Secure RAG for Banks & Enterprises in the GCC
Secure RAG for Banks & Enterprises in the GCC

Secure RAG for Banks & Enterprises in the GCC
Secure RAG helps GCC enterprises build AI knowledge systems that retrieve trusted documents, verify sources, control access, and reduce poisoned-document risks. For Saudi, UAE, and Qatar organizations, it also supports compliance, Arabic UX, data residency, and safer AI adoption.
GCC enterprises are moving quickly with AI assistants, internal knowledge bases, and bilingual customer support tools. But one poisoned policy file, outdated HR document, or poorly governed support article can manipulate answers, expose sensitive data, or damage customer trust.
For Saudi banks, UAE enterprises, and Qatar fintech firms, secure RAG is no longer a technical luxury. It is a business control. A safe setup combines trusted document pipelines, access control, source verification, LLM guardrails, audit logs, and regional compliance alignment.
For organizations planning AI transformation, Mak It Solutions’ work in Business Intelligence Services and secure backend development can support the data and application foundations needed for safe enterprise AI.
What Is Secure RAG for GCC Enterprises?
How Retrieval-Augmented Generation Works
Retrieval-Augmented Generation connects an AI model to company documents. Instead of answering only from training data, the system searches approved files, retrieves relevant passages, and generates an answer grounded in those sources.
In a Riyadh bank, that may mean retrieving credit policy. In Dubai, it could pull product and delivery rules for an e-commerce support bot. In Doha, a fintech company may use it for onboarding, compliance, and customer service knowledge.
Why Standard RAG Can Become a Security Risk
Standard RAG becomes risky when document ingestion is weak. If anyone can upload files, old versions are not removed, or permissions are ignored, the AI may retrieve unsafe content.
This is where retrieval augmented generation security matters. Without validation, vector database security, and output checks, the system can confidently repeat manipulated content.
Why Saudi, UAE, and Qatar Buyers Need Secure RAG
GCC buyers operate in regulated, multilingual, and trust-sensitive markets. SAMA-supervised financial institutions must think carefully about outsourcing, cybersecurity controls, and third-party risks; SAMA’s rulebook includes expectations around cyber controls in outsourcing processes.
For UAE government and enterprise teams, TDRA’s digital government role and FedNet services show how important secure digital infrastructure has become.
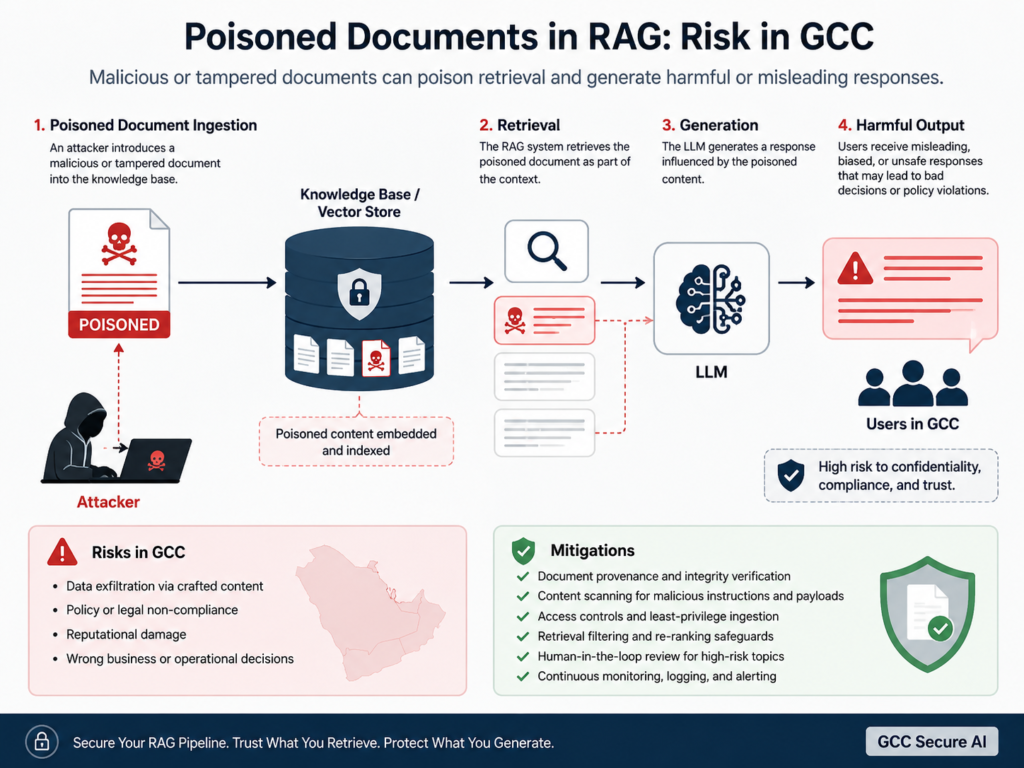
The Biggest Secure RAG Risks: Poisoned Documents and Data Attacks
What Are Poisoned Documents in a RAG System?
Poisoned documents are files intentionally or accidentally inserted into a knowledge base to influence AI output. They may include hidden instructions, false policies, malicious links, or misleading “official” language.
For example, a fake vendor policy could tell the AI to ignore approval workflows or share restricted customer details.
How RAG Poisoning Can Manipulate AI Answers
RAG poisoning works because the model relies on retrieved context. If the retrieval layer selects a malicious document, the AI may treat it as company truth.
This is especially dangerous in AI data poisoning scenarios where manipulated documents rank highly because of repeated keywords, weak metadata, or poorly managed embeddings.
GCC Examples: Banking Policies, HR Files, and Customer Support Knowledge Bases
A Riyadh fintech startup could accidentally expose a draft SAMA compliance note. A Dubai retailer could let an outdated refund policy shape support responses. A Doha SME could mix public FAQs with private finance documents.
For customer-facing platforms, teams should pair secure RAG with strong mobile app development services and front-end development so users see safe, clear, source-backed answers.
Secure RAG Architecture for Saudi, UAE, and Qatar Markets
Secure Document Ingestion and Validation
A secure document ingestion pipeline should verify file origin, scan for malicious content, classify sensitivity, remove duplicates, and require approval before indexing.
Documents should have owners, expiry dates, and version history. In practice, governance is just as important as the model itself.
Vector Database Security and Access Control
Vector database security must include encryption, role-based access, tenant separation, and retrieval filtering. A sales employee should not retrieve board documents simply because the AI search layer can “see” them.
For scalable implementation, teams may use Python development services for AI pipelines and Node.js development services for secure APIs.
Source Attribution, Guardrails, and Human Review
Secure RAG should show citations, confidence levels, and source names. LLM guardrails should block unsafe actions, detect prompt injection, and escalate high-risk answers to humans.
Mak It Solutions’ article on secure AI agents for GCC enterprises is a natural next read for teams expanding from RAG into autonomous workflows.
GCC Compliance Considerations for Secure RAG
Saudi Arabia.
Saudi enterprises should align RAG design with data classification, access control, outsourcing review, and auditability. SDAIA is the Kingdom’s authority concerned with data and AI, including big data, which makes AI governance especially relevant for national and enterprise programs.
UAE.
UAE organizations should consider TDRA expectations, ADGM and DIFC data rules where applicable, and sovereign cloud choices. TDRA has also highlighted generative AI use in UAE government portals through U Ask on FEDnet Sovereign Cloud.
Qatar.
Qatar fintech companies should evaluate QCB-aligned controls, especially for sensitive customer and financial data. QCB’s financial technology page lists fintech resources including regulatory sandbox material, AI guidelines, and DLT guidance.

Secure Arabic and Bilingual RAG for GCC Users
Arabic-English Document Retrieval Challenges
Arabic-English retrieval is not simple translation. GCC firms often store policies in English, contracts in Arabic, and support content in both languages.
Secure RAG should understand Modern Standard Arabic, Gulf phrasing, English technical terms, and mixed-language queries.
Arabic UX, Dialect Sensitivity, and Source-Grounded Answers
Arabic UX must be respectful, clear, and locally familiar. A Saudi user in Jeddah, an Emirati customer in Abu Dhabi, and a Qatari user in Doha may ask similar questions in different ways.
A strong system should return source-grounded answers without forcing users into unnatural search terms.
Why GCC Enterprises Need Localized AI Guardrails
Localized guardrails help prevent unsafe religious, legal, financial, or medical claims. They also help the AI say, “I don’t know,” when retrieved sources are weak.
That refusal is not a failure. In sensitive enterprise settings, it is a safety feature.

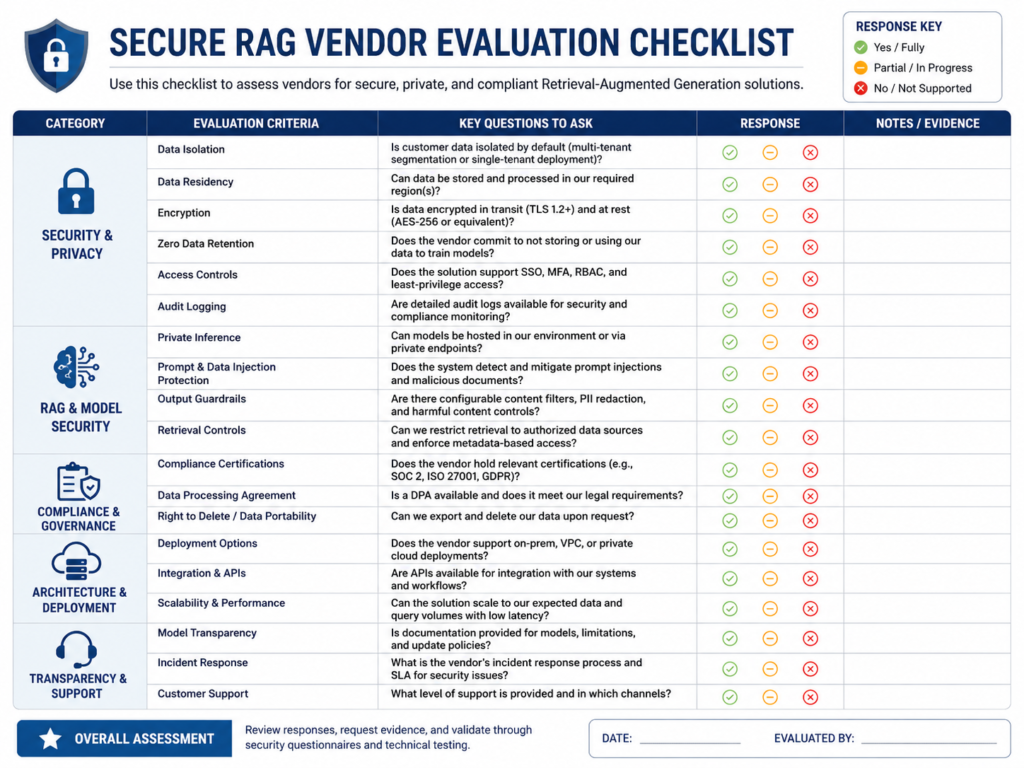
How GCC Enterprises Can Evaluate a Secure RAG Vendor
Security Questions to Ask Before Deployment
Before deployment, ask vendors how they handle.
Document approval workflows
Role-based access control
Embeddings and vector database protection
Audit logs and retrieval monitoring
Prompt injection detection
Source citations and confidence scoring
Human review for high-risk answers
Arabic-first and bilingual testing
A vendor should be able to explain these controls clearly. If the answer is vague, the risk is probably still in the system.
Data Residency Options in Saudi, UAE, and Qatar
Cloud region choices matter. AWS opened its Middle East Bahrain Region in 2019, Microsoft lists UAE Central in Abu Dhabi and Qatar Central in Doha, and Google Cloud announced its Doha region in 2023.
For deeper planning, read Mak It Solutions’ guide on Middle East cloud providers for KSA, UAE, and Qatar CIOs.
Cost, Timeline, and Implementation Readiness
Cost depends on document volume, cloud hosting, security controls, integrations, Arabic testing, and compliance review.
A practical approach is to start with one department, prove the governance model, then scale across enterprise knowledge. This reduces risk and gives compliance teams time to review how the system behaves with real users.
Best Practices for Preventing RAG Poisoning in GCC AI Systems
Create a Trusted Knowledge-Base Governance Model
Assign document owners, approval workflows, expiry rules, and metadata standards. A Riyadh fintech startup, for example, should separate SAMA-related policies from general training notes.
A useful governance model answers three simple questions.
| Area | What to Check |
|---|---|
| Ownership | Who approves and updates each document? |
| Access | Which users can retrieve each knowledge source? |
| Freshness | When does the document expire or need review? |
| Risk | Is the content public, internal, confidential, or regulated? |
Monitor Retrieval Logs, Citations, and AI Output Quality
A Dubai e-commerce brand scaling mobile apps should monitor which documents answer refund, delivery, and payment questions. Weak citations are early warning signs.
Teams should regularly review.
Which documents are retrieved most often
Whether answers cite the correct source
Whether outdated documents still appear
Whether users are asking questions the system cannot safely answer
Combine LLM Guardrails with Compliance Reviews
A Doha SME using cloud regions for data residency should combine technical guardrails with legal and compliance review.
For AI cost governance, Mak It Solutions’ AI cost control GCC guide can help teams avoid waste while improving safety.
Concluding Remarks
Secure RAG gives GCC enterprises a safer way to use AI with internal knowledge. It helps teams reduce poisoned-document risks, protect sensitive data, support Arabic and English users, and align AI systems with regional compliance expectations.
For Saudi Arabia, the UAE, and Qatar, the real advantage is trust. When AI answers are source-backed, permission-aware, and properly monitored, enterprises can move faster without losing control.
Planning secure RAG in Saudi Arabia, the UAE, or Qatar? Contact Mak It Solutions to review your knowledge base, cloud architecture, Arabic UX, and compliance readiness. You can book a consultation or explore our technology services for a custom GCC AI strategy.
FAQs
Q : Is secure RAG suitable for Saudi banks under SAMA expectations?
A : Yes. Secure RAG can support Saudi banks when it is designed with access control, audit logs, document approval, encryption, and vendor-risk review. For SAMA-regulated environments, the key is not simply using AI, but proving that sensitive banking data, customer records, and internal policies are protected.
Q : How can UAE enterprises protect AI knowledge bases from poisoned documents?
A : UAE enterprises should secure the full document lifecycle: upload, validation, classification, indexing, retrieval, and answer generation. A Dubai or Abu Dhabi company should restrict who can add content, scan files before ingestion, verify document provenance, and monitor citations.
Q : Do Qatar fintech companies need QCB-aligned controls for RAG systems?
A : Yes. Qatar fintech companies should treat RAG systems as part of their broader data governance and technology risk environment. If a Doha fintech uses RAG for onboarding, customer support, or compliance workflows, it should apply QCB-aligned controls around sensitive financial data, auditability, access rights, and vendor review.
Q : Can secure RAG support Arabic and English documents in one knowledge base?
A : Yes, but it needs careful design. Arabic and English documents can live in one knowledge base if the system supports bilingual embeddings, metadata tagging, source attribution, and language-aware guardrails.
Q : Where should GCC companies host sensitive RAG data for residency needs?
A : Hosting depends on data sensitivity, regulator expectations, business location, and cloud availability. Sensitive RAG data should be mapped before deployment so residency and cross-border transfer risks are clear.


