Multi Cloud Strategy Guide: Benefits, Risks, Fit
Multi Cloud Strategy Guide: Benefits, Risks, Fit

Multi Cloud Strategy Guide: Benefits, Risks, Fit
A multi cloud strategy is worth the effort when you need regulator-driven diversification, stronger resilience, or access to unique services that a single provider simply can’t deliver. It turns into chaos when you don’t have a clear operating model, shared tooling, and FinOps capacity in which case a well-governed single or hybrid cloud is usually safer for most US, UK and EU teams.
Introduction
If you work in a larger enterprise today, you’re probably already living in some kind of multi cloud reality even if nobody ever signed off a “multi cloud strategy” slide. M&A, shadow IT, local experiments in New York or London, sector regulators, and “quick wins” on different platforms all mean your workloads are quietly spreading across clouds. Recent industry surveys suggest that well over 80% of cloud-mature organisations now use more than one cloud provider, and over 90% report some form of multi- or hybrid-cloud strategy.
The catch: many of those landscapes evolved accidentally. Different teams bought different tools, identity patterns drifted, and suddenly nobody has a single view of risk, spend or resilience.
This guide gives US, UK, German and wider EU IT leaders a practical decision framework to decide if multi cloud is right for you and how to avoid operational chaos if you commit.
In short: a multi cloud strategy is usually justified by regulation, resilience and best-of-breed needs. When those drivers are weak and cloud maturity is low, a focused single or hybrid cloud strategy plus a strong exit and portability plan is often smarter than trying to run multi cloud at scale.
What Is a Multi Cloud Strategy?
A multi cloud strategy means deliberately running production workloads on two or more public cloud providers under a common governance, security and operating model. It’s not just “we happen to use Amazon Web Services (AWS) and one SaaS on Microsoft Azure”; it’s a conscious choice with design principles, patterns and guardrails.
At the same time, multi cloud is different from hybrid cloud: hybrid mixes public cloud with on-prem or private cloud, while multi cloud uses multiple public clouds, sometimes alongside on-prem.
Clear Definition of Multi Cloud Strategy
A multi cloud strategy is the intentional use of two or more public cloud providers (for example AWS, Google Cloud and Azure) for live workloads, with shared policies for identity, networking, security, observability and cost management. You design workloads to land on the “right” cloud, but your governance treats them as one estate.
By contrast, accidental multi cloud emerges when different teams pick different providers, tools and regions with no central design. You see duplicated platforms, inconsistent IAM, overlapping vendor contracts and no single source of truth for cost or risk. Articles like Synergy Labs’ 2026 multi-cloud guide note that around 89% of organisations say they’ve adopted multi cloud, but many underestimate the complexity tax.
For AI overview or featured-snippet style clarity.
A multi cloud strategy is a deliberate plan to run production workloads on more than one public cloud provider under a shared governance and operating model.
Multi Cloud vs Single Cloud
A well-run single-cloud strategy focuses skills, patterns and investment on one dominant provider. You go deep on that platform’s services, landing zone design, automation and guardrails. Governance is simpler, compliance checks are easier to standardise, and in-house skills build faster. Many Mak It Solutions clients pair this with focused cost optimisation sprints and platform engineering on their chosen provider. (Mak it Solutions)
Pros of single cloud.
Simpler governance, tooling and skills management
Deeper optimisation and performance tuning
Easier mapping to frameworks like GDPR/DSGVO, UK GDPR, HIPAA, PCI DSS and SOC 2
Cons of single cloud:
Higher cloud vendor lock-in risk, especially for proprietary PaaS and data services
Cloud concentration risk (too much dependency on one hyperscaler)
Less negotiation leverage if you have no credible alternative
For a bank in Berlin or a health provider working with the National Health Service (NHS) in London, a single-cloud-plus-strong-exit-plan can be entirely reasonable especially early in the cloud journey.
Multi Cloud vs Hybrid Cloud
Hybrid cloud typically means mixing public cloud with on-premises or private cloud infrastructure, often for latency-sensitive or data-sovereign workloads. Multi cloud means using more than one public cloud provider for production workloads, sometimes as part of a broader hybrid architecture.
Hybrid-only may be enough when you:
Have large sunk investment in on-prem (e.g. VMware or Hewlett Packard Enterprise (HPE) stacks)
Need ultra-low latency to factories or hospitals
Face strict sector rules but can meet them with a single strong cloud plus on-prem
Micro-answer for AEO.
Hybrid cloud combines public cloud with on-prem or private data centres, while multi cloud uses multiple public clouds often together with on-prem in complex enterprises.
When Does a Multi Cloud Strategy Actually Make Sense?
Multi cloud makes sense when your risk, regulatory or business drivers clearly demand it—not just because “everyone is doing it”. For many teams in the United States, United Kingdom, Germany and wider European Union, that means a mix of cloud concentration risk, negotiation leverage and sovereignty.
Triggers That Justify Multi Cloud
Common regulatory triggers.
Data residency and sovereignty rules (e.g. GDPR/DSGVO, UK GDPR, sector-specific laws)
Financial services and payments outsourcing rules influenced by BaFin, DORA and Open Banking expectations
Health and public sector rules similar to HIPAA or NHS guidance
BaFin has explicitly framed cloud concentration as a risk to be understood and managed in the outsourcing chain for German and EU financial institutions, not something you can ignore until renewal time.
Business drivers include
Reducing cloud concentration risk (e.g. “all trading in one provider’s region”)
Negotiation leverage when contract renewals or egress fees spike
Access to unique AI, analytics or data services on different platforms
Disaster recovery and regional resilience, especially across US and EU regions
GEO nuance.
US
CIOs in New York or Austin often explore multi cloud as a vendor lock-in escape when one provider’s costs spike or when AI workloads favour another platform.
UK
CMA scrutiny of hyperscaler dominance, high egress fees and licensing practices is pushing some London-based firms towards multi cloud or hybrid for choice and sovereignty.
Germany/EU
Banks and insurers in Berlin or Frankfurt face regulator attention on outsourcing and resilience, making “at least two providers” a realistic board-level question.
When Single Cloud or Hybrid Is Smarter
For many organisations, multi cloud is overkill and actually increases risk. It’s usually smarter to stick to single or hybrid cloud when.
You have small teams and immature SRE/DevOps practices
There is no explicit regulatory push for diversification
You lack a dedicated platform / Cloud Center of Excellence team
You don’t have FinOps capacity or unified cost tooling
Cost-optimisation platforms warn that chasing multi cloud for savings alone can backfire: many UK businesses already struggle to get value from one cloud and report poor cost visibility, with only about a third saying they fully utilise cloud capabilities.
A simpler approach is single-cloud or hybrid with a strong exit strategy:
Design portable workloads (containers, open-source databases, cloud-agnostic data formats)
Maintain tested disaster recovery plans
Negotiate contractual exit clauses and data export guarantees
AEO micro-answer
Single-cloud or hybrid is often smarter than multi cloud when teams are small, cloud practices are immature, or there’s no regulatory push. In those cases, you usually get better cost, security and reliability by going deep on one platform with a clear exit and portability plan than by spreading under-resourced teams across multiple clouds.
Quick Decision Framework for IT Leaders
Use this quick yes/no check with your leadership team.
Do regulators or customers explicitly expect diversification across cloud providers?
Do you run tier-1 workloads where a single-provider outage would be catastrophic?
Do you have a platform/Cloud Center of Excellence team that can own shared standards?
Do you already run mature IAM, observability and security automation in one cloud?
Do you have a FinOps function with bandwidth for multi cloud cost governance?
Are there unique services (e.g. AI, analytics, regional sovereign clouds) you genuinely need from a second provider?
Interpretation.
Mostly “No” → Stay with single or hybrid cloud and design strong portability and an orderly exit path. A guide like Mak It Solutions’ piece on cloud repatriation can help you sanity-check if you’ve over-rotated to cloud-first. (Mak it Solutions)
Mixed “Yes/No” → Consider a “primary + secondary” pattern: one main provider for most workloads, a second for DR, specific regions or a small set of services (often an 80/20 or 90/10 split). (Mak it Solutions)
Mostly “Yes” → Multi cloud is justifiable. Move quickly to operating model and governance design rather than accumulating accidental tool and policy sprawl.
Benefits vs Complexity Smart Strategy or Operational Chaos?
Multi cloud is neither magic nor madness by default: it’s a trade-off of flexibility and resilience against complexity, skills and governance overhead.
Multi Cloud Benefits When Done Well
When designed thoughtfully, a multi cloud strategy can deliver.
Vendor lock-in reduction & negotiation leverage
If one provider hikes prices or egress fees, it’s easier to move workloads over time.
Best-of-breed services
For example, pairing AWS analytics with cutting-edge AI services elsewhere, or using regional providers like OVHcloud for local data residency.
Resilience and DR
You can fail over critical workloads between providers and avoid putting everything in a single region or vendor blast radius. Cloudflare’s guidance on multi-cloud load balancing shows how cross-cloud routing can support this.
Geo and sovereignty benefits
European sovereignty initiatives, such as UK sovereign platforms from providers like BT Group or EU-focused sovereign regions, give extra options for data residency without abandoning hyperscalers. (Mak it Solutions)
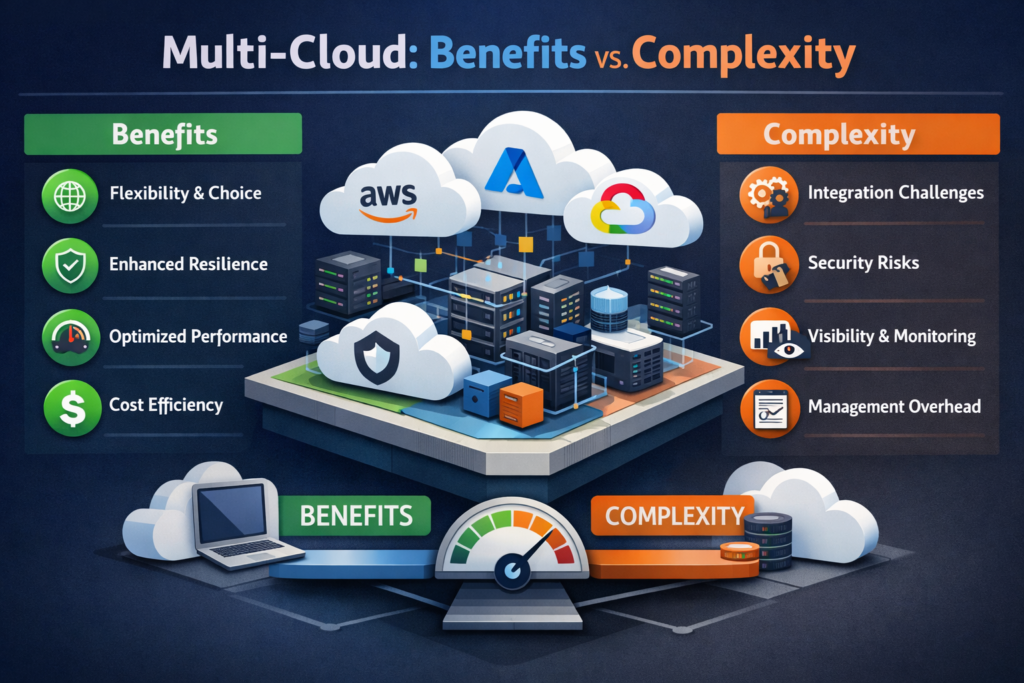
The Real Sources of Multi Cloud Complexity
The complexity doesn’t come from “having two clouds” alone it comes from duplicated everything:
Tool sprawl: three monitoring stacks, three CI/CD patterns, different policy engines
Fragmented IAM: separate identity models, inconsistent role design, weak federation (Mak it Solutions)
Inconsistent security controls: each cloud has its own exceptions and waivers
Cost visibility gaps: no single picture of business-aligned cloud spend across providers
Reports on cloud security posture show that 69% of organisations cite tool fragmentation and lack of visibility as top cloud security challenges, and 88% are already in hybrid or multi-cloud setups.
Early warning signs your multi cloud is turning into operational chaos:
No single source of truth for inventory, identities and costs
Teams re-implementing the same security controls differently in each cloud
Change reviews that only cover one provider at a time
Security exceptions becoming “how we do things”, especially for legacy apps
Frequent surprise bills where nobody can explain which team or product drove spend
If these signals feel familiar, you’ll likely benefit from a focused multi-cloud assessment and a cost-governance reboot, such as Mak It Solutions’ work on multi-cloud FinOps and cost optimisation. (Mak it Solutions)
Sector & GEO Examples of “Smart vs Chaos”
US enterprises (e.g. New York fintechs)
Some set up a secondary provider for DR or specialist AI, but without unified FinOps they simply multiply surprise bills from multiple dashboards. Others treat multi cloud as part of a broader cloud repatriation or workload-placement rethink moving batch workloads off expensive regions while keeping customer-facing systems in the cloud. (Mak it Solutions)
UK firms (London, Manchester)
TechRadar’s research shows around 60% are exploring multi cloud or hybrid ahead of a potential hyperscaler crackdown, yet only 35% report full visibility over data management exactly the conditions where multi cloud can worsen chaos.
Germany/EU banks and insurers
Under DORA and BaFin expectations, they must map cloud concentration risk and outsourcing chains, leading to deliberate multi-cloud or “primary + sovereign cloud” designs not ad-hoc tool sprawl.
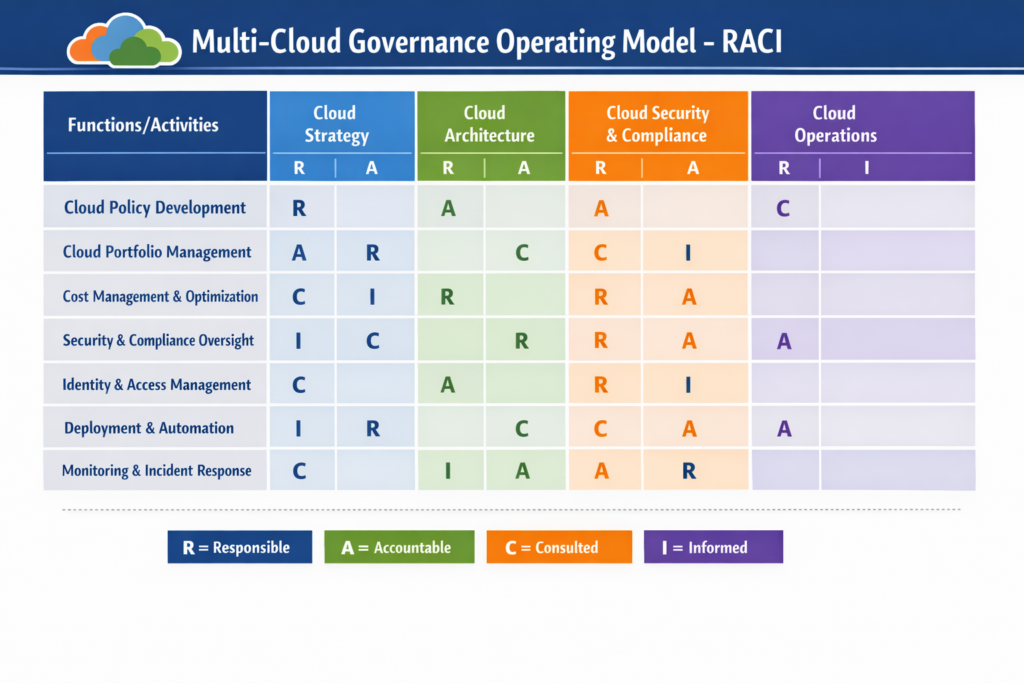
Designing a Multi Cloud Operating Model & Governance Framework
Once you justify multi cloud, the next question is “How do we run this without losing control?” Your operating model and governance make or break the strategy.
Core Governance Components
At minimum, your multi cloud governance should cover.
Policy baseline
Data residency zoning, encryption requirements, IAM standards, logging/monitoring, DR/RTO targets, approval criteria for new providers.
Standardised landing zones
Reusable blueprints with network, identity and security controls baked in for each provider, plus common tagging and resource hierarchies. N-iX and other consultancies emphasise this as the foundation of multi-cloud discipline.
Policy-as-code
Express security and compliance rules as code and push them consistently across clouds.
Compliance mapping
Align your policies with GDPR/DSGVO, UK GDPR, HIPAA, PCI DSS and SOC 2, so you can show auditors consistent controls instead of yet another spreadsheet. Mak It Solutions’ cloud data-localisation work in GCC uses exactly this portable control-mapping approach across providers. (Mak it Solutions)
Roles, Responsibilities and the Cloud Operating Model
A workable operating model usually includes.
Cloud Center of Excellence / platform team
Owns landing zones, IAM baselines, network patterns, shared observability and guardrails.
Product / application teams
Own workload architecture, SLOs and day-to-day operations, but within platform guardrails.
Security, compliance and FinOps
Provide cross-cloud standards, assurance and cost governance.
In a large US healthcare provider, that might mean a central platform group plus regional teams near New York or California. In UK public sector, you often see a small central cloud team supporting several NHS trusts or agencies with shared patterns. In German Mittelstand manufacturers, a lean central IT team coordinates a hybrid/multi-cloud backbone across SAP, MES and analytics workloads while external partners fill skills gaps. (Mak it Solutions)
Governance Patterns by Region & Sector
UK public sector & health (e.g. NHS trusts)
Often hybrid-first with multi-cloud SaaS on top. Sovereign initiatives like UK-based data centres from Zoom and others support stricter residency while still leveraging hyperscalers. (Mak it Solutions)
German/EU financial institutions
Multi-cloud designs that meet BaFin and DORA resilience expectations, often combining hyperscalers with local or sector-specific clouds, plus careful third-party risk management.
Open Banking and payments providers
Strong audit trails, change control and cross-cloud logging are mandatory; they often treat multi cloud and sovereign regions as control-enhancing, not control-weakening, when done with shared governance.
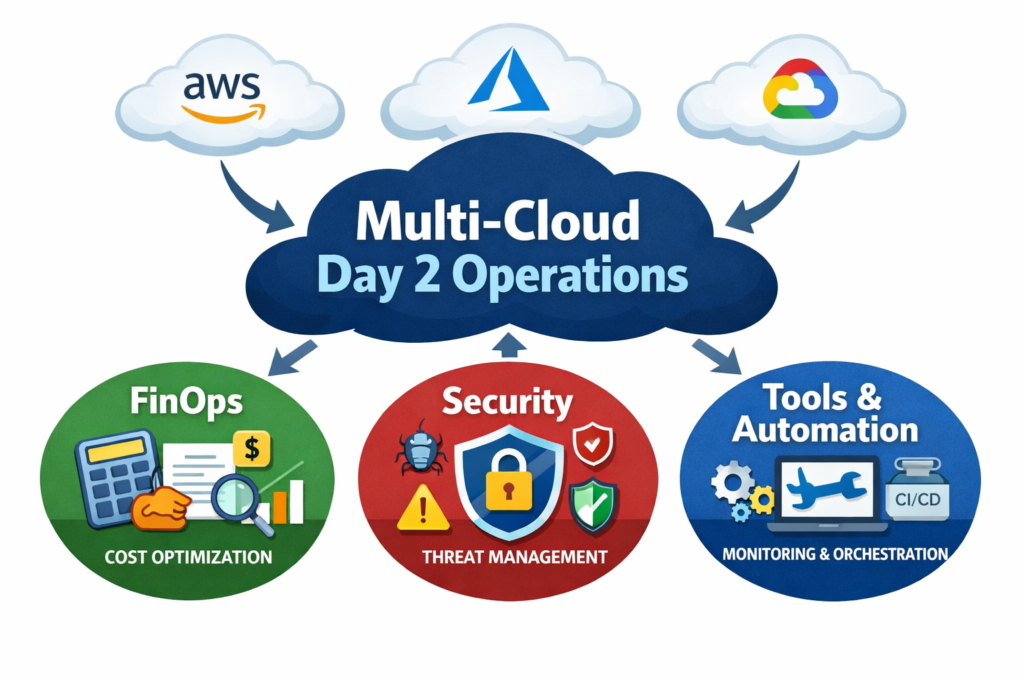
Running Multi Cloud Day 2.
Day-2 operations are where a multi cloud strategy either settles into a reliable platform or becomes an expensive, noisy mess.
Visibility, Monitoring and Incident Response Across Clouds
To keep multi cloud manageable, you need
A shared metrics and logging model across providers
Central log aggregation and APM, even if some signals remain native
SLOs and error budgets that span regions and clouds
A single on-call view instead of three separate NOC consoles
Cloudflare and others highlight how multi-cloud load balancing and global traffic management depend on unified health checks and routing decisions not separate “silos” per cloud.
Mak It Solutions often pairs cross-cloud observability with work on data platforms and lakehouse architectures so US and EU teams can see both infrastructure and data flows in one place. (Mak it Solutions)
Cloud FinOps and Cost Optimisation in Multi Cloud
Cost transparency is harder in multi cloud, not easier. Research on cloud cost intelligence shows that only around 30% of organisations know exactly where their cloud budget goes, even before multi cloud is added. (CloudZero)
At minimum, your multi-cloud FinOps model should include:
Normalised tagging and account/subscription structures across providers
A single “multi-cloud bill” dashboard aligned to products, BUs and environments
Budget alerts and anomaly detection that don’t stop at one hyperscaler
Regular cost and rightsizing reviews, including AI workloads and data-egress patterns
Mak It Solutions’ own work on Multi-Cloud Cost Optimization That Protects Performance uses exactly this approach: a unified cost model with performance guardrails so teams in the US, UK and EU can move workloads without breaking SLOs. (Mak it Solutions)
Over time, many enterprises also bring in multi-cloud management and optimisation tools to augment native dashboards, especially where they need cross-cloud commitments, discount strategies and showback/chargeback.
Cross-Cloud Security & Compliance Platforms
Multi-cloud security reports consistently show.
Tool fragmentation and visibility gaps as top risks
Identity and misconfiguration as the biggest attack vectors.
A cross-cloud security platform or managed service should help you
Centralise policy and posture management (CSPM, CNAPP)
Federate identity and SSO across providers
Manage secrets, keys and KMS integrations consistently
Prove compliance to regulators and auditors with unified evidence
For US financial services or EU critical infrastructure operators under DORA, investing in multi-cloud security as a platform, not a patchwork of tools, is often the difference between safe diversification and unmanaged risk. (Mak it Solutions)
Architecture Patterns: Multi Cloud vs Hybrid in Practice
Architecture is where strategy becomes something engineers can actually run.
Common Multi Cloud Architecture Patterns
You don’t have to go “full mesh” across every provider. Common patterns include:
Primary + secondary cloud
One main provider, a secondary for DR or specific services (e.g. AI, analytics).
DR-only secondary cloud
Critical workloads replicated in another provider, only activated during major incidents.
Best-of-breed single workload
A specific analytics or AI platform runs on a second provider while the rest stays primary.
SaaS multi cloud
Your SaaS or B2B platform runs in multiple clouds or regions for data residency and latency, while customers integrate from their own estates. (Mak it Solutions)
Each pattern maps to drivers:
Latency and user experience
Sovereignty and data residency
DR and business continuity needs
Negotiation and vendor-lock-in risk
Network, Identity and Data Design Considerations
Across multi cloud or hybrid, three things matter most
Networking & latency
Use private connectivity (e.g. interconnects, peering) where feasible and be conscious of cross-cloud egress charges. EU and UK moves to reduce some data transfer fees are helpful but not a silver bullet.
Identity & access
Treat identity as the new perimeter, pushing SSO and least-privilege roles from a central IdP into each cloud instead of reinventing local admin models. (Mak it Solutions)
Data movement & residency
Minimise cross-cloud data movement and adopt zoning: keep regulated data local, use tokenisation or pseudonymisation for cross-border analytics, and log lineage carefully for GDPR/DSGVO, UK GDPR and sector guidance.
Mak It Solutions’ work with data-localisation and sovereign cloud in GCC shows how these patterns translate well to EU and UK settings, particularly for banks and public-sector agencies. (Mak it Solutions)
GEO-Specific Patterns
US (e.g. New York SaaS)
Often “on-prem + primary cloud + secondary for DR or AI/analytics”, with cloud repatriation of some steady-state workloads when costs or latency demand it. (Mak it Solutions)
UK (London, Manchester)
Hybrid plus multi cloud is common in financial services and public sector, sometimes anchored on UK sovereign platforms alongside AWS and Azure regions.
Germany/EU (Berlin, Frankfurt)
SAP-heavy Mittelstand and banks blend on-prem, EU-centric hyperscaler regions and occasionally sovereign or regional providers, guided by DSGVO, DORA and BaFin outsourcing expectations.
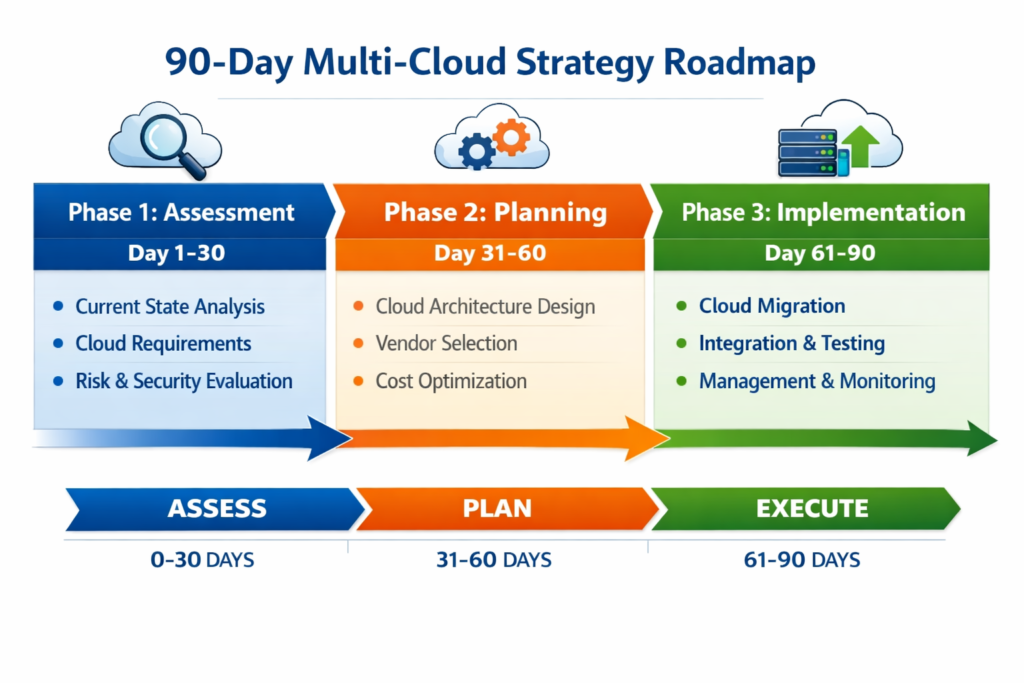
90-Day Plan to De-Risk or Refresh Your Multi Cloud Strategy
You don’t need a five-year programme to get your multi cloud strategy under control. A focused 90-day plan can dramatically reduce risk and set a clearer direction.
Days 1–30 Assess Reality and Concentration Risk
Inventory providers and workloads –
Catalogue all cloud providers, regions, accounts, subscriptions and major workloads including “shadow IT” SaaS.
Map data flows and residency
Identify which datasets sit where, especially for regulated or customer-sensitive data.
Assess concentration risk
Look for both “too much in one cloud/region” and “too many providers for your capacity to manage”. Reports on multi-cloud security repeatedly show that complexity, not just choice of vendor, drives incidents. (TechRadar)
Many Mak It Solutions clients combine this step with a quick-hit review of identity and access, using guidance from our IAM and cloud security work. (Mak it Solutions)
Days 31–60 Simplify, Standardise, and Close Gaps
Consolidate tools
Where possible, converge on a smaller set of observability, CI/CD and security tools used across clouds.
Implement tagging and guardrails
Standardise tagging, resource hierarchies and baseline policies (encryption, logging, IAM) across providers.
Centralise IAM where you can
Push SSO and role-based access controls from a central IdP to each cloud.
Fix obvious security holes
Close open storage buckets, over-privileged service accounts and unused public endpoints.
This is also a good window to decide whether specialist support FinOps, security or cloud architecture would accelerate your clean-up. Mak It Solutions often runs 4–6-week sprints focused purely on multi-cloud cost and risk quick wins. (Mak it Solutions)
Days 61–90 Decide Your Target Strategy and Investment Path
By now you should have a realistic picture of your multi cloud reality. Use it to make a deliberate choice:
“Stay single/hybrid with a strong exit plan”
If multi cloud doesn’t have a compelling driver, simplify and focus.
“Primary + secondary”
Keep one hyperscaler as the core, with another provider for DR, specific regions or unique services.
“Multi cloud at scale”
If regulation and resilience demand it, commit to platform-level investment: cross-cloud security, FinOps, and engineering capabilities.
At this stage, many IT leaders in the US, UK and EU bring in partners like Mak It Solutions for a structured strategy workshop covering governance, cloud concentration risk modelling and cost scenarios especially for highly regulated or multi-region environments. (Mak it Solutions)
Key Takeaways
A multi cloud strategy is a tool, not a religion justify it with clear regulatory, resilience or best-of-breed drivers before you add complexity.
For many teams, a well-governed single or hybrid cloud with a strong exit plan is safer than under-resourced multi cloud.
If you choose multi cloud, governance and operating model are non-negotiable: landing zones, policy-as-code, identity and observability must span providers.
FinOps and cost visibility are harder in multi cloud normalise tagging, build a single “multi-cloud bill” and automate anomaly detection early.
Cross-cloud security platforms and IAM are essential for regulated industries in the US, UK, Germany and the EU, especially under GDPR/DSGVO, DORA and sector rules.
A focused 90-day assessment and simplification plan can quickly de-risk your current estate and clarify whether multi cloud should be expanded or unwound.
If your multi cloud strategy currently lives in a handful of billing dashboards and a few stressed engineers’ heads, you don’t have to untangle it alone. Mak It Solutions already helps US, UK, German and wider EU teams design practical multi-cloud roadmaps that balance resilience, cost and compliance.
Book a short strategy conversation to review your current providers, risks and spend, and we’ll help you map a 90-day plan whether that means doubling down on multi cloud, consolidating to a primary + secondary model, or simplifying back to a safer single or hybrid cloud.( Click Here’s )
FAQs
Q : Does multi cloud always reduce cloud vendor lock-in, or can it backfire?
A : Multi cloud can reduce vendor lock-in by giving you options across AWS, Azure, Google Cloud and regional providers, but only if you design for portability. If each workload depends heavily on proprietary services, you may still be locked into one stack per application while carrying extra complexity across identity, monitoring and networking. In some cases, a well-architected single-cloud or hybrid environment with containerisation and open data formats reduces lock-in more effectively than a poorly governed multi-cloud estate.
Q : How many cloud providers are realistic for a mid-sized enterprise without overwhelming the team?
A : For most mid-sized enterprises, one primary and one secondary provider is the upper limit before complexity overwhelms available skills and budget. A primary cloud hosts the majority of workloads, while a secondary is used for DR, specialist services or specific regions such as EU or UK-only workloads. More than two public clouds usually only makes sense if you have a strong platform team, mature automation, and clear regulatory or business reasons for each provider.
Q : What skills and roles should a cloud platform team have before committing to multi cloud?
A : Before committing to multi cloud, your platform team should include strong skills in cloud networking, IAM, security engineering, SRE/DevOps, FinOps, and automation/IaC. You’ll also need people who can translate regulations like GDPR/DSGVO, UK GDPR, HIPAA and PCI DSS into technical guardrails. In practice, that often means a Cloud Center of Excellence with architects, SREs, security engineers and a FinOps lead who together define standards and reusable patterns for product teams.
Q : How does multi cloud change disaster recovery planning compared with a single-cloud strategy?
A : In a single-cloud strategy, DR planning typically focuses on cross-region resilience plus backup and restore inside one provider. In multi cloud, DR planning must also account for cross-cloud data replication, network connectivity, identity federation and runbooks that work in both environments. This offers better protection against a single-provider outage but adds complexity: you must carefully control RPO/RTO expectations, data-egress costs and configuration drift between primary and secondary clouds.
Q : Can highly regulated industries (banking, healthcare, public sector) adopt multi cloud without breaking data residency rules?
A : Yes highly regulated industries can adopt multi cloud without breaking data residency rules, but only with clear zoning and governance. Banks and public-sector bodies often use a pattern where regulated data stays in tightly controlled regions (e.g. EU or country-specific), while tokenised or pseudonymised data feeds cross-cloud analytics. Combined with strong key management, audit logs and third-party risk management, this allows them to benefit from multi cloud while staying within GDPR/DSGVO, DORA, HIPAA, NHS and local supervisory expectations.



[…] Traditional cloud security has focused on encrypting data at rest and in transit, backed by strong identity and network controls. But most breaches now happen while data is in use when applications decrypt it in memory for processing, training models or running analytics. Around 45% of data breaches now involve cloud environments, and the average cost of a cloud breach is over $5 million. […]
[…] already supported clients on topics like multi-cloud strategy, cost optimisation, confidential computing and data analytics architectures. (Mak it Solutions) If […]