Canary vs Blue Green Deployment for Safer Releases
Canary vs Blue Green Deployment for Safer Releases
Canary vs Blue Green Deployment for Safer Releases
Choosing between canary vs blue-green deployment is really about one thing: how much release risk you want to expose at once.
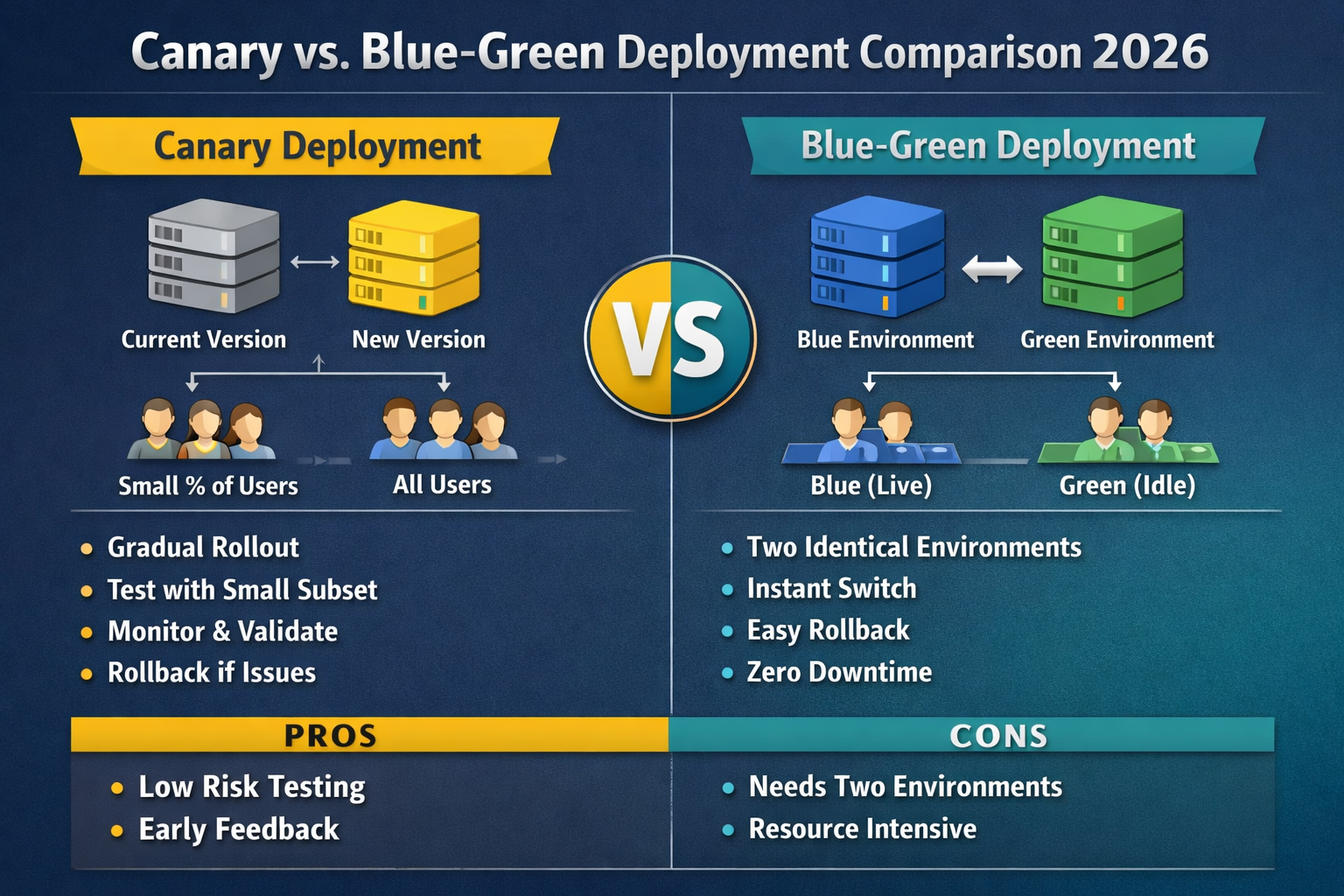
If you need the direct answer up front, here it is. Canary deployment sends a small slice of live traffic to a new release first, then expands gradually if metrics stay healthy. Blue-green deployment keeps two production-ready environments and switches traffic from one to the other, which usually makes rollback simpler and faster.
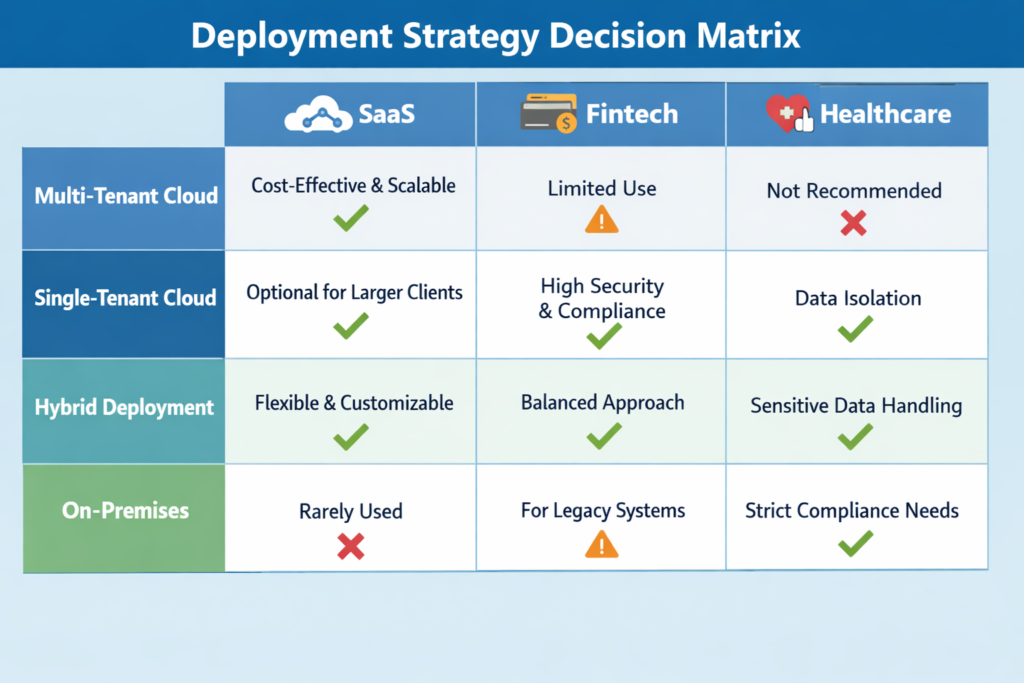
For SaaS, fintech, healthcare, and enterprise teams across the US, UK, Germany, and the wider EU, the better option is rarely the trendier one. It is the one that matches your traffic patterns, rollback expectations, infrastructure budget, and compliance needs.
Kubernetes adoption alone shows why this matters: CNCF reported in January 2026 that 82% of container users were running Kubernetes in production in 2025. Around the same time, Google Cloud highlighted DORA research showing that faster code reviews were linked to 50% better software delivery performance, while high-quality documentation was associated with 25% higher team performance. In other words, shipping faster only works when releases are controlled well.
What is the difference between canary and blue-green deployment?
The core difference is simple.
A canary deployment rolls out a new version to a small percentage of users first. If latency, error rates, and business KPIs stay healthy, traffic expands step by step until the new version is fully live. Google Cloud’s documentation describes canary as a progressive rollout that splits traffic between an existing version and a new one before full release.
A blue-green deployment runs two separate environments: one live, one staged. Once the new version is validated, traffic shifts from blue to green. AWS describes blue-green as shifting traffic between two identical environments running different versions of an application, mainly to reduce downtime risk and improve rollback capability.
So in practical terms.
Canary is better for gradual validation under real traffic
Blue-green is better for clean cutovers and quick reversals
Canary spreads risk over time
Blue-green concentrates change into a controlled switch
Canary vs blue-green deployment.
Neither strategy is universally better. Each one solves a different release problem.
Where canary deployment shines
Canary works well when your team wants evidence before a full rollout.
It is especially useful for.
High-traffic SaaS applications
APIs with sensitive latency requirements
Microservices environments
Teams using feature flags, SLOs, and observability gates
Product teams that want to reduce blast radius during launches
Argo Rollouts supports canary as an advanced Kubernetes deployment pattern, and Istio explicitly supports percentage-based traffic control for staged rollouts. That makes canary a strong fit for teams that already have mature routing and monitoring in place.
Where blue-green deployment shines
Blue-green is strong when the business cares most about operational clarity.
It often fits.
Enterprise systems with formal change windows
Regulated environments that need a clean rollback story
Applications where traffic switching is easier than progressive routing
Teams that want simpler release communication across ops, audit, and leadership
Azure’s architecture guidance for AKS describes blue-green as a way to validate a new version while the current one remains live, then shift traffic after testing. That is exactly why blue-green is popular in predictable, governance-heavy environments.
The real tradeoffs
Here is the short version:
| Factor | Canary Deployment | Blue-Green Deployment |
|---|---|---|
| Rollout style | Gradual | Environment switch |
| Rollback | Fast, but routing-dependent | Usually fastest |
| Infrastructure cost | Lower to moderate | Higher |
| Observability needs | High | Moderate |
| Operational complexity | Higher | Moderate |
| Best for | Live validation | Clean cutovers |
Canary usually needs stronger telemetry, smarter traffic controls, and clearer promotion rules.
Blue-green usually needs more infrastructure because both environments may need to run side by side. It can also get tricky when shared databases, queues, and stateful dependencies are involved.
That part matters. Fairwinds’ 2024 Kubernetes Benchmark Report evaluated more than 330,000 workloads, which is a useful reminder that tooling alone does not make releases safe. Operational discipline does.
Which strategy is better for zero-downtime releases and rollback?
If your priority is instant rollback, blue-green usually wins.
Because the previous environment is already standing by, rollback can often be handled with a traffic switch instead of a partial unwind. AWS explicitly frames blue-green as a deployment technique built to reduce downtime and improve rollback capability.
If your priority is safer validation before full exposure, canary is usually the better choice.
That is why product-led SaaS teams, API platforms, and experimentation-heavy companies often lean toward canary. You learn from real production traffic before making the full move.
A practical rule of thumb works well here:
Choose blue-green when the main question is, “How do we reverse instantly?”
Choose canary when the main question is, “How do we learn safely under live load?”

Canary vs blue-green deployment in Kubernetes
For Kubernetes teams, this is less about theory and more about the tooling stack you already trust.
Argo Rollouts supports both canary and blue-green strategies for Kubernetes. Istio adds percentage-based traffic management that is useful for staged validation. Google Cloud Deploy supports canary strategies for GKE, and Microsoft documents blue-green deployment patterns for AKS.
Canary in Kubernetes
Canary gets easier when you can separate deployment state from traffic control.
That usually means combining.
A rollout controller such as Argo Rollouts
Ingress or service mesh traffic splitting
Metrics from Prometheus, Datadog, Grafana, or similar tools
Promotion gates tied to SLOs or error budgets
In practice, this setup is a strong fit for microservices and high-traffic APIs.
Blue-green in Kubernetes
Blue-green is often easier to reason about in environments where stability matters more than fine-grained traffic shaping.
It works well when.
Your release process already depends on well-defined environments
Stakeholders want a simple rollback narrative
You are deploying a cluster or workload upgrade that benefits from side-by-side validation
That is why blue-green remains common in enterprise Kubernetes programs, especially where change management is formal.
What should US, UK, Germany, and EU teams consider?
Deployment strategy is not just a DevOps choice. For many teams, it is also a governance choice.
United States
For US healthcare teams, the HIPAA Security Rule requires administrative, physical, and technical safeguards to protect electronic protected health information. For payments environments, PCI DSS provides a baseline of technical and operational requirements to protect payment account data. In both cases, release processes need strong monitoring, controlled access, and a rollback path that can be explained clearly.
United Kingdom
UK teams need to account for resilience, vendor assurance, and personal data handling. The ICO’s UK GDPR guidance remains the key starting point for organizations processing personal data in the UK. In practice, blue-green is often easier to document in formal change records, while canary may reduce release risk where live validation matters more.

Germany and the wider EU
Across Germany and the EU, GDPR remains technology-neutral and applies regardless of how personal data is processed. For regulated firms, BaFin’s cloud computing guidance adds another layer of outsourcing, control, and oversight expectations. That is why teams in places like Frankfurt, Berlin, or Munich often evaluate deployment models on recoverability and auditability, not speed alone.
How to choose the right deployment strategy
A simple decision matrix is usually enough.
Choose canary when you have.
High production traffic
Strong observability
Mature routing controls
A product culture that values gradual validation
Microservices or service mesh architecture
Choose blue-green when you have.
Strict rollback requirements
Stable environments
Lower release frequency
Formal change governance
A need for clean environment separation
From a small business and platform engineering point of view, many mature teams eventually support both. They use blue-green for some systems, canary for others, and avoid forcing one model onto every workload.
Best practices for safer releases
No matter which model you choose, the same guardrails still matter.
Define promotion and rollback rules before release day
Set thresholds for:
Error rate
Latency
Availability
Business KPIs
Rollback triggers
This keeps release decisions evidence-based instead of emotional.
Keep database changes backward-compatible
This is where both strategies can fail.
Expand-and-contract migration patterns are usually safer than hard schema breaks because they let old and new versions coexist during the transition.
Add feature flags and audit logging
Feature flags reduce risk by separating code deployment from feature exposure.
Audit logging matters just as much in regulated environments, especially when you need to show who changed what, when, and why.
Match the strategy to your operating model
The best deployment strategy is the one your team can actually operate well.
A technically elegant canary process is still a bad choice if your routing, telemetry, and on-call maturity are weak. A clean blue-green process is still risky if your state management and rollback testing are poor.

Concluding Remarks
When teams compare canary vs blue-green deployment, the smartest choice is usually the one that fits the system, not the one that sounds more advanced.
If your team needs gradual confidence, smaller blast radius, and better real-world validation, go with canary. If you need cleaner cutovers, simpler rollback, and a release process that is easier to explain to operations and compliance stakeholders, blue-green is often the better fit.( Click Here’s )
Key takeaways
Canary vs blue-green deployment is really a choice between gradual validation and clean cutover
Canary lowers blast radius and supports progressive delivery
Blue-green usually offers the clearest rollback path
Kubernetes teams commonly support both with tools like Argo Rollouts, Istio, GKE, and AKS
Regulated teams should weigh auditability, rollback clarity, and evidence collection as heavily as speed
Database and state compatibility often decide whether either strategy succeeds
FAQs
Q : Is canary deployment better than blue-green deployment?
A : Not by default. Canary is better when you need gradual validation under live traffic. Blue-green is better when you need clean cutover and fast rollback.
Q : Is blue-green deployment more expensive?
A : Often, yes. Running parallel environments can increase infrastructure cost. Canary may cost less in infrastructure but more in operational complexity.
Q : Which is better for Kubernetes?
A : Both are valid. The better choice depends on whether your team is stronger at traffic management and observability or at environment-based release control.
Q : Does canary deployment require a service mesh?
A : No. A service mesh helps, but it is not mandatory. Some teams start with ingress-based traffic splitting and basic metric gates.
Q : Which is safer for fintech or healthcare apps?
A : There is no single winner. In regulated environments, the safer option is the one that is easiest for your team to monitor, document, and reverse cleanly.



[…] balance matters even more for teams across the US, UK, and EU, where release pressure is high but auditability, privacy, and operational clarity still […]
[…] comparative table, based on an analysis of modern deployment strategies, clarifies the decision matrix for […]