Terraform Security Best Practices for Safer Cloud IaC
Terraform Security Best Practices for Safer Cloud IaC

Terraform Security Best Practices for Safer Cloud IaC
Terraform security best practices start with four priorities: protect remote state, keep secrets out of code and state, enforce least-privilege access, and scan every change before apply. For regulated teams, that foundation matters because Terraform is not just an automation tool. It is part of your governance, audit, and compliance model across AWS, Azure, and Google Cloud.
The real risk is usually not Terraform itself. It is the way teams handle credentials, state files, modules, runners, and approvals. In regulated environments, one loose backend policy or one over-privileged pipeline can create exposure across multiple accounts, regions, and production systems.
That risk is not theoretical. Google Cloud reported that weak or absent credentials accounted for 47.1% of observed cloud initial access activity in the first half of 2025, while misconfigurations accounted for 29.4%. Verizon’s 2025 DBIR analyzed more than 22,000 security incidents, including 12,195 confirmed breaches, and said credential abuse made up 22% of leading initial attack vectors. ISC2’s 2024 workforce study also estimated a global cybersecurity workforce of 5.5 million, with a gap of 4.8 million. Put together, those numbers explain why regulated teams need simpler, enforceable Terraform controls instead of more manual review.
What Terraform Security Best Practices Actually Cover
Terraform security best practices cover five connected areas: state protection, secrets handling, identity and access, misconfiguration scanning, and governance before apply.
Terraform hardening is the Terraform-specific part of the picture. It includes backend security, provider credentials, workspace controls, version pinning, and safer plan/apply workflows. Broader infrastructure as code security goes further. It includes repository access, CI/CD trust, policy checks, audit evidence, and cloud guardrails.
For regulated teams in the US, UK, Germany, and the wider EU, compliance should sit inside that workflow, not outside it. If your team supports payment data, healthcare systems, or customer platforms processing personal data, Terraform changes need traceability, approvals, and evidence from the start. The HIPAA Security Rule and UK GDPR guidance both reinforce the importance of access control, safeguards, and accountable handling of sensitive systems and data.
Protect State Files and Secrets First
If you only fix one area first, fix state and secrets.
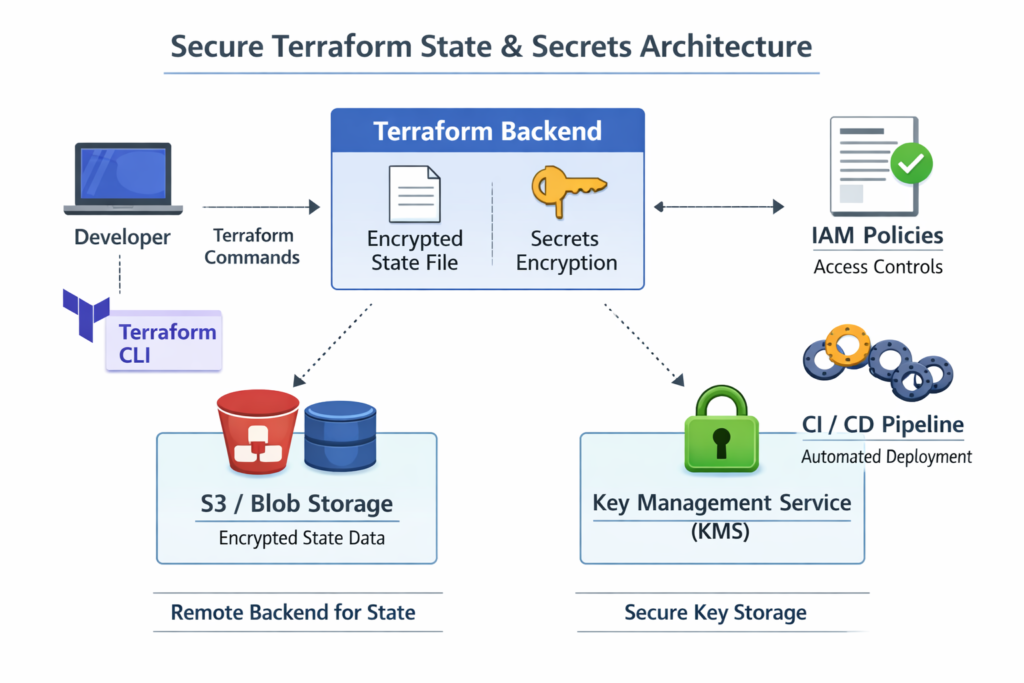
Terraform state can contain passwords, tokens, connection details, IDs, and infrastructure metadata. HashiCorp’s guidance is clear: state should be treated as sensitive, and local state is stored in plaintext by default. That alone makes unsecured local workflows risky for regulated teams.
Use remote state with encryption, locking, and narrow access
For AWS, that usually means an encrypted S3 backend with tightly scoped bucket access and locking controls. For Azure, it often means Azure Blob Storage with restricted RBAC. For Google Cloud, it typically means GCS with narrow IAM, logging, and retention.
The pattern stays the same everywhere.
Encrypt state at rest
Restrict who can read it
Control who can write or update it
Log access for audit purposes
For teams operating across London, New York, Frankfurt, or Berlin, this matters even more because state often becomes the shared layer between engineering velocity and audit evidence.
Keep secrets out of code, outputs, and long-lived variables
Marking a variable as sensitive helps reduce exposure in CLI output, but it does not make state harmless. Sensitive values can still end up in state, logs, or downstream tooling if the workflow is poorly designed.
A better model is secret reference, not secret storage. Use Vault, AWS Secrets Manager, Azure Key Vault, or Google Secret Manager to inject or broker secrets at runtime instead of hardcoding them in .tfvars, outputs, or CI variables. That improves rotation, reviewability, and separation of duties.
Enforce Least Privilege Across Terraform Workflows
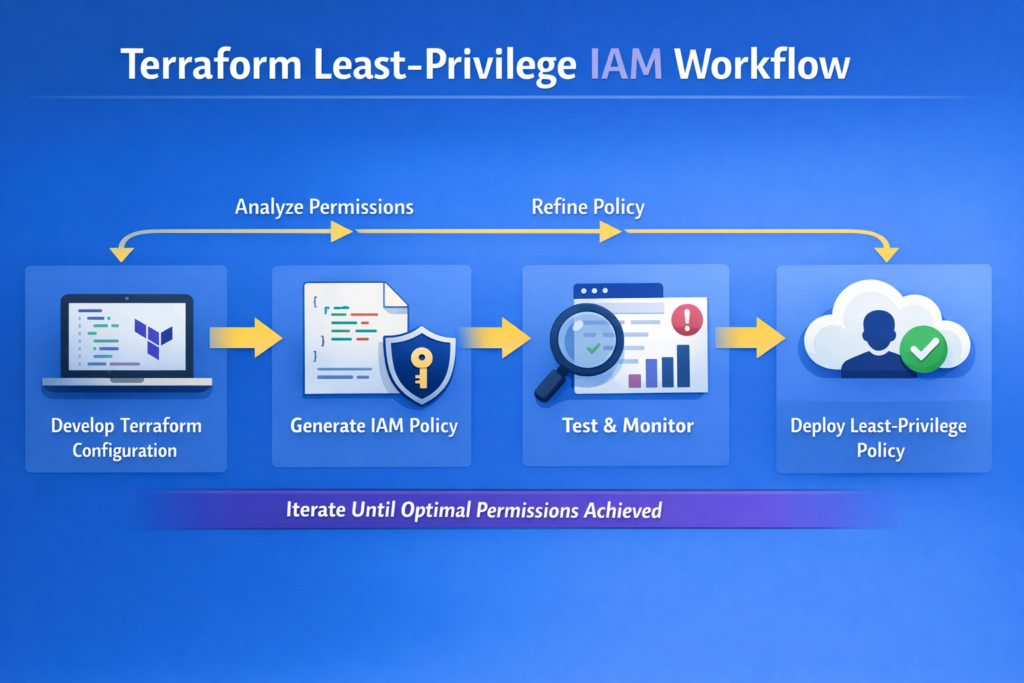
Least privilege is where many Terraform programs either mature quickly or stall.
A plan for a dev environment should not carry the same power as a production apply. A CI runner should not have blanket admin rights. And a break-glass path should never become the everyday path.
Separate human, runner, and admin identities
High-trust teams usually split access into three layers.
Human engineers get visibility and scoped planning rights
CI runners get tightly bounded execution identities
Admins manage exceptional settings, backend changes, and emergency access
That separation reduces blast radius and makes approvals easier to defend during an audit.
Prefer short-lived credentials over static keys
Static cloud keys sitting in CI secrets are still common, but they are rarely the best choice. GitHub recommends OpenID Connect-based federation for cloud deployments so teams can avoid storing long-lived credentials in repositories. For Terraform automation, that is a stronger default for AWS and similar patterns apply across other cloud platforms.
Split plan, apply, and privileged administration
Mature Terraform teams separate the ability to review, the ability to execute, and the ability to administer the platform itself. That separation is especially useful for fintech, healthcare, and enterprise SaaS teams that need to show who proposed a change, who approved it, and what controls were enforced before production execution.
Shift Left With Terraform Misconfiguration Scanning
Terraform misconfiguration scanning works best when it happens before anyone reaches terraform apply.
That means adding checks in local workflows, pull requests, CI validation, and pre-apply gates. The goal is to catch risky defaults early: public storage, missing encryption, open security groups, broad IAM, weak logging, and unsafe module patterns.
What to scan
A practical scanning baseline should look for.
Public exposure on storage or services
Encryption gaps
Over-broad IAM permissions
Logging disabled where it should be enabled
Drift-prone defaults
Insecure networking and open ingress paths
Teams often get more value when they treat scan findings as architecture feedback, not just pass/fail noise.
Where scanning belongs
Layered scanning is usually the strongest model.
Pre-commit checks for fast developer feedback
Pull request scanning for code review visibility
CI validation for consistent enforcement
Pre-apply policy gates for production protection
That structure reduces rework and keeps risky changes from moving downstream.
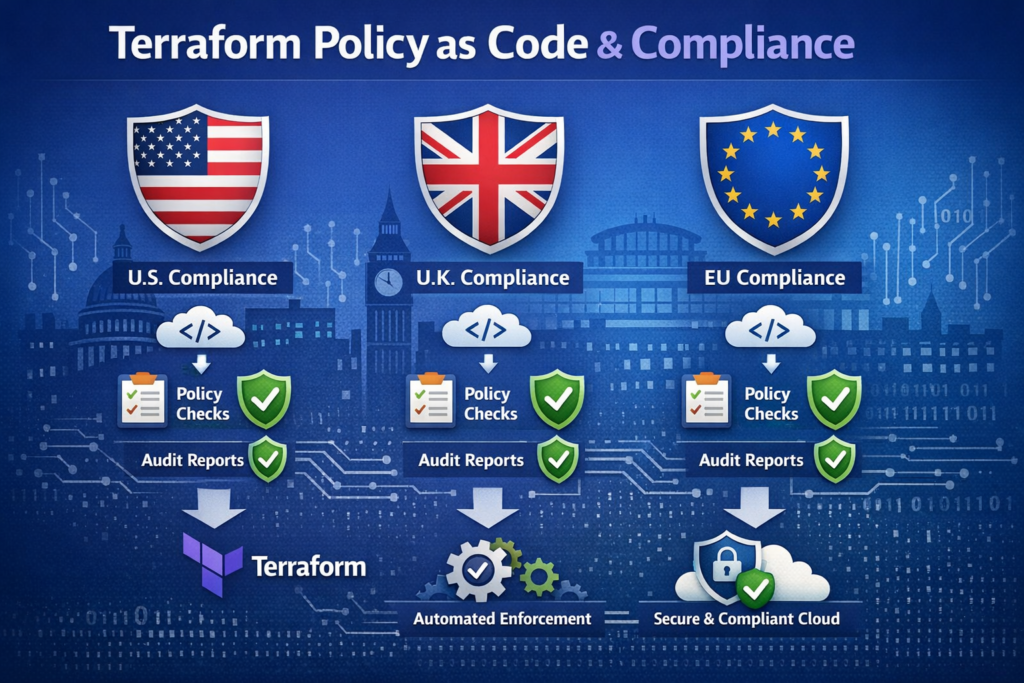
Use Policy as Code for Terraform Compliance and Governance
Policy as code is what turns Terraform from “secure when people remember” into “secure by default.”
Instead of relying on manual review to catch the same issues repeatedly, teams can encode rules such as:
Deny public buckets
Require encryption
Block certain production applies without approval
Enforce tagging, logging, or region restrictions
Require documented exceptions for policy overrides
Sentinel vs. OPA
Sentinel fits naturally in HashiCorp-centered workflows. OPA is broader and works well across CI/CD, APIs, and platform controls beyond Terraform. OPA describes itself as a general-purpose policy engine, which is why many platform teams use it as part of a wider governance model rather than a Terraform-only solution.
Map technical rules to real compliance duties
Good policy is not just technical preference. It should map to obligations your organization already has.
For example.
US healthcare teams may need stronger evidence around access, encryption, and safeguards
US and UK fintech teams often need cleaner approval trails and stronger change accountability
Germany and wider EU teams may need documented data residency and GDPR-aligned control decisions
UK teams handling personal data should align workflows with UK GDPR governance expectations
That mapping is what makes Terraform governance useful to both engineers and auditors.
Make room for exceptions without losing control
Real environments need exceptions. The right approach is not to bypass policy informally. It is to allow time-bound exceptions with reviewer identity, business justification, and compensating controls. That makes later audits much easier.
Secure Pipelines, Modules, and Runners
Terraform runners are privileged systems. Treat them that way.
Use ephemeral execution where possible. Limit outbound access. Keep logs free from secrets. Avoid static credentials on runners. Review who can trigger workflows and from which branches or environments.
Version pinning also matters. Pin providers and modules, review their source, and avoid floating dependencies in production. Supply-chain risk is easier to manage when dependencies are intentional and reproducible.
This is one area where regulated teams often gain a lot from standardization. An approved module catalog, trusted provider policies, and repeatable runner hardening can reduce both security noise and delivery friction.
Regional Priorities for US, UK, Germany, and EU Teams
United States
US teams usually focus on auditability, access control, and evidence retention. In healthcare and payments, HIPAA and PCI-linked expectations can make Terraform governance part of the wider control environment rather than just a DevOps issue.
United Kingdom
For UK teams, UK GDPR-aligned data handling, clear approvals, and careful treatment of cross-border access are important. That becomes more visible in London-based financial platforms and NHS-adjacent delivery environments, where traceability matters as much as technical correctness.
Germany and wider EU
German and EU teams often care more deeply about accountability, outsourcing governance, and data residency. For organizations with strong regional hosting requirements, European-hosted platform options can help reduce cross-border concerns and simplify internal review.
Terraform Security Checklist for 2026
Quick wins in the first 30 days
Move state to a secured remote backend
Remove secrets from code, outputs, and long-lived CI variables
Pin provider and module versions
Add pull request and CI scanning
Replace static CI credentials with short-lived federation
Mid-term controls for scaling teams
Separate dev, staging, and production identities
Enforce policy as code
Standardize trusted modules
Add formal exception handling
Improve backend and runner logging
When dedicated platform controls make sense
If you support regulated workloads, multiple business units, or production estates across the US and Europe, manual review usually stops scaling after a point. That is when stronger platform controls, centralized policy, and audit-ready workflows become worth the investment.

Final Take
Terraform security best practices matter most when they move beyond theory and become part of daily operations. Regulated teams need more than basic infrastructure automation. They need secure state management, least-privilege access, secrets protection, policy enforcement, and audit-ready workflows that hold up under real scrutiny. When these controls are built into Terraform from the start, teams reduce risk, improve consistency, and make compliance easier to manage across cloud environments.
In practice, the strongest Terraform programs are the ones that combine automation with governance. Scanning early, enforcing policy before apply, and standardizing secure modules helps teams scale without losing control. For US, UK, Germany, and EU organizations, that balance is essential. Strong Terraform security best practices create a safer foundation for cloud growth, faster delivery, and long-term operational trust.( Click Here’s )
Key Takeaways
Terraform security best practices are really about operational discipline. Secure the state. Keep secrets out of Terraform wherever possible. Use least-privilege identities. Scan early. Enforce policy before apply. And make sure the workflow produces the kind of evidence regulated teams will need later.
That is how Terraform security best practices move from a checklist to a control system your cloud team can actually trust.
FAQs
Q : How often should Terraform security policies be reviewed?
A : Quarterly is a sensible baseline, but it should not be the only trigger. Review policies after incidents, major architecture changes, new compliance requirements, or material workflow changes.
Q : Is HCP Terraform better than self-managed pipelines for auditability?
A : Sometimes, yes. It can simplify run history, approvals, and policy hooks. But a well-designed self-managed pipeline can still be highly auditable if identity, logging, approvals, and evidence retention are handled properly.
Q : What should teams do when modules fail compliance checks?
A : Do not bypass the check by default. First decide whether the finding is a real risk, a policy gap, or a false positive. Then fix the module, replace it, or document a time-bound exception with compensating controls.
Q : Can Terraform security controls support multi-cloud governance?
A : Yes, if the controls are defined at the right level. Most teams do best with a shared baseline for encryption, IAM, logging, public exposure, and approvals, then provider-specific implementation for AWS, Azure, and Google Cloud.
Q : Is this legal, compliance, or financial advice?
A : No. This article is for educational purposes and should be used alongside your legal, compliance, and security review processes.



[…] Service mapping […]