Policy as Code DevSecOps for Regulated Teams
Policy as Code DevSecOps for Regulated Teams
Policy as Code DevSecOps for Regulated Teams
Policy as code DevSecOps gives regulated engineering teams a practical way to enforce security and compliance without slowing every release down. Instead of relying on static documents, manual sign-offs, and spreadsheet-based audit prep, teams define rules in version-controlled code and enforce them automatically in pull requests, CI pipelines, infrastructure changes, and Kubernetes admissions. OPA describes itself as a general-purpose policy engine that unifies policy enforcement across the stack, while Kyverno applies policy directly inside Kubernetes as a dynamic admission controller.
In simple terms, policy as code DevSecOps means your compliance rules stop living in PDFs and start running where engineers already work. That matters across the US, UK, and EU because continuous enforcement helps reduce drift, improves evidence collection, and makes audit conversations easier when you are dealing with SOC 2, HIPAA, PCI DSS, UK GDPR, or DSGVO expectations.
For teams in New York fintech, London health tech, or Berlin SaaS, the pressure looks familiar: ship fast, prove control, and stay audit-ready. Policy as code is how those goals start to work together instead of fighting each other.
What Is Policy as Code in DevSecOps?
Policy as code in DevSecOps is the practice of writing governance, security, and compliance rules as machine-readable code, storing them in version control, and evaluating them automatically throughout the delivery lifecycle. The rule might be simple, such as “deny public storage,” or more context-aware, such as “require approval for production changes touching regulated workloads.”
That shift sounds small, but it changes how teams operate. Instead of discovering violations during audit prep, you catch them when someone opens a pull request, changes Terraform, or tries to deploy an unsafe Kubernetes manifest.
Policy as code vs. compliance as code
The two terms overlap, but they are not identical.
Policy as code focuses on decisions.
What is allowed
What is blocked
What needs approval
What should be flagged for review
Compliance as code is broader.
Control mapping
Evidence collection
Reporting
Exception workflows
Audit support
In practice, policy as code is one of the core engines behind compliance as code.
Why Continuous Compliance Matters
Modern CI/CD moves too quickly for quarterly checks to be enough. A team can change infrastructure, containers, permissions, secrets handling, and deployment settings dozens of times between formal reviews. If controls only get tested before an audit, the organization is measuring documentation quality more than day-to-day control discipline.
That is one reason continuous compliance is gaining traction. IBM reported that the global average cost of a data breach reached USD 4.88 million in 2024. For regulated teams, the business case is not just security. It is also rework, customer trust, enterprise sales readiness, and lower audit friction.
What continuous compliance actually improves
When done well, continuous compliance helps teams.
Reduce configuration drift
Catch risky changes earlier
Build cleaner audit evidence over time
Cut down on last-minute remediation
Make exceptions visible and time-bound
It also creates a shared operating model for security, platform, and GRC teams. Everyone can see which controls exist, where they run, and what evidence they produce.
How Policy as Code Works Across the Pipeline
The strongest policy as code programs do not wait until deployment. They enforce guardrails across the software lifecycle.
Pull requests and branch protection
Start at the merge layer. GitHub branch protection can require approving reviews and passing status checks before pull requests are merged. That makes it a solid foundation for control enforcement in engineering workflows.
Examples:
Require at least one or two approvers for regulated services
Block merges when security scans fail
Enforce change-ticket references for production-impacting changes
CI/CD pipeline checks
Next, evaluate policies during CI jobs. This is where teams typically scan:
Terraform and other IaC
Kubernetes manifests
Container image rules
Secrets exposure
Encryption defaults
Tagging and ownership standards
The point is simple: risky builds should fail before they become deployment problems.
Deployment gates and runtime enforcement
Finally, enforce at deployment and cluster admission time. This matters most in cloud-native environments, where speed and scale make manual review unreliable.
Typical deployment-stage controls include
Denying privileged containers
Blocking latest image tags
Requiring approved registries
Enforcing non-root execution
Restricting public exposure
Preventing unapproved infrastructure changes
Best Tools for Policy as Code DevSecOps
No single tool covers everything. The best setup usually combines flexible policy engines with workflow and platform enforcement.
OPA and Rego
OPA is a strong choice when you want one policy engine across APIs, CI/CD, infrastructure workflows, and cloud-native environments. Its Rego language is built for evaluating structured inputs such as API requests, IaC files, and configuration data.
OPA is especially useful when.
You want reusable policy logic across multiple systems
Your teams need custom decisions beyond Kubernetes
You want policy tests and versioning in Git
Kyverno
Kyverno is especially attractive for Kubernetes-first teams. It runs as a dynamic admission controller and can validate, mutate, and scan cluster resources.
It fits well when.
Most enforcement is inside Kubernetes
Teams prefer Kubernetes-native policy management
You want fast adoption without building everything around custom integrations
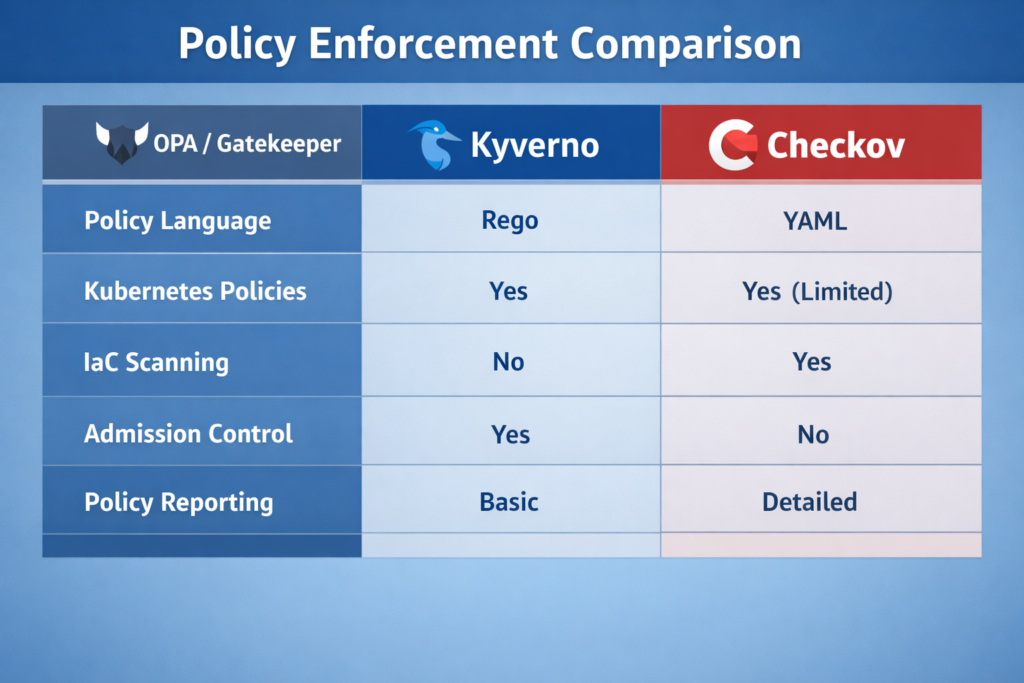
Checkov, GitLab, and workflow-level governance
Tools like Checkov are useful earlier in the pipeline for infrastructure scanning before deployment. GitLab also frames compliance automation around pipeline enforcement, continuous monitoring, and auditability, which is useful for teams that want policy embedded in delivery workflows rather than handled as a separate governance function. GitLab’s 2024 report was based on a survey of more than 5,000 professionals worldwide.
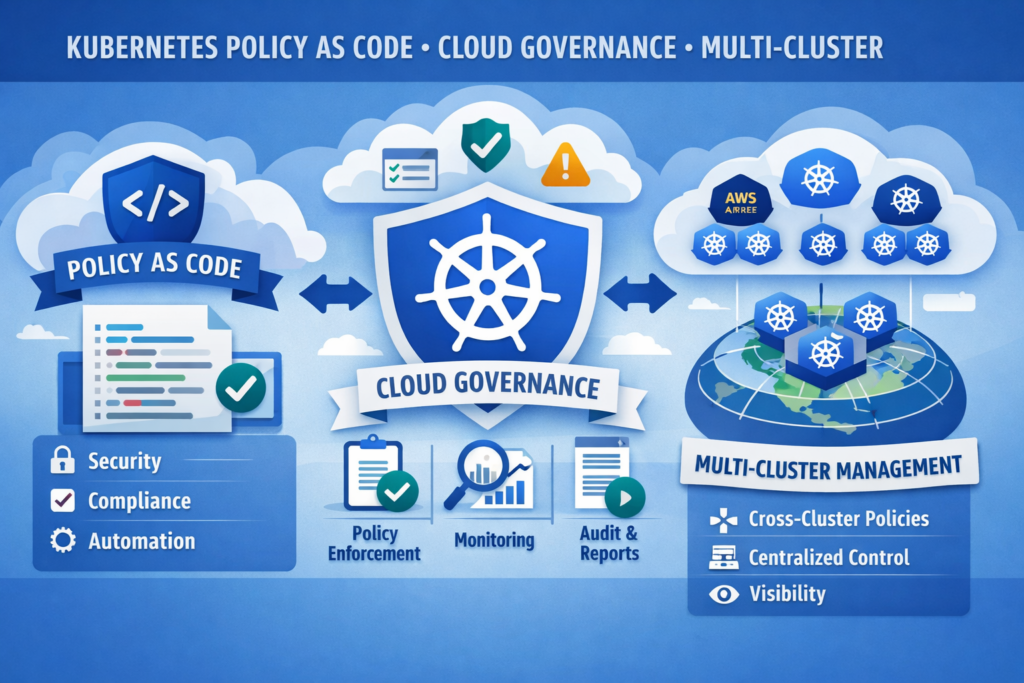
Kubernetes Policy as Code for Cloud Governance
Kubernetes is where policy as code often delivers the clearest early win. Clusters change quickly, misconfigurations are easy to miss, and security mistakes can spread across environments fast.
CNCF reported that 66% of potential or actual consumers were using Kubernetes in production in 2023, and its later research said 80% of organizations were running Kubernetes in production in 2025. The same 2025 CNCF research said 60% of organizations were using CI/CD for most or all applications.
That makes admission-time guardrails much more than a niche concern.
Common Kubernetes policies
Common examples include:
Deny privileged pods
Require approved image registries
Block hardcoded secrets
Enforce resource limits
Require network policies
Prevent hostPath mounts
Require non-root containers
Multi-cluster governance across the US, UK, and EU
For organizations operating across AWS, Azure, and Google Cloud, consistency matters just as much as enforcement. A central policy repository, clear exception workflow, and per-cluster reporting can make governance more defensible across regions such as London, Frankfurt, Dublin, Amsterdam, or US production hubs.
That regional view matters for regulated teams. UK buyers may focus more on governance and auditability under UK GDPR expectations, while Germany and wider EU teams often ask harder questions about cloud controls, data handling, and documented exceptions.
Policy as Code in Regulated Industries
Regulated environments adopt policy as code because manual control enforcement becomes brittle at scale.
Fintech
Fintech teams often automate controls around:
Encryption defaults
Segmentation
Access restrictions
Image signing
Terraform standards
Approval requirements for payment-related services
For firms serving Germany, BaFin guidance adds pressure around outsourcing governance, data security, and auditability in cloud environments.
Healthcare
Healthcare teams usually prioritize:
Secure build paths
Least privilege
Logging and traceability
Environment separation
Secrets handling for sensitive workloads
US organizations map these controls to HIPAA Security Rule expectations, while UK suppliers may face stricter evidence expectations during procurement or assurance reviews.
SaaS and enterprise software
SaaS vendors selling into the UK and EU often use policy as code to support:
Privacy-by-design controls
Region-aware deployment rules
Retention guardrails
Cross-border evidence readiness
Customer security questionnaire responses
The EU AI Act entered into force on August 1, 2024, with staged application dates following after that, so teams building AI-enabled delivery platforms increasingly need governance that is documented and testable.

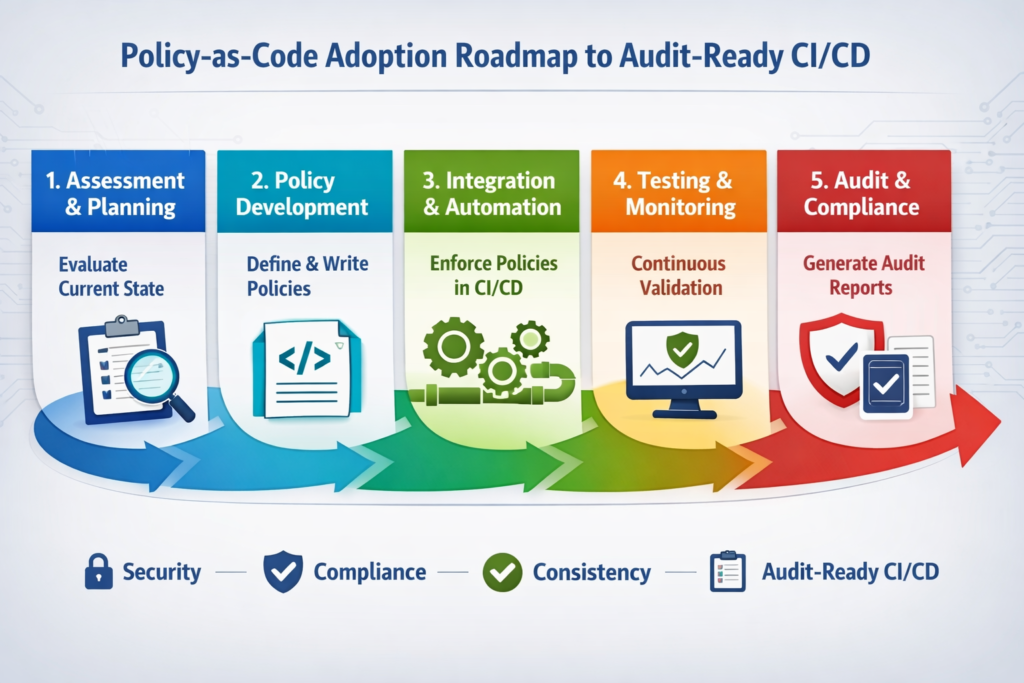
How to Roll It Out Without Creating Developer Friction
The biggest mistake is trying to codify everything at once. Start with the controls that prevent expensive mistakes and are easy to explain to both engineers and auditors.
Start with high-risk controls
A practical first wave usually includes:
Secrets exposure
Public network or storage exposure
Excessive IAM permissions
Encryption defaults
Privileged Kubernetes settings
Missing approvals for sensitive changes
These controls are commercially meaningful, regulator-friendly, and relatively easy to validate.
Build evidence collection into delivery
Do not bolt audit evidence on later. Capture it alongside delivery activity.
Pull request approvals
Pipeline logs
Policy pass/fail decisions
Scan outputs
Exception approvals
Deployment metadata
This makes audit prep far easier because evidence is produced continuously, not reconstructed under pressure.
Treat exceptions as controlled decisions
Exceptions should never become silent bypasses. A mature workflow records.
Reason
Owner
Scope
Compensating controls
Approval trail
Expiry date
That keeps delivery moving without making governance meaningless.
Measure the right things
Good metrics include.
Policy coverage across repositories
Violation rate by severity
Mean time to remediate
Exception age
Evidence completeness
Audit findings linked to pipeline gaps
Those metrics show whether policy as code is improving both control quality and delivery outcomes.
Final Thoughts
Policy as code DevSecOps gives teams a practical way to turn compliance from a periodic audit task into a daily engineering habit. By enforcing rules in pull requests, CI/CD pipelines, infrastructure workflows, and Kubernetes environments, organizations can reduce compliance drift, improve visibility, and collect stronger audit evidence without slowing releases. It also helps security, platform, and governance teams work from the same source of truth.
For companies operating across the US, UK, and EU, this approach supports faster delivery with better control. Starting small with high-risk policies, measurable guardrails, and clear exception handling makes adoption more realistic and sustainable. Over time, policy as code builds a more resilient, audit-ready software delivery model.( Click Here’s )
Key Takeaways
Policy as code DevSecOps turns compliance requirements into versioned, testable, enforceable controls that run inside real engineering workflows.
For teams in the US, UK, and EU, that means fewer manual reviews, less compliance drift, cleaner audit evidence, and stronger delivery governance. OPA and Rego are flexible across the stack, Kyverno is excellent for Kubernetes-native enforcement, and continuous compliance works best when policies are tied directly to pull requests, CI checks, deployment gates, and time-bound exception handling.
This article is for general informational purposes and should not be treated as legal, regulatory, or compliance advice. Teams should validate specific obligations against their industry, contracts, and jurisdictional requirements.
FAQs
Q : How is policy as code different from manual compliance checks?
A : Manual checks rely on people remembering what to review and when to review it. Policy as code turns those expectations into repeatable rules that run automatically in pull requests, CI pipelines, and runtime environments.
Q : Which controls should teams automate first?
A : Start with controls that prevent the most expensive mistakes: secrets exposure, public access, encryption defaults, privileged containers, risky IAM permissions, and missing approvals for sensitive changes.
Q : Is policy as code only useful for Kubernetes?
A : No. Kubernetes is a major use case, but policy as code also works for APIs, CI/CD pipelines, infrastructure as code, access workflows, and cloud governance more broadly.
Q : Can smaller teams adopt policy as code without a large platform team?
A : Yes. Smaller teams usually begin with protected branches, IaC scanning, a few high-risk rules, and limited Kubernetes or workflow enforcement. That can deliver meaningful risk reduction before a larger platform rollout.
Q : How does policy as code help with audits?
A : It creates consistent enforcement and a better evidence trail. Instead of scrambling to prove controls at audit time, teams can show versioned policies, pipeline results, approvals, and exception records collected during normal delivery work.


