
Saudi AI Agent IAM Security Guide
AI agent IAM security is now a real priority for teams in Saudi Arabia, the UAE, and Qatar. AI agents can access APIs, cloud systems, SaaS dashboards, customer records, support tickets, and internal workflows, so they need the same identity discipline as any other high-risk digital user.
In simple terms, AI agent IAM security means treating every AI agent as a governed non-human identity. Each agent should have a clear owner, limited permissions, short-lived credentials, audit logs, and approval controls for sensitive actions.
For GCC organizations, this is not just a technical best practice. It supports safer AI adoption, stronger Zero Trust security, and better readiness for regulatory conversations with SAMA, NCA, TDRA, QCB, and internal risk teams.
What Is AI Agent IAM Security?
AI agent IAM security is the process of controlling what an AI agent can access, what it can do, and how its actions are monitored.
An AI agent may look like a software feature, but in practice it behaves more like a digital worker. It can read data, call APIs, update tickets, trigger workflows, or move information between systems. That makes identity and access management critical.
AI Agents as Non-Human Identities
AI agents should be managed as non-human identities, similar to service accounts, workload identities, bots, and automation scripts.
That means every agent needs.
A named business owner
A defined purpose
Scoped permissions
Environment limits
Credential controls
Activity logs
A retirement or review date
Without these basics, agents can become invisible access points inside the business.
How Agent Access Differs From Human Access
Human users usually log in, make decisions, and leave visible activity trails. AI agents can act faster, across more systems, and sometimes without a person watching each step.
That speed is useful. It is also risky.
If an agent has too much access, one bad prompt, weak integration, or compromised credential can create damage across customer data, cloud resources, payment flows, or admin systems.
Why GCC Teams Should Care Now
Saudi fintechs, UAE e-commerce platforms, Qatar banks, and GCC government service teams are all exploring agentic AI. The challenge is simple: how do you let agents work without giving them dangerous access?
For regulated sectors, the pressure is even higher. SAMA’s Cyber Security Framework is used to assess cyber-control maturity and effectiveness for member organizations, so identity governance is a board-level issue for financial services teams in Saudi Arabia.
In Saudi Arabia, NCA’s Essential Cybersecurity Controls set minimum cybersecurity expectations for national entities and information technology assets. The NCA page also references the updated ECC 2-2024 controls, which makes current alignment important for security leaders.
In the UAE, TDRA describes UAE Pass as the first secure national digital identity for citizens, residents, and visitors. That wider identity-first environment is a useful reminder: AI agents should not become a shortcut around trusted authentication and approval flows.
In Qatar, QCB’s Cloud Computing Regulation entered into force on 15 April 2024 for QCB-licensed entities using cloud computing. For banks and fintechs in Doha, AI agent access should be designed with cloud governance, data protection, and audit evidence in mind.
How Least Privilege Secures AI Agents
Least privilege means an AI agent gets only the access it needs for its task nothing more.
A customer-support agent may need to read approved support records. It should not access payroll, finance systems, developer secrets, production databases, or admin panels.
For secure API boundaries around agent workflows, Mak It Solutions’ back-end development services can support controlled access patterns.
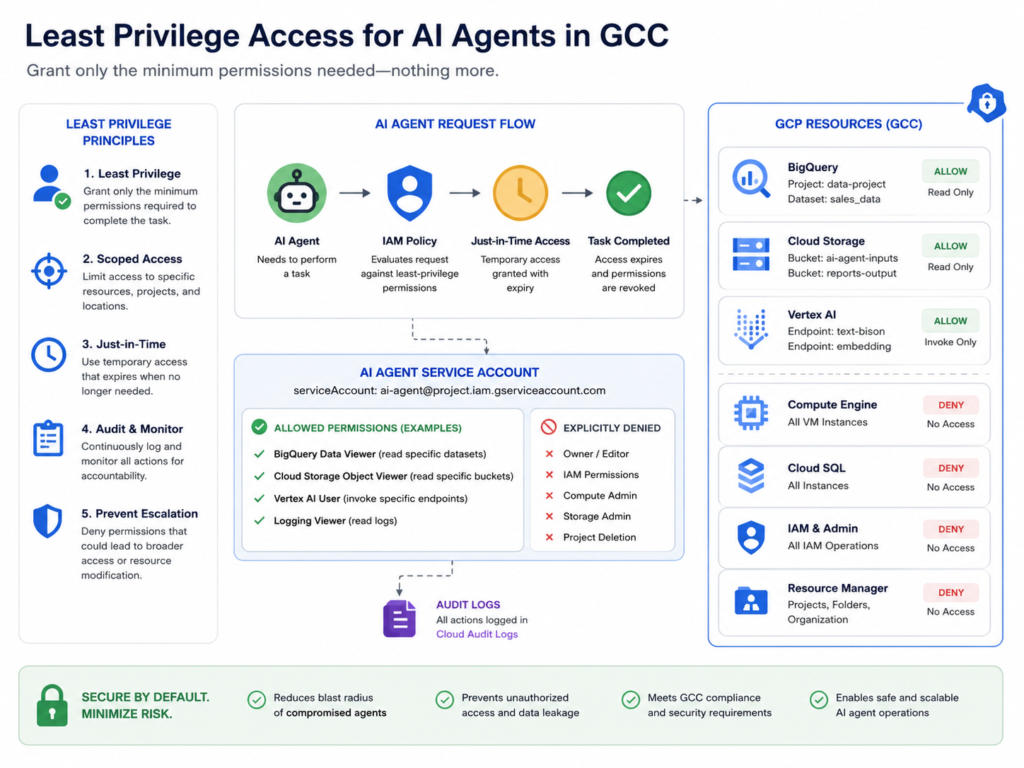
Use Scoped Roles and Short-Lived Credentials
Avoid giving AI agents permanent, broad permissions.
Use.
Scoped IAM roles
Time-bound tokens
Just-in-time access
Separate identities per agent
Automatic credential rotation
Approval gates for sensitive actions
This matters most for production changes, payment workflows, refunds, data exports, and privileged cloud operations.
Control Agent Tool Use Across APIs and SaaS
AI agents should not call every tool directly. A safer pattern is to route agent actions through a controlled gateway or policy layer.
That gateway can check.
Who owns the agent
What tool the agent wants to use
Which data category is involved
Whether the action is read-only or write-level
Whether human approval is required
For secure portals, customer journeys, and admin panels, teams can combine PHP web development with policy-based access checks.
GCC Compliance Considerations for AI Agent IAM
Compliance does not mean blocking AI. It means proving that AI access is controlled, explainable, and auditable.
Here is a practical GCC view.
| Region | Key IAM Focus for AI Agents |
|---|---|
| Saudi Arabia | Map agent access to SAMA, NCA, and data governance expectations |
| UAE | Align identity flows with Zero Trust, TDRA context, and UAE Pass where relevant |
| Qatar | Keep QCB cloud, cyber, and audit expectations visible in design decisions |
This article is general guidance, not legal or regulatory advice. Regulated teams should confirm requirements with their compliance, legal, and security teams before deploying AI agents in production.
Saudi Arabia.
A Riyadh fintech may allow an AI agent to summarize KYC files, but not approve onboarding or change customer risk ratings.
That separation matters. The agent can assist, but final regulated decisions should remain with approved staff and proper evidence.
UAE.
A Dubai platform using AI agents should keep identity flows reliable and auditable. For example, an AI agent can route a service request, but identity-linked actions should still depend on approved authentication and authorization methods.
In Abu Dhabi or Dubai financial environments, agent access should also be reviewed through risk, privacy, and compliance lenses.
Qatar.
A Doha bank or fintech should pay close attention to agent access in cloud environments.
An AI agent may summarize alerts, prepare internal reports, or classify documents. It should not independently approve sensitive financial actions, change privileged settings, or export regulated data without clear approval.

AI Agent IAM Architecture for Saudi, UAE, and Qatar Clouds
Good architecture gives agents identity, policy, secrets control, logging, and human approval.
A practical AI agent IAM setup includes.
Agent identity layer every agent has its own managed identity.
Policy engine access is checked against role, market, data type, and risk.
Secrets manager API keys and tokens are never stored in prompts or plain code.
Audit logging every sensitive action is traceable.
Human approval workflow high-risk actions require a person.
Monitoring dashboard security teams can detect unusual behavior.
Cloud Region and Data Residency Planning
GCC cloud choices should reflect latency, residency, regulator comfort, and product availability.
AWS documentation lists Middle East regions including Bahrain and UAE. Microsoft Azure’s geography page lists Qatar Central, UAE North, UAE Central, and Saudi Arabia East among its regional options. Google Cloud documentation lists me-central1 in Doha, Qatar. Teams should still confirm service availability, contractual terms, and regulator expectations before deployment.
For analytics visibility, business intelligence services can help turn IAM and agent logs into executive dashboards.
Human-to-Agent Delegation
Agents should not approve high-risk actions alone.
Use human approval for.
Payment release
Refund approval
Production deployment
Privileged cloud changes
Customer data exports
Identity-linked government services
This creates a safer balance: agents speed up work, while humans keep control of business-critical decisions.
Zero Trust Controls for AI Agent Access
Zero Trust works well for AI agents because it assumes access must be continuously verified.
The question is not “does this agent have access?” The better question is: “Should this agent have this access, in this context, right now?”
Continuously Verify Identity and Context
Before every sensitive action, verify.
Agent identity
Owner
Workload environment
Request type
Data sensitivity
Market or region
Risk score
Approval status
This helps prevent an agent in one workflow from quietly crossing into another system or market.
Monitor Runtime Behavior
AI agent behavior should be monitored during runtime, not only during setup.
For example, a Dubai retail agent suddenly exporting customer records should trigger review. A Doha banking agent calling unusual APIs should be blocked or challenged. A Saudi fintech agent requesting admin access outside its task should create an alert.

Segment Access by Role, Market, and Data Sensitivity
Do not treat GCC operations as one flat environment.
Separate access by.
KSA, UAE, and Qatar operations
Production and staging systems
Customer data and internal data
Payment records and support records
Arabic content workflows and regulated identity workflows
Segmentation limits blast radius when something goes wrong.
Use Cases Across GCC Industries
AI agent IAM security becomes easier to understand when mapped to real business scenarios.
Fintech and Banking in Riyadh, Dubai, and Doha
A Riyadh fintech can allow an AI agent to summarize KYC cases, prepare risk notes, and flag missing documents.
But the agent should not approve onboarding, override compliance flags, or change account status without human review.
For related banking AI ideas, see Mak It Solutions’ Arabic LLMs for banking guide.
Government and Smart City Services
A UAE smart-city agent may route citizen service requests, classify complaints, or help users find the right department.
But identity-linked actions should use trusted authentication, clear consent, and full audit logs.
For secure user interfaces, React development services can support controlled citizen dashboards.
Retail and Logistics AI Agents
A Dubai e-commerce brand may use agents to check inventory, update delivery exceptions, or summarize customer support issues.
That is useful. But refund approval, payment actions, address changes, and loyalty account changes need stronger controls.
For mobile-first workflows, mobile app development services can support secure customer and operations experiences.
AI Agent IAM Security Checklist for GCC Teams
Use this checklist before moving any AI agent into production.
Classify Every AI Agent
Give every agent.
Name
Owner
Purpose
Environment
Risk rating
Data access scope
Review dateRetirement plan
This helps prevent orphaned agents from keeping hidden access.
Apply Least Privilege Before Launch
Test permissions in staging first.
Remove unused access, block shared service accounts, and confirm that the agent can only perform its approved task.
A Doha SME using GCP Doha for residency-sensitive workloads, for example, should validate cloud region, logging, IAM policy, and support arrangements before launch.
Protect Secrets and Rotate Credentials
Never place API keys in prompts, agent instructions, spreadsheets, or plain code.
Use a secrets manager, rotate credentials automatically, and make sure the agent cannot reveal secrets through chat responses or logs.
Add Human Approval for Sensitive Actions
Set approval gates for high-risk steps.
This is especially important for payments, regulated customer decisions, production changes, data exports, and privileged access management.
Review Logs and Evidence Regularly
Review agent access regularly, not only during annual audits.
Security teams should track.
API calls
Permission changes
Failed requests
Data access events
Approval records
Secrets usage
Policy exceptions
For broader regional context, Mak It Solutions’ GCC cybersecurity startups guide is a useful companion.
Common AI Agent IAM Mistakes to Avoid
Many risks come from basic shortcuts.
Avoid these mistakes.
Using shared service accounts for multiple agents
Giving agents admin access “just for testing”
Keeping long-lived API keys inside prompts
Skipping audit logs for read-only access
Letting agents approve sensitive actions alone
Forgetting to remove agents after a pilot ends
Treating Saudi, UAE, and Qatar data flows as identical
In practice, most AI agent IAM problems are not caused by one big failure. They come from small access decisions that were never reviewed.

Concluding Remarks
AI agent IAM security gives GCC teams a safer way to adopt agentic AI without losing control of identity, access, and compliance evidence.
For Saudi, UAE, and Qatar organizations, the best approach is practical: treat every agent as a managed identity, apply least privilege, use short-lived credentials, log every sensitive action, and keep humans in charge of high-risk decisions.
Planning AI agent IAM security for your GCC business? Contact Mak It Solutions to design secure access controls, cloud-ready architecture, Arabic UX, and compliance-aware workflows. Start with our services page or book a consultation for a custom GCC strategy.
FAQs
Q : Is AI agent IAM security required for Saudi fintech companies?
A : Saudi fintech companies should treat AI agent IAM security as a practical requirement when agents touch customer data, KYC workflows, payment systems, or cloud workloads. SAMA-regulated teams need strong governance, audit evidence, and control maturity, so unmanaged AI agents can create real operational and compliance risk.
Q : How can UAE enterprises secure AI agents under Zero Trust?
A : UAE enterprises can secure AI agents by verifying every request, limiting permissions, and logging sensitive actions. Zero Trust should include agent identity, workload context, data sensitivity, API scope, and approval workflows.
Q : What IAM controls should Qatar banks use for AI agents?
A : Qatar banks should use role-based access, workload identity, short-lived credentials, secrets management, region-aware cloud controls, and continuous audit logging. AI agents can assist with summaries and alerts, but final regulated decisions should remain with approved staff.
Q : Can AI agents use shared service accounts in GCC companies?
A : No. GCC companies should avoid shared service accounts for AI agents because they weaken accountability. Each agent should have its own managed identity, scoped permissions, owner, logs, and lifecycle review.
Q : How do GCC businesses audit AI agent access to cloud systems?
A : GCC businesses should audit AI agent access by collecting identity logs, API calls, permission changes, approval records, secrets usage, and data-access events. Dashboards should highlight unusual access, privilege escalation, failed requests, and policy exceptions.


