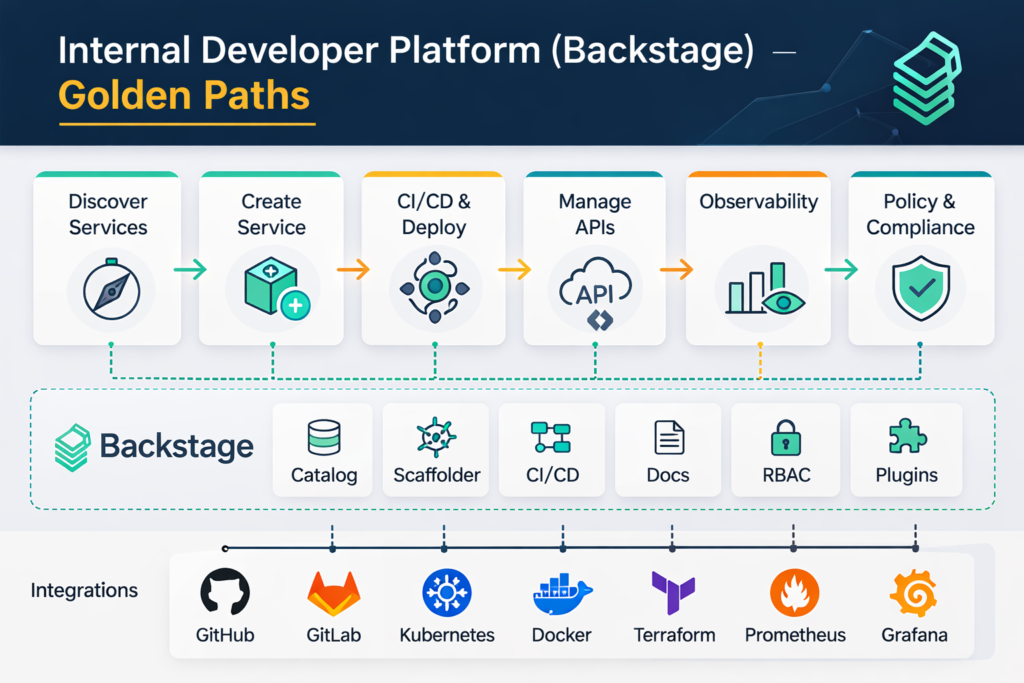
Platform engineering is the discipline of designing and building toolchains and workflows that enable self-service for software teams. Usually, that shows up as an internal developer platform, service catalog, reusable templates, policy checks, and automated delivery workflows wrapped in a product mindset.
Platform engineering vs. DevOps vs. SRE
DevOps is still the broader culture of shared ownership across development and operations. SRE is more focused on reliability, service levels, incident response, and operational resilience. Platform engineering takes those principles and turns them into a usable product layer, with paved roads teams can adopt without reinventing the same patterns every quarter.
That distinction matters because most organizations do not struggle with a lack of tools. They struggle with inconsistency. Platform engineering solves that by standardizing how teams build, deploy, and operate software, while still leaving room for sensible exceptions.
Why internal developer platforms matter
An internal developer platform gives teams self-service access to common workflows such as service creation, environment setup, secrets references, deployment pipelines, and operational metadata. Backstage, for example, describes its software catalog as a centralized system for ownership and metadata across services, websites, libraries, data pipelines, and other software components.
The payoff is lower cognitive load. Developers spend less time hunting for the right repo settings, pipeline steps, or compliance checks, and more time shipping product work.
Why golden paths and platform teams matter
Golden paths are opinionated defaults for common journeys: starting a new service, deploying to production, rotating secrets, or publishing artifacts safely. They do not remove flexibility. They remove avoidable friction.
That matters in cloud-native environments where the ecosystem keeps expanding. As of March 2026, CNCF lists 34 graduated projects, 37 incubating projects, and 147 sandbox projects. Without platform standards, that amount of choice quickly becomes delivery drag.
Why Engineering Leaders Are Investing in Platform Engineering
The strongest case for platform engineering is simple: teams want faster delivery, but they also need traceability, repeatability, and stronger controls. Leaders are not looking for another dashboard. They are trying to fix slow onboarding, fragmented pipelines, inconsistent security practices, and rising audit pressure.
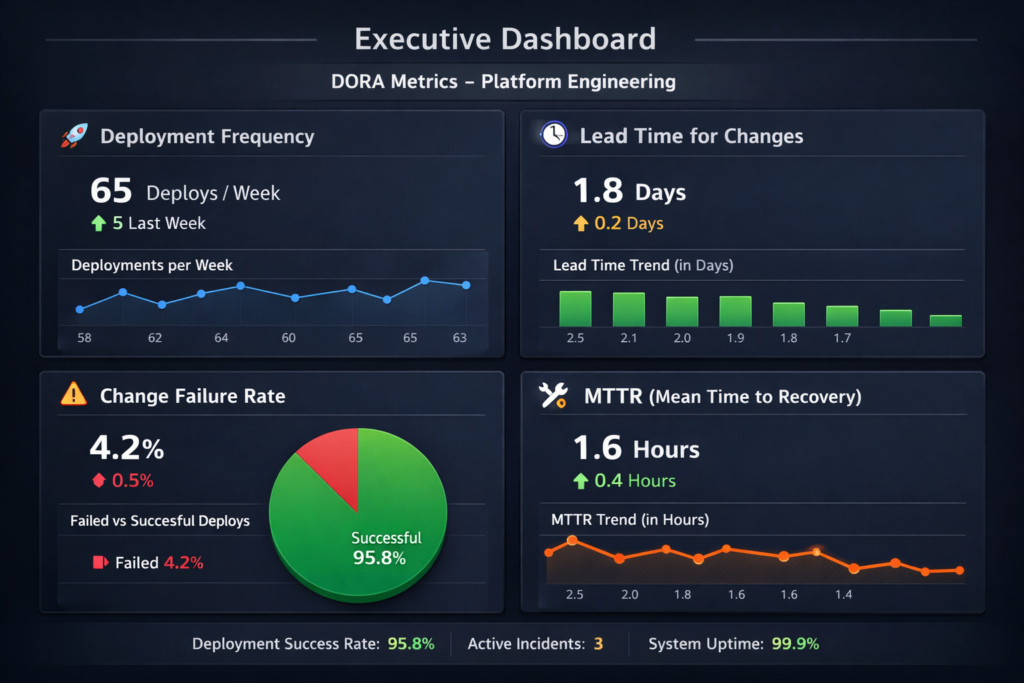
DORA research keeps reinforcing the value of fundamentals here. Google Cloud’s DORA findings say high-quality documentation is associated with 25% higher team performance, and faster code reviews are linked to a 50% improvement in software delivery performance. Those are exactly the kinds of gains a good platform team can support through templates, docs, and standardized workflows.
Where platform engineering pays off fastest
The biggest wins usually show up in a few places:
New service creation becomes repeatable instead of tribal knowledge.
CI/CD pipelines stop drifting across teams.
Security controls move into automation instead of ticket queues.
Audit evidence is easier to capture because workflows are standardized.
Onboarding gets faster because engineers have one front door.
For organizations balancing APIs, web apps, mobile releases, and analytics across multiple teams, that consistency compounds quickly.
Core Components of a Modern Internal Developer Platform
A strong internal developer platform should feel simple on the surface and strict underneath. Developers need a clean path. Security and compliance teams need identity, auditability, and policy enforcement.
Developer portal and service catalog
The portal is the front door. The service catalog provides ownership, metadata, dependencies, and visibility across the software estate. Backstage’s model is useful here because it treats metadata and ownership as first-class platform features, not documentation afterthoughts.
Reusable golden paths
Golden paths should cover the most common and highest-friction workflows, such as.
Creating a new API service
Bootstrapping a frontend app
Provisioning a non-production environment
Releasing to production with approvals
Rolling back safely
The goal is not to support every edge case on day one. It is to make the most common path fast, safe, and obvious.
Self-service infrastructure and templates
Templates should handle the boring but critical parts automatically:
Repository defaults
CI workflow setup
Logging and telemetry baselines
Secrets references
Runtime defaults
Required policy checks
This is where platform engineering starts to feel like leverage instead of governance theater.
Identity, secrets, and deployment governance
Mature platforms rely on identity-based access, short-lived credentials, and auditable deployment controls. That is the difference between “secure in theory” and secure in a way teams will actually use at scale. GitHub explicitly recommends OpenID Connect to harden deployments, and its guidance on reusable workflows shows how teams can standardize secure deployment steps across repos.
How to Secure CI/CD Without Slowing Delivery
Secure CI/CD is not about adding more manual gates. It is about improving automation so the pipeline itself produces stronger evidence and fewer hidden risks.
Secure the workflow surface first
Start with the basics.
Minimize repository and environment permissions
Lock down runners for sensitive workloads
Pin third-party actions to trusted versions
Separate production environments with protection rules
Reduce or eliminate long-lived secrets
GitHub’s OIDC guidance exists for a reason: replacing stored cloud credentials with short-lived identity-based access cuts a major class of CI/CD risk.
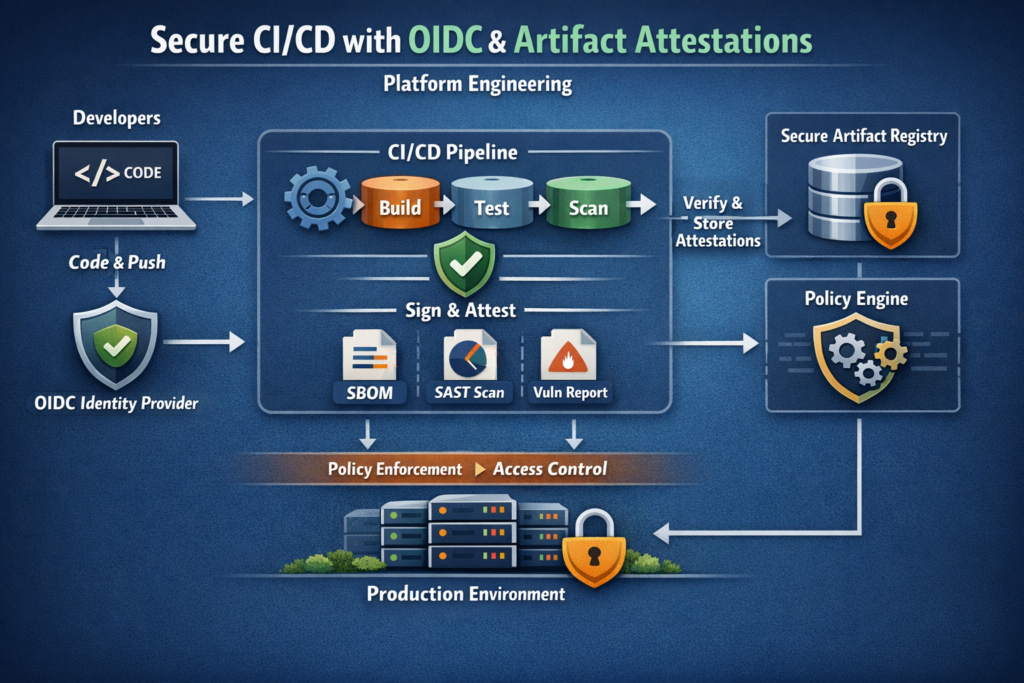
Add provenance and artifact attestations
Artifact attestations help establish where and how software was built. GitHub describes them as cryptographically signed claims that establish build provenance, and SLSA defines provenance as verifiable information about where, when, and how an artifact was produced.
That becomes especially important when teams rely on open source packages, shared runners, and third-party actions. You need a clear story for artifact integrity, not just a successful pipeline run.
Platform Engineering in US, UK, and Germany Compliance Contexts
The delivery model may be shared, but the compliance context is not identical across markets. This is where platform engineering becomes especially valuable: you can standardize the workflow while adjusting the controls.
United States
US teams often map software delivery controls to the NIST Secure Software Development Framework. NIST describes SSDF as a core set of high-level secure software development practices that can be integrated into each SDLC implementation. For healthcare, the HIPAA Security Rule sets administrative, physical, and technical safeguards for electronic protected health information. For payment environments, PCI DSS provides baseline technical and operational requirements to protect payment account data.
United Kingdom
For UK teams, data handling and accountability are central. The ICO’s UK GDPR guidance emphasizes core data protection principles, including integrity, confidentiality, and accountability. In health-related delivery, the NHS Data Security and Protection Toolkit is a required self-assessment for organizations with access to NHS patient data and systems.
Fintech is another clear use case. Open Banking Limited reported that by December 2025, the UK had reached 16.5 million user connections, and open banking payments hit 351 million transactions in 2025, up 57% year over year. When usage is operating at that scale, resilience and controlled delivery become board-level concerns.
Germany and the wider EU
In Germany and the EU, GDPR pushes organizations toward stronger accountability, security, and risk-aware data handling. BaFin’s MaRisk framework remains a key reference point for risk management in German banking supervision, and it reinforces the need for controlled, auditable operating models. For delivery teams in Berlin, Frankfurt, Munich, or cross-border EU environments, that usually means stricter access control, clearer logging, and careful residency decisions.
Build, Buy, or Standardize?
This is where many platform programs lose momentum. They try to build everything.
A better rule is to build the differentiating glue, buy the commodity capabilities, and standardize aggressively where custom complexity does not create business value.
A practical evaluation framework looks like this:
| Decision Area | Build | Buy | Standardize |
|---|---|---|---|
| Developer portal experience | When workflows are unique | When speed matters most | Always |
| CI/CD orchestration | Rarely | Often | Yes |
| Identity and secrets | Rarely | Usually | Yes |
| Compliance evidence capture | Sometimes | Often | Yes |
| Service templates and golden paths | Usually | Sometimes | Yes |
Backstage is often useful when you need a unifying portal across several tools. GitHub or GitLab can be strong consolidation points when teams want fewer surfaces. The right answer depends less on vendor branding and more on ownership clarity and operating model maturity.
How to Start a Platform Engineering Program in 90 Days
The fastest way to fail is trying to platform everything at once. The better move is to pick one painful journey and make it dramatically better.
A practical 90-day sequence
Choose one high-friction workflow
Good starting points include new service creation, environment provisioning, or production promotion.
Define one golden path
Include templates, permissions, required checks, and rollback expectations.
Embed guardrails early
Add identity-based access, policy checks, audit logging, and evidence capture from the start.
Measure adoption and outcomes
Track onboarding time, deployment consistency, failed changes, and restore readiness.
Expand only after proof
Once one journey works, move to the next highest-friction path.
Most teams see early value when the platform removes waiting, cuts exceptions, and makes safer delivery the default rather than the special case.

Key Takeaways
Platform engineering turns DevOps principles into reusable delivery products.
The best internal platforms reduce cognitive load while improving control.
OIDC, artifact attestations, and provenance are now core CI/CD security patterns.
DORA metrics matter more when teams can act on them, not just report them.
US, UK, and Germany programs benefit most when compliance requirements are built into workflows instead of handled through manual exceptions.
Wrap It Up
If your teams are still shipping through a patchwork of scripts, tickets, and one-off exceptions, platform engineering is usually the clearest way to regain speed without giving up governance. Start small, standardize one journey, and treat the platform like a product. That is how faster, safer delivery becomes sustainable.
You can also pair this strategy with related service areas such as web development services, mobile app development services, or business intelligence services when the delivery model spans applications, data products, and customer-facing platforms.( Click Here’s )
FAQs
Q : What is platform engineering in simple terms?
A : Platform engineering is the practice of building internal tools, workflows, and guardrails that let developers ship software without managing every infrastructure and compliance detail themselves. Think of it as creating a paved road for delivery.
Q : How is platform engineering different from a developer portal?
A : A developer portal is usually the interface developers interact with. Platform engineering is the broader operating model behind it, including automation, templates, policy, identity, provisioning, and delivery controls.
Q : Can smaller SaaS teams benefit from platform engineering?
A : Yes, as long as the scope stays tight. A smaller team does not need a large platform department to get value; one strong golden path can reduce rework, onboarding friction, and deployment inconsistency.
Q : What should a platform team measure first?
A : Start with adoption, onboarding time, deployment frequency, change failure rate, and restore readiness. Those metrics show whether the platform is actually reducing friction and improving reliability.
Q : Is this only for heavily regulated companies?
A : No, but regulated teams often see the fastest return because inconsistency is more expensive for them. Even non-regulated SaaS teams benefit from better self-service, clearer ownership, and safer defaults.


