Software Supply Chain Security with SBOMs: Guide
Software Supply Chain Security with SBOMs: Guide
Software Supply Chain Security with SBOMs: Guide
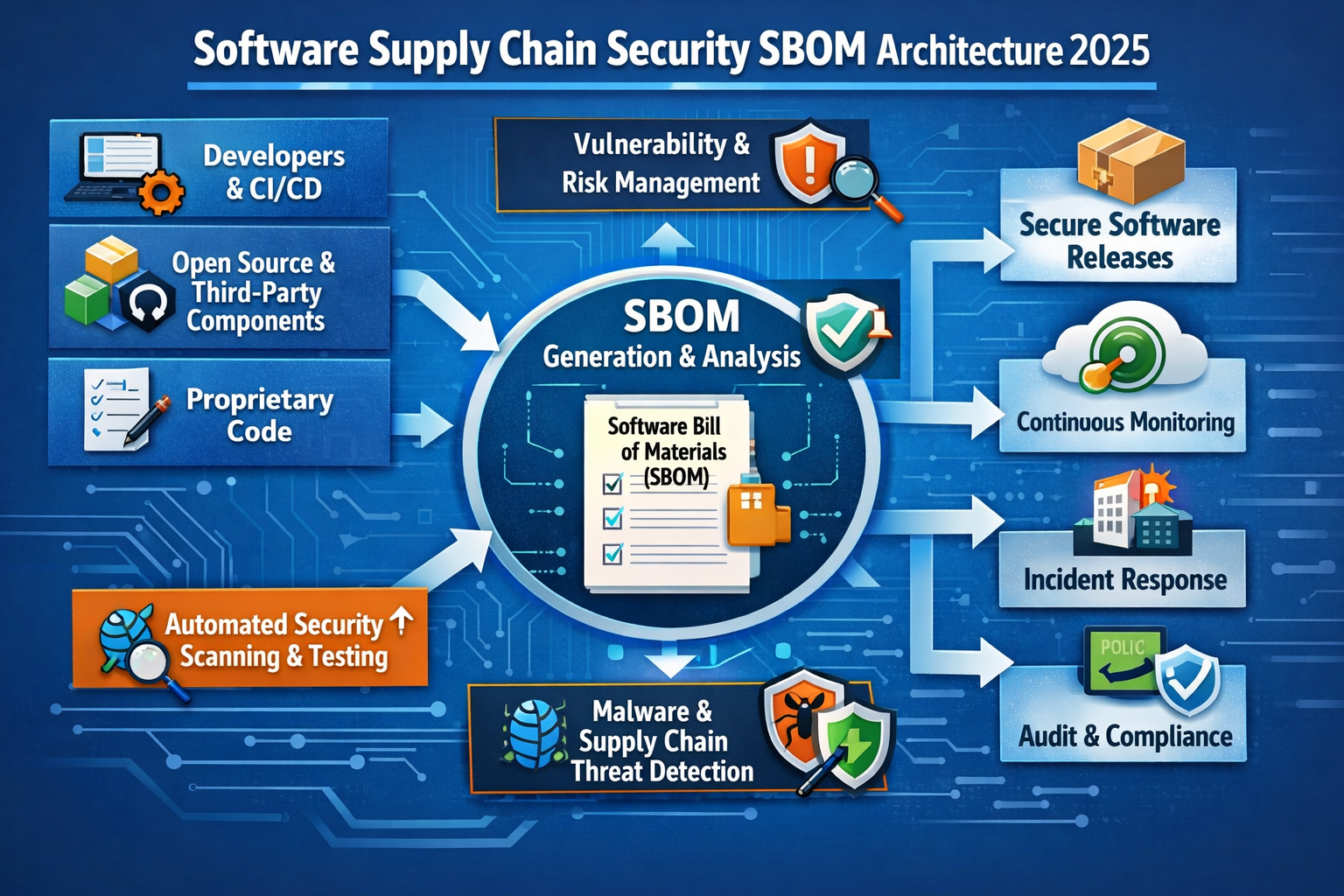
Software supply chain security with SBOMs means protecting every component that goes into your software code, open-source dependencies, CI/CD pipelines and cloud infrastructure so attackers can’t tamper with it before it reaches customers. SBOMs give you a machine-readable inventory of all components so you can manage vulnerabilities, prove compliance to regulators in the US, UK and EU, and respond quickly when a new zero-day hits.
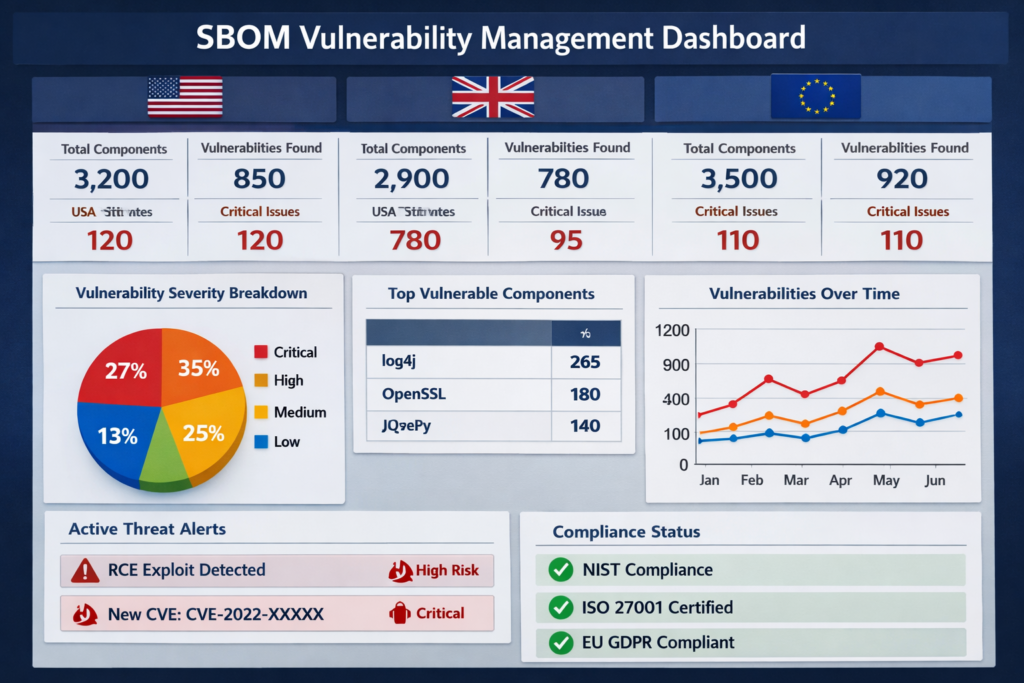
Over the last few years, software supply chain attacks have gone from edge cases to board-level risks. Incidents like SolarWinds-style build compromises, Log4Shell in ubiquitous Java libraries and the XZ Utils backdoor showed how a single upstream component can ripple through thousands of products and services in the United States, United Kingdom and across the wider European Union. ENISA has noted that supply chain compromises jumped from under 1% of intrusions to double-digit percentages in just a few years.
At the same time, regulations are catching up. EO 14028 is reshaping how US federal agencies buy software, NIS2 and the Cyber Resilience Act (CRA) expand expectations on European suppliers, and DORA adds ICT risk rules for financial entities.
In this environment, three pillars now define modern software supply chain security with SBOMs:
SBOMs and software bill of materials compliance
Open-source dependency controls and registry guardrails
CI/CD and build pipeline hardening with integrity and provenance
This guide is for CISOs, product security, platform, DevSecOps and GRC teams in the US, UK, Germany and the EU who need a practical, 90-day path from “we should do something about SBOMs” to demonstrable, audit-ready controls.
What Is Software Supply Chain Security?
Quick answer (AEO)
Software supply chain security is the set of practices, tools and policies used to protect all components that go into your software code, open-source dependencies, build systems, CI/CD and infrastructure from compromise or tampering before they reach customers.
In other words, it doesn’t just look at your first-party code. It covers every stage of the SDLC where an attacker could slip in malicious changes: your source repos, your npm/PyPI/Maven packages, your CI jobs, artifact repositories and cloud runtimes.
The Modern Software Supply Chain Attack Surface
A modern software “chain” typically spans.
Source code and pull requests
Third-party and open-source libraries
Package registries (npm, PyPI, Maven Central, NuGet)
CI/CD systems and runners
Container registries and images
Cloud infrastructure and Kubernetes clusters
High-profile incidents like SolarWinds (build environment compromise), Log4j (ubiquitous vulnerable component) and the XZ Utils backdoor (maintainer account takeover) illustrate both upstream (dependency) and build-stage compromise patterns.
Traditional AppSec focused mostly on first-party code through SAST/DAST. Software supply chain security adds a layer across the SDLC covering software composition analysis for supply chain security, CI/CD pipeline integrity and provenance, and runtime controls on platforms like AWS and other clouds.
Common Software Supply Chain Attack Patterns
Common attack patterns now include
Dependency confusion and typosquatting publishing malicious packages with similar names or higher versions than internal ones.
Malicious maintainer takeovers attackers compromise or buy a maintainer account, then push a backdoored update.
Compromised CI/CD runners and build agents injecting code into build scripts, pipeline definitions or container base images.
Stolen signing keys allowing attackers to sign malicious artifacts that look legitimate in production.
Attackers love these patterns because they scale: compromise one component and you get “one-to-many” leverage across hundreds of SaaS environments, fintech platforms in London, KRITIS operators in Germany or healthcare providers using systems integrated with the NHS.
Why CISOs and Boards Now Care About SBOMs
SBOMs make hidden third-party risk visible. Instead of asking “are we exposed to this new OpenSSL bug?” and guessing, you can query a normalized inventory of components across all applications.
US regulators and agencies such as CISA and the National Institute of Standards and Technology (NIST) now explicitly reference SBOMs and secure development frameworks (like NIST SP 800-218 SSDF) in guidance for software suppliers and federal buyers.
Boards care because SBOMs and supply chain controls are increasingly how you prove due diligence under NIS2, DORA, SOC 2 and sectoral regimes such as HIPAA and PCI DSS.
SBOMs as the Foundation of Software Supply Chain Security
Quick answer (AEO)
An SBOM (Software Bill of Materials) is a machine-readable inventory of all components in an application including open-source libraries, versions and licenses used to improve vulnerability management, compliance and incident response.
Think of SBOMs as your ingredient list for every microservice, mobile app and desktop client you ship.
SBOM Basics Formats, Fields and Where They Fit in the SDLC
A useful SBOM typically includes.
Component name and version
Supplier/namespace
License information
Dependency relationships (graph)
Hashes and other identifiers
The most common formats are SPDX and CycloneDX, and many teams now use open-source tooling or projects like Protobom under the OpenSSF to normalize SBOM data across formats.
SBOMs can be.
Generated at build time in CI/CD
Embedded in container images
Delivered by vendors for COTS or SaaS products
From SBOM to Action Vulnerability Management and Transparency
SBOMs really pay off when you connect them to vulnerability management using SBOM data.
Map SBOM components to CVEs, EPSS scores and exploit intel
Use VEX (Vulnerability Exploitability eXchange) or similar to encode whether a vulnerability is actually exploitable in your context
Prioritize fixes by exploitability and business impact, not just CVSS
CISA and partners have published recommended practices for SBOM consumption that describe how to automate ingestion, normalization and continuous monitoring as new CVEs are disclosed. ([CISA][6])
When the next Log4j-style zero-day drops, teams with robust SBOMs can rapidly answer: which apps, which environments, which customers, and what’s the remediation plan?
SBOM Regulations and Guidance in the US, UK, Germany and EU
In the US, EO 14028 and NIST SSDF SP 800-218 set expectations for secure software development, while CISA’s SBOM work (including SBOM “minimum elements”) guides federal agencies and suppliers on software supply chain security SBOM requirements for US federal agencies.
Across the EU, NIS2 and the CRA increasingly embed SBOM-style transparency into expectations for vendors in sectors like connected vehicles, medical devices and critical infrastructure, with ENISA’s good practices for supply chain cybersecurity reinforcing these trends.
In Germany, BaFin and KRITIS guidance already expect strong oversight of ICT and cloud suppliers; many banks in Frankfurt or Berlin now treat SBOMs as standard evidence of component transparency.
In the UK, emerging procurement practices particularly in the public sector and Open Banking ecosystems in places like Manchester and London increasingly ask for SBOMs and secure SDLC evidence as part of software supply chain security checklists for UK public sector tenders.
Many German CISOs are now asking very specifically about “software supply chain security SBOM Pflichten unter NIS2 in der EU” in RFPs and contract negotiations.
Securing Open-Source Dependencies and Package Registries
Quick answer (AEO)
To secure open-source dependencies, organizations combine SBOM-driven visibility with automated scanning, policy enforcement and registry-level guardrails that block risky packages before they enter builds.
In practice, that means treating open source like any other supplier with inventory, risk scoring and controls.
Building a Live Inventory and Risk Score for Dependencies
SBOMs plus software composition analysis (SCA) tools give you the baseline: a live inventory of every npm, PyPI, Maven, NuGet and OS package in use. Open source now typically makes up 70–90% of application code by volume.
On top of that inventory, you can risk-score components based on:
Known vulnerabilities and exploitability
Maintainer reputation and activity
Popularity and ecosystem adoption
Update cadence and release hygiene
Modern, developer-first platforms surface this in IDEs, pull requests and CI pipelines so engineers can see open-source dependency scanning and remediation suggestions before code merges.

Guardrails for npm, PyPI and Other Registries
Registry-level guardrails stop risky components at the gate:
Block known malicious packages and untrusted namespaces
Use internal mirrors and “golden images” of approved libraries
Pin versions and enforce checksums
Apply policy-as-code in GitHub/GitLab workflows to prevent unreviewed dependencies from entering builds
This is especially important when engineers in New York, Austin or San Francisco are working across microservices that share internal package names classic territory for dependency confusion attacks.
Sector and GEO Examples Fintech, Healthcare and Critical Infrastructure
US fintech and healthcare: tying dependency security to HIPAA Security Rule expectations for protecting ePHI and PCI DSS requirements around secure software development.
UK Open Banking and NHS suppliers: strong third-party vetting of SDKs, APIs and mobile libraries to avoid “shadow” components processing personal data.
German BaFin-regulated banks and KRITIS operators: expecting traceability for every open-source component running in core payment, trading or industrial control systems, often mapped to ISO 27001 and BaFin cloud outsourcing expectations.
CI/CD and Build Pipeline Controls for Supply Chain Security
Quick answer (AEO)
Securing the CI/CD pipeline means enforcing strong identity, tamper-evident build steps and signed artifacts so that only verified code can be promoted from source to production.
This is where NIST SSDF practices meet real-world DevSecOps.
Hardening CI/CD: Identity, Least Privilege and Secrets Management
Start by treating CI/CD like production
Isolate runners and restrict network access
Use strong MFA and hardware-backed keys for admins and service accounts
Minimize long-lived credentials; prefer OIDC-based, short-lived tokens
Centralize secrets (tokens, signing keys) in a vault with rotation and audit logs
NIST SSDF explicitly calls for securing build environments and enforcing least privilege on tooling and infrastructure, and many AWS, Azure and GCP services now provide native features to support this.
Code Signing, Provenance and SLSA Levels
To assure integrity and provenance, you need.
Provenance metadata: who built what, when, from which commit, with which dependencies
Signed artifacts: containers, binaries and even SBOMs signed so tampering is detectable
SLSA-style maturity: using the SLSA framework as a roadmap for pipeline hardening, from basic build integrity to fully isolated, hermetic builds with auditable logs.
This “CI/CD pipeline integrity and provenance” story is increasingly what regulators and risk committees expect to see, not just unit test and coverage percentages.
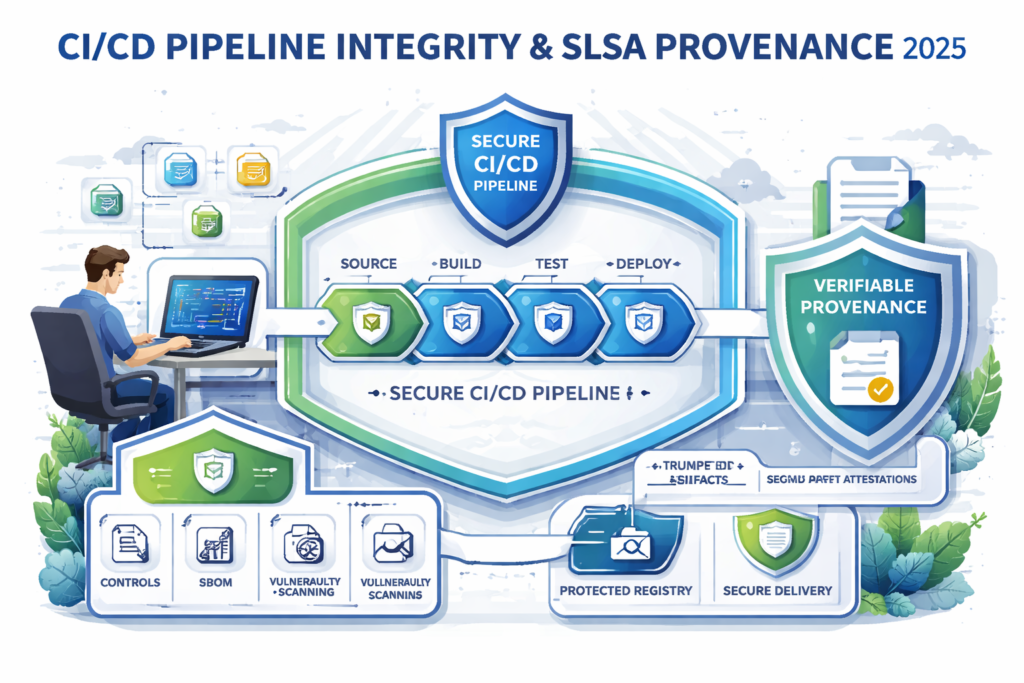
Detecting Pipeline Tampering and Production Drift
Finally, assume controls can fail. Put monitoring around your pipelines:
Alert on unusual pipeline changes: new jobs, modified workflows, unapproved plugins
Compare source, build outputs and runtime images for integrity and drift
Use runtime detection in Kubernetes and serverless to catch suspicious behavior that looks like supply chain exploitation (e.g., unexpected outbound connections from build-time tools)
This detection layer nicely complements identity-first approaches you may already be using for cloud IAM.
Software Supply Chain Risk Management and Regulatory Alignment
Quick answer (AEO)
Software supply chain risk management connects technical controls like SBOMs and CI/CD security with governance frameworks and regulations so that CISOs can prove due diligence to regulators, auditors and customers.
Boards don’t want a tool list; they want evidence that you map controls to NIST SSDF, NIS2, GDPR, HIPAA, PCI DSS and SOC 2.
Mapping Technical Controls to NIST SSDF, CISA and ENISA Guidance
You can explicitly map.
SBOM generation and consumption → NIST SSDF practices around identifying and managing third-party components.
Dependency screening and SCA → CISA recommendations on using SBOMs in software procurement and vulnerability management.
Pipeline security → SSDF build environment controls and ENISA’s good practices for supply chain cybersecurity around supplier security and ICT/OT environments.
This mapping makes it much easier to explain to a risk committee in Berlin or a US federal ATO reviewer how your DevSecOps program supports their expectations.
Aligning with NIS2, GDPR/DSGVO, HIPAA, PCI DSS and SOC 2
NIS2 Article 21 explicitly calls out supply chain security as part of required risk-management measures.
GDPR / DSGVO and UK-GDPR, especially Article 28, require controllers to ensure processors provide appropriate security and govern sub-processors exactly where SBOM-backed supply chain oversight helps.
HIPAA Security Rule updates and enforcement focus heavily on vendor risk and technical safeguards, including encryption and multi-factor authentication.
PCI DSS and SOC 2 expect evidence of secure software development, vulnerability management and third-party oversight, all of which your software supply chain security program can generate.
DORA further tightens ICT third-party risk management for EU financial entities, requiring robust frameworks for identifying, monitoring and managing ICT-related risks including software supply chains.
Vendor Risk, Due Diligence and Contractual Controls
When assessing SaaS, cloud and tooling vendors, treat software supply chain security with SBOMs as a first-class topic
Ask for SBOMs, SLSA/SSDF alignment and their approach to open-source dependency scanning and remediation
Include contractual clauses for SBOM delivery, vulnerability SLAs, notification timelines and support for incident response exercises
Align RFP questions with templates such as CISA’s vendor SCRM questionnaires and ENISA guidance
This is where a platform like Mak It Solutions can help engineering and procurement teams standardize questions and evidence across New York, London, Berlin and Frankfurt-based stakeholders.
How to Choose a Software Supply Chain Security Platform
Quick answer (AEO)
The right platform should centralise SBOM management, dependency risk, CI/CD controls and compliance reporting into one view, integrating with your existing developer tools and cloud stack.
Think of it as the “single pane of glass” for your software supply chain.
Core Capabilities Checklist
Look for at least.
Automated SBOM generation and ingestion (SPDX, CycloneDX, multi-language)
SCA and registry scanning for open-source and third-party components
Policy engine to enforce risk thresholds and compliance rules in CI (block builds/deploys when violated)
CI/CD pipeline integrity checks and artifact signing support
Dashboards for software bill of materials compliance across portfolios
These combine into an actionable software supply chain security checklist your teams can use day-to-day.
Integrations with Repos, Pipelines and Cloud
Your platform should meet teams where they already work:
Native integrations with GitHub, GitLab, Azure DevOps, Jenkins and other CI/CD tools
Hooks into container registries, Kubernetes and cloud services on AWS, Azure and GCP for runtime enforcement
Developer-friendly UX: PR comments, IDE plugins and CLI workflows, not just another web console
This is particularly important for teams already working with Mak It’s web development, back-end development and mobile app development services, where integration depth often determines adoption.
GEO, Data Residency and Deployment Models
For US, UK and EU buyers, data residency often makes or breaks the deal.
US vs EU hosting options and EU-only data paths for German/EU workloads
On-prem, private cloud or VPC-isolated deployments for high-sensitivity sectors
Audit-ready reporting for regulators like BaFin, the FCA, HHS/OCR and data protection authorities
Local references say, a financial services client in London, a SaaS platform in Berlin or a healthcare provider near Frankfurt help prove that the platform already works in similar regulatory environments.
90-Day Rollout Plan for US, UK and EU Teams
Quick answer (AEO):
A pragmatic 90-day plan starts with visibility (SBOMs and dependency inventory), then pilots CI/CD guardrails in one product, and ends with standardized policies and board-level reporting.
Below is a simple how-to roadmap you can adapt to your own context.
Days 0–30 Baseline and Quick Wins
Identify critical applications and business services: payment rails, clinical systems, trading platforms, public-facing portals.
Generate initial SBOMs and dependency inventories for top-risk apps using automated tooling.
Assess current CI/CD setups, secrets management and third-party vendor exposure especially in systems that handle regulated data under GDPR, HIPAA or PCI DSS.
Aim to produce an initial “as-is” view you can show to your CISO, CIO and key product owners.
Days 31–60 Pilot SBOM and Dependency Controls
Roll out automated SBOM generation and SCA for one high-value product line (for example, a customer-facing web app hosted on Kubernetes).
Enable basic dependency policies and CI checks for new libraries, starting in one US squad (e.g. New York) and one EU/UK squad (e.g. London or Berlin)
Tune developer workflows so that SBOM and SCA results show up where engineers already work.
By the end of this phase, you should have a working slice of software supply chain security with SBOMs that proves value and informs your platform and tooling choices.
Days 61–90 Scale Policies, Reporting and Stakeholder Engagement
Standardise branch protection rules, required checks (SBOM, SCA, code review) and artifact signing across repositories and pipelines.
Build dashboards that tie risk metrics directly to NIST SSDF, NIS2 and DORA obligations so GRC, internal audit and regulators can all see progress.
Document a software supply chain security playbook: incident response steps for new CVEs, vendor due-diligence checklists and escalation paths.
If you need help, Mak It Solutions can bundle this into a scoped engagement: platform selection, integration work across web/mobile/data stacks, and enablement for engineering and GRC teams in the US, UK, Germany and the EU.
If you’re staring at a patchwork of SBOM pilots, ad-hoc dependency scans and fragile CI pipelines, you’re not alone and you don’t have to fix it alone. Mak It Solutions helps teams in New York, London, Berlin, Frankfurt and across the EU design and implement software supply chain security with SBOMs that regulators understand and engineers actually like using.
Ready to turn this 90-day plan into a concrete roadmap for your SaaS or regulated platform? Reach out to Mak It Solutions to schedule a short discovery call and get a scoped proposal for SBOM, dependency and CI/CD supply chain security aligned with your US, UK and EU obligations.( Click Here’s )
FAQs
Q : Do I need an SBOM for every release of my software, or only major versions?
A : In regulated or high-risk environments, you should generate an SBOM for every production build, not just major versions. Vulnerabilities are disclosed continuously, and even a minor dependency update can change your risk profile. Many organizations keep SBOMs for all supported versions so they can answer “are we exposed?” for any customer quickly, while archiving older SBOMs once products reach end of life. Automation in CI/CD makes this cheap enough that “every build” becomes the default.
Q : How is software supply chain security different from traditional application security testing?
A : Traditional application security testing (SAST, DAST, penetration tests) focuses mainly on your own code and runtime behavior. Software supply chain security widens the lens to include open-source dependencies, third-party components, build infrastructure, code signing keys and cloud deployment pipelines. It adds practices like SBOM management, SCA, CI/CD hardening and vendor due diligence so you can reduce “one-to-many” risk from upstream components and tooling, not just bugs in your own code.
Q : Are SBOMs mandatory under NIS2 or just a recommended best practice in the EU?
A : NIS2 doesn’t use the term “SBOM” in every article, but Article 21 explicitly requires supply chain security and better visibility into ICT and software components. Many EU regulators and sectoral schemes now interpret this as requiring SBOM-style transparency for critical software and services, especially when combined with ENISA guidance and CRA obligations. In practice, organizations treating SBOMs as “optional” today may find them de-facto mandatory in future audits, tenders or incident investigations.
Q : What should I ask third-party SaaS vendors about their software supply chain controls before signing a contract?
A : At minimum, ask whether they can provide SBOMs for key services, how they manage open-source dependencies, and whether they follow frameworks like NIST SSDF or SLSA for CI/CD security. Request sample reports from their SCA tooling, evidence of artifact signing and details of their vulnerability SLAs and incident notification timelines. For EU workloads, clarify how they comply with GDPR Article 28 and, where relevant, NIS2 and DORA. Build these expectations into contracts so you can enforce them throughout the relationship, not just at onboarding. ([NIST Computer Security Resource Center][8])
Q : How can small and mid-size engineering teams improve software supply chain security without a dedicated AppSec function?
A : Start small and automate as much as possible. Use managed or open-source SCA tools integrated into GitHub/GitLab, generate SBOMs in CI/CD and enforce simple policies like “no unknown or malicious packages” and “all builds must be signed.” Reuse public guidance from CISA, NIST and ENISA instead of inventing your own framework, and prioritise controls that reduce the most risk per hour invested: secrets management, MFA for CI, dependency inventory and basic vendor due diligence. Partnering with a services firm like Mak It Solutions lets you bootstrap design and implementation without hiring a full AppSec team on day one.



