Sovereign Cloud vs Hyperscalers: GCC Decision Guide
Sovereign Cloud vs Hyperscalers: GCC Decision Guide

Sovereign Cloud vs Hyperscalers: GCC Decision Guide
In the GCC, sovereign cloud is usually best for highly regulated, security-sensitive and government workloads where data residency and national laws from SAMA, TDRA, QCB, NDMO and others are non-negotiable. Hyperscalers win when you need global reach, cutting-edge AI and ecosystem speed — and for many Saudi, UAE and Qatar organisations the real answer is a hybrid model that keeps sensitive data on sovereign or in-country cloud while using AWS, Azure or Google Cloud for analytics, GenAI and burst capacity. (Mak it Solutions)
If you’re comparing GCC sovereign cloud vs hyperscalers, start by asking which datasets regulators care most about, then decide which parts of your stack can safely live on global platforms without putting licences or trust at risk.
Introduction
“Where does our data actually live?” has become a board-level question in Saudi Arabia, the UAE and Qatar. Between fast-moving GenAI pilots, stricter data sovereignty in GCC regulations and new sovereign financial and government clouds, CIOs can no longer treat “cloud region” as a technical detail it’s now a core part of each country’s digital sovereignty strategy. (Mak it Solutions)
Across Riyadh, Dubai, Abu Dhabi and Doha, you now have a mix of global hyperscalers (AWS, Azure, Google Cloud) and national/telecom-backed platforms such as sccc by stc, SITE Cloud, G42/Core42 and Ooredoo Qatar, plus in-country regions like AWS Bahrain, Azure UAE Central and Google Cloud Doha. (Mak it Solutions)
In simple terms
Sovereign cloud “wins” when you’re dealing with Saudi-compliant government data, regulated banking records or national security workloads.
Hyperscalers “win” when you need global scale, advanced AI services and rich SaaS ecosystems.
Hybrid and multi-cloud models are becoming default for GCC enterprises: sovereign for sensitive data, hyperscalers for innovation and scale, with smart connectivity in between. (Mak it Solutions)
Kuwait, Bahrain and Oman are following similar patterns, but the deepest GCC sovereign cloud vs hyperscalers moves are happening in KSA, UAE and Qatar this playbook focuses on them.
Sovereign Cloud vs Hyperscalers in the GCC What’s the Real Question?
Defining sovereign cloud vs “normal” public cloud in GCC context
In GCC conversations, sovereign cloud usually means a cloud platform where infrastructure, operations, legal jurisdiction and often ownership are tied to a specific country, with controls aligned to local regulators and national security priorities. That can be a fully national cloud (e.g. SITE Cloud in KSA), a telecom-backed platform (like sccc by stc or Ooredoo Qatar), or a joint-venture model where a hyperscaler partners with a local player under local law.
By contrast, “normal” public cloud in the GCC means standard AWS, Azure or Google Cloud regions which may be in-country (Bahrain, UAE, Qatar, Dammam) or near-country but still under the provider’s home legal regime.
Why GCC CIOs compare sovereign cloud vs hyperscalers instead of “cloud vs on-prem”
Most large organisations in Riyadh, Dubai and Doha are already in the cloud for at least some workloads. The real buyer journey is no longer “Should we move off-prem?” but:
Which workloads can live on global hyperscalers without regulatory friction?
Which workloads must sit on sovereign financial or government clouds?
How do we design for regulated workloads in Middle East cloud without losing innovation speed? (Mak it Solutions)
This is especially true for Arabic-first digital banking, e-government, health and logistics platforms that Mak It Solutions already supports across the GCC. (Mak it Solutions)
Key decision lenses.
When GCC leaders say “sovereign cloud vs hyperscalers”, they’re really weighing five lenses:
Data sovereignty in GCC
Can we guarantee residency, classification and lawful access under KSA/UAE/Qatar law?
Innovation speed & ecosystem
Do we need thousands of SaaS integrations, open-source communities and cutting-edge AI services?
Sovereign AI infrastructure in Gulf states
Where will our Arabic LLMs, GPUs and sensitive analytics actually run? (Mak it Solutions)
Operational model & talent
Do we have skills to run complex multi-cloud, or do we need more managed-service layers?
Total cost of ownership
Not just list prices, but networking, licences, compliance and people.
Compliance, Data Residency & Regulators in KSA, UAE and Qatar
AEO core answer
The key GCC compliance and data residency requirements are sector laws from SAMA, the Central Bank of the UAE and QCB; horizontal data-governance frameworks like Saudi’s NDMO; and telecom/digital regulators such as TDRA and Qatar’s CRA. Together they define where citizen and financial data may be stored, which cloud types are allowed, and when you must use sovereign or in-country regions for specific workloads.
Data residency and localisation.
KSA, UAE and Qatar all now treat GCC cloud localisation and residency as strategic policy. Examples include:
Saudi Arabia
NDMO data-classification policies and sector rules that strongly prefer in-kingdom hosting for sensitive and secret data. (Mak it Solutions)
UAE
TDRA and federal PDPL requirements that push critical government workloads into approved in-country clouds. (Mak it Solutions)
Qatar
QCB and CRA guidelines plus Hukoomi-aligned rules for government portals and banking. (Mak it Solutions)
For many organisations, this turns “Which region is cheapest?” into “Which region is allowed for this workload?” especially for Saudi-compliant sovereign cloud for government data.
Financial-sector rules from SAMA, QCB and UAE Central Bank
Banks, insurers and fintechs face an extra layer.
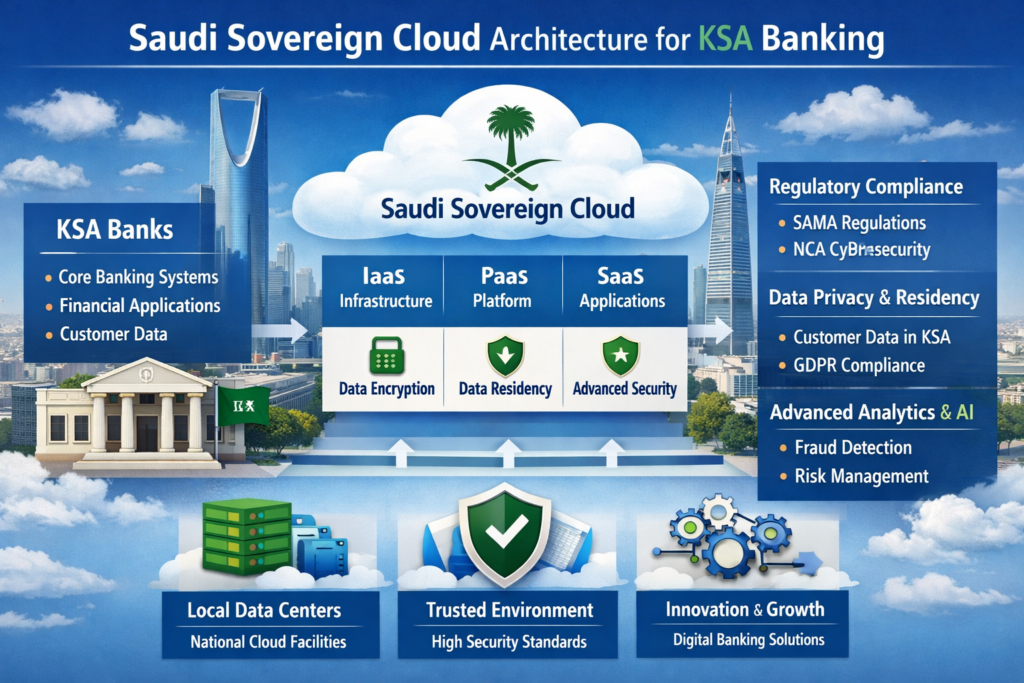
SAMA cloud and outsourcing guidelines emphasise risk, data residency and exit planning for regulated workloads in KSA.
QCB rules define what Qatar banks can host outside Doha and when they must keep data in-country. (Mak it Solutions)
CBUAE is going further with a sovereign financial cloud in partnership with Core42, designed as a fully isolated, AI-enabled cloud for UAE financial institutions under domestic jurisdiction. (GKToday)
If you’re running open banking APIs, instant payments or Sharia-compliant digital banking, these rules often push core systems toward sovereign cloud while allowing analytics and experimentation on hyperscalers. (Mak it Solutions)
Role of TDRA, NDMO, ADGM and DIFC in classifying and governing cloud workloads
Frameworks from TDRA (UAE), NDMO (Saudi), and financial zones like ADGM and DIFC give you the playbook for classifying workloads: public, internal, confidential, secret and so on and which class may run where. (Mak it Solutions)
For GCC CIOs, the practical pattern is.
Use these frameworks as your source of truth for cloud workload classification.
Map each class to allowed locations: sovereign-only, in-country hyperscaler, or global region OK.
Document this mapping inside your internal “sovereign cloud playbook” so product and data teams can move without arguing policy every time.
Architecture Options Sovereign-Only, Hybrid and Multi-Cloud Models
Sovereign-only cloud for highly classified and critical national workloads
Sovereign-only architectures show up in defence, national security, core government registers and certain central-bank systems. Everything from identity to logging lives on national or defence-grade clouds operated under local jurisdiction, sometimes with on-prem extension for ultra-sensitive data. This is where you see SITE Cloud, sccc by stc or government-owned platforms in Riyadh, plus state-backed sovereign zones in Abu Dhabi and Doha. (Mak it Solutions)
Hybrid model: sovereign for sensitive data, hyperscalers for AI, analytics and burst capacity
For most enterprises, the sweet spot is hybrid
Systems of record (citizen IDs, core banking, clinical data) on sovereign or in-country cloud.
Systems of intelligence (AI agents, analytics, personalisation) on hyperscalers with strong controls. (Cybersecurity Insiders)
Low-latency, encrypted links between them, often through SD-WAN or dedicated interconnect in GCC data centres.
This pattern aligns perfectly with using sovereign cloud GCC platforms for compliance, while leveraging AWS, Azure or Google Cloud’s AI stacks for innovation. Mak It Solutions’ guides on Middle East cloud providers and GCC sovereign cloud and data residency go deeper into these hybrid patterns. (Mak it Solutions)
Multi-cloud with low-latency links between GCC sovereign clouds and hyperscaler regions
Multi-cloud models are becoming common when you.
Need DR between Riyadh and Jeddah plus failover into Bahrain or UAE. (Mak it Solutions)
Want sovereign AI in Doha while also using US/EU regions for non-sensitive workloads.
Rely on partners like Edarat or other regional integrators to run complex interconnects and migration projects. (Mak it Solutions)
In practice, you’ll end up with traffic patterns like: Riyadh ↔ AWS Bahrain ↔ Azure UAE Central ↔ Google Cloud Doha, tied together via GCC peering and carrier-neutral hubs. (Mak it Solutions)
Country Playbooks Saudi Arabia, UAE and Qatar
Saudi Arabia: national clouds, data-localisation and regulated workloads strategy
Saudi Arabia is positioning itself as a hyperscale desert cloud hub and a sovereign anchor at the same time. Riyadh and Jeddah host growing national clouds (sccc by stc, SITE Cloud and others) alongside new hyperscaler regions like Google Cloud Dammam and strong connectivity into AWS Bahrain. (Mak it Solutions)
For sovereign cloud Saudi Arabia, patterns look like this.
Classified government and national-security data: sovereign-only in-kingdom.
Regulated workloads in KSA banking and fintech: SAMA-aligned, often sovereign or in-kingdom regions with strict exit and DR.
AI and analytics: mixed some on sovereign AI infrastructure in Gulf states, some on regional hyperscalers. (Mak it Solutions)
UAE: sovereign financial cloud, AI campuses and distributed cloud from hyperscalers
The UAE is doubling down on being an AI mega-campus and interconnect node. AWS UAE, Azure UAE North/UAE Central and local platforms like G42 Cloud/Core42 sit alongside neutral hubs in Dubai and Abu Dhabi. (Mak it Solutions)

Two big moves matter for sovereign cloud UAE.
The sovereign financial cloud launched by CBUAE with Core42 a fully isolated national cloud for banks and fintechs. (GKToday)
Deep partnerships between G42/Core42 and Microsoft to offer regulated, AI-ready sovereign environments while still tapping the Azure ecosystem. (ft.com)
If you’re comparing UAE sovereign cloud vs Azure/AWS regions, the practical pattern is: keep regulated core systems on CBUAE/sovereign environments, and run global-facing digital channels and experimentation on the public regions.
Qatar: telecom-backed sovereign cloud and AI infra for government and critical infrastructure
Qatar is leaning on Ooredoo Qatar and the Google Cloud Doha region to anchor a sovereign strategy for banking, government and critical infrastructure. (Mak it Solutions)
Typical pattern
Ministries and government portals host data in Doha, using sovereign cloud plus GCP Doha for analytics.
Banks balance QCB rules with regional DR in UAE or KSA. (Mak it Solutions)
Energy, logistics and sports mega-events use multi-cloud setups for global reach but keep sensitive data in sovereign or in-country regions.
Why are KSA, UAE and Qatar investing in sovereign cloud instead of relying only on hyperscalers? Because they want the innovation of hyperscale plus assurance of national control over financial, citizen and AI data especially as AI agents spread fast across the region. (Cybersecurity Insiders)
Cost, Latency and Business Trade-Offs Sovereign Cloud vs Hyperscalers
Cost dimensions: build vs buy, opex vs capex, talent and regulatory overhead
From a TCO angle, sovereign cloud vs hyperscalers isn’t just “more expensive vs cheaper”:
Sovereign clouds sometimes carry higher unit prices but lower legal and regulatory overhead for sensitive workloads. (Kiteworks | Your Private Data Network)
Hyperscalers may be cheaper per VM, but GCC organisations pay extra in cross-border networking, compliance reviews and vendor-lock-in risk.
You also need to cost the talent required to run multi-cloud and the overhead of audits against SAMA, TDRA, QCB and others. (Mak it Solutions)

Latency, performance and user experience
Latency is a business issue, not just a network metric. Citizens in Jeddah expect Riyadh-hosted portals to feel snappy; ecommerce users in Dubai abandon slow checkout flows; traders in Doha won’t tolerate lag on real-time dashboards. GCC data centres in Riyadh, Dubai, Abu Dhabi and Doha now give sub-region latency for most users, especially when combined with CDNs and edge nodes. (Mak it Solutions)
Risk and resilience.
Sovereign clouds reduce geopolitical and legal exposure to foreign jurisdictions but can increase dependency on a smaller ecosystem. Hyperscalers bring resilience and massive ecosystems but expose you to cross-border data and sanctions risk. Most GCC boards are therefore asking for:
At least one sovereign or in-country anchor.
Clear exit plans for each cloud provider.
Regular joint reviews with regulators to keep them comfortable with your architecture choices. (Mak it Solutions)
Sector Use Cases Banking, Government, Healthcare, Retail & Logistics
Banks and fintech.
A Riyadh fintech working under SAMA might run its core ledger and KYC on a Saudi sovereign cloud, while using Azure or AWS Bahrain for sandbox experiments, fraud analytics and GenAI-powered customer support all governed by a clear data-classification model. (Mak it Solutions)
Ministries and government platforms: digital ID, e-government and content filtering
A Dubai-based government entity may choose CBUAE’s sovereign financial cloud (for fees and collections) plus a TDRA-approved national cloud for citizen identity, while using distributed cloud from hyperscalers for global access to tourism or investment portals. Saudi ministries follow similar patterns under DGA and NDMO, keeping critical registers on sovereign infrastructures while using in-country hyperscaler regions for portals and APIs. (Mak it Solutions)
Healthcare, retail and logistics
A Doha hospital group uses sovereign cloud for patient records, Google Cloud Doha for imaging analytics and DR in UAE for resilience. (Mak it Solutions)
A Dubai ecommerce brand runs its headless storefront on a global hyperscaler but ensures customer profiles and payment tokens sit in UAE regions to respect data sovereignty in GCC. (Mak it Solutions)
A Riyadh logistics platform uses local data centres plus AWS Bahrain edges for fleet tracking and customs data, balancing latency and residency. (Mak it Solutions)
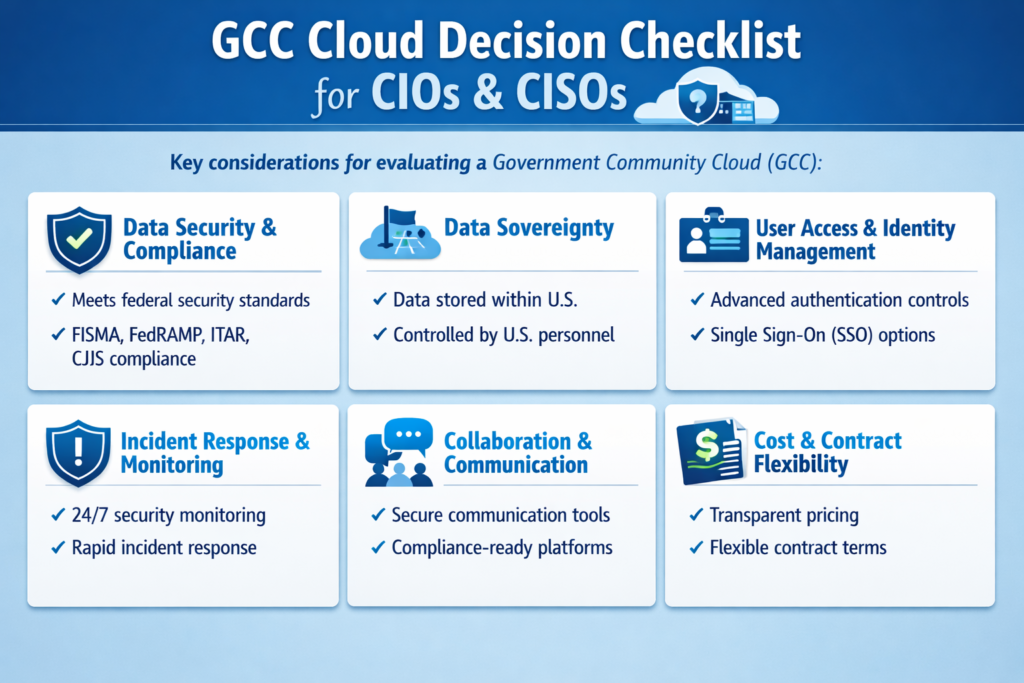
Decision Framework How GCC CIOs Can Choose Their Cloud Mix
Step-by-step decision checklist for GCC CIOs and CISOs
Here’s a practical how-to checklist you can take into your next strategy workshop.
Map regulators and data classes
List every regulator (SAMA, TDRA, QCB, NDMO, ADGM, DIFC, sector bodies) and classify data into clear tiers (public, internal, confidential, secret).
Inventory workloads and dependencies
Catalogue key apps (core banking, ERP, citizen portals, AI platforms), the data they touch and who uses them.
Assign an allowed hosting pattern per workload
For each app, decide: sovereign-only, in-country hyperscaler, or global hyperscaler region — and document the rationale.
Design reference architectures
Draw target blueprints for small, mid-size and large regulated entities, covering network, identity, encryption, DR and observability.
Plan migration and landing zones
Build GCC-aware landing zones (for example, AWS Bahrain + Azure UAE Central + sovereign KSA) and phased migration waves. (Mak it Solutions)
Align cost, FinOps and GenAI strategy
Integrate FinOps for AI so GPU-heavy workloads in Bahrain, Abu Dhabi or Doha have clear unit economics and cost guardrails. (Mak it Solutions)
Codify a “sovereign cloud playbook”
Turn all of this into a living document so product teams can move fast without re-negotiating compliance every time.
Example reference architectures for small, mid-size and large regulated entities
Smaller fintech or health startup
Single in-country hyperscaler region (e.g. Azure UAE Central) plus a managed sovereign data store for the most sensitive fields.
Mid-size bank or insurer
Dual-region hyperscaler (e.g. AWS Bahrain + UAE) plus a sovereign financial cloud zone for core banking, all tied together via Zero Trust identity controls. (Mak it Solutions)
Large ministry or telco
Multi-cloud across national clouds, AWS/Azure/GCP and AI campuses, with strong segmentation, shared observability and cross-country DR (e.g. Riyadh ↔ Jeddah ↔ Doha). (Mak it Solutions)
Building an internal “sovereign cloud playbook” for KSA/UAE/Qatar operations
Your internal playbook should
Capture per-country rules (Saudi, UAE, Qatar) and where Kuwait, Bahrain and Oman differ.
Include sample patterns for banking, government, healthcare, ecommerce and logistics.
Reference key partners from sovereign providers (sccc by stc, SITE Cloud, Core42, Ooredoo Qatar) to neutral advisors like Mak It Solutions. (Mak it Solutions)
Concluding Remarks
Choose sovereign-only when regulators or national-security stakeholders say the data is too sensitive to leave national jurisdiction.
Choose hyperscalers when you’re optimising for global reach, ecosystem depth and fast-moving AI features.
In reality, most GCC strategies going into 2026 will be hybrid or multi-cloud, mixing sovereign cloud GCC platforms with AWS, Azure and Google Cloud under a clear data-sovereignty playbook. (Mak it Solutions)
This article is for general information only and does not replace formal legal, regulatory or compliance advice for your specific organisation.
What to discuss with regulators and providers in your next GCC cloud strategy workshop
In your next session with internal stakeholders and with SAMA, TDRA, QCB or ADGM/DIFC where needed focus on
Which workloads must move to sovereign or in-country cloud in the next 12–24 months.
How you will run GenAI, Arabic LLMs and analytics without breaching residency rules. (Mak it Solutions)
What interconnect and DR topology best balances latency between Riyadh, Dubai, Abu Dhabi, Doha and second-tier GCC cities.
If you’d like a partner who already understands both GCC regulations and modern cloud/AI architectures, the team at Mak It Solutions can help you turn this playbook into a concrete roadmap for KSA, UAE and Qatar operations.
We’ve already published deep dives on Middle East cloud providers, GCC sovereign cloud and data residency, GenAI cost optimization in GCC and Arabic LLMs for regulated sectors and we can adapt those patterns to your banking, government, healthcare, retail or logistics context. (Mak it Solutions)
Reach out via our Services page to book a strategy workshop, or simply start with a short discovery call to map your current workloads, cloud contracts and regulator expectations.( Click Here’s )
FAQs
Q : Is sovereign cloud mandatory for Saudi banks under SAMA, or can they still host some workloads on hyperscalers?
A : Sovereign or in-kingdom cloud is effectively mandatory for core, regulated workloads under SAMA think core banking, payment switches, KYC and key risk systems but SAMA’s outsourcing and cloud guidelines still allow some supporting workloads to run on hyperscalers if risk, residency and exit plans are properly managed. Non-critical analytics, experimentation environments and some customer-facing digital channels can live on AWS Bahrain or other regional clouds as long as sensitive data is tokenised, encrypted and auditable. In practice, most Saudi banks end up with a hybrid mix: sovereign or national cloud for core data, hyperscalers for innovation and scale, all under a documented SAMA-aligned risk framework. (Mak it Solutions)
Q : How does the UAE’s sovereign financial cloud change cloud strategy for local and international banks in Dubai and Abu Dhabi?
A : The CBUAE–Core42 sovereign financial cloud gives banks a regulator-blessed landing zone that keeps financial data fully within UAE jurisdiction while still offering modern AI and analytics capabilities. For local and international banks in Dubai and Abu Dhabi, that means core systems, regulatory reporting and highly sensitive datasets can move off legacy on-prem hardware into a managed national cloud without long debates about data residency. At the same time, non-critical front ends, partner APIs and some AI experiments can continue to run in Azure UAE regions or other clouds, with clear segmentation and TDRA-aligned network design. The result is a more tiered cloud strategy anchored by sovereign financial infrastructure.
Q : What types of government and critical-infrastructure workloads in Qatar should stay on sovereign cloud only?
A : In Qatar, workloads that typically require sovereign-only hosting include core government registers (citizen ID, land and company records), national-security and defence systems, some law-enforcement platforms and the most sensitive layers of banking and payments regulated by QCB. These systems often run in Doha data centres operated by state-linked providers, sometimes combined with the Google Cloud Doha region under strict controls. Less sensitive portals — such as tourism, events or general information sites — can use regional or global cloud with appropriate safeguards. When in doubt, QCB and Qatar Digital Government rules generally push you to keep the crown-jewel datasets in sovereign environments and use multi-cloud mainly for reach and redundancy. (Mak it Solutions)
Q : Can GCC retailers and logistics companies meet data residency rules while using global CDNs and hyperscalers for edge performance?
A : Yes most GCC regulators focus on where primary customer data is stored and processed, not on transient cache copies in CDNs. Retailers and logistics platforms can keep authoritative customer profiles, payment tokens and sensitive shipment data inside approved GCC regions (for example, in AWS Bahrain, Azure UAE Central or a national cloud), while using global CDNs and edge nodes to accelerate images, static content and some API responses. The key is to avoid storing unencrypted personal or financial data outside allowed regions, document exactly which services run where, and align with TDRA, NDMO, SAMA or QCB guidance. Done properly, you can have fast, omnichannel experiences and still tick every data-residency box. (Mak it Solutions)
Q : How should a GCC organisation negotiate data-residency and support SLAs when choosing between local sovereign providers and hyperscalers?
A : Start by translating your regulatory obligations (from SAMA, TDRA, QCB, NDMO, ADGM, DIFC) into specific contractual requirements: exact data-location guarantees, who can access data, breach-notification timelines and audit rights. With sovereign providers, push for clarity on ecosystem roadmap, interoperability and long-term pricing; with hyperscalers, push for instances and storage pinned to GCC regions, detailed support SLAs in Middle East time zones, and explicit commitments around law-enforcement access and change management. Many GCC organisations run competitive RFPs where both national clouds and hyperscalers respond to the same residency and SLA template, then choose a portfolio of providers rather than a single winner. This gives you leverage while keeping regulators comfortable. (Mak it Solutions)


