Remote Work Security Policy for GCC Enterprises
Remote Work Security Policy for GCC Enterprises

Remote Work Security Policy for GCC Enterprises
A remote work security policy for GCC companies defines who can work remotely, on which devices, from which locations, and under what technical controls (VPN, MFA, endpoint protection, logging). For mid–large organisations in Saudi Arabia, the UAE and Qatar, it should align with frameworks such as NCA Telework Cybersecurity Controls, TDRA’s Information Assurance Regulation and QCB technology-risk expectations, while staying realistic for hybrid teams and local cloud regions
Across Saudi Arabia, the United Arab Emirates and Qatar, hybrid work is now the default – but in many organisations the remote work security policy is still a forgotten PDF or a few lines in the HR manual. That’s a real risk for banks, government entities, healthcare, logistics and energy providers that must show regulators they can secure staff working from home, co-working spaces and hotels.
In practical terms, a GCC-grade remote work security policy should define devices (corporate vs BYOD), access (VPN, Zero Trust, identity), locations, monitoring and incident response and then tie those rules to NCA Telework Cybersecurity Controls, TDRA Information Assurance Regulation and Qatar’s cybersecurity and tech-risk frameworks.
Why GCC Companies Need a Remote Work Security Policy Now
From emergency remote work to regulated hybrid models in KSA, UAE and Qatar
What started as emergency remote work in 2020 has turned into long-term hybrid models in Riyadh, Dubai and Doha. Boards now expect clear risk ownership, and regulators want to see formalised policies, not ad-hoc emails from IT. For example, the Saudi NCA Telework Cybersecurity Controls explicitly extend earlier Essential Cybersecurity Controls into remote work, while TDRA’s IA Regulation and Qatar’s national cybersecurity frameworks push entities to treat telework as part of their core security posture, not a side arrangement.
Common device and access risks seen by CISOs in Riyadh, Dubai and Doha
CISOs across Riyadh, Dubai and Doha report the same patterns: employees using unmanaged laptops, shared family PCs, weak or default Wi-Fi routers, and personal cloud apps for file sharing. Shadow IT SaaS, unsanctioned VPN apps and staff connecting from high-risk countries all complicate compliance with banking and government rules. Without a clear policy, even strong tools like EDR or MFA cannot compensate for inconsistent decisions by line managers granting “temporary” access.
How GCC regulations are tightening expectations on telework security
Frameworks from the National Cybersecurity Authority (NCA), the Saudi Central Bank (SAMA), TDRA, Q-CERT and Qatar Central Bank (QCB) increasingly reference remote or off-premise access as part of overall technology risk. Telework controls, communication-security clauses and technology-risk circulars expect documented policies, centralised monitoring and the ability to evidence controls during audits including for contractors.
Core Building Blocks of a Remote Work Security Policy
Defining scope: who can work remotely, on which devices, from where
Your policy should start by defining eligibility: which roles can work remotely, what data they handle, and whether cross-border work is allowed. For example, KSA-based staff handling payment data under Open Banking schemes may be restricted to in-kingdom locations, whereas marketing teams can work from wider GCC countries like Kuwait, Bahrain or Oman.
Include explicit rules for travel, such as.
Prior approval for access from new countries
Use of corporate VPN / Zero Trust gateways on untrusted networks
Handling of shared networks such as hotels, airports and co-working spaces
Roles and responsibilities for HR, IT, Security and line managers
Remote work security only works when responsibilities are crystal clear:
HR updates contracts, NDAs and disciplinary language to cover data handling and monitoring during telework.
IT defines standard builds and manages provisioning and de-provisioning of devices and accounts.
Security sets technical controls, monitors compliance and leads incident response.
Line managers approve or reject remote work requests based on risk and must trigger revocation of access when staff change roles or leave.
A simple RACI matrix attached to the policy helps avoid blame-shifting when an incident occurs.
Linking remote work security with ISMS, PDPL and vendor policies
In KSA and Qatar, many entities already operate an ISO 27001 ISMS and local data-protection or PDPL-style obligations. Your remote work security policy should reference those classifications and the National Data Management Office (NDMO) guidance on data residency and retention.
For UAE and free-zone entities (DIFC/ADGM), ensure telework rules align with.
Internal privacy notices
Cloud and outsourcing contracts
Third-party support agreements and remote access models
This includes defining what remote access vendors may use, from which countries they may connect, and how their sessions are monitored.
Device, BYOD and Endpoint Security Standards
Corporate laptop and mobile baselines for Saudi, UAE and Qatar teams
For corporate devices, define a minimum baseline that includes.
Full-disk encryption
Centrally managed anti-malware and host firewall
OS and browser patching SLAs
EDR agents to provide endpoint protection for remote staff
Privileged users such as admins supporting banking systems in Jeddah or Abu Dhabi should use hardened jump hosts, separate admin accounts and stronger authentication. Document how lost or stolen devices are reported, remotely wiped and investigated, especially for highly regulated sectors.

BYOD security policy
Why is BYOD security so critical for hybrid work teams in GCC countries like KSA, UAE and Qatar?
Because personal devices often sit outside corporate control, weak BYOD rules can expose regulated data to malware, family use and insecure apps directly undermining telework cybersecurity controls and local regulators’ expectations. In GCC hybrid teams, strong BYOD governance lets you support flexibility without losing control of banking, health or citizen data.
If you allow BYOD, set clear criteria such as.
Only low-risk roles are eligible
No access to core banking, payment or national ID systems
Compliance with minimum controls (modern OS, encryption, screen lock, MDM or mobile app-management agent)
Clarify privacy boundaries in HR policy: what telemetry the organisation collects, how monitoring works, and how employees give informed consent under local laws.
MDM, EDR and DLP tooling options for GCC mid large organisations
For mid–large enterprises, centralised tools are non-negotiable.
Mobile Device Management (MDM) to enforce baselines on laptops and phones, including remote wipe if a device is lost in Dubai or Doha.
Endpoint Detection and Response (EDR) to give your SOC the telemetry needed for incident investigations across home networks.
Data Loss Prevention (DLP) to help control uploads, email exfiltration and USB usage in work from home setups.
When choosing tools, check whether they support in-region cloud hosting (for example AWS Bahrain, Azure UAE Central, GCP Doha) to meet residency and regulator expectations.
Secure Remote Access, VPN and Identity Controls
VPN and Zero Trust options for compliant remote access in regulated sectors
Traditional VPNs are still common in GCC banks and government entities, but many are moving towards zero trust network access for GCC companies to limit lateral movement and over-privileged tunnels. For sectors supervised by SAMA, QCB or UAE financial regulators, your remote access design should avoid broad “full network” VPNs and instead grant application-level access with strong logging, geo-controls and explicit approvals. Split-tunnelling decisions should be risk-based and documented, especially for critical systems.
MFA, SSO and session management for remote users
A robust identity layer is at the heart of a good remote work security policy. Use MFA and SSO for remote employees across VPN, ZTNA and SaaS, preferring app-based tokens or hardware keys over SMS where possible. Implement role-based access, just-in-time elevation for admins and strict session timeouts for sensitive applications such as Open Banking APIs or citizen-data portals integrated with UAE Pass or Qatar Digital ID.
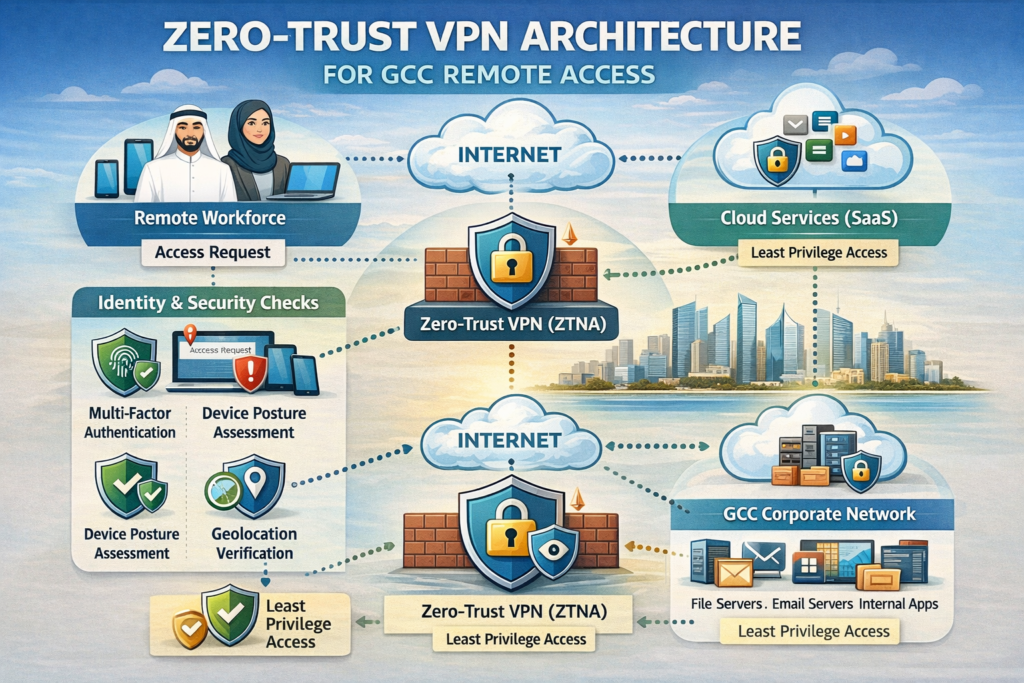
Monitoring, logging and incident response for remote sessions
Your SOC should log VPN, ZTNA and identity events in detail: device posture, location, MFA method, session duration and privileged actions. Remote-friendly playbooks must cover lost devices, suspected credential theft, phishing campaigns and misuse of SaaS collaboration tools.
Coordination between SOC, HR and Legal is especially important for cross-border incidents (for example, a contractor in another GCC state accessing a Saudi government system), where local labour and privacy rules differ.
GCC Compliance Mapping.
Aligning your policy with NCA Telework Cybersecurity Controls and SAMA Cyber Security Framework
What remote work security controls do Saudi companies need to meet NCA Telework Cybersecurity Controls?
In practice, Saudi organisations should show that telework follows the same discipline as on-prem work: approved users, secure devices, strong authentication, encrypted connections, monitoring and documented incident response.
The NCA Telework Cybersecurity Controls build on existing Essential and Cloud Cybersecurity Controls to define governance, asset management, access control, operations security and incident management in remote scenarios. Saudi companies especially those regulated by SAMA should map each control to concrete policy clauses and technical measures (for example VPN configuration, EDR deployment, logging retention) and keep evidence for audits.
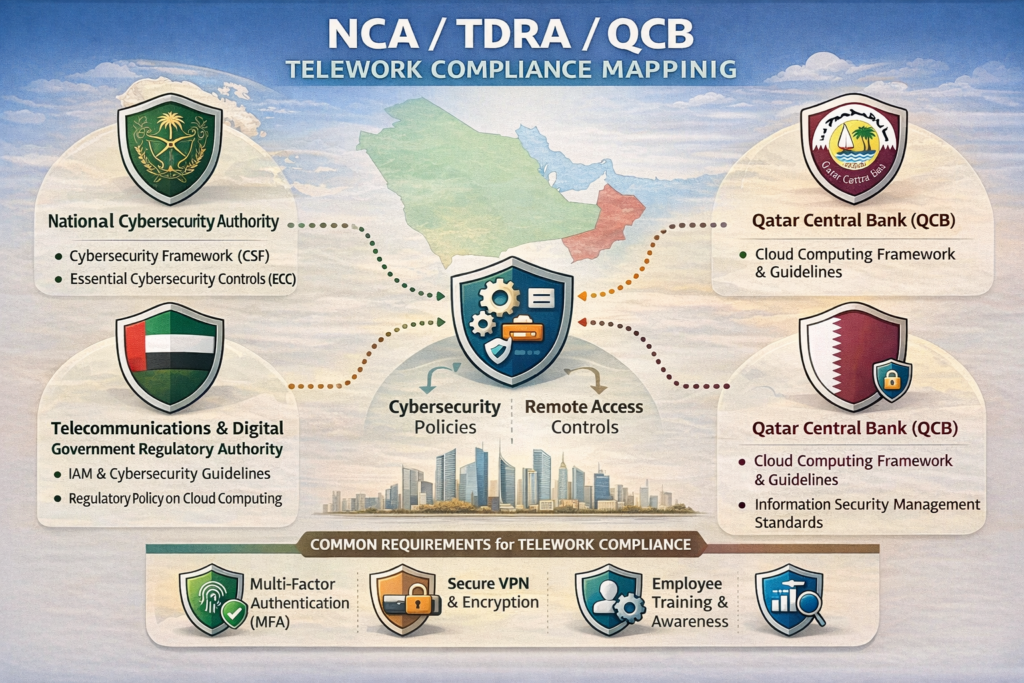
Meeting UAE TDRA Information Assurance and free-zone expectations
How should UAE businesses define a remote access policy that aligns with TDRA’s Information Assurance Regulation for off-premise work?
Start by treating remote access as a critical communication-security scenario: define acceptable teleworking environments, mandate secure VPN or ZTNA with strong encryption, prohibit storage of sensitive data on unmanaged devices, and require MFA for all off-site access. TDRA’s IA Regulation explicitly calls out secure remote access design, protection of information over networks and control of privately owned equipment, and newer national IA standards tighten expectations for critical sectors.
For free-zones like Dubai International Financial Centre (DIFC) and Abu Dhabi Global Market (ADGM) your policy should also align with their tech-risk and outsourcing rules, including governance around cloud, third-party remote access and incident reporting.
Understanding QCF, Q-CERT guidance and QCB tech-risk for remote access
How can Qatar organisations make their VPN and IAM setup compliant with QCF and local banking tech-risk requirements?
For Qatar banks and government-linked entities, the goal is traceable, well-governed remote access hardened endpoints, approved VPN gateways, strong identity management, central logging and Q-CERT-aligned incident handling. Guidance from Q-CERT on securing home workers, combined with QCB’s Technology Risk Instructions and payment-sector cyber regulations, expects robust identity and access management, continuous monitoring and clear board oversight.
Implementation, Cost and Next Steps for GCC Organisations
Step-by-step rollout plan for remote work security in KSA, UAE and Qatar
Assess
Inventory remote users, locations, devices and applications; review existing telework practices against NCA, TDRA, QCF/QCSF and internal ISMS controls.
Design
Define your remote work security policy, including scope, BYOD, VPN/Zero Trust, logging and incident playbooks; align with data-classification and residency rules.
Pilot
Run a pilot in one business unit in Jeddah or Abu Dhabi, testing tools, user experience and audit trails.
Roll out
Gradually extend to all departments in KSA, UAE and Qatar, updating HR contracts and training materials along the way.
Audit and improve
Perform regular internal audits, simulate incidents and refine controls based on regulator feedback and SOC findings.
Estimating costs: tooling, training and audits for mid large organisations
Budget lines usually fall into.
Endpoint tooling (MDM, EDR, VPN/ZTNA)
Identity stack (SSO/MFA and directory services)
Email and web security
Security awareness and phishing simulations
Consulting, penetration testing and periodic audits
Costs will vary depending on where you host (for example Azure UAE Central vs AWS Bahrain vs GCP Doha) and whether you rely on local partners in Riyadh or Dubai. Investing early in policy design and training often reduces later compliance remediation and incident-response costs.
Governance, KPIs and when to bring in external GCC security experts
A remote work security programme should report KPIs such as phishing-click rates, patch compliance, remote-access failures, DLP events and audit findings. Triggers to bring in external GCC experts include regulator observations, cross-border expansion (for example adding Kuwait or Oman operations), large-scale cloud migrations or persistent shadow IT.
Partners like Mak It Solutions, already helping enterprises modernise GCC web and cloud platforms, can work alongside your CISO and IT teams to translate frameworks into practical roadmaps.

Concluding Remarks
For GCC boards and executives, a remote work security policy is now a core risk-management and compliance asset, not a nice-to-have. The shift to hybrid work in KSA, UAE and Qatar, combined with tightening telework cybersecurity controls, means you must treat remote endpoints, VPN/IAM, monitoring and incident response with the same rigour as your data centre.
By defining scope, hardening devices (including BYOD), modernising VPN and identity, and mapping controls to NCA, TDRA, QCF and QCB expectations, you reduce risk while making hybrid work sustainable. The next step is to turn this guidance into a living policy, supported by training, automation and regular review as regional regulations evolve.
If you’re responsible for security or digital transformation in Riyadh, Dubai or Doha and your remote work policy still lives in scattered emails, this is the moment to fix it. Mak It Solutions can help you translate GCC regulatory frameworks into a pragmatic, human-friendly policy and architecture for your teams.
From secure web and app platforms to end-to-end advisory, we support organisations through assessment, design, rollout and optimisation. Explore our Web Development Services and Web Designing Services, then reach out for a consultation tailored to your KSA, UAE and Qatar remote work agenda.( Click Here’s)
FAQs
Q : Is a remote work security policy mandatory under NCA rules for private companies in Saudi Arabia?
A : NCA’s Telework Cybersecurity Controls primarily target government entities and operators of critical national infrastructure, but they are increasingly treated as best practice for serious private-sector organisations in Saudi Arabia. In reality, if you are regulated by SAMA or supporting Saudi Vision 2030 programmes, auditors will expect your remote work security policy to reflect NCA’s governance, access control, operations and incident-management requirements. Even when not explicitly “mandatory”, aligning with NCA TCC and related frameworks significantly reduces regulatory and cyber-risk exposure.
Q : Can UAE employees use personal laptops for remote work under TDRA and free-zone guidelines (DIFC/ADGM)?
A : TDRA’s Information Assurance Regulation does not outright forbid BYOD, but it does require secure remote access, protection of sensitive information and controls over privately owned equipment used for work. Free-zones like DIFC and ADGM add their own expectations around technology risk, outsourcing and data protection, so high-risk roles in finance or critical services are often limited to fully managed devices. A practical approach is to allow BYOD only for low-risk roles under strict MDM or app-management controls, with clear privacy notices for staff and an option to move individuals to corporate devices if risk increases.
Q : How should Qatar banks secure VPN and IAM access for staff working from home to satisfy QCB tech-risk expectations?
A : QCB technology-risk and cyber-security regulations expect banks to maintain strong identity and access management, secure remote connections and continuous monitoring for staff working from home. Practically, that means hardened, centrally managed endpoints, approved VPN or ZTNA gateways with strong encryption, mandatory MFA, granular role-based access and centralised logging fed into a SOC. Playbooks should align with Q-CERT guidance for incident reporting and response. Boards and executive management are expected to maintain oversight of these controls, with QCB reserving the right to audit at any time.
Q : What are best-practice remote work security rules for GCC government contractors handling citizen data?
A : GCC government contractors whether hosting portals, developing apps or providing outsourcing services should assume their remote workers are held to the same standard as civil-service staff. That typically includes mandatory corporate devices, strong MFA, strict VPN/ZTNA design, DLP on endpoints and email, plus explicit bans on printing or saving citizen data to personal storage. Contractors should map their policies to frameworks such as Saudi’s NCA and DGA guidance, UAE’s IA and digital government standards, and Qatar’s national cybersecurity strategy and sector regulations, documenting how remote access and monitoring work in practice.
Q : How can multinational teams in Riyadh, Dubai and Doha keep data inside local cloud regions while enabling hybrid work?
A : Many GCC organisations now combine multiple in-region cloud locations for example, AWS Bahrain, Azure UAE Central and GCP’s Doha region to keep latency low and meet regulator expectations around data residency. Your remote work security policy should define which systems and data classes must remain in-region, and require VPN/ZTNA endpoints that terminate into those approved environments only. Combine this with DLP, geo-based access controls and strong IAM so that staff in Riyadh, Dubai and Doha can collaborate effectively without copying regulated datasets into unmanaged tools. Regular reviews with compliance and legal teams help keep this architecture aligned with evolving SAMA, TDRA and QCB rules.


