Phishing Resistant MFA Solutions for US, UK & EU Security Teams
Phishing Resistant MFA Solutions for US, UK & EU Security Teams

Phishing Resistant MFA Solutions for US, UK & EU Security Teams
Phishing resistant MFA uses origin-bound, cryptographic authenticators (such as passkeys and FIDO2 security keys) that can’t be replayed on fake sites or intercepted by adversary-in-the-middle (AiTM) proxies. In 2026, security and compliance teams in the US, UK and EU should prioritise replacing SMS codes and basic push prompts with passkeys, FIDO2/WebAuthn and secure device-bound factors for high-risk access.
Introduction
Phishing-resistant MFA is no longer “nice to have” it’s becoming the baseline for protecting identities, SaaS and cloud workloads across the United States, United Kingdom, Germany and the wider European Union. In 2025, one industry analysis estimated credential theft had surged by around 160%, accounting for roughly one in five breaches. Verizon’s 2024 Data Breach Investigations Report still shows stolen credentials as the top initial action in breaches at about 24% of cases.
Meanwhile, Microsoft reports blocking roughly 7,000 password attacks per second, with over 99% of 600 million daily identity attacks still targeting passwords. Legacy MFA (SMS, email OTP, simple pushes) slows attackers down, but AiTM phishing kits, MFA bombing and social engineering mean it no longer reliably stops account takeover.
Phishing-resistant multi-factor authentication (MFA) uses origin-bound, cryptographic authentication for example passkeys and FIDO2/WebAuthn security keys that simply cannot be replayed on look-alike domains or relayed through proxy phishing kits. This guide explains what counts as phishing resistant MFA in 2026, why regulators are pushing for it, and how to migrate from SMS/OTP without breaking your estate.
Quick compliance note
This guide is for general security and compliance awareness only. It’s not legal advice; always align decisions with your own counsel and regulators.
The 2026 Reality: MFA Phishing Kits and Compliance Pressure
Phishing-as-a-Service and AiTM kits now routinely support MFA bypass, token theft and 2FA relay. Reports in 2025 show the median victim count per phishing kit deployment more than doubling since 2021, with increasingly polished kits targeting Microsoft 365, banking and government portals.
Frameworks like NIS2, DORA, PCI DSS 4.0, OMB M-22-09 and updated UK NCSC guidance all lean toward “strong” or phishing-resistant MFA for privileged and high-risk access, not just “any MFA”.For CISOs in New York, London, Berlin or Frankfurt this is now both a threat issue and an audit issue.
What “Phishing Resistant MFA” Means in Practice
Phishing-resistant MFA means authenticators that don’t rely on shared secrets (like OTP codes) and are bound to a specific origin (relying party). In practice, this usually means.
Passkeys (synchronised or device-bound) in browsers and OS login
FIDO2 security keys using WebAuthn and CTAP
Smartcards / PIV in some federal and critical-infrastructure environments
These factors provide verifier impersonation resistance and are explicitly called out by CISA, NIST, the UK National Cyber Security Centre (NCSC) and ENISA as the gold standard.
Who This Guide Is For (CISOs, IAM Leads, Compliance Owners)
This guide is written for CISOs, IAM leads, security architects and compliance owners who.
Must align with NIST SP 800-63-4, OMB M-22-09, NIS2, DORA, PSD2 SCA, GDPR/UK-GDPR and PCI DSS 4.0.
Are already running an IdP such as Microsoft Entra ID, Okta or Duo Security.
Need a pragmatic, 90-day path from SMS/OTP to adversary-in-the-middle (AiTM) resistant MFA across VPNs, SaaS and legacy apps.
If you’re modernising IAM or Zero Trust and need hands-on help, Mak It Solutions already supports identity-first architectures and secure web/mobile builds for clients in the US, UK, Germany and wider EU. ( Mak it Solutions )
What Is Phishing-Resistant MFA?
Phishing-resistant multi-factor authentication in 2026 means MFA mechanisms that cannot be fooled by fake websites, deceptive links or proxied sessions. They rely on public-key cryptography, origin binding and verifier impersonation resistance rather than OTP codes or shared secrets.
Phishing Resistant Multi-Factor Authentication vs Traditional MFA
Phishing-resistant MFA uses origin-bound cryptographic keys (passkeys, FIDO2 security keys, smartcards), while traditional MFA depends on shared codes like SMS, email OTP or simple push approvals that attackers can relay or steal.
In other words: traditional MFA proves you know or receive a code; phishing-resistant MFA proves you control a private key that will only talk to the real site. That’s why CISA and others explicitly recommend FIDO-based or PKI-based approaches as the preferred controls.
Origin-Bound Credentials & Verifier Impersonation Resistance
Two core properties define phishing-resistant MFA.
Origin-bound credentials
Each credential is tied to a specific domain (relying party) via WebAuthn.
Even if a user clicks a phishing link, the authenticator refuses to sign for the wrong origin.
This is what makes FIDO2/WebAuthn and passkeys adversary-in-the-middle (AiTM) resistant.
Verifier impersonation resistance
The server (verifier) can’t be impersonated by a proxy that simply forwards requests.
The authenticator signs a challenge that includes the origin; a proxy can’t change this without detection.
You will also see regulators increasingly use “phishing-resistant” as a label for authenticators in AAL2+ or AAL3 tiers in NIST SP 800-63-4.
Examples of Phishing-Resistant MFA Factors in 2026
In 2026, practical examples include.
Passkeys in Chrome, Safari and Edge on desktop and mobile.
FIDO2/WebAuthn security keys from vendors like Yubico and others.
Platform authenticators (Windows Hello for Business, Apple Face ID/Touch ID, Android device credentials) bound via WebAuthn.
Smartcards / PIV / eID tokens in US federal and some EU KRITIS contexts.
Most organisations will run a mixed estate: platform authenticators for day-to-day sign-in, plus roaming FIDO2 keys for admin, SOC and break-glass accounts.
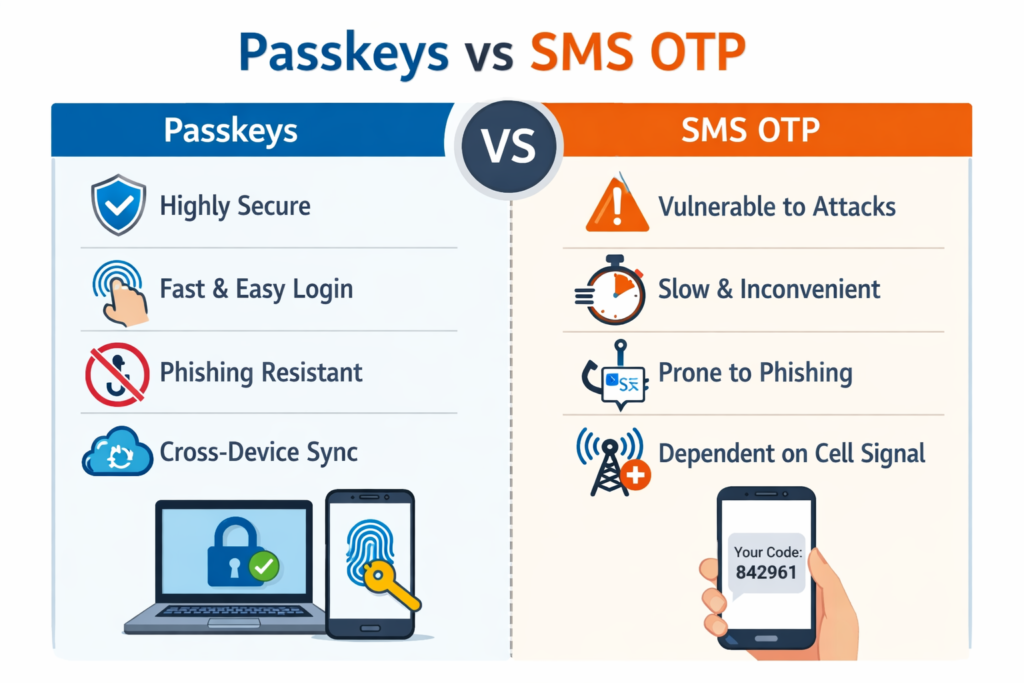
Why SMS Codes and Basic Push Prompts No Longer Count
SMS OTPs and basic push approvals are not phishing-resistant because attackers can relay them through fake sites and automated phishing kits, or trick users into approving fraudulent prompts.
How AiTM Phishing Kits Steal OTPs and Session Tokens
Modern AiTM kits sit between the user and the real site, proxying the full TLS session.
The user opens a phishing link that looks like the real IdP or VPN portal.
The kit relays username, password and SMS/OTP to the real service in real time.
Once MFA succeeds, the kit steals session cookies or tokens and replays them.
Reports show AiTM and PhaaS kits have seen triple-digit growth, with one dataset citing a 146% year-on-year increase in AiTM-style phishing attacks in 2024. Any OTP-based factor can be relayed in this way, making it non-compliant with stricter definitions of phishing-resistant MFA.
Push Fatigue, MFA Bombing and Social Engineering Weaknesses
Push fatigue attacks bypass crypto entirely.
Attackers bombard users with push notifications (MFA bombing)
Users approve “just to stop the noise” or because the attacker poses as IT.
One study found hundreds of thousands of MFA fatigue attacks in a single year, with around 1% of users blindly approving the first push they see. That 1% is more than enough for attackers targeting your finance, HR or admin accounts.
Number-matching and device-bound pushes help, but they are still fundamentally knowledge/consent-based factors that can be socially engineered, not true verifier impersonation-resistant MFA.
Where Legacy MFA Still Shows Up in Your Estate
Even in mature US/UK/EU organisations, you’ll still find legacy MFA in.
VPNs and VDI using RADIUS with SMS or OTP tokens.
Legacy web apps without modern OIDC/SAML support.
Remote access tools and vendor portals.
Customer-facing journeys (e-banking, citizen portals) still using SMS under PSD2 SCA.
A first task in any migration is simply mapping these journeys Mak It Solutions often pairs this with IAM discovery during broader cloud and web modernisation projects. ( Mak it Solutions )
The Technology Stack Behind Phishing-Resistant MFA
Passkeys, FIDO2, WebAuthn and CTAP form the backbone of phishing-resistant authentication plus the IdPs and gateways that integrate them.
Passkeys and FIDO2/WebAuthn security keys are phishing-resistant because they cryptographically bind each credential to a specific website (relying party), so credentials cannot be replayed on look-alike domains.
Passkeys and Device-Bound Credentials in the Browser and OS
Passkeys are essentially user-friendly FIDO credentials that live in the OS or browser.
Device-bound passkeys stay on one device (e.g. hardware-backed secure enclave)
Synced passkeys are stored in platform clouds (Apple, Google, Microsoft) and synced with end-to-end encryption.
They provide origin-bound, cryptographic authentication with strong UX: biometric or PIN, no codes. For US and EU enterprises already standardising on passkeys for customer login, extending them to workforce sign-in via FIDO Alliance-aligned IdPs is a natural next step.
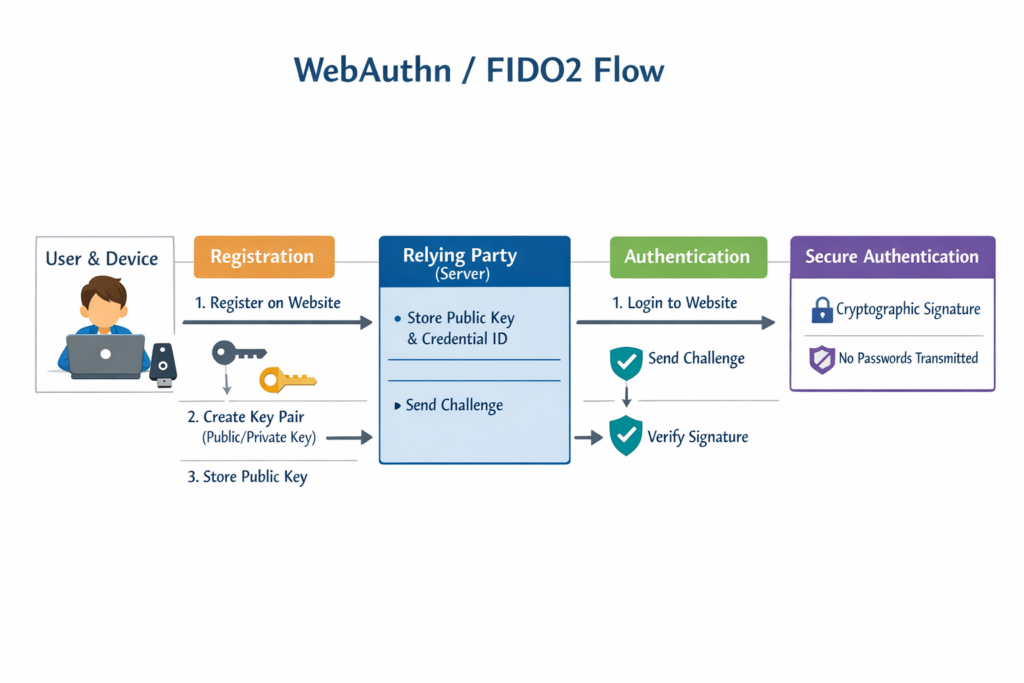
FIDO2 Phishing Resistant Authentication and WebAuthn Flows
FIDO2 comprises
WebAuthn (W3C) browser APIs and server protocol for registration and authentication.
CTAP protocol between the platform and external security keys.
A normal WebAuthn flow
The server issues a challenge and indicates the expected relying-party ID (RP ID)
The authenticator signs the challenge including that RP ID with the private key.
The server verifies the signature and RP ID before issuing a token.
Because the RP ID is baked into the signature, an AiTM kit pretending to be your IdP cannot rebind the challenge to a different domain. That’s what gives WebAuthn its verifier impersonation resistance.
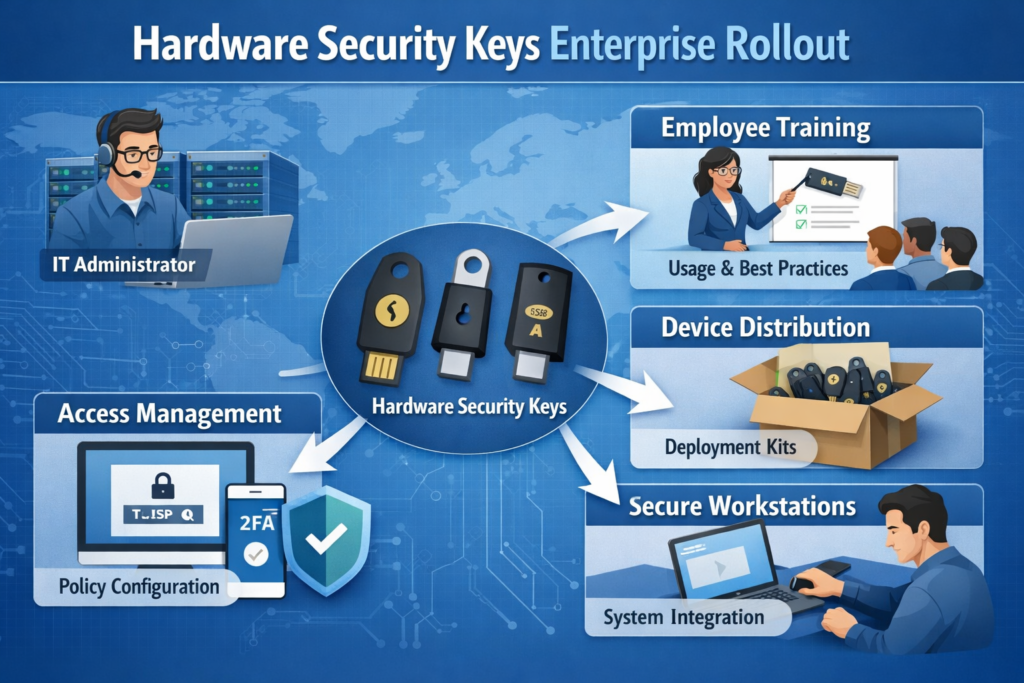
Security Keys and Platform Authenticators Side by Side
Many US, UK and EU organisations run a hybrid model.
Platform authenticators (Windows Hello, Touch ID, Android) for most employees.
Hardware security keys for admins, SOC, finance and high-risk roles.
Vendors like Yubico, Feitian and others supply FIDO2 keys; IdPs like Okta, Microsoft Entra ID and Duo Security offer policy engines and enrolment flows.
The trick is to design enrolment, recovery and step-up flows that keep UX smooth while delivering AiTM-resistant MFA for the highest-risk journeys.
Compliance Drivers in the US, UK and EU
Across US, UK and EU regulations, phishing-resistant MFA is emerging as the default expectation for high-risk access: federal and public-sector systems, financial services, and operators of essential and critical infrastructure.
United States.
Draft NIST SP 800-63-4 updates explicitly push stronger authenticators:
AAL2 solutions must offer users a phishing-resistant option.
AAL3 requires hardware-bound, public-key based authenticators.
OMB M-22-09, the US Federal Zero Trust strategy memo, requires agencies to use strong, phishing-resistant MFA at the application layer for staff and contractors.CISA reinforces this in its “Implementing Phishing-Resistant MFA” fact sheet and Zero Trust maturity model.
For US financial services and healthcare, PCI DSS 4.0 and HIPAA/HHS guidance also expect robust MFA for administrative access and remote access to cardholder or ePHI systems, increasingly interpreted as passkeys/FIDO2 for privileged users.
United Kingdom.
Updated MFA guidance from the UK National Cyber Security Centre (NCSC) is blunt: not all MFA is equal, and organisations should prefer FIDO2 or similarly strong phishing-resistant methods over SMS and basic push.
Cyber Essentials and the NCSC Cyber Assessment Framework (CAF) don’t yet mandate passkeys everywhere, but they increasingly expect.
MFA on all remote admin and cloud admin interfaces.
Strong authentication for SaaS used by critical services like the NHS.
For London-based financial or public-sector organisations, using SMS OTP for cloud admin in 2026 will be a hard sell to auditors.
Germany & EU.
The European Commission’s NIS2 directive sets a much higher bar for “essential” and “important” entities, including KRITIS operators in Germany. It explicitly calls out MFA for remote access and privileged accounts, and ENISA guidance strongly recommends phishing-resistant MFA, warning against SMS/voice.
In the EU financial sector.
PSD2 SCA already mandates Strong Customer Authentication for payments; many banks in Berlin and Frankfurt are piloting passkeys.
DORA focuses on operational resilience but reinforces strong access controls and identity assurance.
PCI DSS 4.0.1 adds definitions for “phishing resistant authentication” in its glossary, aligning with passkeys/FIDO2 even though it still requires multi-factor, multi-category controls.
For German readers: phishing resistente MFA für NIS2 Compliance und kritische Infrastrukturen is rapidly becoming a board-level topic rather than a technical detail.
Migrating from SMS/OTP to Phishing-Resistant MFA
Organisations typically migrate from legacy MFA in phases: start with high-risk admin and remote access accounts, add passkeys or FIDO2 keys behind an identity provider, and use secure proxies or passwordless gateways for legacy apps.
Inventory MFA Journeys and Risk-Rank Your Applications
Start with a journey-level inventory, not just an app list.
Catalog all logins (workforce, contractors, partners, admin)
Note authentication methods (password only, SMS OTP, app push, SSO, passkeys)
Classify risk: data sensitivity, privilege level, internet-exposed vs internal.
Mak It Solutions often combines this with broader IAM discovery and cloud architecture reviews for example, mapping identity flows across Amazon Web Services (AWS), Microsoft Azure and Google Cloud Platform (GCP) as described in our cloud comparison and shadow IT guides. ( Mak it Solutions )
Design Target States by User Group
Define target patterns by cohort.
Admins / privileged IT always-on FIDO2/passkeys + hardware keys; conditional access with strict device & location checks.
Knowledge workers platform passkeys on managed devices, roaming keys for high-risk access.
Contractors/partners cross-tenant trust or external identities with phishing-resistant MFA where possible.
Tie these to business scenarios (e.g. developers in New York accessing staging in Berlin) and compliance drivers (GDPR/UK-GDPR, NIS2, sector regulators such as BaFin).
Handling Legacy Apps, VPNs and Non-FIDO-Capable Systems
For apps that can’t speak OIDC/SAML or WebAuthn, patterns include.
Reverse proxy / access gateways that terminate FIDO2/WebAuthn then pass Kerberos/NTLM/HTTP auth internally.
Agent-based connectors on legacy apps that trust SSO assertions from the IdP.
VPN migration from RADIUS + SMS to ZTNA/SDP with WebAuthn at the edge.
Our IAM-focused clients often pair this with web/app modernisation, as covered in Mak It Solutions’ work on web development and secure SaaS architectures. ( Mak it Solutions )
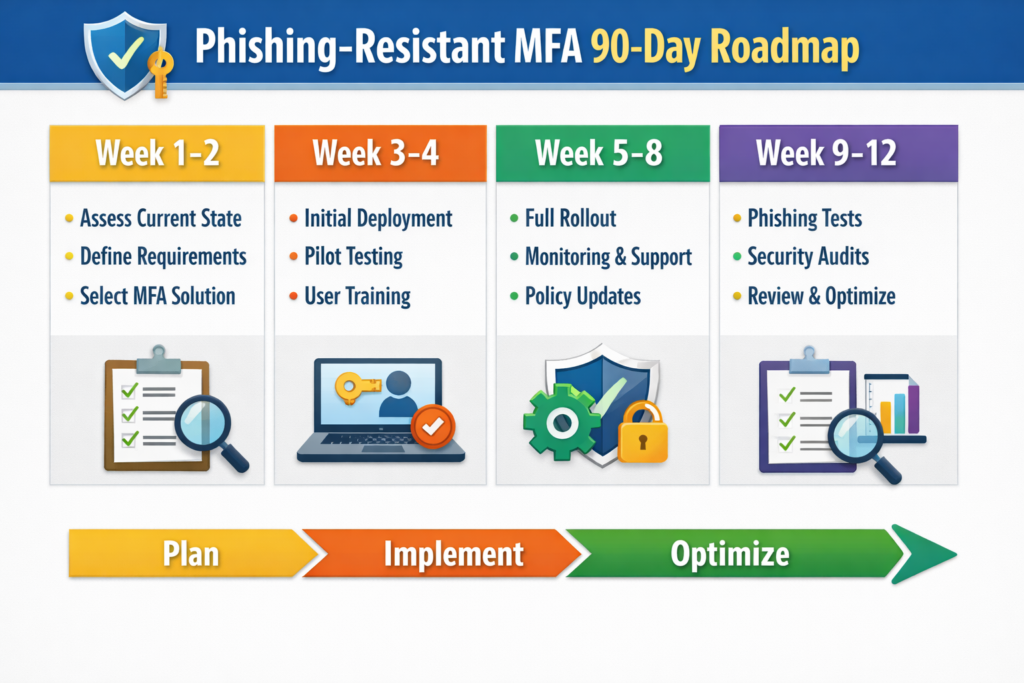
Rollout Patterns for US, UK and EU Organisations
A practical 90-day rollout pattern.
Weeks 1–4 pilot with security/IT admins in one region (e.g. London), focusing on enrolment UX and break-glass.
Weeks 5–8 expand to high-risk SaaS (finance, HR, data platforms) in US and EU offices.
Weeks 9–12 integrate VPN/VDI and legacy apps behind a proxy; roll out to the broader workforce.
For regulated environments (NHS trusts, EU KRITIS, US federal contractors), align the rollout with audit cycles and use internal champions to train non-technical staff. Mak It Solutions can help you structure this as a formal project with clear milestones and KPIs, similar to our IAM and cybersecurity programs for CIOs. ( Mak it Solutions )
How to Choose a Phishing-Resistant MFA Solution in 2026
The best phishing-resistant MFA solution balances FIDO2/passkey support, coverage for legacy systems, strong regulatory mapping (NIST, NIS2, PCI DSS 4.0) and an adoption-friendly user experience.
Core Evaluation Criteria: Security Strength, UX, Coverage and Total Cost
Key dimensions for your RFP.
Security genuine AiTM resistance, origin-bound credentials, verifier impersonation resistance.
Coverage WebAuthn and CTAP support, mobile apps, offline access, legacy protocols via gateways.
UX minimal prompts, clear recovery, device portability and strong push fatigue / MFA bombing protection.
Economics licensing vs hardware, lifecycle costs of issuing/replacing keys and support overhead.
Ask vendors to show live AiTM demos (phishing kit vs their solution) as part of evaluation.
Entra, Google Workspace, Okta and VPN/VDI Platforms
Check native support for
Workforce IdPs like Microsoft Entra ID, Google Workspace and Okta.
VPN/VDI platforms (AnyConnect, GlobalProtect, Citrix, Horizon) via SAML/OIDC or RADIUS-fronting gateways.
Cloud providers (AWS, Azure, GCP) admin consoles and CI/CD pipelines.
Solutions that plug directly into your current SSO and Zero Trust stack will shorten your migration from months to weeks.
Compliance & Audit Questions to Ask Every Vendor
During security reviews, ask.
Which authenticators are recognised as phishing-resistant under NIST SP 800-63-4 and PCI DSS 4.0.1?
How does the platform support NIS2, DORA and PSD2 SCA for EU entities?
Can they map features directly to OMB M-22-09, Cyber Essentials, CAF and sector guidance (e.g. ENISA, NCSC, CISA)
What logs and reports exist for demonstrating MFA strength and exception handling to auditors?
Best Practices, Training and Operations
Strong technology still fails without good policies, device hygiene and operations.
Preventing MFA Bypass: Policies, Device Hygiene and Conditional Access
Combine phishing-resistant MFA with:
Conditional access (device state, location, risk).
Device compliance checks (EDR, OS version, jailbreak/root detection)
Least privilege and just-in-time access for admin roles.
Zero Trust guidance from CISA, NIST and EU agencies all emphasise continuous verification not just a strong login. ( Centers for Medicare & Medicaid Services )
Explaining Passkeys and Security Keys to Non-Technical Staff
Humans still sit in the critical path:
Explain why SMS and basic pushes are no longer enough.
Use concrete stories (e.g. recent AiTM phishing against MPs, healthcare or banks) rather than abstract risks. ( ncsc.gov.uk )
Run simulations that include “approve/don’t approve” push scenarios and phishing sites that almost look right.
Monitoring, Logging and Incident Response for Phishing-Resistant MFA
Ensure your SIEM or XDR ingests:
Failed/passkey vs legacy MFA attempts.
Unusual device registrations and key resets.
Changes to conditional access and MFA policies.
Practically, this means instrumenting your IdP and gateways and aligning them with your existing incident playbooks something Mak It Solutions routinely designs alongside IAM and cloud security programs. ( Mak it Solutions )
Checklist and Next Steps
10-Point Phishing-Resistant MFA Readiness Checklist
We have a current inventory of all MFA journeys (incl. VPN, VDI, legacy apps).
High-risk and privileged accounts are clearly identified and grouped.
Our IdP supports WebAuthn, passkeys and FIDO2 security keys.
Conditional access policies exist for admin and sensitive data access.
We have a documented policy against SMS OTP for privileged accounts.
VPN/VDI and legacy apps have a clear path via proxies or modernisation.
Hardware key procurement, issuance and lifecycle processes are defined.
User training includes passkeys, security keys and MFA bombing scenarios.
Logs for authentication strength and exceptions feed into our SIEM.
Our roadmap explicitly maps to NIST, NIS2/DORA, PCI DSS 4.0 and sector guidance.
90-Day Roadmap Template for US, UK and EU Teams
Days 1–30 Discovery and pilots
Finalise journey inventory and risk map.
Pilot passkeys/FIDO2 for security and IT admins in one location (e.g. London or Berlin).
Days 31–60 High-risk rollout
Extend phishing-resistant MFA to cloud admin and Tier-0 systems.
Front VPN/VDI with an IdP or ZTNA service enforcing WebAuthn.
Days 61–90 Scale and embed
Roll out to workforce, focusing on US and EU hubs like New York and Frankfurt.
Integrate logs, tune conditional access, refine training and update policies.
When to Engage External IAM Partners or Vendors
You should seriously consider external help when.
Internal IAM capacity is already consumed by cloud, data or AI initiatives.
You operate in multiple regulatory regimes (US federal, UK public sector, EU KRITIS/finance)
You need to modernise web/mobile apps, not just swap an authenticator.
Mak It Solutions combines IAM, cloud and application engineering, so we can design phishing-resistant MFA and implement the identity plumbing inside your SaaS, mobile apps and cloud platforms not just at the login page. ( Mak it Solutions )
Key Takeaways
Phishing-resistant MFA relies on origin-bound public-key credentials (passkeys, FIDO2) that defeat AiTM phishing and social engineering against codes.
Regulators across the US, UK and EU now expect phishing-resistant options for high-risk access, especially in public sector, finance and critical infrastructure.
SMS OTP and basic app pushes no longer meet the bar; they remain useful as backup factors but should not protect admin or crown-jewel systems.
A phased, 90-day roadmap starting with admins and remote access, then extending to workforce and legacy apps is realistic for most mid-size enterprises.
Success requires more than technology: conditional access, device hygiene, SIEM integration and training users on passkeys and security keys are equally critical.
Working with an experienced IAM and cloud engineering partner like Mak It Solutions can de-risk the phishing resistant MFA migration while keeping your product and delivery roadmaps on track.
If you’re staring at a tangle of SMS OTPs, VPN tokens and aging MFA apps, you don’t have to untangle it alone. Mak It Solutions already helps teams in the US, UK, Germany and across the EU design identity-first architectures, secure cloud landing zones and Zero Trust-aligned IAM controls.
Share a shortlist of your critical apps and regulators, and our Editorial Analytics Team can turn it into a scoped phishing-resistant MFA roadmap from passkey design to FIDO2 rollout and legacy app bridges. Start by exploring our identity and cloud security content on MakItSol.com, then request a consultation to translate this guide into a concrete 90-day plan.( Click Here’s )
FAQs
Q : Is FIDO2 always considered phishing-resistant MFA for audits and regulators?
A : FIDO2/WebAuthn authenticators are widely treated as phishing-resistant because they use origin-bound public-key cryptography rather than shared codes. CISA, NIST, ENISA and the UK NCSC all point to FIDO2-style methods as examples of strong, phishing-resistant MFA. However, individual regulators and auditors still look at implementation details: how keys are enrolled, how recovery works, whether policies actually require these methods for high-risk access, and whether weaker factors remain enabled as primary methods.
Q : Can phishing-resistant MFA replace passwords completely, or do I still need them?
A : Passkeys and FIDO2 keys can absolutely support passwordless login for workforce and customer journeys, and many organisations are already moving there for SSO and mobile apps. In practice, you’ll often run hybrid modes for some time: passwords for certain legacy systems, plus phishing-resistant MFA for SSO and admin roles. Over time, the goal is to make passwords a backup or break-glass method only, while day-to-day access relies on phishing-resistant MFA inside a Zero Trust architecture.
Q : How do passkeys work on shared or BYOD devices in US, UK and EU organisations?
A : On managed corporate devices, passkeys usually live in secure enclaves and are protected by device PIN or biometrics; policy and MDM decide which apps and accounts they can access. On BYOD and shared devices, you’ll rely more on synced passkeys with strong device posture checks, plus conditional access that can step up to hardware keys for risky sessions. For GDPR/UK-GDPR and NIS2 compliance, you should document how device management, revocation and data residency are handled, especially if passkeys are synced via consumer cloud accounts.
Q : What are common pitfalls when rolling out hardware security keys at scale?
A : Typical pitfalls include underestimating logistics (ordering, shipping, spares), not defining clear ownership (who pays, who stores spares), and weak recovery processes when keys are lost. Users may resist carrying a new device if UX is poor or if keys are required for every low-risk login. Successful programmes define where keys are mandatory (admins, finance, SOC), where platform passkeys are enough, and they invest in simple enrolment, self-service recovery and good support documentation.
Q : How does phishing-resistant MFA fit into a Zero Trust architecture for remote and hybrid workforces?
A : In Zero Trust, every access request is continuously evaluated; phishing-resistant MFA is the identity front door. It ensures initial claims are strong and AiTM-resistant, so device posture, network context and behaviour analytics are built on a trustworthy identity signal. Frameworks from CISA, NIST and EU bodies all treat strong MFA as a core pillar of Zero Trust, especially for remote and hybrid users accessing SaaS, cloud admin consoles and critical data.


