GCC Sovereign Cloud and Data Residency Guide
GCC Sovereign Cloud and Data Residency Guide
GCC Sovereign Cloud and Data Residency Guide
GCC sovereign cloud and data residency mean running critical workloads on cloud infrastructure where Saudi Arabia, the UAE or Qatar keep legal, operational and security control, and where defined datasets must stay in-country. For 2026, CIOs and CISOs in Riyadh, Dubai, Abu Dhabi and Doha need a clear roadmap that classifies data, selects the right mix of sovereign, hybrid and multi-cloud, and can prove compliance to financial, telecom, government and privacy regulators.
2026 is a “no-delay” year for GCC sovereign cloud and data residency. Saudi Arabia’s PDPL is now fully enforceable, the UAE’s Federal Data Protection Law 45/2021 is embedded into digital government and private-sector operations, and Qatar’s 2024 QCB Cloud Computing Regulations are live for banks and fintechs.
At the same time, boards expect faster AI, mobile and smart-city platforms—often on hyperscale cloud. The real pain point for GCC leaders is simple: how to use cloud and AI at scale while staying compliant with PDPL, UAE data protection law and QCB rules, plus sector regulators like Saudi Central Bank (SAMA), TDRA and QCB.
Quick answer for CIOs in Riyadh, Dubai, Abu Dhabi and Doha:
Sovereign cloud is about who controls the infrastructure and data, not just where the data centre sits. Data residency and localization define which data must remain inside Saudi, UAE or Qatar, when it can move cross-border, and under what contractual, technical and regulatory safeguards.
This guide is written for CIOs, CISOs, Heads of IT and Heads of Compliance in large enterprises and regulators, as well as fast-growing fintech, health and logistics players across Riyadh, Jeddah, NEOM, Dubai, Abu Dhabi, Sharjah, Doha and Lusail.
What Is GCC Sovereign Cloud and Data Residency? (Definitions & Context)
What Is a Sovereign Cloud in the GCC Context?
In the GCC, a sovereign cloud is a cloud environment where infrastructure is physically located in-country and subject to that country’s laws, oversight and approved security controls. Typically it is operated by a national provider or a tightly governed joint venture, with controls aligned to frameworks like Saudi’s NCA Cloud Cybersecurity Controls (CCC) and UAE federal cloud requirements.
By contrast, a normal public cloud region in the “Middle East” might be technically nearby but still governed by foreign law, with support, operations or backup taking place outside the GCC. For Saudi, UAE and Qatar entities handling regulated or strategic workloads, that distinction—who can compel access, where admin operations happen, how keys are held is exactly what sovereign cloud is designed to solve.
Data Residency vs Data Localization vs Data Sovereignty
Data residency: where your data primarily lives.
Example: a Saudi ecommerce platform hosting customer profiles in an AWS Bahrain database to reduce latency and support GCC data sovereignty and digital trust.
Data localization: strict rules that certain categories (e.g. Saudi banking, national ID, health records) must stay inside the country, often at a specific classification level under the National Data Management Office (NDMO) framework.
Data sovereignty: the overarching principle that data is subject to the laws, courts and regulators of the country where it is collected/held critical for PDPL, UAE DP law and Qatar’s financial sector rules.
For example, a Saudi bank might localize core transaction data in Riyadh while allowing anonymised analytics to run in another GCC region. A UAE ecommerce brand, meanwhile, may keep payments and ID documents in a UAE sovereign cloud but use global regions for catalog search and A/B testing.
Why 2026 Is a Breakpoint Year for GCC Cloud Strategy
Several timelines converge in 2026.
Saudi’s PDPL grace period ended in September 2024; SDAIA has issued guidance on cross-border transfers, DPOs and retention, and regulators are now actively expecting compliance evidence.
The UAE’s Federal Decree-Law No. 45 of 2021 on Personal Data Protection is fully in force alongside sectoral rules (health, banking, telecom), and TDRA continues to mature its sovereign cloud and FedNet-style initiatives.
Qatar Central Bank (QCB)’s Cloud Computing Regulations came into effect in April 2024, requiring approvals, robust risk management and, for some workloads, in-country hosting.
At the same time, hyperscalers and regional providers are ramping up sovereign and AI cloud offerings e.g. AI campuses and sovereign stacks in Abu Dhabi and Riyadh pushing CIOs to lock in an operating model that will last beyond a single project.
GCC Data Residency and Privacy Laws in Saudi, UAE and Qatar
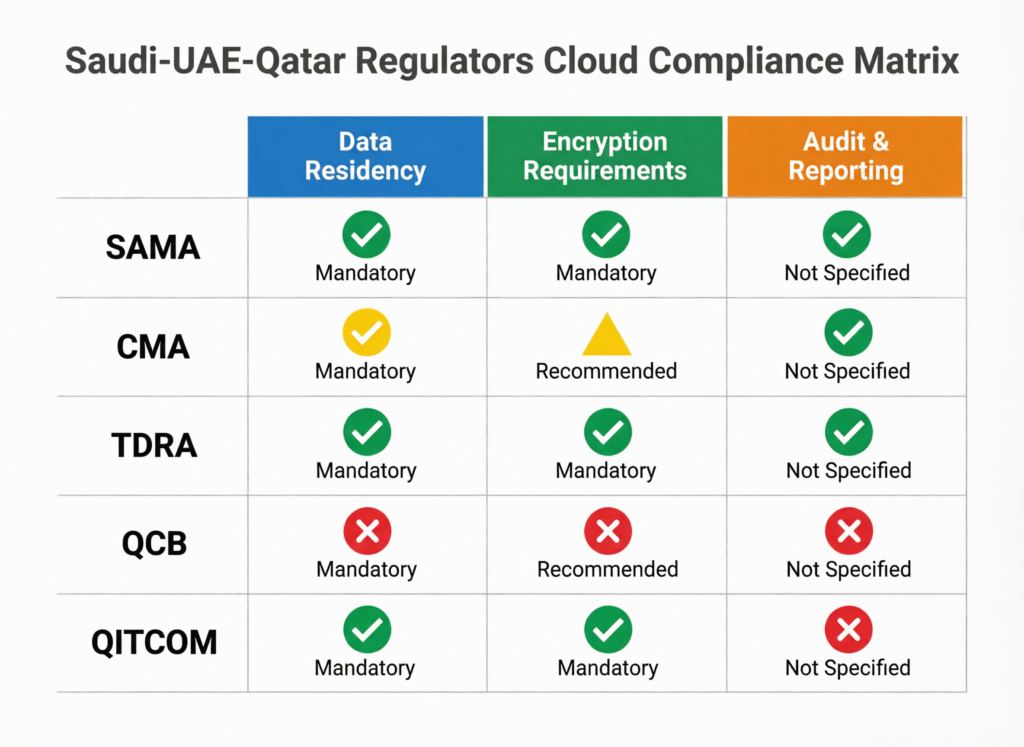
Saudi Arabia PDPL, NDMO/NCA and Sector Regulators (SAMA, NCA, SDAIA)
Saudi’s PDPL, overseen by Saudi Data & AI Authority (SDAIA), is now fully enforceable and places strict conditions on transferring personal data outside the Kingdom, including adequacy assessments, contractual safeguards and approvals in some cases.
Under NDMO data governance policies, government and many regulated entities must classify data (Public, Confidential, Secret/Top Secret) and host higher-classified datasets on infrastructure controlled within Saudi. The National Cybersecurity Authority (NCA) adds Cloud Cybersecurity Controls that push banks, telecoms and government agencies to use compliant providers and maintain detailed logging, key management and tenancy isolation.
For financial services, SAMA expects clear data residency, outsourcing and cloud-risk frameworks, particularly as Saudi Open Banking and digital-only banks scale.
UAE Federal DP Law 45/2021, TDRA and Federal Cloud Initiatives
The UAE’s Federal Decree-Law 45/2021 applies broadly to onshore UAE entities and requires lawful bases, clear notices, purpose limitation and rights for data subjects, along with controls over international transfers.
Telecoms and digital government are overseen by the Telecommunications and Digital Government Regulatory Authority (TDRA), which also recognizes and coordinates with cloud service providers through programmes like the CLSP information form and sovereign cloud initiatives built over the Federal Digital Network (FedNet)
For public-sector workloads in Abu Dhabi, Dubai and Sharjah, UAE Pass and national digital identity flows mean ID, authentication logs and some transaction data are treated as sensitive and often expected to remain in accredited UAE or GCC sovereign environments.
Qatar QCB Cloud Computing Regulations 2024 and Digital Sovereignty
Qatar’s 2024 QCB Cloud Computing Regulations define how banks, insurers and fintechs may use cloud, with a strong emphasis on governance, risk management, contractual safeguards and data protection.
“In-country” typically means using data centres physically located in Qatar (or QCB-approved alternatives) for critical financial and payment data. Cross-border processing is allowed under conditions: QCB approval, clear mapping of data flows, strong encryption and the ability to produce logs and records on demand.
These rules fit into Qatar’s broader digital sovereignty and AI agenda, including guidance for AI use by QCB-licensed entities that stresses governance, risk management and data controls.
Cloud Compliance for Regulated Sectors in the GCC
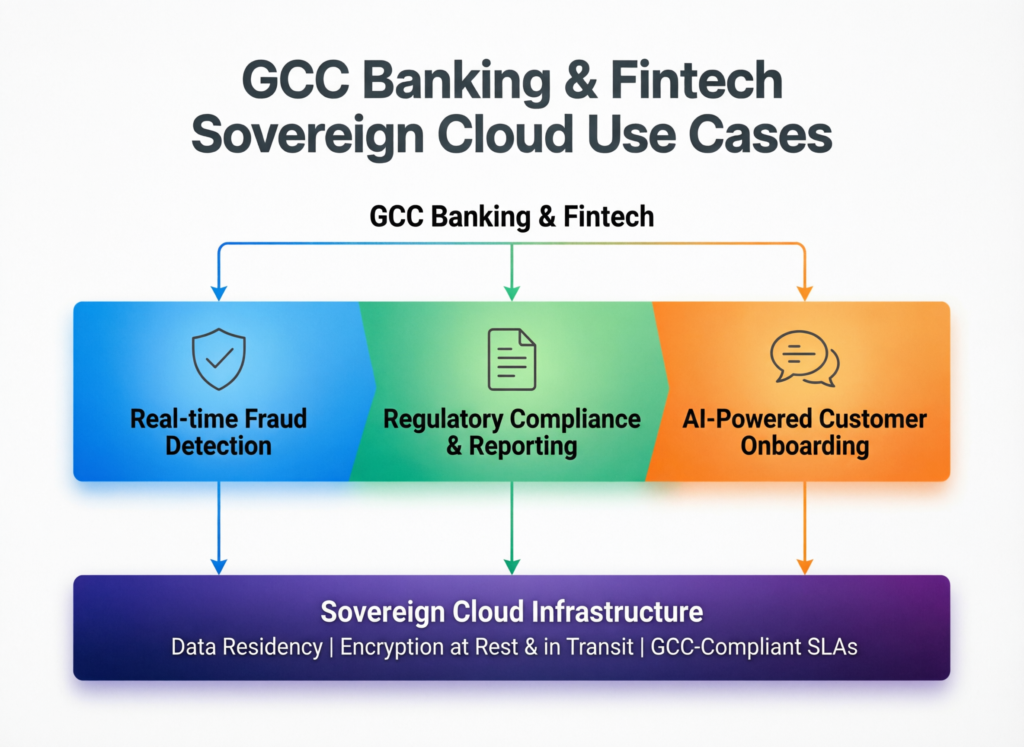
Banking and Fintech SAMA, QCB, UAE Central Bank Expectations
Typical regulated workloads include core banking systems, Open Banking APIs, payment gateways, AML/KYC engines and digital channels. In practice.
A Riyadh fintech might keep core ledgers and identity data in a Saudi-based sovereign cloud, while running fraud analytics in a regional GCC region using tokenised data, in line with SAMA and NCA expectations.
A Dubai bank under UAE Central Bank oversight and operating in Dubai International Financial Centre (DIFC) could place mission-critical workloads in an approved UAE sovereign cloud, while using global regions for sandbox and partner test environments, governed by strong contractual and encryption controls.
A Doha-based Islamic bank following QCB rules might host its Qatar bank cloud solution under QCB regulations in a local data centre or sovereign cloud, using cross-border analytics only for properly anonymised datasets.
Sharia-compliant fintech must also align with Islamic finance governance while still meeting data residency rules Mak It Solutions explores this intersection more deeply in its guide on sharia-compliant digital banking in the GCC. (Mak it Solutions)
Government and Smart City Programs in Riyadh, Dubai, Abu Dhabi and Doha
Government and smart-city platforms in Riyadh, Jeddah and NEOM rely on GCC data sovereignty and digital trust as a foundation: citizen services, traffic systems, IoT sensors and digital identity cannot depend solely on offshore regions. Saudi DGA, NDMO and NCA frameworks all reinforce this.
In Dubai, Abu Dhabi and Sharjah, smart-city and federal e-government platforms often use UAE sovereign cloud options or closely governed UAE regions, combining TDRA, UAE DP law and sectoral standards.
In Doha and Lusail, smart-stadium, transport and e-government services typically leverage local data centres and, increasingly, Qatar-hosted AI and analytics platforms to keep operational and citizen data inside the country while still integrating with global partners.
Healthcare, Identity and Citizen Data Workloads
Health records, national ID and citizen digital identity systems are among the most sensitive workloads in KSA, UAE and Qatar:
Saudi’s digital ID, health platforms and Vision 2030 programmes strongly encourage local hosting and robust access controls. (Mak it Solutions)
In the UAE, healthcare data is subject to specific health regulations that sit on top of DP Law 45/2021, pushing hospitals and healthtech to use local or GCC-based cloud with strong encryption and logging.
In Qatar, health data and citizen services on portals like Hukoomi must respect local privacy and security requirements, even when using regional cloud providers.
For these workloads, encryption, hardware security modules, fine-grained access controls and auditable logs are not “nice to have”they are the evidence your regulator will ask for.
GCC Cloud Operating Models Under Sovereignty Constraints
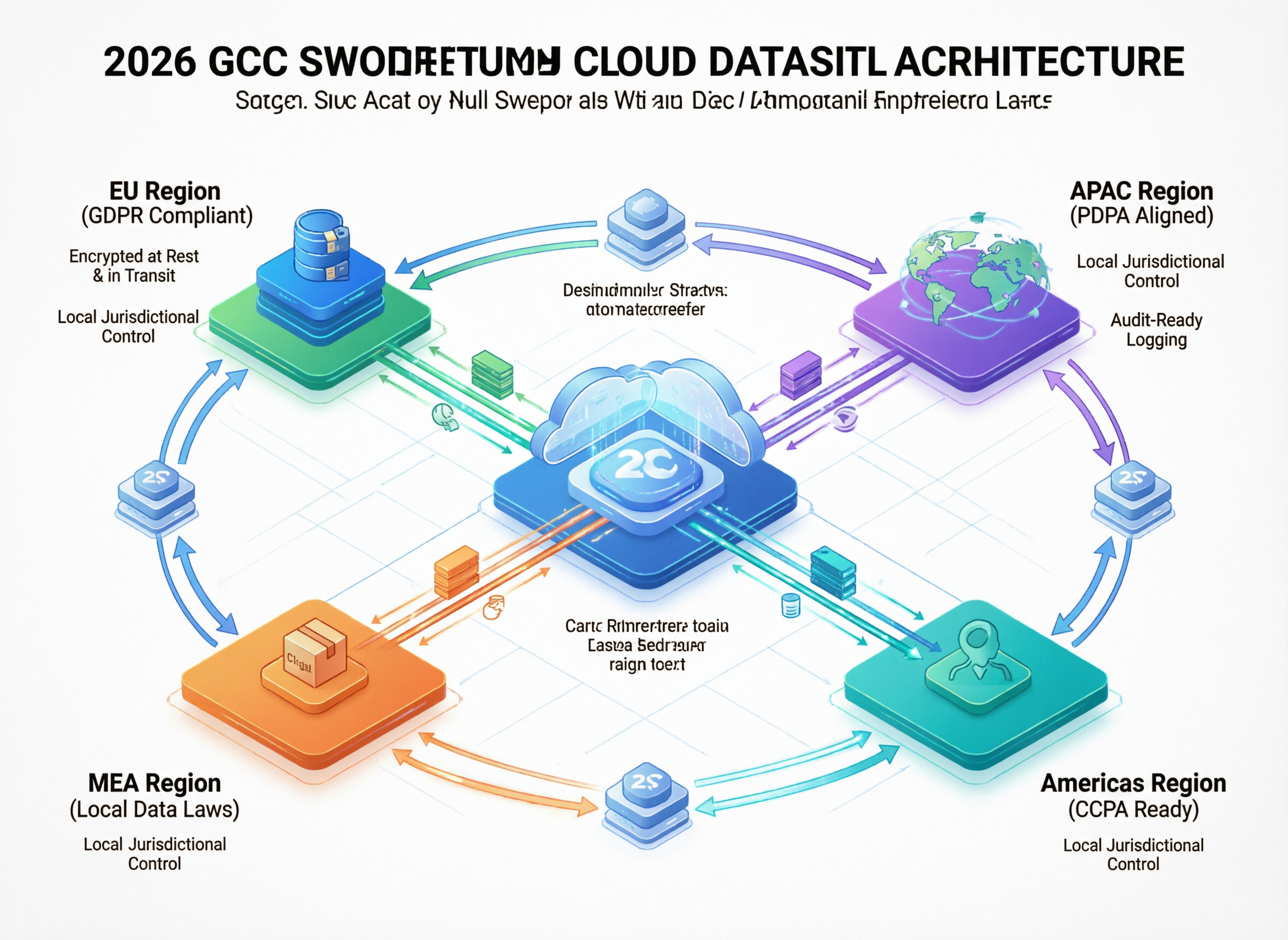
Hybrid, Multi-Cloud and Sovereign Landing Zones (SLZ) for the GCC
Most GCC organizations land on some mix of
Hybrid: on-prem in Riyadh or Dubai plus sovereign region plus global region—for example, core systems in Saudi data centres, analytics in AWS Bahrain, and DR in another GCC location.
Multi-cloud: combining AWS Bahrain, Azure UAE Central and GCP Doha to balance data residency with AI and analytics capabilities. (Mak it Solutions)
Sovereign Landing Zones (SLZs): pre-approved cloud baselines (networking, IAM, logging, encryption, patterns) designed to satisfy NCA, PDPL, TDRA or QCB expectations from day one.
Public-sector teams in Dubai or Abu Dhabi might maintain a UAE-sovereign landing zone for citizen services and a separate, more flexible landing zone for corporate or international workloads.
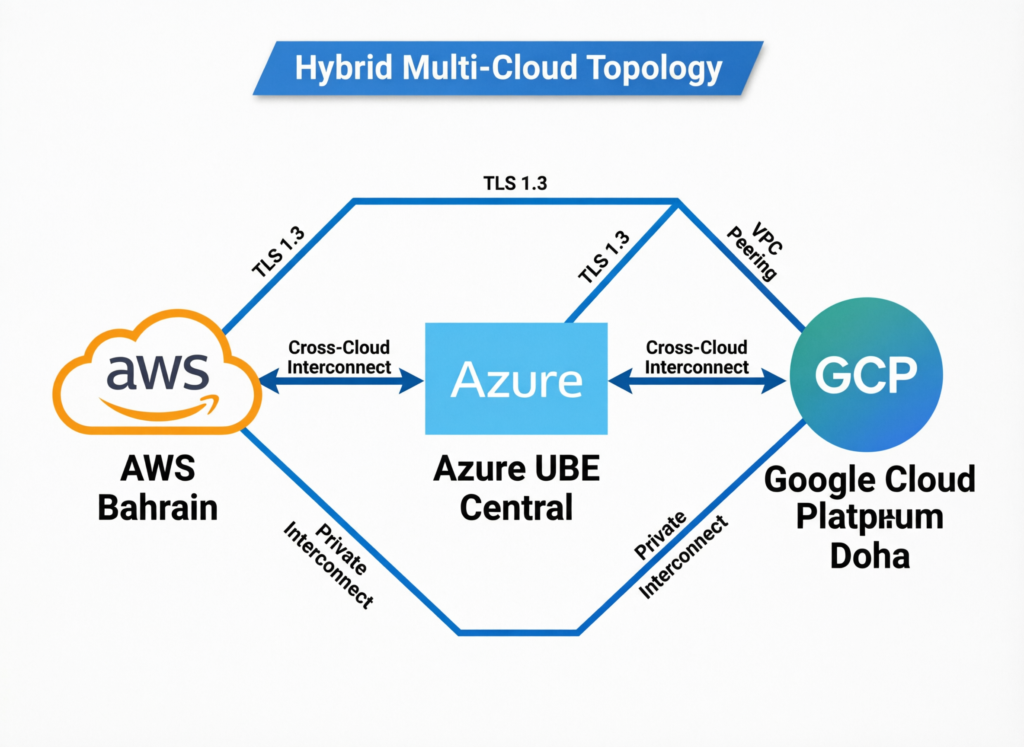
Data Residency Controls, Key Management and Encryption by Design
A GCC-ready design usually includes.
In-country key management and HSMs, with keys held under national jurisdiction.
Clear segmentation of “in-country only” datasets (e.g. Saudi PDPL and SAMA-regulated data) versus data that can be replicated to other GCC or global regions.
Centralised telemetry, immutable logging and evidence packs that map directly to NCA CCC, PDPL, UAE DP Law and QCB cloud requirements.
This is also where Mak It Solutions often pairs architecture work with business intelligence services and web development services so dashboards, portals and APIs are aligned with residency and audit needs from day one. (Mak it Solutions)
Architecting for AI: Training, Inference and Model Hosting Under GCC Rules
AI adds another layer
Training models on raw Saudi banking or health data will often have to happen in Saudi or an approved sovereign AI cloud, with strict anonymisation or tokenisation if any processing moves outside the Kingdom.
UAE government data may need to stay in UAE sovereign or accredited federal clouds, while private-sector datasets can use regional or global AI platforms if DP Law 45/2021 transfer rules and TDRA expectations are met.
In Qatar, QCB’s AI guidelines for financial institutions emphasise governance, explainability, data governance and security controls for AI systems that touch customer or transaction data.
For large AI workloads, Mak It Solutions’ playbook on FinOps for AI and GPU cost control can be combined with GCC residency requirements to keep both cost and compliance under control. (Mak it Solutions)
Cost, Risk and Timeline for GCC Sovereign Cloud Programs
Cost Drivers In-Country Regions, Sovereign Services and Compliance by Design
Sovereign cloud and strict GCC data residency are more expensive than “vanilla” cloud.
Premium pricing for sovereign or telco-hosted regions.
Additional spend on HSMs, private connectivity and local support.
Hidden costs: legal opinions on PDPL/DP Law transfers, QCB approvals, audits and contracted SLAs for exit or migration.
For UAE organisations choosing between global public regions and UAE sovereign cloud options that meet TDRA and federal requirements, a simple lens is.
Put citizen, regulated financial, critical infrastructure and national-ID linked data in UAE-sovereign or TDRA-aligned clouds.
Use global regions for less sensitive workloads only when transfer rules, encryption and vendor risk are fully documented and approved.
Risk Trade-Offs Regulatory, Operational and Vendor Risk
Key trade-offs:
Regulatory risk: PDPL breaches, QCB non-compliance or misaligned NCA controls can lead to fines, licence restrictions or reputational damage. (Hala Privacy)
Operational risk: over-complex hybrid/multi-cloud estates without clear RACI or observability.
Vendor risk: lock-in to a single regional sovereign provider vs more portable multi-cloud patterns, including the ability to shift between GCC regions over time.
A real-world example: a data leak at an Abu Dhabi finance conference highlighted the consequences of poorly configured third-party cloud services even outside core banking systems. (Reuters)
Typical Timelines for Saudi, UAE and Qatar Migration Programs
Indicative timelines (heavily simplified)
Assessment & design (3–6 months) data classification, regulatory mapping across KSA/UAE/Qatar, and reference architecture.
Build SLZ & controls (3–9 months) cloud landing zone, network, IAM, logging, key management, plus integration with SOC and SIEM.
Pilot migrations (3–6 months) one or two workloads (e.g. a Riyadh fintech app, a Dubai customer portal, a Doha analytics platform).
Full migration & optimisation (12–24+ months) especially for banks, governments and healthcare with deep legacy estates.
Governments and tier-1 banks often sit at the longer end; digital-native fintech or ecommerce brands can move much faster.
Building a 2026-Ready GCC Cloud Roadmap
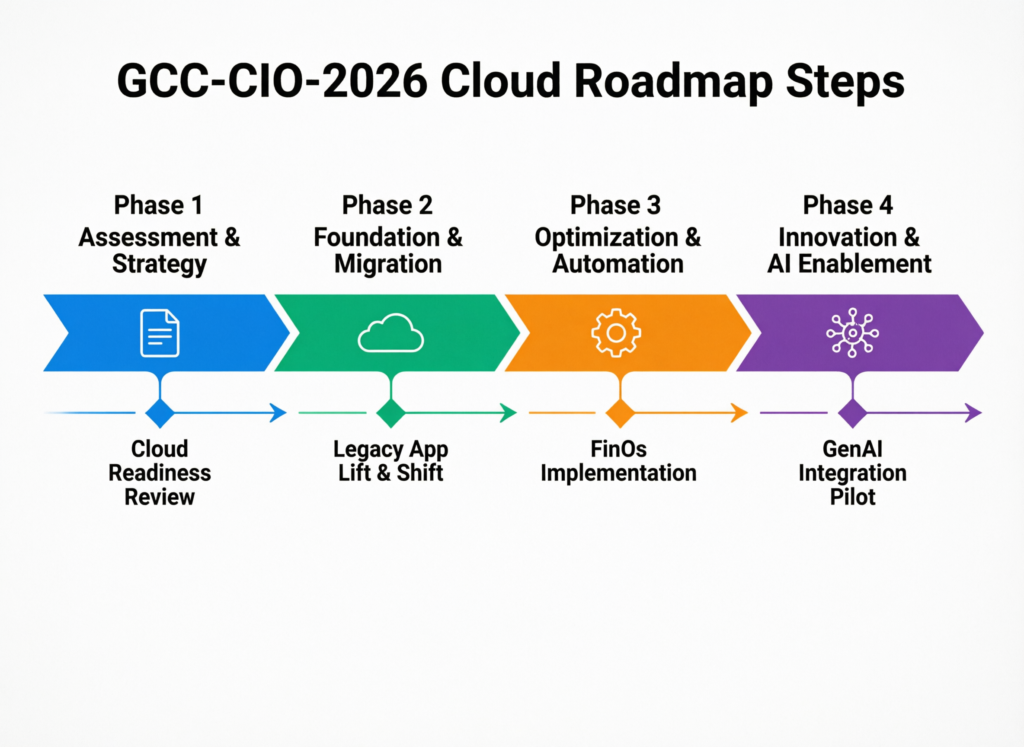
Step-by-Step Roadmap for GCC CIOs and CISOs
Short framework: classify, choose, design, prove.
Assess data & regulatory scope
Map personal, financial, citizen and operational data across KSA, UAE, Qatar; tie each domain to PDPL, UAE DP Law, QCB regs, SAMA/TDRA/NCA expectations and free-zone rules (e.g. Abu Dhabi Global Market (ADGM))
Choose operating model
Decide where you must be sovereign-only, hybrid or multi-cloud, and which providers meet regulator-approved or regulator-aligned criteria.
Design a minimum viable SLZ
Build a GCC-specific sovereign landing zone with guardrails, logging and key management that can be reused across workloads.
Sequence workloads
Start with high-impact but low-risk workloads (e.g. digital channels) before core banking or citizen systems.
Institutionalise continuous compliance
Embed controls, evidence collection and regular reviews into BAU.
Mak It Solutions often combines this roadmap with insights from Middle East cloud providers for KSA, UAE & Qatar CIOs and edge computing in the Middle East for Saudi & UAE to give GCC teams a realistic view of provider options and latency. (Mak it Solutions)
Governance, Operating Model and Skills for Sustained Compliance
A GCC-ready operating model usually includes:
A Cloud Center of Excellence (CCoE) in Riyadh, Dubai or Doha with representation from security, compliance, architecture and business.
Clear RACI for who can approve new cloud services, cross-border transfers and AI workloads.
Continuous posture management, using dashboards and BI built on internal and external telemetry so you can show regulators an up-to-date view on residency and security controls supported by partners like Mak It Solutions and its services portfolio. (Mak it Solutions)
Selecting Partners Hyperscalers, Telco-Cloud, Integrators and Advisors
When evaluating providers and partners, look for
Evidence of alignment with SAMA, TDRA, QCB, NCA and sectoral standards.
Real GCC case studies in fintech, government, healthcare or logistics (not just generic references).
Ability to support both sovereign and global regions, with credible exit strategies and portability.
For deeper digital and application work—for example, sovereign-ready citizen portals or ecommerce platforms it helps to partner with teams who understand both GCC cloud and modern web, such as Mak It’s work on web development trends in the Middle East for KSA & UAE. (Mak it Solutions)
Concluding Remarks
GCC sovereign cloud and data residency are no longer niche compliance topics; they are central to how GCC organisations compete, unlock AI and digital services, and maintain trust with citizens, customers and regulators. Saudi PDPL enforcement, UAE DP Law 45/2021 and QCB’s 2024 cloud regulations mean 2026 is the year when “we’ll fix it later” is no longer acceptable.
A simple 2026-readiness checklist for Saudi, UAE and Qatar teams:
Have we classified our data and mapped it to each country’s rules?
Do we know which workloads must be sovereign, and which can safely use regional/global cloud?
Can we produce clear, regulator-friendly evidence for residency, encryption, logging and AI workloads?
If any answer is “no” or “not sure”, it’s time to run a focused GCC cloud strategy and architecture review before your next regulator visit or board strategy session.
If you’re leading IT, security or compliance in Riyadh, Dubai, Abu Dhabi or Doha and need to turn regulations into a practical cloud roadmap, you don’t have to do it alone. Mak It Solutions can help you assess your current workloads, design GCC-ready sovereign landing zones, and plan migrations that balance AI scale with Saudi, UAE and Qatar data residency rules. Explore our services and related guides such as Middle East cloud providers for KSA, UAE & Qatar CIOs, then reach out for a consultation tailored to your regulatory footprint and growth plans. (Mak it Solutions)
FAQs
Q : Can Saudi government or banking data be stored outside the Kingdom under PDPL and SAMA rules?
A : In general, sensitive Saudi government and banking data is expected to stay inside the Kingdom, especially when it includes personal data covered by PDPL or regulated financial information. Cross-border transfers are only allowed in specific circumstances, such as when adequate protection, contractual safeguards and, in some cases, regulatory approvals are in place. For banks, SAMA (Saudi Central Bank) and the National Cybersecurity Authority also impose strict outsourcing and cloud security conditions, so any offshore hosting should be carefully assessed and documented, not treated as a default.
Q : Is data residency mandatory for all workloads hosted on cloud in the UAE, or only specific sectors?
A : The UAE’s DP Law 45/2021 does not force all cloud workloads to remain onshore, but it sets conditions for any transfer of personal data outside the UAE, including appropriate safeguards and, in some cases, adequacy assessments. Sectoral regulators and frameworks then add stricter rules for specific sectors such as banking, telecoms and healthcare. TDRA and UAE federal digital government strategies push many public-sector workloads toward UAE sovereign cloud or accredited providers, while private-sector organisations can often blend onshore and offshore regions if they follow the law and keep strong records of where data goes and why.
Q : How can Qatar banks use global public cloud providers while still complying with the 2024 QCB Cloud Computing Regulations?
A : Qatar banks can use global public cloud providers, but only within the framework set by QCB’s 2024 Cloud Computing Regulations. That usually means obtaining QCB approval for material cloud outsourcing, keeping critical financial and payment data in Qatar or an approved location, implementing strong encryption and access controls, and ensuring that QCB can access logs, audit trails and systems when required. Banks should also align cloud contracts with QCB requirements for incident response, subcontracting and exit, and consider how QCB’s AI guidelines apply if they use cloud-based AI services for credit, fraud or customer analytics.
Q : What are the key differences between hosting in a sovereign GCC cloud vs a standard Middle East public cloud region?
A : A sovereign GCC cloud is typically designed so that infrastructure, operations and legal jurisdiction sit firmly under a specific country’s control, with requirements aligned to frameworks from bodies like NCA, SDAIA, TDRA, QCB or national digital authorities. A standard Middle East public cloud region might be physically close but subject to foreign laws, with some admin and support functions located elsewhere. For workloads regulated under Saudi PDPL, UAE DP Law or QCB rules, sovereign options reduce legal and geopolitical risk, at the cost of higher pricing and sometimes fewer services; less sensitive workloads can safely use standard regions if transfers and security controls are properly designed and documented.
Q : Do GCC companies need separate cloud strategies for Saudi, UAE and Qatar when operating across multiple jurisdictions?
A : Most GCC groups do need some level of country-specific cloud strategy, because Saudi PDPL, UAE DP Law and Qatar’s banking and data regulations are similar in spirit but different in detail. A practical pattern is to define a single GCC cloud and data governance framework, then add country addenda for PDPL, TDRA and QCB requirements, and any sector-specific rules (e.g. ADGM/DIFC for financial entities). In practice, that could mean one shared multi-cloud architecture across AWS Bahrain, Azure UAE Central and GCP Doha, with stricter routing and classification for Saudi, UAE or Qatar-origin data. This approach also aligns well with Saudi Vision 2030 and wider GCC digital-economy integration. (Mak it Solutions)


