Privacy by Design for IoT in Saudi, UAE & Qatar
Privacy by Design for IoT in Saudi, UAE & Qatar

Privacy by Design for IoT in Saudi, UAE & Qatar
Connected sensors can create privacy risk long before launch, even when a team thinks it is only collecting technical telemetry. In Saudi Arabia, the UAE, and Qatar, privacy by design for IoT means building products so data minimization, access control, retention, and transparency are part of the architecture from day one.
That matters in practice. A sensor platform that is privacy-aware from the start is easier to review, easier to procure, and easier to scale across Riyadh, Dubai, Abu Dhabi, and Doha without expensive redesigns later.
For GCC businesses, this is not just a legal checkbox. It is a commercial advantage. Buyers increasingly want clear documentation, trustworthy governance, and deployment models that respect local privacy expectations.
What Privacy by Design for IoT Means in GCC Markets
Privacy by design for IoT is the discipline of reducing unnecessary data collection and controlling how information is processed, stored, shared, and deleted before a product goes live.
Instead of adding policies at the end, teams shape the product early around practical controls such as.
Data minimization
Edge processing where possible
Role-based access
Retention limits
Deletion workflows
Clear user notices
Vendor and cloud review processes
In GCC markets, that early planning is especially important because deployments often involve regulated buyers, public-sector procurement, cross-border data concerns, and heightened trust expectations.
Why IoT Sensors Often Collect Personal Data Indirectly
Many sensor teams focus only on obvious personal data like names, phone numbers, or email addresses. The real issue is often indirect identification.
A simple device can become privacy-sensitive when its data is tied to.
Device IDs
Geolocation
Badge events
Worker behavior
Customer movement patterns
IP logs
Time-stamped activity trails
A temperature sensor in a warehouse, for example, may look harmless on paper. But once its readings are tied to a location, a shift pattern, or a specific operator, the data may reveal personal or behavioral information.
That is why privacy by design starts with full signal mapping, not assumptions.
Why Late Compliance Fixes Usually Cost More
Late-stage fixes tend to focus on notices, forms, and policy updates after engineering decisions are already locked in.
That approach is expensive. It can force teams to rebuild storage logic, change user permissions, adjust analytics flows, or revisit cloud architecture after procurement is already underway.
Privacy by design works differently. It asks the harder questions earlier.
What data is actually necessary?
Can some processing stay on the edge?
Who really needs access to raw data?
How long should the information be retained?
What happens when a customer asks for deletion or review?
Answering those questions early usually leads to smoother launches and fewer surprises during buyer assessments.
Why Buyers in Saudi Arabia, the UAE, and Qatar Care Early
Enterprise and public-sector buyers across the GCC are paying closer attention to how connected products handle data.
Before rollout, they may want to see evidence such as.
Data-flow maps
Hosting decisions
Retention logic
Processor and vendor controls
Incident response procedures
User notice language
Risk assessment records
This is particularly relevant in sectors like fintech, logistics, smart infrastructure, healthcare, and government-linked projects, where privacy and security reviews can directly affect procurement speed.
From a business point of view, a privacy-first product simply feels lower risk.
Where Legal and Operational Risk Usually Starts
Sensor data types that commonly raise exposure
Some categories deserve extra caution from the start.
Video feeds
Audio capture
Biometric inputs
Occupancy data
Geolocation
Telematics
Access-control logs
Environmental readings tied to a person or place
Even when the raw data looks technical, the surrounding metadata can change the risk profile quickly.
The hidden problem with metadata and identifiers
Serial numbers, gateway logs, IP addresses, timestamps, and movement trails are easy to underestimate.
On their own, they may look operational. Combined, they can reveal identity, routine, or sensitive behavior. That is where privacy issues often emerge quietly, and later than expected.
Why public-space and workplace deployments face more scrutiny
Smart-city, workplace, and public-environment deployments usually involve more people, more visibility, and more governance pressure.
A sensor rollout in a Riyadh office tower, a Dubai retail chain, or a Doha transport environment may affect staff, contractors, customers, and visitors at scale. That raises expectations around necessity, transparency, access control, and documented safeguards.
Saudi Arabia, UAE, and Qatar Compliance Signals Teams Should Watch
Saudi Arabia
In Saudi Arabia, teams should design with the PDPL environment in mind, alongside related guidance and standards that can influence data management, hosting, and sector expectations.
For vendors selling into Riyadh or Jeddah, this becomes even more important when projects touch regulated industries or public-sector environments.
United Arab Emirates
In the UAE, the compliance picture can vary depending on where and how the deployment operates.
Federal law may set the baseline for many onshore use cases, while environments such as DIFC and ADGM can introduce separate data protection considerations. For fintech and cross-border platforms, that difference matters.
Qatar
In Qatar, privacy-by-design thinking is especially relevant for projects involving monitoring, sensitive environments, or regulated sectors.
For teams launching in Doha, an early risk assessment is often the smart move, even before it becomes a formal requirement in procurement or governance discussions.
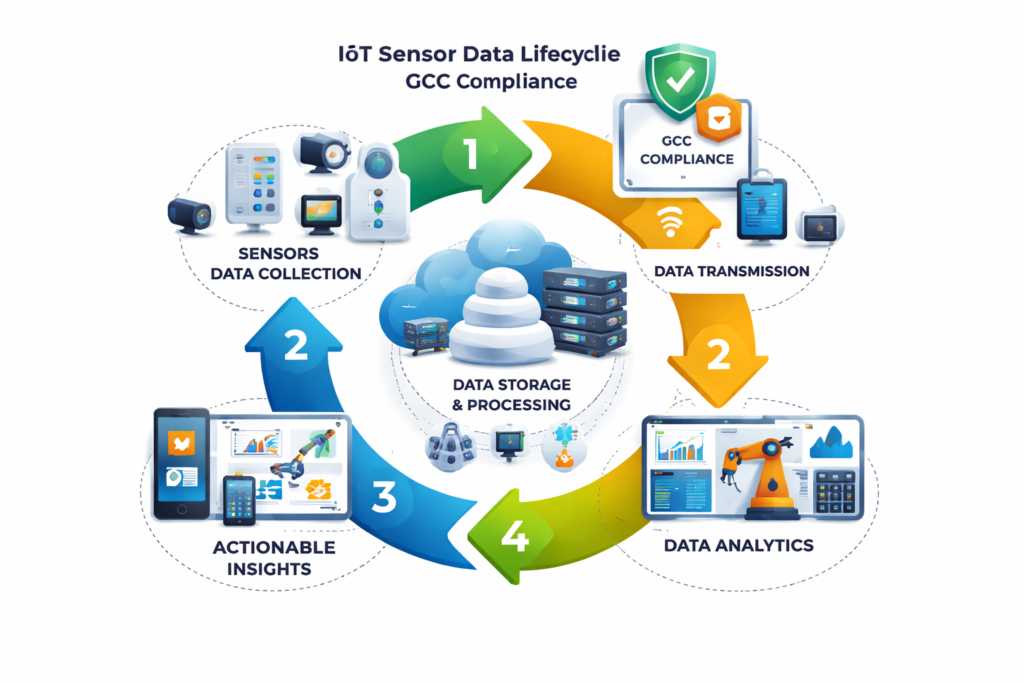
How to Apply Privacy by Design Across the Sensor Data Lifecycle
Minimize what the device collects
Start by asking whether each data point is necessary.
If a device only needs an alert, it may not need to store raw continuous data. If analytics can be aggregated, they may not need direct identifiers attached.
Less collection usually means less risk.
Process closer to the edge where possible
Edge processing can reduce the amount of sensitive information sent upstream.
A Riyadh fintech deployment might process alerts locally and transmit only essential events. A Dubai retail deployment might separate traffic analytics from customer-linked data. A Doha logistics setup might limit raw location visibility to only the roles that truly need it.
Control access by role
Not everyone should see everything.
Use role-based access so engineering, operations, analytics, compliance, and customer teams only see the data required for their responsibilities. This reduces both accidental exposure and internal misuse risk.
Define retention and deletion early
One of the most common mistakes is keeping data indefinitely because no one set a rule.
Retention should follow a clear business purpose. Deletion schedules should be defined before launch, not added after storage starts growing across systems.
Build transfer and hosting logic into the design
Cross-border transfer decisions should never be treated as a simple infrastructure choice.
In GCC projects, hosting region, sector rules, procurement terms, and customer expectations can all affect what is acceptable. In many cases, regional hosting is the safer starting point for both latency and trust.
Review processors, vendors, and cloud partners
A privacy-first IoT stack is not just about the device.
It also depends on.
Cloud providers
Analytics vendors
Processors
Integrators
Support workflows
Contractual safeguards
Audit evidence
If third parties touch the data, they are part of the privacy design story too.
Deployment Scenarios in Riyadh, Dubai, Abu Dhabi, and Doha
Smart-city and public-environment sensors
These projects often need stronger purpose limitation, visible notice practices, and tighter governance because they can affect large groups of people in shared spaces.
Retail, logistics, and workplace monitoring
In Dubai warehouses, Abu Dhabi offices, or large retail environments, movement and productivity signals can quickly enter employee-privacy territory. Teams should be careful not to normalize excessive monitoring just because the technology allows it.
Fintech, government, and regulated-industry use cases
In higher-trust sectors, privacy by design also supports security reviews, vendor approvals, and audit readiness. That can make a measurable difference during procurement.

A Practical Privacy-by-Design Checklist Before Launch
Before deployment, product teams should be able to answer these questions clearly.
What personal data could the sensor collect directly or indirectly?
Which identifiers, logs, or metadata fields increase privacy exposure?
Can edge logic reduce what leaves the device?
Does each user role really need access to raw data?
How long will each category of data be retained?
What is the deletion process?
Will any data move across borders?
Which vendors or processors handle the data?
Is a risk assessment needed before launch?
Are notices available in clear Arabic and English where appropriate?
Teams should also keep buyer-ready documents in place, including.
Data-flow maps
Retention rules
Processor lists
Incident procedures
Access-control summaries
Hosting decisions
Risk assessment records
For GCC users, especially in Saudi Arabia, the UAE, and Qatar, bilingual transparency matters. Clear Arabic and English notices can reduce confusion, support trust, and make deployments easier to defend during review.

How Privacy by Design Lowers Legal and Commercial Risk
When privacy controls are built early, businesses usually avoid the most painful part of IoT deployment: going back to redesign core systems after concerns are raised.
That brings real benefits.
Fewer architecture changes later
Faster procurement reviews
Stronger buyer confidence
Better audit readiness
Clearer internal accountability
Smoother regional expansion
In practice, privacy by design for IoT is not just about reducing legal exposure. It helps businesses launch more credible products across the GCC with less friction.
This is also where related planning matters. For example, teams working on connected platforms may want to align privacy controls with broader digital architecture and delivery planning through resources like smart city dashboard strategy, edge AI architecture for GCC teams, mobile app development services, or web development services.

Final Thoughts
Privacy by design for IoT gives businesses in Saudi Arabia, the UAE, and Qatar a stronger foundation for launch, procurement, and long-term scale.
The earlier a team maps data, limits unnecessary collection, defines retention, and reviews hosting and vendor decisions, the easier it becomes to build trust with buyers and reduce avoidable risk.
If your business is planning a connected-device rollout in the GCC, now is the time to review your architecture, governance model, and deployment decisions before scale. This article is for general information and should not be treated as legal advice for any specific project.( Click Here’s )
FAQs
Q : Is sensor data considered personal data in Saudi Arabia?
A : It can be. Sensor data does not need to include a person’s name to create privacy obligations. If device IDs, location trails, metadata, or behavioral patterns can identify or single out an individual, the data may become privacy-relevant.
Q : Do IoT vendors in Dubai need different privacy controls for DIFC or ADGM projects?
A : Often, yes. A platform used across mainland UAE, DIFC, and ADGM may need different documentation, workflows, or governance treatment depending on the deployment context and sector.
Q : When should Qatar-based teams run a privacy risk assessment for sensor deployments?
A : Before launch is usually the best point, especially for systematic monitoring, sensitive environments, or regulated-sector use cases. Early review helps teams assess necessity, safeguards, retention, and transparency before the product is exposed to commercial or regulatory scrutiny.
Q : Can smart-city sensor data be hosted outside Saudi Arabia or the UAE?
A : Possibly, but it should never be treated as a routine technical choice. Transfer logic, procurement conditions, sector-specific rules, and customer expectations can all affect what is practical or acceptable.
Q : What should Arabic privacy notices include for connected-device users in GCC markets?
A : They should clearly explain what the device collects, why the data is used, how long it is kept, who can access it, and whether it is transferred or analyzed elsewhere. Clear wording matters just as much as legal accuracy.



[…] Saudi Arabia, the UAE, and Qatar Approach AI Traffic Optimization […]