OWASP Top 10 Practical Fixes: Fast Remediation Guide
OWASP Top 10 Practical Fixes: Fast Remediation Guide

OWASP Top 10 Practical Fixes: Fast Remediation Guide
If your team is searching for OWASP Top 10 practical fixes, the fastest wins are usually the least glamorous ones: lock down access control, remove insecure defaults, patch exposed components, strengthen authentication, and make logging useful enough to spot abuse early. That is the work that cuts exploitability first and gives security teams something they can actually ship.
For most product teams in 2026, a good remediation plan is not about fixing every scanner finding in order. It is about ranking issues by exploitability, business impact, and exposure of regulated or customer-sensitive workflows, then turning those findings into sprint-ready engineering tasks with clear verification steps.
Modern teams are also fixing these issues under more pressure than before. OWASP’s current released version is Top 10:2025, IBM reported the global average cost of a data breach at USD 4.88 million in 2024, and GitHub said it found 39 million secret leaks in 2024. Those numbers explain why remediation has to be practical, prioritized, and operational.
Why the OWASP Top 10 Still Matters
The OWASP Top 10 remains the clearest shared language between developers, AppSec teams, auditors, and product owners. It is not a full security program on its own, but it gives teams a reliable baseline for what tends to get exploited in real applications.
The 2025 release matters because it keeps the focus on classic high-impact risks while reflecting how modern applications now depend on APIs, cloud infrastructure, third-party packages, and delivery pipelines. In other words, secure code is not enough if the surrounding system is weak.
OWASP Top 10 Practical Fixes: Where to Start First
The best starting point is simple: fix what an attacker can abuse right now.
Use this triage order.
Exploitability
Can it be abused easily from the internet or by a normal user?
Business impact
Does it affect revenue, customer data, tenant isolation, or privileged actions?
Compliance exposure
Would this weakness create problems for HIPAA, PCI DSS, UK GDPR, GDPR, or a customer audit?
A broken access control flaw in a billing API should usually outrank a lower-risk issue on an internal admin screen. The goal is not theoretical severity. The goal is reducing real attack surface.
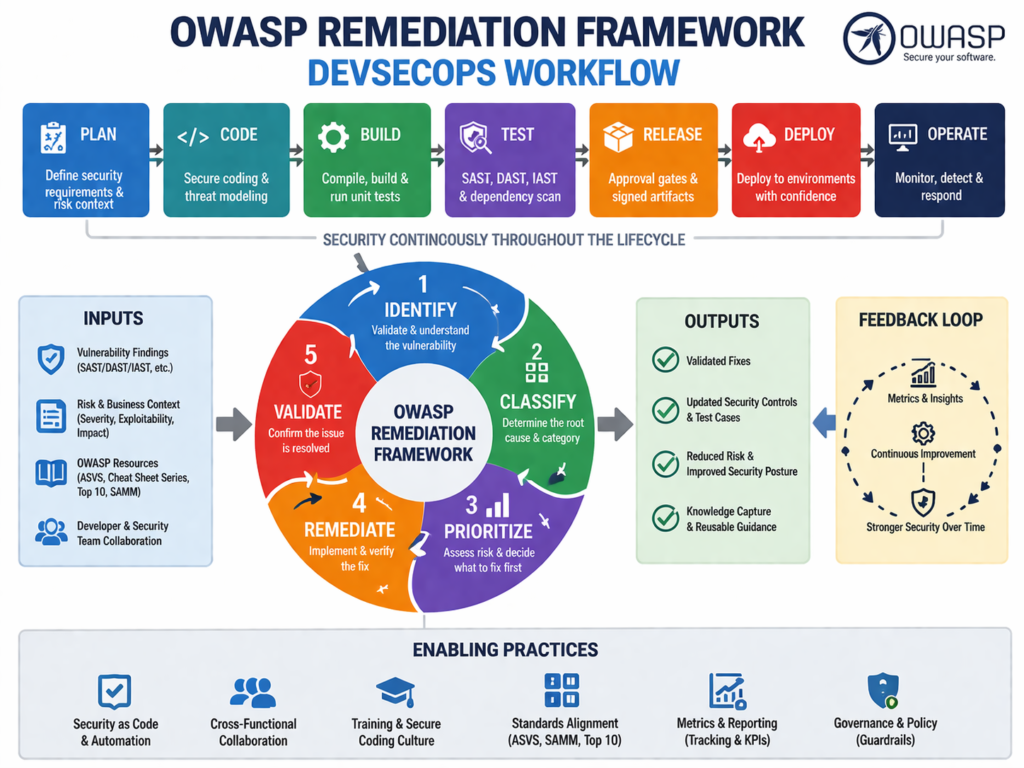
A Practical Remediation Framework for Product Teams
Triage findings by risk, not by scan order
Too many teams treat scanner output like a to-do list. That creates noise and delays. A better approach is to group findings into risk families such as.
Access control
Authentication and session handling
Cryptographic failures
Injection
Misconfiguration
Vulnerable components
Logging and monitoring gaps
That makes ownership clearer and helps teams fix patterns instead of isolated bugs.
Assign work across the right teams
Remediation works better when ownership is explicit.
Engineering fixes code, design, and test coverage
AppSec defines required controls and review standards
DevOps / Platform hardens pipelines, secrets handling, and deployment defaults
QA validates negative paths, permissions, edge cases, and regression behavior
OWASP’s Cheat Sheet Series and related guidance are useful here because they translate broad risk categories into practical defensive patterns developers can follow.
Turn every finding into a shippable ticket
A weak ticket says: “Fix injection.”
A useful ticket says.
Parameterize these queries
Validate this API input path
Add regression tests for abuse cases
Verify no sensitive errors are exposed
Document how closure was tested
That level of detail is what turns security advice into delivered work.
OWASP Top 10 Vulnerabilities and Solutions by Risk Category
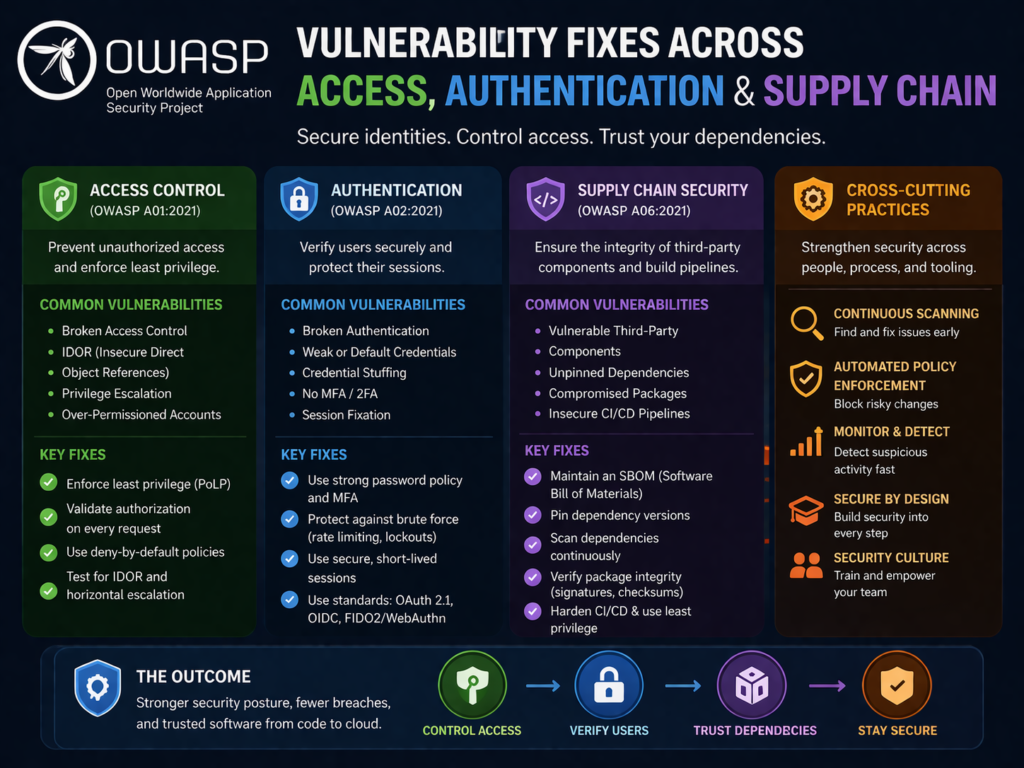
Broken access control, cryptographic failures, and insecure design
These are still among the most damaging classes of weakness because they often affect core business flows.
Practical fixes include.
enforce server-side authorization on every sensitive action
Centralize role and policy checks
Review object-level and tenant-level access in APIs
Encrypt sensitive data in transit and at rest
Replace weak keys and poor key handling
Add threat modeling before major feature releases
In practice, access control failures are dangerous because they often look like normal application use until someone tests the edges.
Injection, misconfiguration, and vulnerable components
These are the issues that often produce quick, measurable risk reduction.
Focus on.
Parameterized queries
Safe ORM usage
Input validation and output encoding
Removing default accounts and unused services
Locking down admin interfaces
Standardizing secure infrastructure baselines
Tracking dependency freshness
Scanning for exposed secrets before code is merged
GitHub’s 2024 secret leak figure is a strong reminder that secret scanning and dependency governance are now baseline controls, not nice-to-haves.
Authentication, integrity, SSRF, and logging gaps
These are often under-prioritized until an incident happens.
Start with.
MFA for privileged users
Stronger session management
Artifact signing and trusted build paths
Outbound allow lists where appropriate
Metadata service protections in cloud environments
Centralized logging tied to real abuse scenarios
Alerting that helps responders investigate quickly
Good logging does more than support investigations. It also gives your team better evidence for customers, audits, and incident review. IBM’s breach-cost reporting is a useful reminder that slow detection and messy response are expensive.
Secure Coding and Compliance Checklists
Developer checklist
Before code reaches production, developers should.
Validate authorization on sensitive routes
Keep secrets out of source code and pipelines
Use secure defaults
Review dependency risk
Peer review high-impact changes
Test both expected and abusive flows
Security review checklist
Security reviews should collect evidence such as.
Scan results
Approval records
Exception decisions
Retest notes
Pull requests
Architecture decisions for sensitive changes
That evidence matters when customers ask for proof, not promises.
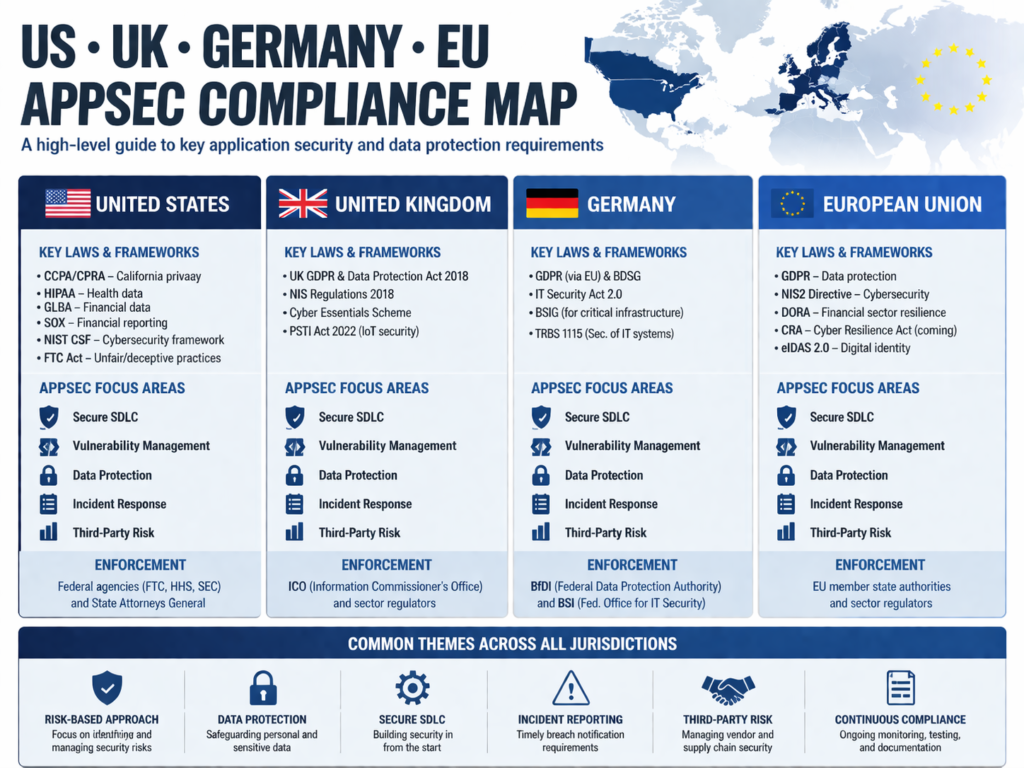
Compliance checklist for US, UK, Germany, and the wider EU
The same technical issue can carry different urgency depending on region and buyer expectations.
In the US, healthcare and regulated SaaS teams often need strong safeguards for electronic protected health information under the HIPAA Security Rule.
In the UK, teams should align remediation with accountability and data protection expectations under UK GDPR guidance.
In Germany and across the EU, GDPR obligations shape how teams think about personal data handling, access, and system design.
For payment environments, PCI DSS v4.0.1 is the current minor revision, and PCI SSC says it added clarifications but no new or deleted requirements versus v4.0.
For teams working with clients in New York, London, Berlin, or across the EU, this usually means remediation has to be evidence-ready from the start, not cleaned up at the end.
How to Test OWASP Top 10 Issues in a DevSecOps Pipeline
Different testing methods catch different problems.
| Method | Best for |
|---|---|
| SAST | code-level flaws early in development |
| DAST | runtime weaknesses and exposed behavior |
| SCA | vulnerable libraries and supply chain risk |
| IaC scanning | cloud misconfiguration before deployment |
| Manual testing | access control, business logic, tenancy, workflow abuse |
That last one still matters. Broken access control and insecure design are often difficult to validate with tooling alone. Human reviewers still need to test how the product behaves across roles, tenants, and multi-step flows.
Regional Guidance for US, UK, Germany, and EU Teams
USA
For healthcare SaaS, fintech, and ecommerce products, focus on.
Access control
Audit trails
Encryption
Vendor and dependency governance
US buyers in regulated spaces usually care about implementation detail, not just tool reports.
UK
For NHS-facing suppliers, fintech platforms, and data-heavy SaaS products, repeatable controls and clear documentation matter. UK GDPR guidance puts the emphasis on responsible handling of personal data and accountability, so remediation should support both security and governance.
Germany and the wider EU
For teams serving Germany or the broader EU market, privacy-by-design thinking is not just a legal phrase. It influences architecture, data minimization choices, access boundaries, and how clearly you document processing activity. That often makes clean system design just as important as the code fix itself.
Why OWASP Remediation Fails
Most failed remediation programs break down for three reasons.
Teams fix scanner output instead of root causes
Ownership is split across engineering, security, and platform teams
Closure is declared without strong retesting or evidence
The result is predictable: the same issue pattern comes back in the next sprint, next release, or next customer review.
A better approach is to build one repeatable playbook per risk family. Define the owner, define the expected control, define the evidence, and review repeat findings monthly.
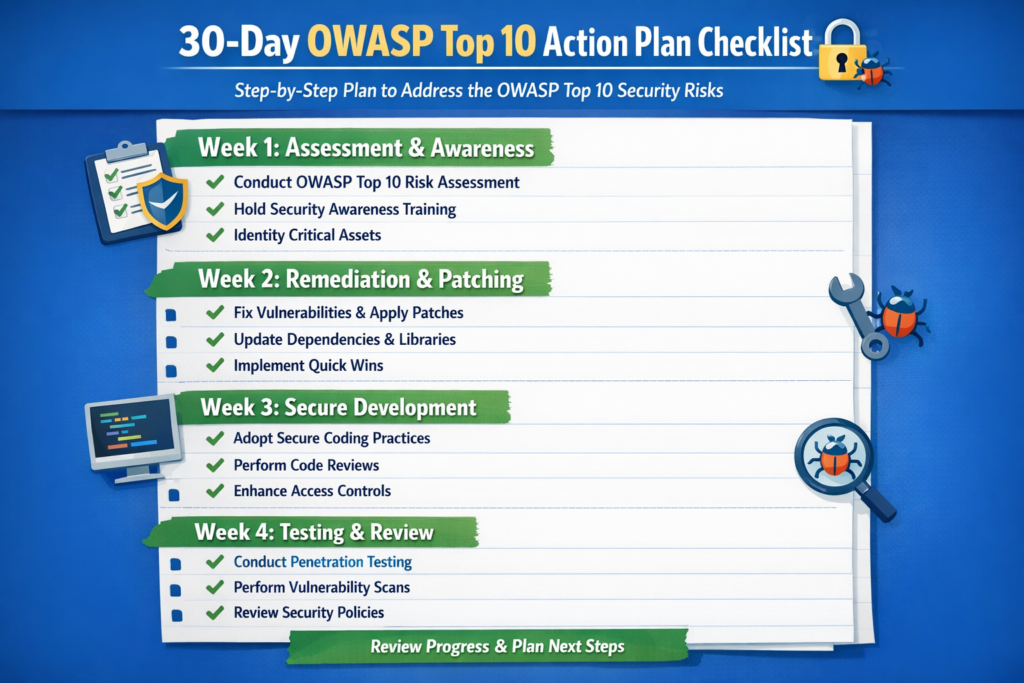
Final Checklist.
Here is a practical sequence most teams can use:
Week 1
Fix exposed access control gaps
Remove hard-coded secrets
Patch known exploitable components
Week 2
Harden authentication flows
Secure CI/CD and cloud defaults
Retest sensitive APIs and admin paths
Week 3
Improve logging and alerting
Document evidence for audits and customers
Review unresolved exceptions with engineering leadership
This is where OWASP Top 10 practical fixes become useful: not as a generic checklist, but as a short, disciplined plan your team can actually execute.
Concluding Remarks
The best OWASP Top 10 practical fixes are not the ones that sound impressive in a report. They are the ones your team can prioritize, ship, verify, and defend in front of customers, auditors, and internal stakeholders. Start with exploitable issues, tie every fix to business risk, and build evidence as you go. ( Click Here’s )
FAQs
Q : Is the OWASP Top 10 enough on its own?
A : No. It is a strong starting point, but mature teams usually combine it with secure coding standards, threat modeling, architecture review, dependency governance, and operational monitoring.
Q : Which OWASP risks are hardest to automate?
A : Broken access control, insecure design, and multi-step business logic abuse are usually the hardest to automate well because they depend on how the product behaves in real workflows.
Q : How often should teams review their backlog against the OWASP Top 10?
A : Quarterly is a good baseline, and faster-moving teams should revisit it whenever there is a major architecture change, new integration, or regulated customer requirement.
Q : What matters most for startups with limited resources?
A : Focus on the controls that prevent the most damage per hour spent: strong authentication, least-privilege access, dependency hygiene, secure defaults, and actionable logging.


